Healthcare Information Security: A Focus on Prevention | Dell SecureWorks
- 1. 38 Fall 2012 Volume 26 / Number 4 www.himss.org n n FOCUS HITECH—Privacy & Security Issues Healthcare Information Security A Focus on Prevention Is the Best Remedy for Medical Record Breaches By Keith Tyson and Robert Slocum Abstract With the implementation of basic controls and measures, however, healthcare organizations can effectively reduce Between 2009 and 2011, more than 18 million patients’ the majority of their risk. A critical first step toward building Protected Health Information (PHI) was compromised.2 a robust security program is conducting a comprehensive Over the past year alone, healthcare breaches in the United risk assessment, along with implementing stronger controls States have increased by 32 percent.3 As these numbers and cost-effective technologies. This paper explores the clearly show, securing medical information is one of the trends driving the need for more comprehensive security most pressing issues facing hospitals and other healthcare programs while continuing to embrace new technology, organizations. However, a 2012 report from the American and why an approach that incorporates factors such as National Standards Institute notes, a lack of resources mobile devices is critical for positive change throughout the and leadership support have made it hard for many healthcare security ecosystem. By laying a solid foundation organizations to effectively protect such data.1 In recent Dell for security that includes visibility into an organization’s SecureWorks roundtables with health IT executives, almost vulnerabilities, encryption, endpoint access security, mobile all participants personally knew of an organization that had device strategies and security risk monitoring, healthcare experienced a PHI (protected health information) breach. organizations can effectively address malware risk and data Several admitted to experiencing a breach themselves in loss, enable better response to a threat environment that the past year. As responses at these roundtable events is rapidly evolving, and more efficiently meet compliance indicate, health IT executives are very aware of security requirements. concerns, but many obstacles make it difficult for them to seamlessly implement a security program that works on both a technical and human level.This challenge creates a Keywords “perfect storm” of risk, resulting in penalties and fines that Healthcare data security, information security, healthcare have already exceeded $1.5 million per facility, per breach.4 compliance, healthcare data management, data breach Experts estimate that costs to the healthcare industry could management, HIPAA security compliance, mobile device total more than $6.5 billion per year.5 security, managed security.
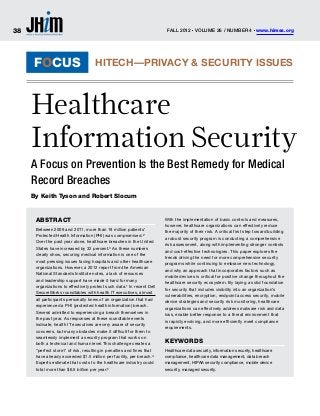
- 2. www.himss.org Fall 2012 Volume 26 / Number 4 n n 39 focus: healthcare Information Security H ealthcare data security and response measures, without the need care providers had at least one data breach has become a primary con- to pursue increasingly sophisticated tech- in the past two years,10 and Information cern for firms of all types, nologies. Week reported that two of the top six data from providers and business breaches of 2011 were healthcare-related.11 partners, to clinical research organiza- The Risk Landscape This trend is likely occurring because 69 tions. Within a “perfect storm” of looming It is no secret that healthcare has faced percent of hospitals do not have the proper federal audits, new penalties under the increasing risks to PHI, relative to other policies and controls to detect and respond Meaningful Use incentive program, and industries. These risks are driven partially to breaches.12 risk of public exposure resulting from the by the adoption of electronic health records Ironically, despite incentives for imple- federal Breach Notification Rule, organi- (EHR), and increasing interconnectedness menting secure EHRs, and the growing zations that have not properly planned within and among institutions through disincentives for maintaining the status for and understood security risks are fac- the adoption of mobile devices and the quo, healthcare leaders have yet to allocate ing increased public scrutiny. However, rollout of health information exchanges. significant capital budgets to security ini- in the barrage of priorities, security often The incentives for healthcare companies tiatives. Of eight major industries, health- takes second place to issues such as bud- to rapidly adopt EHRs are in place, as are care organizations spend by far the least get concerns and patient care initiatives. disincentives for losing sight of data secu- per employee on security. The financial In Dell-moderated, security-focused dis- rity in the process. industry spends more than six times per cussions with health IT leaders, partici- In fact, the American Recovery and employee