redone pdf of prior slideshow fix errors
•
0 likes•148 views
the keynote to ppt conversion was bad, this hopefully fixed it
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
More Related Content
Featured
Featured (20)
Product Design Trends in 2024 | Teenage Engineerings

Product Design Trends in 2024 | Teenage Engineerings
How Race, Age and Gender Shape Attitudes Towards Mental Health

How Race, Age and Gender Shape Attitudes Towards Mental Health
AI Trends in Creative Operations 2024 by Artwork Flow.pdf

AI Trends in Creative Operations 2024 by Artwork Flow.pdf
Content Methodology: A Best Practices Report (Webinar)

Content Methodology: A Best Practices Report (Webinar)
How to Prepare For a Successful Job Search for 2024

How to Prepare For a Successful Job Search for 2024
Social Media Marketing Trends 2024 // The Global Indie Insights

Social Media Marketing Trends 2024 // The Global Indie Insights
Trends In Paid Search: Navigating The Digital Landscape In 2024

Trends In Paid Search: Navigating The Digital Landscape In 2024
5 Public speaking tips from TED - Visualized summary

5 Public speaking tips from TED - Visualized summary
Google's Just Not That Into You: Understanding Core Updates & Search Intent

Google's Just Not That Into You: Understanding Core Updates & Search Intent
The six step guide to practical project management

The six step guide to practical project management
Beginners Guide to TikTok for Search - Rachel Pearson - We are Tilt __ Bright...

Beginners Guide to TikTok for Search - Rachel Pearson - We are Tilt __ Bright...
redone pdf of prior slideshow fix errors
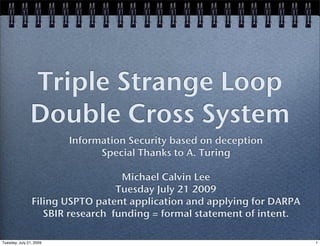
- 1. Triple Strange Loop Double Cross System Information Security based on deception Special Thanks to A. Turing Michael Calvin Lee Tuesday July 21 2009 Filing USPTO patent application and applying for DARPA SBIR research funding = formal statement of intent. Tuesday, July 21, 2009 1
- 2. Single Strange Loop send lots of data most is false some is true only Valid Participants know the difference Tuesday, July 21, 2009 2
- 3. Problem: inefficient! most data is noise and a waste of bandwidth high noise/signal ratio to be secure 3 Tuesday, July 21, 2009 3
- 4. Triple Strange Loop Most Data is true, a tiny bit is false use p2p relay mesh clusters to send data Multipoint to Multipoint efficiency The valid recipient is only known to participants The context of data only known to recipient. 4 Tuesday, July 21, 2009 4
- 5. Principles of Operation You can intercept data, but you don’t know who it’s intended for Even if you determine that, you don’t know the context If you get both of those, there is a question of is it true or not. 5 Tuesday, July 21, 2009 5
- 6. Algorithm! Representation of base 10 integer as base phi positional numeral system Reduction to minimal representation in base phi Mathematically offers two unique properties for data security third loop is based on a quormum/ consensus prototcol to clarify truth 6 Tuesday, July 21, 2009 6
- 7. Security is Prove-able! By unique two properties of base phi representation and reduction to minimalist representation Truth is that the unique properties hold after the random modifier is applied The nodes don’t even know until a message block decode is agreed by consensus 7 Tuesday, July 21, 2009 7
- 8. Explanation of last bit! The call to clarify is based on autonomous systems and some random variable can be made at any time and changes all three strange loops only after message block is received by all does ‘what to do with data’ step used 8 Tuesday, July 21, 2009 8
- 9. The Beauty of It Transmission is automated and does not require human intervention Interception and decryption does knowledge of base phi numerals, private key of all peers, and autonomous systems to be certain anything is true should drive most people nuts 9 Tuesday, July 21, 2009 9
- 10. Conclusion Without being certain of all three double cross loops are actually true... what use is the data? nagging doubts is an intentional design aspect... Tuesday, July 21, 2009 10