SCADA and Control Systems Security Summit
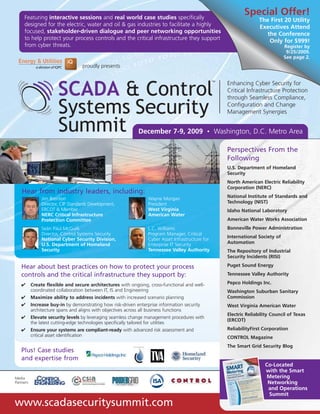
- 1. Hear about best practices on how to protect your process controls and the critical infrastructure they support by: Plus! Case studies and expertise from Media Partners: ✔ Create flexible and secure architectures with ongoing, cross-functional and well- coordinated collaboration between IT, IS and Engineering ✔ Maximize ability to address incidents with increased scenario planning ✔ Increase buy-in by demonstrating how risk-driven enterprise information security architecture spans and aligns with objectives across all business functions ✔ Elevate security levels by leveraging seamless change management procedures with the latest cutting-edge technologies specifically tailored for utilities ✔ Ensure your systems are compliant-ready with advanced risk assessment and critical asset identification www.scadasecuritysummit.com December 7-9, 2009 • Washington, D.C. Metro Area Perspectives From the Following U.S. Department of Homeland Security North American Electric Reliability Corporation (NERC) National Institute of Standards and Technology (NIST) Idaho National Laboratory American Water Works Association Bonneville Power Administration International Society of Automation The Repository of Industrial Security Incidents (RISI) Puget Sound Energy Tennessee Valley Authority Pepco Holdings Inc. Washington Suburban Sanitary Commission West Virginia American Water Electric Reliability Council of Texas (ERCOT) ReliabilityFirst Corporation CONTROL Magazine The Smart Grid Security Blog Featuring interactive sessions and real world case studies specifically designed for the electric, water and oil & gas industries to facilitate a highly focused, stakeholder-driven dialogue and peer networking opportunities to help protect your process controls and the critical infrastructure they support from cyber threats. proudly presents Enhancing Cyber Security for Critical Infrastructure Protection through Seamless Compliance, Configuration and Change Management Synergies Special Offer! The First 20 Utility Executives Attend the Conference Only for $999! Register by 9/25/2009. See page 2. Hear from industry leaders, including: Jim Brenton Director, CIP Standards Development, ERCOT & Member NERC Critical Infrastructure Protection Committee Seán Paul McGurk Director, Control Systems Security National Cyber Security Division, U.S. Department of Homeland Security Wayne Morgan President West Virginia American Water L.C. Williams Program Manager, Critical Cyber Asset Infrastructure for Enterprise IT Security Tennessee Valley Authority Co-Located with the Smart Metering Networking and Operations Summit
- 2. At SCADA & Control Systems Security Summit you will meet… VPs, Directors and Managers responsible for: • SCADA/Process Controls/Real Time Systems • Information Technology • Information Security • Cyber Security • Critical Infrastructure/Resource Protection • Engineering • Regulatory Affairs/Compliance • Risk Management • System Operations • Smart Grid • Telemetry Venue Information Please visit the website for venue information: www.scadasecuritysummit.com Dear Colleague, This year the President pledged to safeguard the Nation’s vital digital systems, stating, “Protecting this infrastructure will be a national security priority. We will ensure that these networks are secure, trustworthy and resilient.” With 85 percent of the critical infrastructure in the U.S. in private hands, enhancing SCADA systems and other process controls supporting them will be no small task between Government and the utilities. Security experts agree the question is not whether a cyber security breach will occur, but when! Are your systems ready if the target is you? At SCADA & Control Systems Security Summit, you will hear from a speaker faculty of leading government officials, policymakers, regulators, technology experts and utility practitioners on how you can better assess the vulnerability of your SCADA system to attack and bolster its security layers accordingly. In response to the relatively recent shift of control systems over to open, interlocked networks, the expansion of the Smart Grid, increasingly sophisticated hacking capabilities and more stringent compliance requirements, security should be your #1 priority! Guarantee your seat at the table of industry leaders as they address and work through the most pressing cyber security critical to your business. In addition to the technical components to be discussed, change and configuration management will be a major part of the conversation so that you can better address the human barriers around security implementation. I look forward to meeting you in Washington, D.C.! Christopher Boucher Program Director Christopher.Boucher@iqpc.com Please note multiple discounts cannot be combined. A $99 processing charge will be assessed to all registrations not accompanied by credit card payment at the time of registration. MAKE CHECKS PAYABLE IN U.S. DOLLARS TO: IQPC * CT residents or people employed in the state of CT must add 6% sales tax. TEAM DISCOUNTS: