Binomial1
•Descargar como PPT, PDF•
0 recomendaciones•276 vistas
Denunciar
Compartir
Denunciar
Compartir
Recomendados
Recomendados
Más contenido relacionado
Más de Samantha Turi
Más de Samantha Turi (11)
Último
Último (20)
Digital Identity is Under Attack: FIDO Paris Seminar.pptx

Digital Identity is Under Attack: FIDO Paris Seminar.pptx
Varsha Sewlal- Cyber Attacks on Critical Critical Infrastructure

Varsha Sewlal- Cyber Attacks on Critical Critical Infrastructure
Generative Artificial Intelligence: How generative AI works.pdf

Generative Artificial Intelligence: How generative AI works.pdf
Zeshan Sattar- Assessing the skill requirements and industry expectations for...

Zeshan Sattar- Assessing the skill requirements and industry expectations for...
TrustArc Webinar - How to Build Consumer Trust Through Data Privacy

TrustArc Webinar - How to Build Consumer Trust Through Data Privacy
New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024

New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024
Transcript: New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024

Transcript: New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024
Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx

Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx
How to Effectively Monitor SD-WAN and SASE Environments with ThousandEyes

How to Effectively Monitor SD-WAN and SASE Environments with ThousandEyes
Merck Moving Beyond Passwords: FIDO Paris Seminar.pptx

Merck Moving Beyond Passwords: FIDO Paris Seminar.pptx
The Role of FIDO in a Cyber Secure Netherlands: FIDO Paris Seminar.pptx

The Role of FIDO in a Cyber Secure Netherlands: FIDO Paris Seminar.pptx
Abdul Kader Baba- Managing Cybersecurity Risks and Compliance Requirements i...

Abdul Kader Baba- Managing Cybersecurity Risks and Compliance Requirements i...
UiPath Community: Communication Mining from Zero to Hero

UiPath Community: Communication Mining from Zero to Hero
Bridging Between CAD & GIS: 6 Ways to Automate Your Data Integration

Bridging Between CAD & GIS: 6 Ways to Automate Your Data Integration
Microsoft 365 Copilot: How to boost your productivity with AI – Part one: Ado...

Microsoft 365 Copilot: How to boost your productivity with AI – Part one: Ado...
Potential of AI (Generative AI) in Business: Learnings and Insights

Potential of AI (Generative AI) in Business: Learnings and Insights
Glenn Lazarus- Why Your Observability Strategy Needs Security Observability

Glenn Lazarus- Why Your Observability Strategy Needs Security Observability
Binomial1
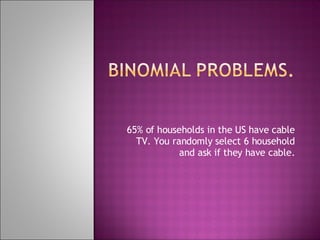
- 1. 65% of households in the US have cable TV. You randomly select 6 household and ask if they have cable.