Journalism toolkit
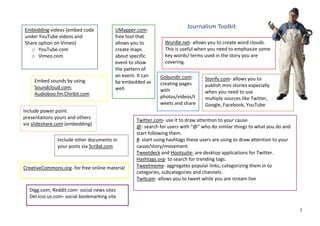
- 1. Embedding videos (embed code UMapper.com- Journalism Toolkit under YouTube videos and free tool that Share option on Vimeo) allows you to Wordle.net- allows you to create word clouds. o YouTube.com create maps This is useful when you need to emphasize some o Vimeo.com about specific key words/ terms used in the story you are event to show covering. the pattern of an event. It can Gobundlr.com- Embed sounds by using Storify.com- allows you to be embedded as creating pages Soundcloud.com; publish mini stories especially well. with Audioboo.fm;Chirbit.com when you need to use photos/videos/t multiple sources like Twitter, weets and share Google, Facebook, YouTube Include power point presentations yours and others Twitter.com- use it to draw attention to your cause. via slideshare.com (embedding) @- search for users with “@” who do similar things to what you do and start following them. Include other documents in #- start using hashtags these users are using to draw attention to your your posts via Scribd.com cause/story/movement. Tweetdeck and Hootsuite- are desktop applications for Twitter. Hashtags.org- to search for trending tags. CreativeCommons.org- for free online material Tweetmeme- aggregates popular links, categorizing them in to categories, subcategories and channels. Twitcam- allows you to tweet while you are stream live Digg.com; Reddit.com- social news sites Del.icio.us.com- social bookmarking site 1
- 2. Online Security Bypass proxies for blocked sites: HTTPS- by adding “s” to the usual “http” - anonymouse.org- to access blocked blogs (hypertext transfer protocol) you can access - ninjacloak.com- hides your IP when browsing blocked sites and encrypt traffic between online and access websites anonymously your PC and the site - publicproxyserver.com- to access blocked websites TORproject.org- free software that protects users from Ultrasurf- free proxy tool for Windows. It can open surveillance.Its free to download. If blocked or for some most of blocked websites. reason not accessible in your country use:www.torproject.org/mirrors.html.en; Bypass proxies can also be used to protect your IP http://tor.cybermirror.org; http://tor.zdg-gmbh.eu; address. http://tor.anonymity.cn Firefox and Google Chrome especially if used in “incognito mode” too can keep you safe from hackers. Orbot- is an application for androids and other smart phones to access web, do instant messaging and e- For maximum secure online browsing: mail without being monitored or blocked by mobile - block all cookies internet service provider. Its similar to TOR but for - disable search savings mobile. - disable login information storage Orweb- works with Orbot to provide access to bypass - block all pop- ups web filters and firewalls. You can stay anonymous - disable location tracking with Orweb. It keeps no local history, disable flash, Use cached pageswhen accessing blocked pages- this allows and safe from malicious content you to retrieve copy of a blocked page from search engine (https://github.com/guardianproject/orweb). server rather than the blocked site itself . 2
- 3. Gmail: - access your gmail account directly from https://mail.google.com - https://m.gmail.com- if accessing via mobile phone - Gmail uses “HTTPS”- secure connection which keeps your messages encrypted - Refer to Gmail’s Security Center for complete checklist - Check when you logged in to your account by scrolling to the bottom of your page- you will see IP addresses - Always sign out especially if on public computer Hushmail.com- secure e-mail service that encrypts all your correspondence.Similar to Gmail. 3
- 4. Useful online resources Onorobot.org/en- online digital activism tool neworganizing.com/toolbox/newmedia- how to use new media in organizing and reaching out to Howtobypassinternetcencorship.org- reports on online people security and more and it is available in Spanish http://marianne-elliott.com/category/top-tips- Newtactic.org- this is a database to human rights tactics for-zen-peacekeepers/zen-peacekeeper-guide- to-twitter/-zen peacekeeping guide to twitter Yourfreedom.net- free software for bypassing firewall and filtering http://www.rsf.org/rubrique.php3?id_rubrique= 542-Reporters Without Borders, Handbook for Guardianproject.info Cyber- Dissidents and Bloggers Digital-democracy.org- website with resources on Opennet.net- website that documents internet technology for democracy building, improving human censorship worldwide rights. Movements.org- an extensive website with Tacticaltech.org resources for activists, support and more Diaspora- social network for activists IREvolution.net- personal blog by Patrick Meier on resistance through digital means Security.ngoinabox.org- website with resources and how- to guides to online security, internet privacy for Truthout.com activists and media 4
- 5. Few useful notes Authentic journalist’s strategy for covering a planned action Use Google to learn about search optimization: or event: title is important and especially the first word (adwords.google.com) 1. Know what the action will look like. Highlight certain words in bold (Ex: war on drugs) 2. Understand the goal of the action. Continuity (keep updating; keep tweeting- its 3. Understand the larger aims of the useful to share same links often) movement/organization. Timing- when you post material online (after 7AM 4. Determine the audience of your coverage based on and before 11PM) numbers 2 and 3. Meta tags 5. Identify which types of messages/stories will speak to (http://support.google.com/webmasters/bin/ans your audience. wer.py?hl=en&answer=79812) 6. Select the media tools that you will use for documenting the action and amplifying the stories. 5