For information on team discounts, please contact IQPC Customer Service at 1-800-882-8684. Only one discount may be applied per registrant. Special Discounts Available: A limited number of discounts are available for the non-profit sector, government organizations and academia. For more information, please contact customer service at 1-800-882-8684. Details for making payment via EFT or wire transfer: JPMorgan Chase Penton Learning Systems LLC dba IQPC: 957-097239 ABA/Routing #: 021000021 Reference: Please include the name of the attendee(s) and the event number: 18253.001 Payment Policy: Payment is due in full at the time of registration and includes lunches and refreshments. Your registration will not be confirmed until payment is received and may be subject to cancellation. For IQPC’s Cancellation, Postponement and Substitution Policy, please visit www.iqpc.com/cancellation Special Dietary Needs: If you have a dietary restriction, please contact Customer Service at 1-800-882-8684 to discuss your specific needs. ©2008 IQPC. All Rights Reserved. The format, design, content and arrangement of this brochure constitute a trademark of IQPC. Unauthorized reproduction will be actionable under the Lanham Act and common law principles. Register by Register by Register by Register by Standard 9/25/2009 10/9/2009 10/23/2009 11/6/2009 Price Conference Only (save $400) (save $300) (save $200) (save $100) $1199 $1299 $1399 $1499 $1,599 All Access (save $1347) (save $1247) (save $1147) (save $1047) (save $947) $1899 $1999 $2099 $2199 $2299 Workshop(s) $549 each $549 each $549 each $549 each $549 each Qualified Utilities Professionals Other Register by Register by Standard 10/23/2009 11/6/2009 Price Conference Only (save 600) (save $300) $1999 $2299 $2,599 All Access (save $1547) (save $1347) (save $1147) $2699 $2899 $3099 Workshop(s) $549 each $549 each $549 each Registration Information 2 Reasons Why SCADA & Control Systems Security Summit Gives You the Best Value for Your Marketing Spend: You will be exposed to senior decision makers from the electric, water and oil and gas industries. We actively maintain a reduced vendor ratio, which creates a more intimate networking and knowledge sharing environment for utilities. 15+ confirmed industry speakers with first-hand experience and foresight on the key security challenges to be discussed. Extensive networking opportunities, allowing face- to-face interaction with heads of your target market. Expert advice on how to effectively deploy new security, change and configuration management protocols. 1 5 2 3 4 5 P .S. Maximize your learning experience by attending our interactive training sessions! See page 3 and register today! Special Offer! The First 20 Utility Executives Attend the Conference Only for $999! Register by 9/25/2009
- 3. Pre-Conference Workshops 8:00am – 11:00am 7:45am Registration for Workshop A Introduction to Enhancing Control Systems Security from the Department of Homeland Security Monday, December 7, 2009 Today’s interconnected utilities demand that you protect systems controls for critical infrastructure and business-specific protection. Though this is a major challenge for any single utility to overcome, possessing a complete understanding of the threat landscape, known incidents and risk exposure to your specific system is critical to know what and where to secure as well as how to respond adequately when and if attack does occur. The purpose of this course is to introduce students to the basics of industrial control systems security, which includes a high level overview of the comparative analysis of IT and control system architecture, security vulnerabilities and mitigation strategies unique to the control system domain. What will be covered: • Overview on the current cyber security landscape: understanding the risks • Industrial Control Systems Applications • Current State of Industry • Practical Application of Cyber Security How you will benefit: • Reduce organizational risk by understanding how real and perceived threats will affect service reliability system operability, service deliverability and business continuity • Prevent exploits and detect intrusions using mitigation strategies to common vulnerabilities • Minimize and reduce system downtime with a well-governed response and recovery strategy Workshop Leader: Jeffrey Hahn, Training & Education, DHS Control Systems Security Program, Idaho National Laboratory These training sessions will provide participants with an opportunity to engage in a hands-on, deep-dive working group environment to help address and unravel the key issues and challenges associated with control system cyber security, critical infrastructure protection and the change and configuration protocols required for total business transformation! Sign up today! 