on security than do healthcare pants conveyed an environment in which Reinvestment Act of 2009 (ARRA) has organizations.13 When this spending is the magnitude of threats is difficult to breathed unprecedented life into the quest compared to the overall costs of a breach,14 assess. A number of participants also for electronic information, with providers healthcare again lands at the bottom rung expressed concern about the low level eligible to receive up to $27 billion overall of the preparedness ladder (Figure 1). of commitment in their organizations in incentive funds for the meaningful use This indicates that not only are health- to improving information security, and of EHRs.7 In addition to the incentives, care providers reluctant to spend money several said that management and clinical healthcare providers also could face reduc- on security; they are one of the industries leaders were often at odds on the issue.6 tions in Medicare reimbursement if they do that would ideally spend the most to gain Developing an effective and efficient not comply with the legislation’s Meaning- a firm security posture based on a higher defense against external and internal ful Use standards by 2015. risk profile than most industries. attacks requires a high level of situational Despite these incentives, more than 18 To gain a broader perspective on these awareness and comprehensive controls. million patients’ records were breached risks, Dell conducted focus groups with The attacks themselves have become between 2009 and 2011,8 with an increase more than 100 health IT executives to learn increasingly sophisticated and evolved, of 32 percent from 2010 to 2011; which could the most prevalent and concerning threats with increased points of entry for hackers, be costing the healthcare industry an aver- they face. Almost all participants were per- but there are simple and powerful steps age $6.5 billion per year.9 More unsettling, sonally acquainted with an organization healthcare organizations can take to greatly a December 2011 study from the Ponemon that has had a breach of ePHI, and some said minimize the magnitude of these risks. By Institute indicated that 96 percent of health- they had experienced a breach themselves in conducting periodic risk assessments, enabling endpoint access security, devel- Figure 1: Spending Compared to the Overall Costs of a Breach oping a monitoring and security mitigation plan, and implementing a mobile device Security Spend Breach Costs per Spend/Cost strategy, healthcare companies can help per Employee* Employee** protect themselves against the vast major- Financial $904 $247 366% ity of the threats they face, and for far less Professional Services $665 $185 359% than the cost of an average breach. A critical starting point for effective Communications $995 $334 298% * Source: Gartner, IT security is visibility—visibility into where Education $298 $142 210% Metrics Data 2012: data resides, and visibility into what the Key Information Transportation $308 $196 157% Security Measures – real risks are. Stronger controls and cost- by Industry (12-2011) effective technologies, if integrated into Retail $253 $174 145% ** Source: Ponemon, an organization’s core operational expen- Industrial $237 $235 101% Cost of a Data diture investments, can also provide rela- Breach Study (2011) Healthcare $145 $240 60% (US only) (03-2012) tively inexpensive protection of the data perimeter and beyond, and address risk Last on List Top-3
- 3. 40 Fall 2012 Volume 26 / Number 4 www.himss.org n n focus: healthcare Information Security A critical first step toward building a robust security program is conducting a comprehensive risk assessment, along with implementing stronger controls and cost-effective technologies. the past year. As responses at these round- itself (and not the data on the device); but other industries. Healthcare organizations table events indicate, awareness of security once the device is stolen, the repercussions are viable testing platforms for “proof of concerns is high, but many obstacles make are similar, regardless of the intent. concept” attacks, due to the general lack of it difficult to seamlessly implement a secu- The external threat landscape, however, effective controls and high state of vulner- rity program that works on both a techni- is also a force with which to be reckoned, ability throughout their networks. cal and human level. The typical approach and presents its own unique set of challeng- Organizations can protect against both is primarily symptomatic and reactionary. es for the IT security professional. Recent common and advanced threats by gaining Frameworks, if they are adopted, are often attacks perpetrated against many indus- situational awareness, and forming defen- an incomplete work in progress. tries are highly sophisticated, well orga- sive strategies around the risk posture Event participants noted that they typi- nized, and often are connected to