Adequate securitynew1404.019
•Descargar como PPTX, PDF•
1 recomendación•569 vistas
Denunciar
Compartir
Denunciar
Compartir
Recomendados
Más contenido relacionado
La actualidad más candente
La actualidad más candente (20)
An Intro to Resolver's InfoSec Application (RiskVision)

An Intro to Resolver's InfoSec Application (RiskVision)
Cybersecurity Disrupters and Cybersecurity Insurance in the COVID-19 Era – Is...

Cybersecurity Disrupters and Cybersecurity Insurance in the COVID-19 Era – Is...
Integrating Cybersecurity into Supply Chain Risk Management

Integrating Cybersecurity into Supply Chain Risk Management
The Measure of Success: Security Metrics to Tell Your Story

The Measure of Success: Security Metrics to Tell Your Story
Similar a Adequate securitynew1404.019
This presentation from the NTXISSA June 2015 Lunch and Learn meeting covers: “Survival in an evolving threat landscape” and “How to talk security in the boardroom”Luncheon 2015-06-18 Security Industry 2.0: Survival in the Boardroom by David...

Luncheon 2015-06-18 Security Industry 2.0: Survival in the Boardroom by David...North Texas Chapter of the ISSA
Similar a Adequate securitynew1404.019 (20)
Aceds 2015 Cyberseucity and the Legal Profession - NYC - April 7, 2015

Aceds 2015 Cyberseucity and the Legal Profession - NYC - April 7, 2015
Stay Ahead of Threats with Advanced Security Protection - Fortinet

Stay Ahead of Threats with Advanced Security Protection - Fortinet
Luncheon 2015-06-18 Security Industry 2.0: Survival in the Boardroom by David...

Luncheon 2015-06-18 Security Industry 2.0: Survival in the Boardroom by David...
Enterprise under attack dealing with security threats and compliance

Enterprise under attack dealing with security threats and compliance
ION-E Defense In Depth Presentation for The Institiute of Internal Auditors

ION-E Defense In Depth Presentation for The Institiute of Internal Auditors
Cyber Attacks aren't going away - including Cyber Security in your risk strategy

Cyber Attacks aren't going away - including Cyber Security in your risk strategy
The Journey to Cyber Resilience in a World of Fear, Uncertainty and Doubt

The Journey to Cyber Resilience in a World of Fear, Uncertainty and Doubt
Focusing on the Threats to the Detriment of the Vulnerabilities

Focusing on the Threats to the Detriment of the Vulnerabilities
Rapid Risk Assessment: A New Approach to Risk Management

Rapid Risk Assessment: A New Approach to Risk Management
How to Simplify Audit Compliance with Unified Security Management

How to Simplify Audit Compliance with Unified Security Management
2015 Global Threat Intelligence Report - an analysis of global security trends