3 A 11:15am – 2:15pm 11:00am Registration for Workshop B – Lunch will be served. Mitigating Risk and Increasing Audit-ability of SCADA Systems with Best-in-Class Configuration and Change Management Strategies SCADA environments present unique challenges around security in that they must be consistently available and cannot be shut down to perform security upgrades. It is however, critical that these systems be protected from cyber threats, and other vulnerabilities such as human error. This workshop will provide you with practical knowledge of the unique requirements in securing SCADA infrastructure, as well as insight into implementing effective change management and business process improvement techniques. What will be covered: • Integrating security, monitoring and control techniques into control systems environments • Methodologies for developing reliable audit trails to help monitor and respond to system changes • Meeting security compliance attestation requirements for audit purposes How you will benefit: • Gain a deeper understanding of unique requirements of control systems environments as they relate to security and audit-ability • Exposure to best practices in change management for control systems environments • Achieve and maintain ongoing compliance by process mapping organizational structures and governance Workshop Leader: Walter Sikora, VP Security Solutions, Industrial Defender B 2:30pm – 5:30pm 2:15pm Registration for Workshop C Conducting Full-Risk Assessments and Identifying Critical System Assets to Fortify Security & Enable Process Control Redesign Without identifying the proper assets to protect, no control system or the infrastructure they purport to protect will work. In fact, protection requires that you closely examine all systems within the enterprise in totality and not in isolation as well as to achieve the proper balance between a compliant system and one that is fully secure. What is involved in protecting cyber assets as opposed to physical ones? How do you design systems without replacing entire architectures and then sustain those changes over time? What will be covered: • How to appropriately assess and identify multi-layered protection based on best-in-class critical cyber asset methodologies • How to design and redesign control systems that are compliant without compromising optimal security levels • How to leverage and integrate cutting-edge security technologies into legacy SCADA environments without disrupting mission critical processes or compromising system operability How you will benefit: • Ensure the successful and secure upgrade of SCADA systems with project management strategies that do not compromise real-time system availability • Overcome business continuity challenges by understanding your system gaps and security assurance level • Support IT improvements over time with increased self-monitoring and enterprise-wide process mapping procedures Workshop Leader: Michael Toecker, Control Systems Security Designer, Compliance & Infrastructure Protection, Burns & McDonnell Engineering C www.scadasecuritysummit.com
- 4. 7:30 Registration & Coffee 8:00 Chairperson’s Welcome and Opening Remarks 8:15 Keynote: Enhancing Control Systems Security by Aligning National Policy with Private Interests With approximately 85 percent of the systems controlling critical infrastructure in private hands, it will be crucial for Government and utilities to work in coordination with one another in addressing today’s cyber security concerns as well as to help shape policy, increase awareness and drive implementation. In this session, you will learn about: • Current threat landscape, common vulnerabilities and key control system security issues based on the Risk = Threat x Vulnerability x Consequences formula • Ongoing mitigation strategies being developed as part of the National Infrastructure Protection Plan, including the creation of public-private partnerships and joint working groups • Future policy actions and regulatory recommendations being taken by the DHS Seán Paul McGurk Director, Control Systems Security, National Cyber Security Division U.S. Department of Homeland Security 9:00 Technology Panel: Upgrading Legacy Control Systems with Best-in-Class Next Generation Technologies and Seamless Configuration Management Decades ago, developers gave little consideration that the SCADA device would ever be connected to anything other then a closed network. The reality, though, is that utilities must implement security improvements outlined in the SCADA procurement standards by understanding the appropriate implementation how-to, and then ensure that those enhancements are maintained over time. It is this that will create the most pressing ongoing challenge: sustainable security. In this session, you will learn how to: • Deal with the existing base of equipment during process upgrades • Integrate network security into process designs in-line with the continual evolution of control systems and regulatory standards • Introduce process self-integrity monitoring as a means of ensuring reliable and safe controls Moderator: Doug Maughan Program Manager, Cyber Security R&D U.S. Department of Homeland Security Panelists: L.C. Williams Program Manager Critical Cyber Asset Infrastructure for Enterprise IT Security Tennessee Valley Authority Andrew Labovitch Manager of Information Technology Pepco