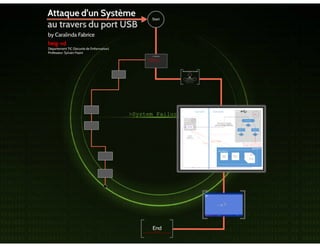
Rump attaque usb_caralinda_fabrice
•
1 recomendación•1,227 vistas
1
Denunciar
Compartir
Denunciar
Compartir
Descargar para leer sin conexión
Recomendados
Global healthcare and global healthcare marketing is changing. As emerging markets industrialize and mature, their healthcare systems rapidly change. Brazil, China, India and Saudi Arabia serve as primary examples of new healthcare markets.
www.healthcaremedicalpharamceuticaldirectory.com
John G. BareskyNew Global Healthcare - Another Chapter In Healthcare Marketing Brand Management

New Global Healthcare - Another Chapter In Healthcare Marketing Brand ManagementHealthcare-Marketing
Recomendados
Global healthcare and global healthcare marketing is changing. As emerging markets industrialize and mature, their healthcare systems rapidly change. Brazil, China, India and Saudi Arabia serve as primary examples of new healthcare markets.
www.healthcaremedicalpharamceuticaldirectory.com
John G. BareskyNew Global Healthcare - Another Chapter In Healthcare Marketing Brand Management

New Global Healthcare - Another Chapter In Healthcare Marketing Brand ManagementHealthcare-Marketing
Más contenido relacionado
Destacado
Destacado (11)
Evaluation Question 1 – In what way does your media product use, develop or c...

Evaluation Question 1 – In what way does your media product use, develop or c...
National Civic Summit - BBB Civic Ethics - Lisa Jemtrud

National Civic Summit - BBB Civic Ethics - Lisa Jemtrud
«Самоорганизуй» себя, пока не «самоорганизовали» тебя

«Самоорганизуй» себя, пока не «самоорганизовали» тебя
6° básico b semana del lunes 07 al 11 de noviembre 

6° básico b semana del lunes 07 al 11 de noviembre
Más de Cyber Security Alliance
C+ +11
METAPROGRAMMING APPLIED TO SOFTWARE OBFUSCATIONApp secforum2014 andrivet-cplusplus11-metaprogramming_applied_to_software_obf...

App secforum2014 andrivet-cplusplus11-metaprogramming_applied_to_software_obf...Cyber Security Alliance
Más de Cyber Security Alliance (20)
Robots are among us, but who takes responsibility?

Robots are among us, but who takes responsibility?
Why huntung IoC fails at protecting against targeted attacks

Why huntung IoC fails at protecting against targeted attacks
Corporations - the new victims of targeted ransomware

Corporations - the new victims of targeted ransomware
Introducing Man in the Contacts attack to trick encrypted messaging apps

Introducing Man in the Contacts attack to trick encrypted messaging apps
Reverse engineering Swisscom's Centro Grande Modem

Reverse engineering Swisscom's Centro Grande Modem
Easy public-private-keys-strong-authentication-using-u2 f

Easy public-private-keys-strong-authentication-using-u2 f
Create a-strong-two-factors-authentication-device-for-less-than-chf-100

Create a-strong-two-factors-authentication-device-for-less-than-chf-100
Offline bruteforce attack on wi fi protected setup

Offline bruteforce attack on wi fi protected setup
App secforum2014 andrivet-cplusplus11-metaprogramming_applied_to_software_obf...

App secforum2014 andrivet-cplusplus11-metaprogramming_applied_to_software_obf...
Warning Ahead: SecurityStorms are Brewing in Your JavaScript

Warning Ahead: SecurityStorms are Brewing in Your JavaScript
Killing any security product … using a Mimikatz undocumented feature

Killing any security product … using a Mimikatz undocumented feature
