Mobile Vision 2020
•
4 recomendaciones•1,524 vistas
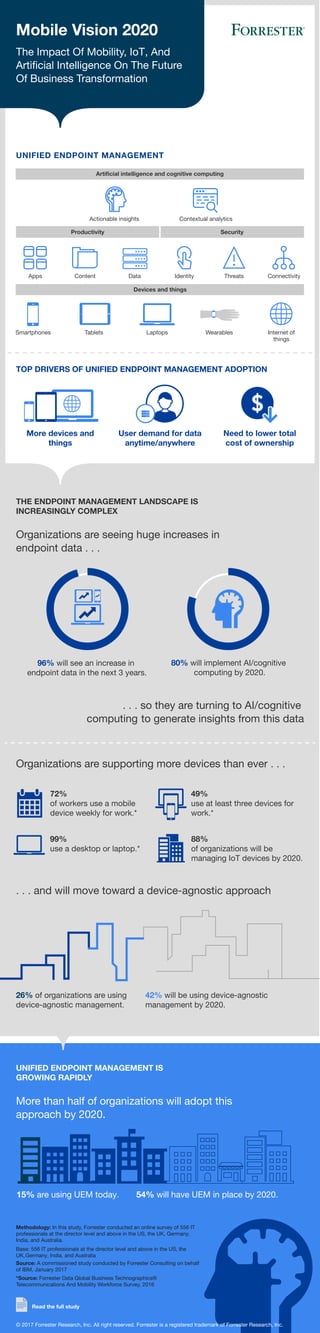
Organizations are supporting more devices than ever and unified endpoint management is growing rapidly. More than half of organizations will adopt this approach by 2020. This infographic demonstrates the impact of mobility, Internet of Things (IoT), and artificial intelligence on the future of business transformation. To learn more, read the complete Forrester report, "Mobile Vision 2020" at https://ibm.co/2pxhisB.
Denunciar
Compartir
Denunciar
Compartir
Descargar para leer sin conexión
Recomendados
Recomendados
Securing the internet of things: The conversation you need to have with your CEO

Securing the internet of things: The conversation you need to have with your CEOThe Economist Media Businesses
Más contenido relacionado
La actualidad más candente
Securing the internet of things: The conversation you need to have with your CEO

Securing the internet of things: The conversation you need to have with your CEOThe Economist Media Businesses
La actualidad más candente (20)
Recent ECB/ EBA regulations how they will impact European banks in 2016

Recent ECB/ EBA regulations how they will impact European banks in 2016
The ROI on Intrusion Prevention: Protecting Both Your Network & Investment

The ROI on Intrusion Prevention: Protecting Both Your Network & Investment
How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration

How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration
Securing the C-Suite: Cybersecurity Perspectives from the Boardroom

Securing the C-Suite: Cybersecurity Perspectives from the Boardroom
Cybersecurity in the Cognitive Era: Priming Your Digital Immune System

Cybersecurity in the Cognitive Era: Priming Your Digital Immune System
Security Intelligence: Finding and Stopping Attackers with Big Data Analytics

Security Intelligence: Finding and Stopping Attackers with Big Data Analytics
IBM Security AppExchange Spotlight: Threat Intelligence & Monitoring Microso...

IBM Security AppExchange Spotlight: Threat Intelligence & Monitoring Microso...
QRadar & XGS: Stopping Attacks with a Click of the Mouse

QRadar & XGS: Stopping Attacks with a Click of the Mouse
Orchestrate Your Security Defenses; Protect Against Insider Threats 

Orchestrate Your Security Defenses; Protect Against Insider Threats
How to Improve Threat Detection & Simplify Security Operations

How to Improve Threat Detection & Simplify Security Operations
Securing the internet of things: The conversation you need to have with your CEO

Securing the internet of things: The conversation you need to have with your CEO
Internet of Things Security: IBM HorizonWatch 2016 Trend Brief

Internet of Things Security: IBM HorizonWatch 2016 Trend Brief
IBM Mobile Security: A Comprehensive Approach to Securing and Managing the Mo...