Holdings Inc. Jake Brodsky Control Systems Engineer Washington Suburban Sanitary Commission Larry Bugh Chief Security Officer ReliabilityFirst Corporation & Member, NERC CIP Committee Kevin Morley Security & Preparedness Program Manager American Water Works Association 10:00 Morning Networking Break 10:45 Achieving Highly Secure and Compliant IT Architectures through Full-Scale Process Assessment & Redesign What we've learned so far isn't so much that you need to know your system architecture as you need to know the requirements and then redesign your architecture to meet those requirements. Because this is a journey and not a destination – evidenced by more stringent regulation and evolving threats – the security you had in place yesterday is not good enough for today and today’s isn’t good enough for tomorrow. In this session, you will learn how to: • Reduce risk exposure by understanding the business requirements for connectivity, what isn’t needed and what is negotiable • Meet federal regulations by leveraging compliance software and establishing liability for self-monitoring responsibilities • Create flexible architectures with ongoing, cross-functional collaboration between IT, IS and engineering Andrew Labovitch Manager of Information Technology Pepco Holdings Inc. 11:30 Attaining Non-Disruptive SCADA Security Upgrades with a Systematic, Incremental Change Strategy Unlike other industries, utilities cannot shut down entire systems to make the necessary upgrades, thereby presenting enormous challenges, including how you do so without disrupting service levels. For those who have tackled this challenge, the project management component is like walking on pins and needles. In this session, you will learn how to: • Relieve budgetary strain and minimize operational disruption with an in- house SCADA design and integration team • Effectuate successful security migrations using DNP Secure Authentication and other communications protocols • Improve system reliability and boilerplate standards with post mortem analysis Jake Brodsky Control Systems Engineer Washington Suburban Sanitary Commission 12:15 Networking Luncheon 1:15 Point/Counterpoint Roundtable: Achieving Compliance and a Strong Security Posture without Impacting System Operability or Process Efficiency Because utilities often use the terms ‘compliant’ and ‘security’ interchangeably, it is highly possible for your baseline standards to effectively meet threshold requirements without achieving a secure environment. In this session, you will discuss and learn how to: • Balance threshold standards with added security via advanced system metrics • Sustain secure, compliant environments with regular system monitoring and risk assessment processes embedded into new, internal operational directives • Save costs and resources by automating policy compliance with standards and regulation Larry Bugh Chief Security Officer ReliabilityFirst Corporation & Member, NERC CIP Committee Main Conference Day 1 4 Tuesday, December 8, 2009
- 5. 2:15 Selling Security to Key Stakeholders Using Quantifiable Risk & Financial Metrics Long before implementation becomes a reality, you must first demonstrate that the costs associated with control system security upgrades are justified by organizational decision makers. The challenge remains: how do you communicate potential exposure as a tangible, monetized business metric that upper management will understand? In this session, you will learn how to: • Increase buy-in by demonstrating how risk-driven enterprise information security architecture spans and aligns with objectives across all business functions • Develop a ‘security culture’ by leveraging key performance indicators of the core business • Transform information security from a cost center into an actively managed component of overall profit L.C. Williams Program Manager, Critical Cyber Asset Infrastructure for Enterprise IT Security Tennessee Valley Authority 3:00 Afternoon Networking Break 3:45 Preparing for SCADA Cyber Intrusion with an Executable Enterprise Incident Response Plan Though SCADA operators and IT professionals are actively involved in enhancing the security of their control systems as a result of past incidents, what they may not be adequately prepared for is how to adequately respond to a real time attack, especially since automation is not conducive to knowledge of manual operation. In this session, you will learn how to: • Avert system downtime with a response plan tailored to the unique organizational structures and management philosophies • Assure business continuity with multi-tiered approach to cross- functional training requirements, security governance and contingency planning • Elevate ability to adequately address incidents with increased due diligence and configuration and patch management Wayne Morgan President West Virginia American Water Day 1 Continued 4:30 Interactive Q&A Session: Balancing the Dichotomy Between Security and Compliance Companies and public agencies alike continually struggle with compliance deadlines while serving their customers and meeting