2015 Global Threat Intelligence Report - an analysis of global security trends
Último
💉💊+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHABI}}+971581248768
+971581248768 Mtp-Kit (500MG) Prices » Dubai [(+971581248768**)] Abortion Pills For Sale In Dubai, UAE, Mifepristone and Misoprostol Tablets Available In Dubai, UAE CONTACT DR.Maya Whatsapp +971581248768 We Have Abortion Pills / Cytotec Tablets /Mifegest Kit Available in Dubai, Sharjah, Abudhabi, Ajman, Alain, Fujairah, Ras Al Khaimah, Umm Al Quwain, UAE, Buy cytotec in Dubai +971581248768''''Abortion Pills near me DUBAI | ABU DHABI|UAE. Price of Misoprostol, Cytotec” +971581248768' Dr.DEEM ''BUY ABORTION PILLS MIFEGEST KIT, MISOPROTONE, CYTOTEC PILLS IN DUBAI, ABU DHABI,UAE'' Contact me now via What's App…… abortion Pills Cytotec also available Oman Qatar Doha Saudi Arabia Bahrain Above all, Cytotec Abortion Pills are Available In Dubai / UAE, you will be very happy to do abortion in Dubai we are providing cytotec 200mg abortion pill in Dubai, UAE. Medication abortion offers an alternative to Surgical Abortion for women in the early weeks of pregnancy. We only offer abortion pills from 1 week-6 Months. We then advise you to use surgery if its beyond 6 months. Our Abu Dhabi, Ajman, Al Ain, Dubai, Fujairah, Ras Al Khaimah (RAK), Sharjah, Umm Al Quwain (UAQ) United Arab Emirates Abortion Clinic provides the safest and most advanced techniques for providing non-surgical, medical and surgical abortion methods for early through late second trimester, including the Abortion By Pill Procedure (RU 486, Mifeprex, Mifepristone, early options French Abortion Pill), Tamoxifen, Methotrexate and Cytotec (Misoprostol). The Abu Dhabi, United Arab Emirates Abortion Clinic performs Same Day Abortion Procedure using medications that are taken on the first day of the office visit and will cause the abortion to occur generally within 4 to 6 hours (as early as 30 minutes) for patients who are 3 to 12 weeks pregnant. When Mifepristone and Misoprostol are used, 50% of patients complete in 4 to 6 hours; 75% to 80% in 12 hours; and 90% in 24 hours. We use a regimen that allows for completion without the need for surgery 99% of the time. All advanced second trimester and late term pregnancies at our Tampa clinic (17 to 24 weeks or greater) can be completed within 24 hours or less 99% of the time without the need surgery. The procedure is completed with minimal to no complications. Our Women's Health Center located in Abu Dhabi, United Arab Emirates, uses the latest medications for medical abortions (RU-486, Mifeprex, Mifegyne, Mifepristone, early options French abortion pill), Methotrexate and Cytotec (Misoprostol). The safety standards of our Abu Dhabi, United Arab Emirates Abortion Doctors remain unparalleled. They consistently maintain the lowest complication rates throughout the nation. Our Physicians and staff are always available to answer questions and care for women in one of the most difficult times in their lives. The decision to have an abortion at the Abortion Cl+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...?#DUbAI#??##{{(☎️+971_581248768%)**%*]'#abortion pills for sale in dubai@
A Principled Technologies deployment guide
Conclusion
Deploying VMware Cloud Foundation 5.1 on next gen Dell PowerEdge servers brings together critical virtualization capabilities and high-performing hardware infrastructure. Relying on our hands-on experience, this deployment guide offers a comprehensive roadmap that can guide your organization through the seamless integration of advanced VMware cloud solutions with the performance and reliability of Dell PowerEdge servers. In addition to the deployment efficiency, the Cloud Foundation 5.1 and PowerEdge solution delivered strong performance while running a MySQL database workload. By leveraging VMware Cloud Foundation 5.1 and PowerEdge servers, you could help your organization embrace cloud computing with confidence, potentially unlocking a new level of agility, scalability, and efficiency in your data center operations.Deploy with confidence: VMware Cloud Foundation 5.1 on next gen Dell PowerEdg...

Deploy with confidence: VMware Cloud Foundation 5.1 on next gen Dell PowerEdg...Principled Technologies
Último (20)
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...

Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
Connector Corner: Accelerate revenue generation using UiPath API-centric busi...

Connector Corner: Accelerate revenue generation using UiPath API-centric busi...
Boost PC performance: How more available memory can improve productivity

Boost PC performance: How more available memory can improve productivity
HTML Injection Attacks: Impact and Mitigation Strategies

HTML Injection Attacks: Impact and Mitigation Strategies
Tata AIG General Insurance Company - Insurer Innovation Award 2024

Tata AIG General Insurance Company - Insurer Innovation Award 2024
TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery

TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery
Deploy with confidence: VMware Cloud Foundation 5.1 on next gen Dell PowerEdg...

Deploy with confidence: VMware Cloud Foundation 5.1 on next gen Dell PowerEdg...
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe

Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe
Why Teams call analytics are critical to your entire business

Why Teams call analytics are critical to your entire business
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
Exploring the Future Potential of AI-Enabled Smartphone Processors

Exploring the Future Potential of AI-Enabled Smartphone Processors
Adequate securitynew1404.019
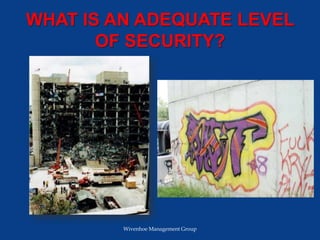
- 1. WHAT IS AN ADEQUATE LEVEL OF SECURITY? Wivenhoe Management Group
- 2. What is an Adequate Level of Security? There is clearly a substantial difference in protecting a facility from persons intent on destroying the infrastructure to those intent on defacing it. Defining that difference is critical Wivenhoe Management Group
- 3. Factors That Determine An Adequate Level of Security 1. Type of Facility 2. Cost 3. Risk Acceptance 4. Insurance Requirements 5. SVA Recommendations 6. Liability Wivenhoe Management Group
- 4. Factors That Determine An Adequate Level of Security 1. Basis of Security Understanding 2. Threat Level 3. Accepted Security Industry Standards & Practice 4. Legal Compliance 5. Environment 6. Incident History 7. Other Wivenhoe Management Group
- 5. Basis of Security Understanding Sandia - Detect, Delay, Respond DHS - Deter, Detect, Delay, Respond Security Industry Experience Keep the Problem Out Deter the Problem Elsewhere Wivenhoe Management Group
- 6. Threat Level Crime Rate Statistics • Homicide • Rape • Robbery • Aggravated Assault • Crimes Against Persons • Burglary • Larceny • Motor Vehicle Theft • Crimes Against Property Wivenhoe Management Group
- 7. Accepted Security Industry Standards & Practices Design Criteria Properly Maintained Equipment Training Manufacturer Authorized Installers Proper Lighting Accepted System Design Current Software & Firmware Wivenhoe Management Group
- 8. Accepted Security Industry Standards & Practices As Built Drawings Response Time to System Failure Back-Up Power Systems Meeting Federal & Local Codes Minimum Video Recording Time Schedules Identifying Types & Quantities of Security Panels Wivenhoe Management Group
- 9. Accepted Security Industry Standards & Practices Due Diligence Related to Contractors Clear Definition of Performance Requirements Required Installation Permits Electric Surge Protection Wivenhoe Management Group
- 10. Legal Compliance • Specific Industry Security Requirements • Data Security Requirements • Physical Security Requirements Wivenhoe Management Group
- 11. Incident History • Five (5) Year History • Type of Incident • Actions Taken • Incident/Serious Breach Wivenhoe Management Group
- 12. Liability • Standard Law Suit • Negligence • Gross Negligence • Repercussions Wivenhoe Management Group
- 13. Environment • Crime Rates • Type of Crime Category • Transportation Hub • Nearby Targets • Sensitive Border • Target Vantage Point Wivenhoe Management Group
- 14. Type of Facility • Hazardous • Strategic Value • Age & Condition • Key Infrastructure • Research Facility • Communication Hub Wivenhoe Management Group
- 15. Cost • Cost, the Leading Factor • Cost, a Double-Edged Sword • Cost, Lowest Bidder • Cost, Technology Changes Wivenhoe Management Group
- 16. Risk Acceptance Higher Risk = Less Cost Lower Risk Safe Choice Difference is Liability Wivenhoe Management Group
- 17. Insurance Concerns Escalating Medical Costs Increasing Value of Assets Ever Present Terrorism Wivenhoe Management Group
- 18. Insurance Requirements UL Certified Alarm System Data Security Compliance Safety Compliance Cyber Crime Prevention Active Shooter Containment Wivenhoe Management Group
- 19. SVA Requirements What is an SVA? Security Vulnerability Assessment Wivenhoe Management Group
- 20. Why Perform An SVA? • Threat Level • Critical Assets • Findings & Recommendations • Federal Grant Funding • Customer Confidence Wivenhoe Management Group
- 21. Why Perform An SVA? • Counter Liability • Phased Solution • Emergency Planning & Response – Active Shooter – Bomb Threat • Measured Response Wivenhoe Management Group
- 22. SUMMARY Basis of Security • Deter Detect Delay Respond • Detect Delay Respond Wivenhoe Management Group
- 23. SUMMARY Many Factors Threat Level Legal Compliance Accepted Standards Environment Incident History Liability Facility Type Risk Acceptance Insurance Cost Security Vulnerability Assessment Wivenhoe Management Group
- 24. SUMMARY More Important Factors Threat Level Liability Facility Type Legal Compliance Wivenhoe Management Group
- 25. QUESTIONS Questions can be sent to: David McCann Principal Consultant Wivenhoe Management Group dmccann@wivenhoegroup.com www.wivenhoegroup.com Wivenhoe Management Group
