Network Protocol Analyzer
•Descargar como PPTX, PDF•
0 recomendaciones•943 vistas
Denunciar
Compartir
Denunciar
Compartir
Recomendados
Más contenido relacionado
La actualidad más candente
La actualidad más candente (20)
Prensentation on packet sniffer and injection tool

Prensentation on packet sniffer and injection tool
Similar a Network Protocol Analyzer
Similar a Network Protocol Analyzer (20)
Basic ccna interview questions and answers ~ sysnet notes

Basic ccna interview questions and answers ~ sysnet notes
Internets Manage Communication Procedure and Protection that Crash on Servers

Internets Manage Communication Procedure and Protection that Crash on Servers
Más de Sourav Roy
Más de Sourav Roy (13)
Último
Mehran University Newsletter Vol-X, Issue-I, 2024

Mehran University Newsletter Vol-X, Issue-I, 2024Mehran University of Engineering & Technology, Jamshoro
Making communications land - Are they received and understood as intended? we...

Making communications land - Are they received and understood as intended? we...Association for Project Management
Último (20)
ICT Role in 21st Century Education & its Challenges.pptx

ICT Role in 21st Century Education & its Challenges.pptx
Mixin Classes in Odoo 17 How to Extend Models Using Mixin Classes

Mixin Classes in Odoo 17 How to Extend Models Using Mixin Classes
Seal of Good Local Governance (SGLG) 2024Final.pptx

Seal of Good Local Governance (SGLG) 2024Final.pptx
Asian American Pacific Islander Month DDSD 2024.pptx

Asian American Pacific Islander Month DDSD 2024.pptx
Micro-Scholarship, What it is, How can it help me.pdf

Micro-Scholarship, What it is, How can it help me.pdf
Making communications land - Are they received and understood as intended? we...

Making communications land - Are they received and understood as intended? we...
UGC NET Paper 1 Mathematical Reasoning & Aptitude.pdf

UGC NET Paper 1 Mathematical Reasoning & Aptitude.pdf
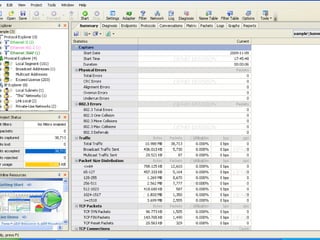
Network Protocol Analyzer
- 8. Detecting ARP attack AS an easy and popular network attack,ARP attack may cause damages to the entire network,so before it brings losses we need to solve ARP attack as earliest time possible.(1)
- 10. Monitor Network Utilization It is the ratio of the current network traffic to the maximum traffic that the port can handle,it indicates network bandwidth so we can understand whether network is busy,normal or idel.(3)
- 11. How To Get Top 10 Traffic Local Host When the network is getting slow we need to find out that who is using our bandwidth.(4)
- 12. Track down bittorrent If somebody in our local network is downloading files using bitTorrent,it will consume large amount of bandwidth,so we need to track down who is using bittorrent and recover normal network condition in time.(5)