business objectives. Couple those challenges with legacy infrastructures not inherently designed for security and internal cultural barriers, and you potentially get chaos. In this session you will learn about risk management and strategies for avoiding the mad dash toward compliance to the detriment of measurable security as well as: • Why your compliance efforts may ultimately fail • Developing a balance between compliance activity and a strong security posture • What prevents effective information sharing and industry collaboration Jon Stanford Chief Security Information Officer Bonneville Power Administration 5:30 Close of Conference Day 1 5 www.scadasecuritysummit.com Sponsorship and Exhibition Opportunities Sponsorships and exhibits are excellent opportunities for your company to showcase its products and services to high-level, targeted decision makers attending the SCADA & Control Systems Security Summit. Energy & Utilities IQ helps companies like yours achieve important sales, marketing and branding objectives by setting aside a limited number of event sponsorships and exhibit spaces – all of which are tailored to assist your organization in creating a platform to maximize its exposure within the industry. For more information on sponsoring or exhibiting at this or upcoming events, please contact Mario Matulich at 1 (212) 885-2719 or sponsorship@iqpc.com. About the Organizer: Energy & Utilities IQ, a division of IQPC, is dedicated to providing practical, detailed information through conferences, training courses, webinars and our monthly e-newsletter. By providing accurate, objective and up-to-date developments and trends in various industries, Energy IQ enables organizations to remain competitive and profitable.
- 6. 7:45 Registration & Coffee 8:00 Chairperson’s Recap of Conference Day 1 8:15 Keynote: Interpreting NERC CIP for Audit: Examining New Paradigms for Categorizing Critical Systems Historically friendly industry standards and a lack of information sharing has bred a culture in which critical assets have been underreported and miscategorized, rendering systems both non-compliant and insecure. Now, a ratcheting up on requirements by agencies like NERC are challenging utilities to balance the need to avoid $1m/violation/day penalties for non-compliance and the need to safeguard controls from cyber threat and imminent system failure – business risks that no utility can afford! In this session you will learn about: • Emerging critical asset standards and the future of critical asset identification • What needs to be protected and at what level • Achieving short-term compliance without compromising long- term security with attainable technical and non-technical strategies for implementation Jim Brenton Director, CIP Standards Development, ERCOT & Member NERC Critical Infrastructure Protection Committee 9:00 Perspectives Panel: Mind the Gap: Bridging SCADA with Smart Technology Security for a Sustainable Energy Future Where SCADA is controlled and users are well-known, the Internet is open and pervasive. As utilities enter into this new era of the Smart Grid and other “smart” technologies, these two worlds are destined to collide, presenting roadblocks and threat to system operators. In this panel, leaders from utilities, academia, vendors and the analyst community will describe the new infrastructure of the Smart Grid, highlighting the likely areas of connection to critical SCADA systems as well as brainstorm solutions to the security challenges increased connectivity will bring and the following: • How to identify new attack vectors as a result of smart implementations • How to select appropriate technologies for SCADA system security upgrades • How to create long-term protection with highly sustainable security governance Moderators: Jack Danahy Co-Founder The Smart Grid Security Blog Andy Bochman Co-Founder The Smart Grid Security Blog Please visit our website for panelist information. 10:00 Morning Networking Break 10:45 R&D Think Tank: An Update on Industry Advancements in Intelligent Control System Security from the National Institute of Standards and Technology This research and development think tank will highlight the latest trends in control system intelligence and the standards that support their application – priorities that are sometimes at odds with one another! In this session you will learn about: • Real and perceived threats to critical infrastructure based on new developments as a result of ongoing research • NIST’s role in influencing regulation, providing professional advice and other cross-benchmarking tools to ensure SCADA security awareness and implementation of best practice strategies • Latest cutting-edge technologies for use in securing SCADA systems in utility environments and the sector-specific applications of such solutions Keith Stouffer Mechanical Engineer, National Institute of Standards and Technology & Voting Member, International Society of Automation 11:30 Peer-to-Peer Interactive Roundtable: Protecting Critical Infrastructure from Risk by Creating Accessible Platforms for Increased