Security Design Patterns
•
2 recomendaciones•800 vistas
Denunciar
Compartir
Denunciar
Compartir
Descargar para leer sin conexión
Recomendados
Develop and deploy a secure portal solution using web sphere portal v5 and ti...

Develop and deploy a secure portal solution using web sphere portal v5 and ti...Banking at Ho Chi Minh city
It security compliance management design guide with ibm tivoli security infor...

It security compliance management design guide with ibm tivoli security infor...Banking at Ho Chi Minh city
It security compliance management design guide with ibm tivoli security infor...

It security compliance management design guide with ibm tivoli security infor...Banking at Ho Chi Minh city
Más contenido relacionado
Similar a Security Design Patterns
Develop and deploy a secure portal solution using web sphere portal v5 and ti...

Develop and deploy a secure portal solution using web sphere portal v5 and ti...Banking at Ho Chi Minh city
It security compliance management design guide with ibm tivoli security infor...

It security compliance management design guide with ibm tivoli security infor...Banking at Ho Chi Minh city
It security compliance management design guide with ibm tivoli security infor...

It security compliance management design guide with ibm tivoli security infor...Banking at Ho Chi Minh city
Similar a Security Design Patterns (17)
Develop and deploy a secure portal solution using web sphere portal v5 and ti...

Develop and deploy a secure portal solution using web sphere portal v5 and ti...
It security compliance management design guide with ibm tivoli security infor...

It security compliance management design guide with ibm tivoli security infor...
It security compliance management design guide with ibm tivoli security infor...

It security compliance management design guide with ibm tivoli security infor...
XAdES Specification based on the Apache XMLSec Project 

XAdES Specification based on the Apache XMLSec Project
RDB Synchronization, Transcoding and LDAP Directory Services ...

RDB Synchronization, Transcoding and LDAP Directory Services ...
Más de Aung Khant
Más de Aung Khant (20)
Último
Último (20)
Tata AIG General Insurance Company - Insurer Innovation Award 2024

Tata AIG General Insurance Company - Insurer Innovation Award 2024
Factors to Consider When Choosing Accounts Payable Services Providers.pptx

Factors to Consider When Choosing Accounts Payable Services Providers.pptx
The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf

The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf
Breaking the Kubernetes Kill Chain: Host Path Mount

Breaking the Kubernetes Kill Chain: Host Path Mount
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
Exploring the Future Potential of AI-Enabled Smartphone Processors

Exploring the Future Potential of AI-Enabled Smartphone Processors
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...

Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
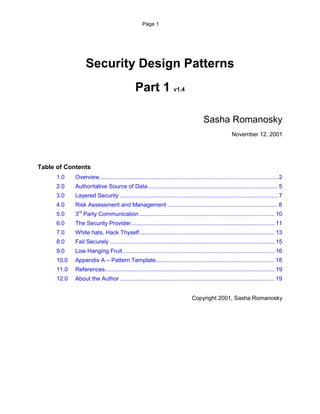
Security Design Patterns
- 1. Page 1 Security Design Patterns Part 1 v1.4 Sasha Romanosky November 12, 2001 Table of Contents 1.0 Overview ............................................................................................................. 2 2.0 Authoritative Source of Data................................................................................ 5 3.0 Layered Security ................................................................................................. 7 4.0 Risk Assessment and Management .................................................................... 8 5.0 3rd Party Communication ..........................................