nation- that exists. Although a foundation for this cally spend less time evaluating new solu- state activities or cyber-crime organizations awareness starts with risk assessments, tions than they do trying to plug holes around the globe. The actors behind these implementing effective network architec- in existing systems, while struggling to attacks are sometimes not motivated as ture, along with penetration testing and maintain visibility into emerging advanced much by recognition or fame, as they are by continuous monitoring are also necessary threats and other malware risks. Hospitals monetary, political or ideological objective. components of a security program. Plan- have difficulty keeping common malware One of the most insidious types of attacks ning for these events and the organization’s out of their networks, but ironically, they is advanced persistent threats (APT), a anticipated response on a continual basis frequently de-prioritize security due to a genre with generally malicious intent that makes it much more difficult for malware perceived immunity to breaches. While greatly compounds the risks inherent in actors to conceal their actions, and will health organizations may have a security EHRs. This type of attack represents an make incident response efforts more effec- strategy, they are typically limited in scope. evolving threat to many organizations’ tive, both for internally- and externally- intellectual property, financial assets, and based threats. Internal vs. External Threats ultimately, their reputations. APT actors Although the risks facing healthcare orga- (the adversaries guiding the attack) target Data Visibility nizations surface from both internal and specific organizations for a singular pur- and Risk Assessments external sources, internal threats have pose, and attempt to gain a foothold in Gaining visibility into where data resides historically been the most common, with a the target’s environment, often through is a critical starting point to developing a reported 49 percent of breaches occurring tactics such as targeted emails, or “spear- robust security strategy, and is the basis due to lost or stolen devices and laptops.15 phishing,” that contain malicious web links for the completion of a comprehensive The prominent media image of a healthcare or attachments designed to compromise a risk assessment. Conducting a risk assess- breach often evokes the occasional rogue particular computer. The attackers then ment as a foundation for IT strategy helps employee who steals information and typically use the compromised systems as the organization meet compliance require- sells it on the black market. In fact, most a conduit into the target network and as a ments such as HIPAA and Meaningful Use, healthcare security incidents result from method to deploy additional tools that help but is also a substantial step in creating the more mundane and unintended causes, fulfill their primary objectives. Dell Secure- capability to react to and mitigate the dam- such as the accidental loss or theft of laptop Works’ Counter Threat Unit has found that age from breaches. These breaches, unfor- computers or mobile devices: a clinician or the healthcare industry is particularly vul- tunately, are an increasing likelihood with employee leaves a laptop or mobile device nerable in recent months, with many of the the proliferation of EHR implementations on a train during their evening commute; most prevalent malware tools used by hack- and recent spikes in device usage. Having or a thief steals an employee’s computer ers (Figure 2). This may be partially due to a comprehensive picture of where data is, bag from the backseat of her car. Situations the attackers’ strategy of using healthcare how it is used, and who is accessing it goes such as these create an easy opportunity for organizations as a “testing ground” for a long way toward maintaining integrity of thieves whose target may be the hardware malware, before deploying it on targets in patient records, preventing negative press,
- 4. www.himss.org Fall 2012 Volume 26 / Number 4 n n 41 focus: title healthcare Information Security Figure 2: Top 15 Malware by Vertical—May 2012 Source: Dell SecureWorks’ Counter Threat Unit (CTU) analysis and avoiding substantial fines and penal- and the physical facility and surrounding patients can use unsecured personal ties. A risk assessment and analysis is also environment as well. devices to carry or access health informa- the primary starting point for two of the tion (often referred to as the “bring-your- primary concerns in healthcare today— Mobile Device Security own-device,” or BYOD movement), which securing mobile devices and meeting the Simultaneous with the expected growth brings into question the ability to consis- Stage I security requirement for meaning- of EHRs is the rapid emergence of mobile tently enforce security controls such as ful use of EHR. devices such as smartphones and