Denunciar
Compartir
Descargar para leer sin conexión
Recomendados
Zco integrates columbitech mobile vpn in police pad and firetab

Zco integrates columbitech mobile vpn in police pad and firetabZco Corporation | Nashua, NH - Profile and Reviews
Recomendados
Zco integrates columbitech mobile vpn in police pad and firetab

Zco integrates columbitech mobile vpn in police pad and firetabZco Corporation | Nashua, NH - Profile and Reviews
Más contenido relacionado
Más de Fraunhofer AISEC
Más de Fraunhofer AISEC (20)
Native Code Execution Control for Attack Mitigation on Android

Native Code Execution Control for Attack Mitigation on Android
Tech Report: On the Effectiveness of Malware Protection on Android

Tech Report: On the Effectiveness of Malware Protection on Android
Innovation braucht Sicherheit - Sicherheit braucht Forschung

Innovation braucht Sicherheit - Sicherheit braucht Forschung
Security for Automotive with Multicore-based Embedded Systems

Security for Automotive with Multicore-based Embedded Systems
Sicherheit im Internet Sichere Identität, sichere Dienste und Compliance

Sicherheit im Internet Sichere Identität, sichere Dienste und Compliance
IT-Sicherheit: Herausforderungen für Wissenschaft und Gesellschaft

IT-Sicherheit: Herausforderungen für Wissenschaft und Gesellschaft
Último
Último (20)
Merck Moving Beyond Passwords: FIDO Paris Seminar.pptx

Merck Moving Beyond Passwords: FIDO Paris Seminar.pptx
Gen AI in Business - Global Trends Report 2024.pdf

Gen AI in Business - Global Trends Report 2024.pdf
Unleash Your Potential - Namagunga Girls Coding Club

Unleash Your Potential - Namagunga Girls Coding Club
Developer Data Modeling Mistakes: From Postgres to NoSQL

Developer Data Modeling Mistakes: From Postgres to NoSQL
Hyperautomation and AI/ML: A Strategy for Digital Transformation Success.pdf

Hyperautomation and AI/ML: A Strategy for Digital Transformation Success.pdf
Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx

Passkey Providers and Enabling Portability: FIDO Paris Seminar.pptx
TeamStation AI System Report LATAM IT Salaries 2024

TeamStation AI System Report LATAM IT Salaries 2024
"Subclassing and Composition – A Pythonic Tour of Trade-Offs", Hynek Schlawack

"Subclassing and Composition – A Pythonic Tour of Trade-Offs", Hynek Schlawack
Digital Identity is Under Attack: FIDO Paris Seminar.pptx

Digital Identity is Under Attack: FIDO Paris Seminar.pptx
Nell’iperspazio con Rocket: il Framework Web di Rust!

Nell’iperspazio con Rocket: il Framework Web di Rust!
"Debugging python applications inside k8s environment", Andrii Soldatenko

"Debugging python applications inside k8s environment", Andrii Soldatenko
New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024

New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024
Unraveling Multimodality with Large Language Models.pdf

Unraveling Multimodality with Large Language Models.pdf
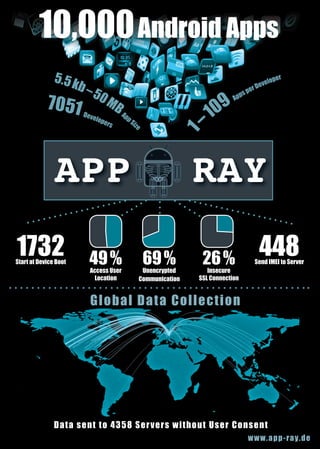
App Ray: 10000 Apps
- 1. 10,000 Android Apps 5.5 k b eve lo p e rs pp Si ze 1 –5 0M 7051 D B A APP 1732 Start at Device Boot 49 % Access User Location 9 0 1 – pe ps Ap ev rD per elo RAY 69 % Unencrypted Communication 26 % Insecure SSL Connection 448 Send IMEI to Server Gl oba l Data Col l e ct i o n D a t a s en t t o 435 8 Ser ver s w it hout User Consent www.ap p - r ay.de
