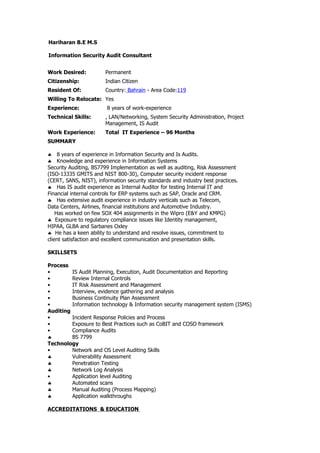
Information Security Audit Consultant
- 1. Hariharan B.E M.S Information Security Audit Consultant Work Desired: Permanent Citizenship: Indian Citizen Resident Of: Country: Bahrain - Area Code:119 Willing To Relocate: Yes Experience: 8 years of work-experience Technical Skills: , LAN/Networking, System Security Administration, Project Management, IS Audit Work Experience: Total IT Experience – 96 Months SUMMARY ♣ 8 years of experience in Information Security and Is Audits. ♣ Knowledge and experience in Information Systems Security Auditing, BS7799 Implementation as well as auditing, Risk Assessment (ISO-13335 GMITS and NIST 800-30), Computer security incident response (CERT, SANS, NIST), information security standards and industry best practices. ♣ Has IS audit experience as Internal Auditor for testing Internal IT and Financial internal controls for ERP systems such as SAP, Oracle and CRM. ♣ Has extensive audit experience in industry verticals such as Telecom, Data Centers, Airlines, financial institutions and Automotive Industry. Has worked on few SOX 404 assignments in the Wipro (E&Y and KMPG) ♣ Exposure to regulatory compliance issues like Identity management, HIPAA, GLBA and Sarbanes Oxley ♣ He has a keen ability to understand and resolve issues, commitment to client satisfaction and excellent communication and presentation skills. SKILLSETS Process • IS Audit Planning, Execution, Audit Documentation and Reporting • Review Internal Controls • IT Risk Assessment and Management • Interview, evidence gathering and analysis • Business Continuity Plan Assessment • Information technology & Information security management system (ISMS) Auditing • Incident Response Policies and Process • Exposure to Best Practices such as CoBIT and COSO framework • Compliance Audits ♣ BS 7799 Technology • Network and OS Level Auditing Skills ♣ Vulnerability Assessment ♣ Penetration Testing ♣ Network Log Analysis • Application level Auditing ♣ Automated scans ♣ Manual Auditing (Process Mapping) ♣ Application walkthroughs ACCREDITATIONS & EDUCATION
- 2. Accreditations ♣ CISSP & CISA ♣ BS 7799 Lead Auditor ♣ BS7799 Lead Implementer ♣ Certified Ethical Hacker -CEH ♣ Certified System engineer -MCSE ♣ CISCO Certified Network Associate - CCNA ♣ Certified Hacking Forensic Investigator -CHFI ♣ Microsoft Certified Systems Professional – MCP Academics ♣ Bachelor of Computer Science Engineering, India (Tamil Nadu) ♣ M .S By Research Information Technology (Thesis work), India(Anna University) Workshops / Trainings attended • IT Audit Best Practices by BSI, India • Application controls Review/Audit by ISACA, Chennai, India • COBIT workshops –Bahrain(ISACA) EMPLOYMENT RECORD •Sr. Information Security Consultant (Audit) EKKANOO B.S.C-Bahrain (Jan 2008 – till date) •Sr. Information Security Consultant Paramount Saudi Arabia-Riyadh (Jan 2007 – Dec 2007) Clients: A. AXA Insurance B. Ministry Of Saudi Arabia-IC C. Riyad Bank D. Saudi Telecom –STC F. Saudi Airways •Information Security Consultant(Band-B2) Wipro Technology (Nov 2005-Dec 2006) Clients: A. AT&T(Lucent Technologies) •Senior Systems Engineer(Trainer) – IT Projects Adept Technologies (April 2002-Oct 2005) Clients: A. Chennai Cyber Crime B. TCS C. Wipro D. Infosys KEY PROJECTS PROJECT - 1 INFORMATION SECURITY RISK ASSESSMENT EKKANOO B.S.C -Bahrain Role IT Security Engineer SUMMARY The engagement includes independent security risk assessment of IT services and critical systems including Billing and systems. The assessment was done using industry best practices and included the following activities. • Risk assessment using BS 7799 standard / GMITS guidelines
- 3. • BS 7799 GAP analysis • Threat analysis • Impact analysis • Vulnerability Assessment • Penetration testing • High Level Risk Assessment for ERP Application systems PROJECT - 2 IS AUDIT CLIENT AXA Insurance , Riyadh Role IS AUDIT CONSULTANT SUMMARY: This engagement included IT internal audit specialist to assist wide risk assessment framework IRM for AXA Insurance . My responsibilities are : •Testing & Documenting the Risk, Expected Control, Actual Controls and Gaps within the IT Process/Application /Application interfaces. Develop Risk and control library for information security discipline •Design Baseline Controls and Controls Assessment after Corporate Risk assessment •Provide Risk and controls matrix for enterprise automated risk assessment and risk reporting •Development of risk control framework and enterprise risk assessment methodology •Compliance assessment on content of Risk Control library for corporate. •GAP analysis of corporate standards with Industry standard regulations such as COBIT, Sarbanes Oxley, ISO 17799, FDIC and GLBA. PROJECT - 3 IS AUDIT SOX COMPLIANCE CLIENT Riyadh BANK, Role IS AUDIT CONSULTANT SUMMARY This engagement included IT internal audit for Sarbanes Oxley/FDICIA regulation. My responsibilities are : •Testing & Documenting the Risk, Expected Control, Actual Controls and Gaps within the IT Process/Application /Application interfaces. •Test the operating effectiveness of general controls like Access control, Change control, Backup, VM, MBS and application controls in Horizon, Advent and other application environments. •Develop narratives for network domain for security controls mapping for general controls. PROJECT - 4 IS AUDIT ( SOX COMPLIANCE) CLIENT STC-RIYADH Role IS AUDIT CONSULTANT SUMMARY This engagement included IT internal audit for Sarbanes Oxley readiness. My responsibilities are : •Develop test plans for IS network area and application areas. •Build detailed audit programs for assisting internal audit teams for management in ERP application security , AS 400, Oracle applications. •Test the operating effectiveness of general controls like Access control, Change control, Backup, and ITGC in Oracle environment. PROJECT - 5 IS AUDIT Testing ( 1X EVDO )
- 4. CLIENT AT & T USA,INDIA Role IT Security Consultant SUMMARY This engagement included IT internal Testing for 1X EVDO Environment regulation. My responsibilities are : •Testing & Documenting the Risk and Gaps within the Application /Application interfaces. •Test the operating effectiveness of general controls like Access control, Change control, Backup, VM, MBS and application controls in 1 x EVDO and other application environments. •Analysis of Infrastructure vulnerabilities with knowledge gained from currently published attack methodologies and exploits •Performance of onsite and remote Penetration tests and vulnerability analysis, •Scanning and using necessary exploit code for testing •Develop narratives for network domain for controls mapping for general controls and network security controls PROJECT – 6 NETWORK INFRASTRUCTURE VULNERABILITY AUDIT CLIENT Ministry of IC -Riyadh Role TEAM LEAD SUMMARY The requirement of the client as to identify their network infrastructure vulnerabilities through onsite and offsite vulnerability testing and penetration testing exercise. As project lead was responsible for •Analysis of Infrastructure vulnerabilities with knowledge gained from currently published attack methodologies and exploits •Performance of onsite and remote Penetration tests and vulnerability analysis, •Scanning and using necessary exploit code for testing •Reporting on vulnerability to various remote and head office sites. •Internal Pen test •Application Audit in Switch Application •Designing IT Security Policies and procedures(Cramm) •Implementation Road Map for Compliance PROJECT – 7 BS 7799:2002 BASED ISMS BUILD CLIENT STC, Riyadh Role TEAM LEAD SUMMARY This engagement involved building an Information Security Management System in accordance with the BS 7799:2002 – Part 2 Specifications for the client. The engagement activity included; •Build ISMS Scope •Risk Assessment Conducted •Review of Internal Controls •Develop Risk Treatment Plan •Statement of Applicability •Internal Control selection •Reviewing and developing Information Security Policies / procedures for the organization as part of an ongoing policy and procedure review. •Regular interaction with client enabling the refinement of policies / procedures over a period of time
- 5. PROJECT – 8 SECURITY POLICY AND PROCEDURE DESIGN CLIENT Saudi Airways-Riyadh Role PROJECT MANAGER SUMMARY Design an enterprise wide information security policies and procedures in accordance with ISO 17799 specifications and implement the security technical controls from Secure Architecture Design. As the project lead, was instrumental in the following activities. •Stakeholder information capture and documents review •Assessment of efficacy of existing controls •Design Secure Architecture •Policy Discussion with business managers •Design of Policy and Procedures •Policy Discussion facilitation •Deployed Implement Defense-in-depth firewall •Deployed Implement enterprise RSA Secur ID Authentication •Deployed Host IDS and Network IDS in critical networks and hosts PROJECT 9 NETWORK SECURITY CLIENT Maruthi Broad Band Pvt Ltd ,India Role PROJECT MANAGER SUMMARY •Design, deploy trader secure information architecture and secure LAN/WAN architecture for customer’s MBB environment and commission treasury networking projects for MBB customers. Network involves VSAT data feeds to backend Sun Solaris application servers with TCP-IP backbone to windows 2000 workstations. •Installation of session firewall server to secure data feeds between MBB and customer private networks. Real-time information systems and dealing 2002 system project management for products and services owned by MBB Group , Chennai. •Securing Sun Solaris and Hardening Windows 2000 servers, Installing, configuring and troubleshooting Firewall based Session services in Linux box were the key responsibilities Contact Information : Mobile: +00973 36438081 / 39366487 Reference : Available on Request