Cybersecurity Essential
•
0 likes•57 views
• Describe the tactics, techniques and procedures used by cyber criminals. • Describe the principles of confidentiality, integrity, and availability as they relate to data states and cybersecurity countermeasures. • Describe technologies, products and procedures used to protect confidentiality, ensure integrity and provide high availability. • Explain how cybersecurity professionals use technologies, processes and procedures to defend all components of the network. • Explain the purpose of laws related to cybersecurity.
Report
Share
Report
Share
Download to read offline
Recommended
More Related Content
What's hot
What's hot (19)
Tonex Cybersecurity Fundamentals, Cybersecurity Training and Certification

Tonex Cybersecurity Fundamentals, Cybersecurity Training and Certification
Cybersecurity - Introduction and Preventive Measures

Cybersecurity - Introduction and Preventive Measures
The Ultimate Guide To Cyber Security Certifications

The Ultimate Guide To Cyber Security Certifications
More from Tobia La Marca
More from Tobia La Marca (20)
Recently uploaded
Rohini Sector 6 Call Girls Delhi 9999965857 @Sabina Saikh No Advance

Rohini Sector 6 Call Girls Delhi 9999965857 @Sabina Saikh No AdvanceCall Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
(INDIRA) Call Girl Pune Call Now 8250077686 Pune Escorts 24x7

(INDIRA) Call Girl Pune Call Now 8250077686 Pune Escorts 24x7Call Girls in Nagpur High Profile Call Girls
Dwarka Sector 26 Call Girls | Delhi | 9999965857 🫦 Vanshika Verma More Our Se...

Dwarka Sector 26 Call Girls | Delhi | 9999965857 🫦 Vanshika Verma More Our Se...Call Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
Russian Call Girls in %(+971524965298 )# Call Girls in Dubai

Russian Call Girls in %(+971524965298 )# Call Girls in DubaiDubai call girls 971524965298 Call girls in Bur Dubai
Recently uploaded (20)
Call Girls In Pratap Nagar Delhi 💯Call Us 🔝8264348440🔝

Call Girls In Pratap Nagar Delhi 💯Call Us 🔝8264348440🔝
WhatsApp 📞 8448380779 ✅Call Girls In Mamura Sector 66 ( Noida)

WhatsApp 📞 8448380779 ✅Call Girls In Mamura Sector 66 ( Noida)
Rohini Sector 6 Call Girls Delhi 9999965857 @Sabina Saikh No Advance

Rohini Sector 6 Call Girls Delhi 9999965857 @Sabina Saikh No Advance
(INDIRA) Call Girl Pune Call Now 8250077686 Pune Escorts 24x7

(INDIRA) Call Girl Pune Call Now 8250077686 Pune Escorts 24x7
Call Girls In Defence Colony Delhi 💯Call Us 🔝8264348440🔝

Call Girls In Defence Colony Delhi 💯Call Us 🔝8264348440🔝
Moving Beyond Twitter/X and Facebook - Social Media for local news providers

Moving Beyond Twitter/X and Facebook - Social Media for local news providers
Dwarka Sector 26 Call Girls | Delhi | 9999965857 🫦 Vanshika Verma More Our Se...

Dwarka Sector 26 Call Girls | Delhi | 9999965857 🫦 Vanshika Verma More Our Se...
✂️ 👅 Independent Andheri Escorts With Room Vashi Call Girls 💃 9004004663

✂️ 👅 Independent Andheri Escorts With Room Vashi Call Girls 💃 9004004663
Low Rate Young Call Girls in Sector 63 Mamura Noida ✔️☆9289244007✔️☆ Female E...

Low Rate Young Call Girls in Sector 63 Mamura Noida ✔️☆9289244007✔️☆ Female E...
GDG Cloud Southlake 32: Kyle Hettinger: Demystifying the Dark Web

GDG Cloud Southlake 32: Kyle Hettinger: Demystifying the Dark Web
AWS Community DAY Albertini-Ellan Cloud Security (1).pptx

AWS Community DAY Albertini-Ellan Cloud Security (1).pptx
Call Girls Service Chandigarh Lucky ❤️ 7710465962 Independent Call Girls In C...

Call Girls Service Chandigarh Lucky ❤️ 7710465962 Independent Call Girls In C...
Hot Call Girls |Delhi |Hauz Khas ☎ 9711199171 Book Your One night Stand

Hot Call Girls |Delhi |Hauz Khas ☎ 9711199171 Book Your One night Stand
Russian Call Girls in %(+971524965298 )# Call Girls in Dubai

Russian Call Girls in %(+971524965298 )# Call Girls in Dubai
VIP Model Call Girls Hadapsar ( Pune ) Call ON 9905417584 Starting High Prof...

VIP Model Call Girls Hadapsar ( Pune ) Call ON 9905417584 Starting High Prof...
Call Girls In Ashram Chowk Delhi 💯Call Us 🔝8264348440🔝

Call Girls In Ashram Chowk Delhi 💯Call Us 🔝8264348440🔝
DDoS In Oceania and the Pacific, presented by Dave Phelan at NZNOG 2024

DDoS In Oceania and the Pacific, presented by Dave Phelan at NZNOG 2024
Russian Call girl in Ajman +971563133746 Ajman Call girl Service

Russian Call girl in Ajman +971563133746 Ajman Call girl Service
CALL ON ➥8923113531 🔝Call Girls Lucknow Lucknow best sexual service Online

CALL ON ➥8923113531 🔝Call Girls Lucknow Lucknow best sexual service Online
(+971568250507 ))# Young Call Girls in Ajman By Pakistani Call Girls in ...

(+971568250507 ))# Young Call Girls in Ajman By Pakistani Call Girls in ...
Cybersecurity Essential
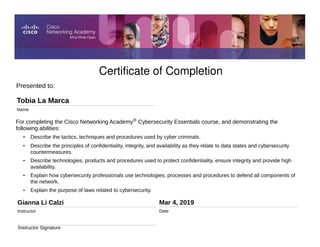
- 1. Certificate of Completion Presented to: Tobia La Marca Name Gianna Li Calzi Instructor Mar 4, 2019 Date Instructor Signature For completing the Cisco Networking Academy® Cybersecurity Essentials course, and demonstrating the following abilities: • Describe the tactics, techniques and procedures used by cyber criminals. • Describe the principles of confidentiality, integrity, and availability as they relate to data states and cybersecurity countermeasures. • Describe technologies, products and procedures used to protect confidentiality, ensure integrity and provide high availability. • Explain how cybersecurity professionals use technologies, processes and procedures to defend all components of the network. • Explain the purpose of laws related to cybersecurity.