tablets. encryption, and track access to appropriate Organizations participating in the EHR The proliferation of such tools indicates data. The unforeseen consequences from Meaningful Use program already have a that many of the “test flights” for EHRs will this can be significant. In recent months compelling incentive to conduct or update be driven by these devices, which combine for instance, a US health insurance firm a security risk analysis, since this is a core potential improvements with new risks. lost 1.5 million clients’ medical records on requirement of both Meaningful Use and The widespread use of portable media, an unencrypted portable drive. This deci- the original HIPAA Security Rule. Howev- smartphones, and tablet computers cre- sion to save money on encryption expenses er, simply pushing the organization to meet ates an urgent need for attention to how resulted in $250,000 fielding lawsuits, more Meaningful Use with the singular goal of col- and where sensitive data is sent within (and than $319,000 in letters to the affected cli- lecting incentive payouts does not prepare outside of ) the provider’s networks. ents, and $1 million for identity theft moni- the organization for inevitable future audits A changing relationship with how and toring services to the victims.20 Although and to mitigate the additional risks posed by where physicians, clinicians, insurers, and BYOD can be a beneficial recruiting tool online data access, mobile devices, health billers access information is complicating and can enable an organization to lower its information exchanges, accountable care the list of vulnerabilities that providers face. IT acquisition costs, the risks inherent in organizations, increased abilities of hackers, Handheld devices are particularly notable this trend (taken without adequate controls and the increased demands from macroeco- because these devices put more power in in place) cannot be overstated. nomic trends such as aging of the population. the palm of the hand today than a desktop The damage from breaches due to mobile There are fundamental components of PC had just a few years ago.16 Moreover, devices also costs the most to repair. A stan- any assessment that healthcare organiza- clinicians have taken notice: more than 70 dard USB drive can store more than 25,000 tions need to consider to address these percent of U.S. physicians now use smart- medical records, and losing just one such emerging risks: understanding what con- phones, up from just 30 percent of physi- device can cost an organization more than trols are currently in effect, determining cians in 2001.17 In addition, some 39 percent $5.7 million in breach mitigation costs.21 the impact of likely events from viruses to of Chief Medical Information Officers have On average, each record breached involv- natural disasters, and documenting expo- rolled out mobile computers or handhelds ing a mobile device can amount to $258 sures and vulnerabilities; not only in sys- at their facilities (as of 2011)18, and 86 per- in mitigation costs, which is higher than tems, but also in processes. A healthcare cent of physicians express that their top the costs associated with other causes of organization’s assessment program should interest in mobile technology is for access- breaches.22 When considered in the con- consider the controls that are implemented ing electronic medical records.19 text that hard drives can carry and manage to safeguard the systems and information, In many cases, both employees and more data with each passing year, there is
- 5. 42 Fall 2012 Volume 26 / Number 4 www.himss.org n n focus: healthcare Information Security a clear imperative to implement a strategy uously move toward adoption of electronic impacting the system’s performance or for each device that touches the organiza- medical records. Compliance officers and patient record access speed. tion’s network. IT staffs are challenged with giving clini- To fully manage security in a mobile cians single-sign-on for immediate access Data Center environment, organizations need to ask to patient records, while simultaneously and Networking Security themselves several key questions to gain keeping the data secure. Single-sign-on As another layer of defense, data center and insight into who is accessing their data capabilities allow for seamless session network security solutions directly address and what types of controls are in place. transfer, which improves the speed of malware. Malware is typically presented They also must consider information access to patient records, while reducing in three various forms, or vectors: inter- security best practices as a part of the the risk posed from unauthorized employ- nal web threats, external web threats, and overall mobile technology and security ees accessing patient data that they may not spam and virus via email attachments. strategy. For instance, both enterprise- have a need to view. The end goal of malware actors is typi- integrated mobile devices and employee- An example of endpoint management is cally to entice a victim to click on a link or patient-owned mobile devices need Dell’s Mobile Clinical Computing solution, or website which contains malware, and to be as secure as possible with identity which uses client virtualization – a solu- can subsequently allow the actor entry authentication, encryption, tracking and tion that removes data including ePHI from to the data center and network; either to trace software, anti-malware, backup and endpoint devices. Coupled with single- extract financial or patient data for mon- extensive monitoring. sign-on capabilities, solutions such as this etary gain, or for other purposes in the Access controls must be implemented to allow clinicians to move from their office, case of advanced threats. Next Generation keep data safe in the mobile environment. then to a nursing station or a patient room, Firewalls and Web Application Firewalls The original HIPAA rule called for granting while logging onto devices via a card reader, can help shield the network and servers role-based access procedures. But as mobile facial scan, or thumb reader. Upon logging from external attacks; and intrusion pre- device usage has required identities and on, the record or image follows the clinician vention systems can bolster this defense. privileges to be stored in multiple applica- virtually, while automatically logging them As an added layer of defense, installing a tions and repositories across the enterprise, off any other systems onto which they may web filter can enable the organization to many current systems may have deficiencies have been logged. With each endpoint or monitor the network and protect internal in this area. A centralized and comprehen- “thin client” being virtualized, there are no employees from picking up malware while sive view of people, views, roles, and privi- data or patient records residing on an indi- browsing the internet. Anti-virus and anti- leges is necessary to enable more accurate vidual client device. The endpoints in these spam gateways can also provide protection and efficient auditing and reporting. cases are simply “gateways” to data. If an from email-based attacks while providing Another critical challenge in keeping employee walks out with a laptop or thin an overall boost to performance by allow- mobile devices secure is the threat posed by client, there is no data loss; and without ing the organization to reduce the volume of personal applications for social media and logon credentials, there is no way for them email traffic consisting of spam messages. games, which are often installed directly to access the medical records. adjacent to work applications. To address For those systems that do contain Continuous Monitoring this risk, a “container approach” to applica- records or data, encryption is necessary. Since the volume and sophistication of tion development and deployment is neces- Historically, encryption was performed at malware is rising, it is imperative that sary in order to separate the high-risk per- the hard drive layer, subsequently slowing healthcare organizations block threats sonal applications from work applications down the workstation or server, which in across all communication layers—from the on the same device. turn impeded physicians from expediently network to e-mail to applications. A solid Remote wiping capability, another com- accessing medical records. As backlash platform for these appliances will provide mon requirement among mobile device ensued, IT managers often turned off labs to monitor and protect the organization users, allows organizations to address the encryption completely to assuage the against the current threats, but that protec- those instances where work applications problems with patient data access. Even tion is limited to that particular appliance. residing on an individual’s mobile device those who did not disable encryption When evaluating their overall security need to be erased without affecting their were still exposed to breaches at the USB strategy, many healthcare organizations personal applications; thus eliminating ports and optical drives. Today, encryp- scrutinize their budgets and try to fund an potential threats when a device is lost or tion methods have evolved, and afford- internal information security staff to exam- an employee leaves the organization. able systems are available that meet the ine current threats, monitor all the endpoint stringent FIPS 140-2 level-three encryp- devices on a network, and monitor all of the Endpoint Access and Encryption tion standards at the system level. These security appliances running in front of their Endpoint security has become a larger advancements encrypt the entire system, data center, in the hopes of staying ahead of imperative as healthcare providers contin- including USB and optical drives without evolving threats.
- 6. www.himss.org Fall 2012 Volume 26 / Number 4 n n 43 focus: title HEAlTHcArE INfOrmATION SEcUrITy A new approach to security is to imple- pursuit. Instead of simply reacting to the references ment outside security monitoring. Moni- call for compliance or the need to prevent 1. American National Standards Institute. The toring services such as Dell SecureWorks or respond to a breach, healthcare leaders financial Impact of Breached Protected Health enable healthcare organizations to assess should adopt a more holistic approach. Information: A Business case for Enhanced PHI Security. 2012. security across the enterprise, from onsite Along with a stronger alignment between 2. http://www.ama-assn.org/ access endpoints to mobile solutions, where administration, IT, and clinicians, more amednews/m/2012/04/02/bsf0405.htm their current and future infrastructure are automation and better tools are necessary 3. Second Annual Benchmark Study on Patient continuously examined and disaster plans to manage a threat landscape that evolves at Privacy & Data Security. Ponemon Institute, December 2011 are created. Services such as these couple an ever-faster clip with each passing year. 4. http://www.healthdatamanagement.com/ risk assessments with threat monitoring, Despite the introduction of new and news/breach-notification-hipaa-privacy- and enable the organization to scale its varied threats with each passing month, security-tennessee-44181-1.html security efforts, and monitor risks across healthcare providers can cost-effectively 5. Second Annual Benchmark Study on Patient Privacy & Data Security,” Ponemon Institute, the entire network. Real-time threat man- manage security with a layered approach December 2011 agement keeps the organization secure, that includes conducting risk assess- 6. http://www.secureworks.com/assets/ helps to meet compliance requirements, ments, managing mobile devices, apply- pdf-store/articles/healthcare_data_security_ landscape_2012.pdf and allows the organization to focus bud- ing encryption and endpoint controls, 7. http://healthit.hhs.gov/portal/server. gets on those activities that deliver infor- implementing data center and network pt?open=512&mode=2&objID=3541 mation-driven healthcare and enhance core security controls, and implementing con- 8. http://www.ama-assn.org/ patient care activities. tinuous monitoring. Using this approach, amednews/m/2012/04/02/bsf0405.htm In the quest to improve patient out- healthcare organizations enable them- 9. Second Annual Benchmark Study on Patient Privacy & Data Security,” Ponemon Institute, comes, organizations need to embrace new selves to focus their human capital and December 2011 innovations. As the cloud has continued core resources on pursuing and manag- 10. Ibid. to mature, more hospitals are embracing ing innovation that furthers the mission 11. http://www.informationweek.com/news/ a cloud strategy to managing their data. of improving patient outcomes. jhim security/attacks/232301079 12. http://www2.idexpertscorp.com/press/ This is evident in medical imaging, as new-ponemon-institute-study-finds-data- healthcare organizations aspire to remove Keith Tyson is a healthcare industry consultant breaches-cost-hospitals-6-billion/ data silos, manage the data explosion that with Dell secureWorks. He has over 12 years of 13. Gartner. IT Key metrics Data 2012: Key Information Security measures – by industry is driving health information exchanges experience managing medical supplies development (12-2011) and effectively confront accountable care and commercialization, oncology program strategy, 14. Ponemon Institute, cost of a Data Breach organizations. To address the evolution in software innovation and development, and providing Study (2011) (US only) (03-2012) data exchange and sharing, organizations thought leadership to the data security community. 15. http://www.informationweek.com/news/ healthcare/mobile-wireless/232601422 are recognizing that there is tangible value He is a frequent blogger, writer, and speaker for Dell 16. http://bits.blogs.nytimes.com/2011/10/12/ in coupling disaster recovery mechanisms on security issues facing healthcare organizations. cell-phones-are-servers-and-servers-are-cell- with geographically separated data centers, He holds an MBA from emory University. phones/ along with fully integrated and around-the- 17. manhattan research, “Taking the Pulse” research report 2011. clock security coverage. Robert Slocum is a sales and marketing 18. http://mobihealthnews.com/7985/cmios- professional with an extensive history leading, 39-percent-have-installed-mobile-devices/ concLusion managing, coaching, marketing and selling in 19. Pricewaterhousecoopers Health research A changing relationship with how and the high-tech, medical and financial industries. Institute report: “Healthcare Unwired,” September 2010. where physicians, clinicians, and billers slocum currently works in Dell’s Healthcare and 20. http://www.forbes.com/sites/ access information is complicating the list life sciences group, helping customers to meet it dell/2011/09/22/mobile-devices-in-healthcare/ of vulnerabilities that exist in the world of security, networking security, data protection and 21. Ibid.; SecureWorks research. healthcare data management. In an envi- enterprise storage solutions. slocum graduated cum 22. HITrUST Alliance. An Analysis of Breaches Affecting 500 or more Individuals in Healthcare. ronment where many security decisions laude from concordia University. are made based on compliance-driven and reactionary motives, organizations risk fighting an uphill battle to stay ahead of current threats, mitigate loss of patient and financial data, and maintain a contin- uous picture of their current state of risk. To more effectively deal with information security in the information age, health- care providers need to make it a strategic