Incident Reporting and Industry-wide Information Sharing With each organization managing a unique business approach to service delivery, there has historically been very little information exchanged between utilities even though security challenges are commonly shared. In response to low incident reporting, for example, RISI created an industry-wide repository and online database for collecting, investigating, analyzing and sharing critical information regarding cyber security. By providing industry with accurate security incident data, organizations can better understand the nature of the security risk to critical control systems. This in turn, allows companies to better focus their resources and prevent such incidents from occurring in the future. In this session, the following questions will be explored: • How urgent is the security risk to control systems and how serious are the consequences? • What are the threat sources and which security vulnerabilities are exploited? • Which industrial cyber-security incidents are fact and which are urban myth? • How can we ensure safe transmission of information and fears without increasing risk? • How can you actively contribute to improving industry-wide system security? Walt Boyes Editor-in-Chief, CONTROL Magazine & Advisory Board Member The Repository of Industrial Security Systems 12:30 Networking Luncheon Wednesday, December 9, 2009 6 Main Conference Day 2
- 7. 1:30 Working Towards Cultural Transformation through the Effective Knowledge Management of Core Business and Change Objectives With an ever-aging workforce of SCADA operators possessing a specific skill set and those on the IT controlling another, it will be important that there are successful knowledge transfer, safety training programs, talent management capabilities, including ensuring that the newer, more sophisticated software required to detect intrusion is not undermined because of improper configuration. The transformation of industry culture must take place for these important changes to take place, first, and then for security to be optimized at the levels these critical controls require. In this session, you will learn how to: • Overcome resistance and effectuate security change management by harmonizing disparate IT and SCADA standards, cross-training functions with new process upgrades and establishing liability to specific processes • Ensure seamless system usability of security enhancements by identifying and appropriating commercial solutions that do not conflict with the control systems domain • Create sustainable organizational human structures by creating a solid governance model and a security threshold that conforms to and exceeds Government regulation Mark Fabro Chief Security Scientist & Panelist for Subcommittee on Emerging Threats Cybersecurity and Science and Technology, DHS 2:15 Improving Control Management by Fostering New Communication Channels and Organizational Structures Between Engineering, IT and IS With control systems taking on more and more of a hybrid function, many SCADA engineers are finding their roles and responsibilities changing with respect to the systems they’ve operated for decades, particularly as IT takes on a greater role. However, without an organization-wide understanding of this shift or a governance structure in place to definitively determine who owns what, many new obstacles have been created with respect to control systems management. In this session, you will learn how to: • Optimize the security and usability of implementations by building matrices between IT and SCADA operators • Avoid threat overexposure by assigning liability to specific SCADA security functions • Track system changes by establishing audit trails and access systems Chris Jager Sr. IT Security Analyst, Puget Sound Energy & Chairman Energy Sector Security Consortium 3:00 Afternoon Networking Break 3:30 30 Ideas in 60 Minutes: Enhancing Cyber Security with Best-in-Class Change and Configuration Management Practices Keeping systems patched, filtering traffic and disconnecting unneeded services to improve security is often met with pushback from control system owners who claim that such procedures compromise reliability and efficiency. Utility companies, public sector stakeholders and technology innovators will break down the risk assessment, technological advances and policy activities that have had the greatest impact in their efforts to secure process controls from cyber attack. The panel will also brainstorm next- steps and outline key takeaways for conference participants, including: • How to assess critical physical and cyber infrastructures, identify risk exposure and create a plan for change • How to optimize control systems around the tradeoffs associated with compliance and security through process redesign • How to ensure sustainable architectures and ongoing control system governance Moderator: Walt Boyes Editor-in-Chief, CONTROL Magazine & Advisory Board Member The Repository of Industrial Security Systems Panelists: Chris Jager Sr. IT Security Analyst, Puget Sound Energy & Chairman Energy