Recommended
More Related Content
What's hot
What's hot (18)
Securing Mobile & Online Identity in the Cyber World

Securing Mobile & Online Identity in the Cyber World
Domain 4 of CEH V11: Network and Perimeter Hacking

Domain 4 of CEH V11: Network and Perimeter Hacking
Pentesting Your Own Wireless Networks, June 2011 Issue

Pentesting Your Own Wireless Networks, June 2011 Issue
Similar to Firewall
Similar to Firewall (20)
What is a Firewall_ The Different Firewall Types.pptx

What is a Firewall_ The Different Firewall Types.pptx
Recently uploaded
31 ĐỀ THI THỬ VÀO LỚP 10 - TIẾNG ANH - FORM MỚI 2025 - 40 CÂU HỎI - BÙI VĂN V...

31 ĐỀ THI THỬ VÀO LỚP 10 - TIẾNG ANH - FORM MỚI 2025 - 40 CÂU HỎI - BÙI VĂN V...Nguyen Thanh Tu Collection
Faculty Profile prashantha K EEE dept Sri Sairam college of Engineering

Faculty Profile prashantha K EEE dept Sri Sairam college of EngineeringSri Sairam College Of Engineering Bengaluru
Mattingly "AI & Prompt Design: Large Language Models"

Mattingly "AI & Prompt Design: Large Language Models"National Information Standards Organization (NISO)
Team Lead Succeed – Helping you and your team achieve high-performance teamwo...

Team Lead Succeed – Helping you and your team achieve high-performance teamwo...Association for Project Management
Recently uploaded (20)
Unraveling Hypertext_ Analyzing Postmodern Elements in Literature.pptx

Unraveling Hypertext_ Analyzing Postmodern Elements in Literature.pptx
31 ĐỀ THI THỬ VÀO LỚP 10 - TIẾNG ANH - FORM MỚI 2025 - 40 CÂU HỎI - BÙI VĂN V...

31 ĐỀ THI THỬ VÀO LỚP 10 - TIẾNG ANH - FORM MỚI 2025 - 40 CÂU HỎI - BÙI VĂN V...
Man or Manufactured_ Redefining Humanity Through Biopunk Narratives.pptx

Man or Manufactured_ Redefining Humanity Through Biopunk Narratives.pptx
MS4 level being good citizen -imperative- (1) (1).pdf

MS4 level being good citizen -imperative- (1) (1).pdf
Faculty Profile prashantha K EEE dept Sri Sairam college of Engineering

Faculty Profile prashantha K EEE dept Sri Sairam college of Engineering
Mattingly "AI & Prompt Design: Large Language Models"

Mattingly "AI & Prompt Design: Large Language Models"
Team Lead Succeed – Helping you and your team achieve high-performance teamwo...

Team Lead Succeed – Helping you and your team achieve high-performance teamwo...
Q-Factor HISPOL Quiz-6th April 2024, Quiz Club NITW

Q-Factor HISPOL Quiz-6th April 2024, Quiz Club NITW
Q-Factor General Quiz-7th April 2024, Quiz Club NITW

Q-Factor General Quiz-7th April 2024, Quiz Club NITW
Using Grammatical Signals Suitable to Patterns of Idea Development

Using Grammatical Signals Suitable to Patterns of Idea Development
Mental Health Awareness - a toolkit for supporting young minds

Mental Health Awareness - a toolkit for supporting young minds
Firewall
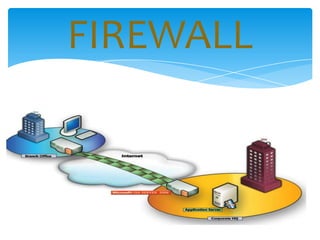
- 1. FIREWALL
- 2. FEATURES OF FIREWALL Network Policy Advanced Authentication Mechanism Packet Filtering Application Gateways
- 3. NETWORK POLICY In order to implement network policy , an organization can issue rules such as , only one computer from the entire network is allowed to establish an ftp connection i.e. to download some content we have to visit that one particular computer.
- 4. ADVANCED AUTHENTICATION While running an application you might be required to enter a user id and password. This help to ensure that malicious programs does not harm your devices, if you are confident about that application you can ask for the combination of id and password by the network admin.
- 5. PACKET FILTERING Packets received by the firewall are analyzed against a database of trusted resources, if verified than they are allowed through otherwise annoying message appears on the screen. Some firewall also logs such request with your IP and you may be later questioned about your intentions while making such request
- 6. APPLICATION GATEWAYS Popularly known by the name of application proxy or application level proxy the proxy establishes the connection with the destination behind the firewall and acts on behalf of the client, hiding and protecting individual computers on the network behind the firewall.
- 7. FIREWALL CAN SAVE US FROM Remote login Application backdoors SMTP session hijacking Operating system bugs Denial of service E-Mail bombs Spam Source routing
- 8. WHAT IT CAN’T DO Can’t protect you against malicious insiders Can’t protect you against connections that don’t go through it like TOR. Can’t protect against completely new threats.
- 9. CONCLUSION In order to protect ourselves from all the threats, we actually have to block everything, but that rules out logic of having an internet connection. Hence the proper way is to block everything and then allow what we need resulting in the need for a good network administrator who completely understands the need of an organization.