Safe use of cloud - alternative cloud
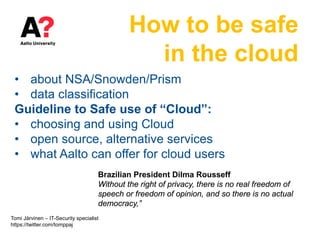
- 1. How to be safe in the cloud • about NSA/Snowden/Prism • data classification Guideline to Safe use of “Cloud”: • choosing and using Cloud • open source, alternative services • what Aalto can offer for cloud users Brazilian President Dilma Rousseff Without the right of privacy, there is no real freedom of speech or freedom of opinion, and so there is no actual democracy,” Tomi Järvinen – IT-Security specialist https://twitter.com/tomppaj
- 2. 2 Snowden’s bomb 6/5/2013 ”Prism” Content is based on several news papers, Financial times, Guardian, New york times, collection of all major news stories, one collection: https://docs.google.com/spreadsheet/pub?key=0Al2LIEgoNIx2dFNCb3dTS1c5Y2ZkQWNzVUc5UkNFeEE&output=html Snowden’s report big issue, Directly?
- 3. 3 Hot topic 2013, Snowden & NSA Facts are based on several news papers, Financial times, Guardian, New york times, collection of all major news stories: https://docs.google.com/spreadsheet/pub?key=0Al2LIEgoNIx2dFNCb3dTS1c5Y2ZkQWNzVUc5UkNFeEE&output=html Claim: Only to prevent terrorism.. Nonsense.. Snowden:these programs were never about terrorism: they're about economic spying, social control, and diplomatic manipulation. So, who are the targets? Angela Merkel, Israeli PM, EU's competition commissioner, UN headquarter, German government buildings, Brazillian oil company Petrobras, heads of institutions that provide humanitarian and financial help to Africa, Médecins du Monde, energy and finance ministries.. And naturally all internet users..(Facebook, Google, Yahoo..) Doesn’t sound like terrorists..
- 4. 4 Hot topic 2013, Snowden & NSA Facts are based on several news papers, Financial times, Guardian, New york times, collection of all major news stories: https://docs.google.com/spreadsheet/pub?key=0Al2LIEgoNIx2dFNCb3dTS1c5Y2ZkQWNzVUc5UkNFeEE&output=html Claim: Only to prevent terrorism.. Nonsense.. Snowden:these programs were never about terrorism: they're about economic spying, social control, and diplomatic manipulation. So, who are the targets? Angela Merkel, Israeli PM, EU's competition commissioner, UN headquarter, German government buildings, Brazillian oil company Petrobras, heads of institutions that provide humanitarian and financial help to Africa, Médecins du Monde, energy and finance ministries.. And naturally all internet users..(Facebook, Google, Yahoo..) Doesn’t sound like terrorists..
- 5. 5 Hot topic 2013, Snowden & NSA Facts are based on several news papers, Financial times, Guardian, New york times, collection of all major news stories: https://docs.google.com/spreadsheet/pub?key=0Al2LIEgoNIx2dFNCb3dTS1c5Y2ZkQWNzVUc5UkNFeEE&output=html Claim: Only few people have access to confidential data Nonsense.. CIA official and principal at Booz Allen: Of the 4.9 million people (government, organizations, contractors) with clearance to access "confidential and secret" government information, 1.1 million, or 21 percent, work for outside contractors, according to a report from Clapper's office. Of the 1.4 million who have the higher "top secret" access, 483,000, or 34 %, work for contractors.
- 6. 6 Hot topic 2013, Snowden & NSA http://foxnewsinsider.com/2013/06/07/how-much-zettabyte-nsa-utah-facility-can-hold-immense-amount-data Claim: They cannot collect all traffic from all users and keep it Nonsense For example NSA Utah data center (estimations): 5 million storage systems running roughly 1.25 billion, 4-terabyte hard drives,” . Latest estimation 5 Zettabytes (1 Zettabyte whole world one year internet use) 1 Gb = 960 minutes of music, 1 Zettabyte = 2 billion years of music.