Sector Security Consortium Mark Fabro Chief Security Scientist & Panelist for Subcommittee on Emerging Threats Cybersecurity and Science and Technology, DHS Keith Stouffer Mechanical Engineer, National Institute of Standards and Technology & Voting Member International Society of Automation Jon Stanford Chief Security Information Officer Bonneville Power Administration 4:30 Chairperson’s Closing Remarks and End of Conference POWERGRID International is the power industry’s leading source of information on electric power transmission and distribution automation, engineering, and information technology. More than 36,000 worldwide electric utility professionals, managers, engineers and other qualified subscribers count on POWERGRID International to present the information they need to make on-the-mark business and technical decisions every day. Advertising in POWERGRID International puts your company’s name where you want it to be–in front of key industry decision makers every day. Please visit www.Power- Grid.Com for more information. Control Engineering continues to set high standards as the multimedia leader of control, instrumentation and automation. For more than 50 years, Control Engineering Magazine has upheld a commitment to consistency and quality, earning subscribers’ trust and building great affinity. We serve the automation market, which designs, implements, maintains, and manages control/instrumentation systems, components, and equipment. Please visit www.controleng.com for more information. CSIA is committed to the business development of control system integration companies and their implementation of best practices in order to provide a healthy, low-risk channel for the application of technology to their industrial client. CSIA brings successful integration to the marketplace by: • Creating recognition and demand for CSIA certified members • Improving system integration best practices and performance; and • Providing an industry forum and networking opportunities. Website: www.controlsys.org Founded in 1945, The International Society of Automation is a leading, global, nonprofit organization that is setting the standard for automation by helping over 30,000 worldwide members and other professionals solve difficult technical problems, while enhancing their leadership and personal career capabilities. Based in Research Triangle Park, North Carolina, ISA develops standards, certifies industry professionals, provides education and training and publishes books and technical articles. Control is the voice of the end user in process automation. The Control brand is an integrated content delivery system that serves relevant content to the global end user audience in all the ways they choose to receive it: print magazine, print supplements, website, e-zines, blogs, RSS feeds, webcasts and podcasts. 7 www.scadasecuritysummit.com Day 2 Continued About our Media Partners
- 8. Featuring interactive sessions and real world case studies specifically designed for the electric, water and oil & gas industries to facilitate a highly focused, stakeholder-driven dialogue and peer networking opportunities to help protect your process controls and the critical infrastructure they support from cyber threats. proudly presents Enhancing Cyber Security for Critical Infrastructure Protection through Seamless Compliance, Configuration and Change Management Synergies Special Offer! The First 20 Utility Executives Attend the Conference Only for $999! Register by 9/25/2009. See page 2. 18253.001/D/SC International Quality & Productivity Center 535 5th Avenue, 8th Floor New York, NY 10017 YES! Please register me for See Page 2 for pricing details. ❑ Main Conference Only- December 8-9 ❑ All-Access Pass- December7-9 ❑ Workshop(s) Only- December 7 Choose Your Workshop(s) ❑ A ❑ B ❑ C REGISTRATION CARD Your customer registration code is: When registering, please provide the code above. Name__________________________________ Job Title ________________________ Organization____________________________________________________________ Approving Manager______________________________________________________ Address________________________________________________________________ City__________________________________State______________Zip____________ Phone________________________________Fax_______________________________ E-mail__________________________________________________________________ ❑ Please keep me informed via email about this and other related events. ❑ Check enclosed for $_________ (Payable to IQPC) ❑ Charge my __Amex __Visa __Mastercard __Diners Club Card #__________________________________Exp. Date___/___ CVM code ______ Details for making payment via EFT or wire transfer can be found on preceding page. ❑ I cannot attend, but please keep me informed of all future events. 5 EASY WAYS TO REGISTER: 3 2 1 4 4 5 Web: www.scadasecuritysummit.com Call: 1-800-882-8684 Email: info@iqpc.com Fax: 1-646-378-6025 Mail: IQPC 535 5th Avenue, 8th Floor, New York, NY 10017 www.scadasecuritysummit.com December 7-9, 2009 • Washington, D.C. Metro Area Media Partners: