Seattle Tech4Good meetup: Data Security and Privacy
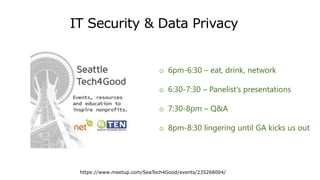
- 1. IT Security & Data Privacy https://www.meetup.com/SeaTech4Good/events/235268004/ o 6pm-6:30 – eat, drink, network o 6:30-7:30 – Panelist’s presentations o 7:30-8pm – Q&A o 8pm-8:30 lingering until GA kicks us out
- 2. Tonight’s Panelists Mary Gardner Chief Information Security Officer Ralph Johnson Chief Information Security and Privacy Officer Peter Kittas Web and IT Consultant Revelate LLC
- 3. Program • Housekeeping (Thank You GA!) • Who is Seattle Tech4Good? • @seatech4good • #datasecurity
- 4. Security, Compliance, Risk Management Mary Gardner, CISSP
- 6. KnowYour Data What kind of data do you have Who has access Where is your data Why is it important to your non-profit When can you delete it?
- 7. Regulations and Standards Regulation Description Triggers Requirements HIPAA Requires that protected health Information (PHI) be maintained in a secure and confidential manner Billing Self-Insured Companies Business Associate Agreements Encryption of PHI Standards for Deidentification Breach Notification Policy and Standards for Protection of Data GLBA Requires that Customers Personally Identifiable Information be secured regardless of where it lives. Also allowed for Investment and Savings banking to be offered at one institution. Chartered as a financial institution under the guidance of the OCC, SEC Protection of PII Vendor Security Breach Notification Required Information Security Function SOX Sarbanes – Oxley act required controls be maintained around financial reporting data. Those controls must be certified by independent 3rd party Publically traded companies Integrity of Accounting Data Self –Assessment Program Attestation of Controls PCI Payment Card Industry Standard requires the protection of cardholder account information Companies Processing Payment card Information Requirements Based on Annual Transaction Volumes Encryption or Obfuscation of Account Numbers Annual Assessment Program Attestation of Controls FISMA Federal Information Security Management Act Requires Institutions Gathering or Processing Information on the Governments behalf Handle that data according to risk based standards Contractual Requirements Stipulation of Certain Grants or Information Sharing Agreements Encryption of Sensitive Information Risk Assessment Program Identification and Notification of Breach State Breach Laws Many States Require that Individuals be Notified in the Event of the Breach of Their Personally Identifiable Information (PII) Public or Private Sector Entities Storing or Processing PII Encryption of PII Breach Notification
- 9. Resources Center for Internet Security https://www.cisecurity.org/ https://www.cisecurity.org/critical-controls/documents/Controls%20Practical%20Guidance%20for%20Web%20v4.pdf OWASP https://www.owasp.org/ SANS https://www.sans.org/ RSA conference slides https://www.rsaconference.com/events/us16/downloads-and-media Cloud Security Alliance https://cloudsecurityalliance.org/
- 10. Building stronger communities through innovative information technology @KingCountyIT Basic Cyber Hyegene Ralph Johnson Chief Information Security and Privacy Officer King County, Washington
- 11. Building stronger communities through innovative information technology What is Information Security? The practice of preventing unauthorized access, use, disclosure, disruption, modification, inspection, recording or destruction of information. Management of Risk to Information and related systems.
- 12. Building stronger communities through innovative information technology Risk Weaknesses in a system or process Effect that the exploitation of a vulnerability by a threat will have on the organization
- 13. Building stronger communities through innovative information technology Humans Behind Threats ThreatsMotivation Terrorist groups sabotage the computer systems that operate our critical infrastructure such as the electrical grid Nation state actors sabotage military and critical infrastructure systems to gain an advantage in the event of conflict Hactivists use computer network exploitation to advance their political or social causes Individuals and sophisticated criminal enterprises steal personal information and extort victims for financial gain Trusted insiders steal proprietary information for personal, financial and ideological reasons Trusted insiders are prone to error and mistakes Nation State actors conduct computer intrusions to steal sensitive state secrets and proprietary information from private companies
- 14. Building stronger communities through innovative information technology Other Threats Environmental Flood Windstorm Volcanic Eruption Earthquake Fire or Explosion Transportation Employee Related Epidemic
- 15. Building stronger communities through innovative information technology Manage Vulnerabilities Through Cyber Hygiene Know what’s connected to and running on your network
- 16. Building stronger communities through innovative information technology Manage Vulnerabilities Through Cyber Hygiene Implement key security settings to help protect your systems
- 17. Building stronger communities through innovative information technology Manage Vulnerabilities Through Cyber Hygiene Limit and manage those who have admin privileges to change, bypass, or override your security settings
- 18. Building stronger communities through innovative information technology Manage Vulnerabilities Through Cyber Hygiene Regularly update all applications, software and operating systems
- 19. Building stronger communities through innovative information technology Manage Vulnerabilities Through Cyber Hygiene Regularize the Top Priorities to form a solid foundation of cybersecurity
- 20. Building stronger communities through innovative information technology
- 21. Cloud vs. On-Premise Security Considerations for Non-Profits Peter Kittas Revelate LLC peter@revelate.io
- 22. What is IT Security? • Three primary elements: ◦ Confidentiality – the data is accessible by only authorized people/systems ◦ Integrity – the data is valid and has not had unauthorized modification ◦ Availability – the resource is accessible when needed • IT security is the culmination of information risk management Peter Kittas | Revelate LLC | peter@revelate.io
- 23. Security Foundations • Crucial that leadership demonstrates it cares about security • Inventory and classify your organization’s critical data • User security awareness training • Physical Security • Use encryption whenever feasible • Trusted computers/devices • (Recoverable) Backups, preferably on-site and off-site Peter Kittas | Revelate LLC | peter@revelate.io
- 24. On-Premise Server Security + Many application choices and ultimate configuration control + Often not dependent on Internet uptime and performance + Data might stay entirely on-site - Managing hardware and software requires ongoing expert attention - Facilities: Dependent on reliable power and HVAC - Physical security: reliable power and HVAC, access to servers and network gear should be controlled Peter Kittas | Revelate LLC | peter@revelate.io
- 25. Cloud Provider Security + Handle all hardware and software installation and maintenance + Typically, very strong physical security controls + Inherent remote access capability + Often provides offsite storage / co-location of data - Less influence over future functionality / changes - May require additional investment in reliability and speed of Internet connection - A larger and more visible target - Anyone in the world can access your login page Peter Kittas | Revelate LLC | peter@revelate.io
- 26. Authentication and Access Control Best Practices • Use strong, unique passwords, along with a password manager • Require two-factor authentication • Role-based access control • Avoid shared accounts • Account / device audit and revocation capability • Review details of password change procedures Peter Kittas | Revelate LLC | peter@revelate.io
- 27. More Cloud Provider Security Considerations • Beware of "free" services • Capability to bulk export all data • Legal and regulatory compliance factors • Examine Knowledge Base/Support pages of provider’s website to gauge their security- mindedness • Does provider conduct independent 3rd party security audits? • Review Terms of Use, Privacy Policy, and Service Level Agreement Peter Kittas | Revelate LLC | peter@revelate.io
- 28. Tonight’s Panelists Mary Gardner Chief Information Security Officer Ralph Johnson Chief Information Security and Privacy Officer Peter Kittas Web and IT Consultant Revelate LLC
- 29. Three Tidbits from Discussion • Don’t underestimate the importance of continuous security training for employees, volunteers, and Board members. • Several attendees recommend Wombat for gamified training • A good first step is to scan your system for vulnerability. • One available tool is Nessus. • All the major browsers are adding changes in 2017 to show more warnings when people visit websites that don’t have the latest security certificates. • Several attendees recommended Let’s Encrypt to enable HTTPS on your website. It’s free and they are a nonprofit too!