- 7. 7 Hot topic 2013, Snowden & NSA http://foxnewsinsider.com/2013/06/07/how-much-zettabyte-nsa-utah-facility-can-hold-immense-amount-data Claim: They cannot collect all traffic from all users and keep it Nonsense For example NSA Utah data center (estimations): 5 million storage systems running roughly 1.25 billion, 4-terabyte hard drives,” . Latest estimation 5 Zettabytes (1 Zettabyte whole world one year internet use) 1 Gb = 960 minutes of music, 1 Zettabyte = 2 billion years of music.
- 8. 8 Hot topic 2013, Snowden & NSA Claim: It is just Metadata Nonsense (US persons it seems to be mostly just metadata) 120 billion cellular calls from all over the world every month, Email, Chat - video, voice, Videos, Stored data, VoIP, Filer transfers, Video Conferencing, Notifications of target activity, logins, Online Social Networking, etc. From US legal point of view there is nothing wrong with this, if target is non-US person. (FISA Amendments Act, Patriot Act) ------- Few academic researchers using Intelius, Google search, and three initial sources associated 91% of the "metadata" to real persons. https://cyberlaw.stanford.edu/blog/2013/11/what%27s-in-your-metadata http://webpolicy.org/2013/12/23/metaphone-the-nsas-got-your-number/ http://en.wikipedia.org/wiki/PRISM_%28surveillance_program%29#Extent_of_surveillance
- 9. 9 Hot topic 2013, Snowden & NSA Claim: It is just Metadata Nonsense (US persons it seems to be mostly just metadata) 120 billion cellular calls from all over the world every month, Email, Chat - video, voice, Videos, Stored data, VoIP, Filer transfers, Video Conferencing, Notifications of target activity, logins, Online Social Networking, etc. From US legal point of view there is nothing wrong with this, if target is non-US person. (FISA Amendments Act, Patriot Act) ------- Few academic researchers using Intelius, Google search, and three initial sources associated 91% of the "metadata" to real persons. https://cyberlaw.stanford.edu/blog/2013/11/what%27s-in-your-metadata http://webpolicy.org/2013/12/23/metaphone-the-nsas-got-your-number/ http://en.wikipedia.org/wiki/PRISM_%28surveillance_program%29#Extent_of_surveillance
- 10. Why should I care about NSA etc? • presumption of guilt vs. modern law presumption of innocence. • false positives • nobody knows about future, Bruce Schneir: it is not about “nothing to hide” – it’s that we have everything to lose • transferring power to security organisations • the loss of personal data control • misuse, enormous overcollecting will lead to misuse, sooner or later. By government or individuals. There is huge money making possibilities • Obama 17.1.2014: ”No more massive collection, as long as I’m the president” (but what after that?) One false positive case, David Mery entered to the subway wearing a jacket in warm weather, an algorithm monitoring the CCTV Dacid suspicious. The police arrested him, and checked his flat. Though he was never convicted of a crime, Mery is still on file as a potential terrorist eight years later, and can't get a visa to travel abroad. http://www.theguardian.com/technology/blog/2013/jun/14/nsa-prism
- 11. 11 big question, do you need to trust over 1 M persons? or just very few http://projects.washingtonpost.com/top-secret-america http://www.worldpolicy.org/blog/2013/08/09/what-nsa-can-learn-sweden http://www.designbuild-network.com/projects/gchq/ http://www.microsoft.com/online/legal/v2/en-us/MOS_PTC_Third_Parties.htm A” Sweden FRA 700 employees UK GCHQ 4000 employees USA NSA 40 000 own employees 483,000 Contractor employees All the Cloud Providers and their contractors.
- 12. Summary about revelations, Think about you and your work • The DATA what you are working with • Some nationalities might be interesting • If you are travelling a lot • If you work with military projects or something innovative, or valuable • Political reasons • Co-operation with external corporations If you are planning to be politician, nobel winner or some other ”VIP” take into consider that lot of people might have access to your whole online life.
- 13. But Cloud is Still Great! Next, guideline to SafeCloud! elastic resources accessible from everywhere typically via browser scalable “pay only for what you use” There is a lot what you can do to keep yourself and your data safe!
- 14. Data classification? Data classification is mandatory when organization is moving to cloud services in larger scale. Aalto university has new data classification policy. Policy provide guideline for separating public data from classified data and separate detailed handling guide. There is six month period of transition, at the moment university IT is building new services for handling classified data. Data classification policy specifies all organization data, determining its security class (public, internal, confidential or secret), and then assigning it to a categories. During spring 2014 there will be trainings about classification.
- 15. First , think about your data In classification, basic rule is that cloud services are only for ”Public data”, meaning all the data what is NOT ”Classified” (confidential, internal, ST levels) in the policy. Examples of classified data: • study attainments, student evaluations • research plans, development work (unpublished) • published intellectual property • unpublished patents • HR and employment • medical • financial • technology and telecommunications data (usage, log data) • security information • confidential business information • trade secrets • financial, tax, and insurance records Full list in Data Classification policy
- 16. 16 Second, your privacy? Privacy, If you like to keep your privacy, hide yourself and your device • use "alias”, create web-identity, or several like :Teemu courseX2012, • use Android device with “Anonymous” account, like JoesSamsung@gmail.com • use anonymity services, VPN & Anonymous proxy • optimize your Browser privacy settings, (in any browser this doesn’t clear all) • F-Secure Freedome, http://freedome.f-secure.com/en/home.html • technical solution - https://www.whonix.org/wiki/Main_Page Whonix is an operating system focused on anonymity, privacy and security You will lose a lot of functionality but think which one is more important for you? Privacy or active online life with your real identity. (In organization network and with organization device options are limited)
- 17. 17 Third, security (1) • you cannot get anything “back” • services may claim ownership of the information • “free” services often collect and disclose information to third parties such as advertisers or collaboration partners. So, think what you share • malicious links, think before clicking • think where you buy from • "fakeware / scareware“, think before buying • be accurate, how and what you write • please do not comment on behalf of the University, unless it belongs to the job description :) • be careful, and specially with Android - > More privacy: https://en.wikipedia.org/wiki/Replicant_(operating_system) One open source operating system for Android devices Open source Android software : https://en.wikipedia.org/wiki/F-Droid Trend micro
- 18. 18 Third, security (2) • keep your password / username combination in safe, if the worst happens (serious illness, even death, or matters related to legislation) • material may be financially or because of some other reason valuable (university or relatives, e.g. script, photos, new 7 brothers:) • use different password and user id, mnemonic?, software like • "KeePass“ http://keepass.info/ for password management • http://nsd.dyndns.org/pwsafe/ , open source password safe In Windows it needs also: http://cygwin.com/ • keep copies of everything on your own computer • do not accept all friend requests! • store files securely with encryption http://www.makeuseof.com/tag/5-ways-to-securely-encrypt-your-files-in-the- cloud/
- 19. • three basic models: Free – Advertisement – Freemium (business) • free service (often end up to advertisement or freemium model) • advertisement:, what is the motivation of the service provider? – money, money, money (Typical services, Google, Facebook) • Freemium, light free version, full with paying something (example Yammer) • and, stay focused, service for one purpose usually fits the user needs better and lasts longer – users learn how to use – service does what it is supposed to do – probably easier to find alternative solution when needed MIT Study: "free" is a special price that confuses peoples' thinking. http://web.mit.edu/ariely/www/MIT/Papers/zero.pdf Fourth, choose the right service (1) 19
- 20. pay attention! • documentation, widely used API:s • standard and multiple formats • anonymity (option to study without giving personal details to external marketing company) • EULA, terms of service, privacy policy (Good or Bad?) • integration to other same provider services (lock in vs. easy exit) More information about EULAs: open community http://tos-dr.info/ ”Terms of service - didn’t read” Fourth, choose the right service (2) 20
- 21. one example: 21 Service vs user, winners and loosers? http://www.talouselama.fi/Tebatti/kysymykset/kuluttaja+ala+luovuta+dataa+ilmaiseksi/a2223878 https://www.schneier.com/about.html http://web.mit.edu/ariely/www/MIT/Papers/zero.pdf Zero as a special price mobile network information, details of how you use the service, search queries, phone number, calling-party number, forwarding numbers, time and date of calls, duration of calls, SMS routing information and types of calls, system activity, hardware settings, browser type, browser language, the date and time of your request and referral URL.. USERS DATA NO COST SERVI- CE NO COST 2013: Profit 12 Billions Turnover 60 Billions T-shirtsetc.com BuyPosters.com CheapCam.com Onlinefurnitures.com bikecarpart.com cartyre.com horseshoes.com feathers.com pillows.com Bellswhistles.com Acme.com…. USERS DATA WITH LITTLE COST MONEY ”Bruce Schneier: users like free things, and don't realize how much value they're giving away to get it. “ Matti Wiberg UTU: Consumers have to learn that the data is valuable. There is no sense to give it away for free, even televisions are collecting data today. Why not to try alternative solutions - >
- 22. Alternative Web-services & open source 22 WEB search https://ixquick.com/ (https://startpage.com/) ixQuick does not collect or share any personal information based in New York and the Netherlands. https://duckduckgo.com/ Anonymous and unlogged web searches. There is also a DuckDuckGo hidden service for Tor users https://safesearch-stg.f-secure.com/ F-Secure Beta service https://disconnect.me/ Coming soon? Proxy for other search engines ------------------- Tools and methods for totally anonymous web use, ”TOR” https://www.torproject.org/
- 23. Alternative Web-services & open source 23 DISK & File Encryption http://www.truecrypt.org/ Real-time disk (hard drive, USB etc) and partition encryption software. http://www.axantum.com/axcrypt/ Open source Encryption tool with “wipe” option https://diskcryptor.net/ Open source partition encryption solution Email encryption https://en.wikipedia.org/wiki/Enigmail User friendly extension for Thunderbird & Seamonkey http://www.gnupg.org/ Complete data encryption and decryption tool, texts, e-mails, files, directories, and whole disk partitions. Plugin for Thunderbird
- 24. Alternative Web-services & open source 24 Secure share and synchronise your data www.bittorrent.com/sync peer-to-peer file synchronization tool available for Windows, Mac, Linux.. http://www.younited.com/ F-Secure sync tool http://sparkleshare.org/ Self-hosted version control and file sync. https://git-annex.branchable.com/ git-annex Synchronize folders on your computers and drives. “Guru tool”, good help pages
- 25. Alternative Web-services & open source 25 Email https://bitmessage.org based on Bitcoin technology. Bitmessage is a promising alternative to email, but it has not yet been audited by security professionals. http://www.autistici.org/ Italian based community, offers logging free email Accounts, Instant Messaging, Web Hosting, etc. https://en.wikipedia.org/wiki/K-9_Mail Open source mail application for the Android operating system. ----- Good to know, https://mykolab.com/ Email, File Storage & Sync accounts hosted in Switzerland. Strong Swiss privacy laws but 10 CHF per month. http://www.kapsi.fi/ 40€/year, Finnish provider
- 26. Alternative Web-services & open source 26 Instant messaging https://otr.cypherpunks.ca/index.php#faqs Off-the-Record (OTR) Messaging allows you to have private conversations and instant messaging https://jitsi.org/ Encrypted text, voice, and video messaging for multiple platforms. https://whispersystems.org/ encrypted end-to-end Android calls and txt https://www.linphone.org/ Encrypted voice and video chat client for multiple platforms. http://mumble.sourceforge.net/ Encrypted multi-user chat.
- 27. Alternative Web-services & open source 27 Publishing & collaboration https://mediacru.sh/ image, audio, video hosting. Note that it Includes Google Analytics and Google Adsense if you do not have Do Not Track enabled. https://img.bi/ Image hosting with in-browser AES-256 encryption. https://foodl.org/ surveys or polls and for scheduling meetings http://etherpad.org/ Self-hosted, real-time collaborative documents. http://ethercalc.net/ Multi-user spreadsheet server.
- 28. Alternative Web-services & open source 28 Publishing & social media http://movim.eu/ Private, decentralized social network server. https://diasporafoundation.org/ Community-run, distributed social network. http://retroshare.sourceforge.net/ Serverless decentralised communication platform. IM, forums, VoIP, file sharing, and more.
- 29. Alternative Web-services & open source 29 Operating systems https://www.whonix.org/wiki/Main_Page https://en.wikipedia.org/wiki/Tails_OS Linux based operating systems focused on anonymity, privacy and security