IBM Mobile Security: A Comprehensive Approach to Securing and Managing the Mo...
The Next Stage of Fraud Protection: IBM Security Trusteer Fraud Protection Suite

The Next Stage of Fraud Protection: IBM Security Trusteer Fraud Protection Suite
Similar a Mobile Vision 2020
Similar a Mobile Vision 2020 (20)
Sécurité Mobile : Votre Entreprise est-elle préparée pour 2020?

Sécurité Mobile : Votre Entreprise est-elle préparée pour 2020?
Survey Report: Managing BYOD in Corporate Environments

Survey Report: Managing BYOD in Corporate Environments
Surviving the mobile invasion - They're spreading fast and they're vulnerable

Surviving the mobile invasion - They're spreading fast and they're vulnerable
Annette Zimmermann (Gartner): Gartner Strategic Predictions: What Will Disrup...

Annette Zimmermann (Gartner): Gartner Strategic Predictions: What Will Disrup...
Exciting it trends in 2015 why you should consider shifting and upgrading yo...

Exciting it trends in 2015 why you should consider shifting and upgrading yo...
The Organizational Psychology of the Internet of Things: How to Use Technolog...

The Organizational Psychology of the Internet of Things: How to Use Technolog...
Driving Towards an IoT Payoff: Keep it Simple – It’s Not Just About the Techn...

Driving Towards an IoT Payoff: Keep it Simple – It’s Not Just About the Techn...
Goode Intelligence: Next-Generation Authentication for the Mobile-Ready Enter...

Goode Intelligence: Next-Generation Authentication for the Mobile-Ready Enter...
Ibm's global ai adoption index 2021 executive summary

Ibm's global ai adoption index 2021 executive summary
Top 8 Tips For Business Technology Strategy in 2015

Top 8 Tips For Business Technology Strategy in 2015
Más de IBM Security
Más de IBM Security (20)
Leaders & Laggards: The Latest Findings from the Ponemon Institute’s Study on...

Leaders & Laggards: The Latest Findings from the Ponemon Institute’s Study on...
The Resilient End-of-Year Review: The Top Cyber Security Trends in 2018 and P...

The Resilient End-of-Year Review: The Top Cyber Security Trends in 2018 and P...
Leveraging Validated and Community Apps to Build a Versatile and Orchestrated...

Leveraging Validated and Community Apps to Build a Versatile and Orchestrated...
Accelerating SOC Transformation with IBM Resilient and Carbon Black

Accelerating SOC Transformation with IBM Resilient and Carbon Black
Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence

Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence
Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...

Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...
Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...

Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...
Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...

Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...
See How You Measure Up With MaaS360 Mobile Metrics

See How You Measure Up With MaaS360 Mobile Metrics
Nowhere to Hide: Expose Threats in Real-time with IBM QRadar Network Insights

Nowhere to Hide: Expose Threats in Real-time with IBM QRadar Network Insights
Safeguard Healthcare Identities and Data with Identity Governance and Intelli...

Safeguard Healthcare Identities and Data with Identity Governance and Intelli...
Cybersecurity In The Cognitive Era: Priming Your Digital Immune System

Cybersecurity In The Cognitive Era: Priming Your Digital Immune System
Último
Último (20)
Transcript: New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024

Transcript: New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024
Generative AI for Technical Writer or Information Developers

Generative AI for Technical Writer or Information Developers
The Ultimate Guide to Choosing WordPress Pros and Cons

The Ultimate Guide to Choosing WordPress Pros and Cons
Arizona Broadband Policy Past, Present, and Future Presentation 3/25/24

Arizona Broadband Policy Past, Present, and Future Presentation 3/25/24
How AI, OpenAI, and ChatGPT impact business and software.

How AI, OpenAI, and ChatGPT impact business and software.
Potential of AI (Generative AI) in Business: Learnings and Insights

Potential of AI (Generative AI) in Business: Learnings and Insights
Merck Moving Beyond Passwords: FIDO Paris Seminar.pptx

Merck Moving Beyond Passwords: FIDO Paris Seminar.pptx
Assure Ecommerce and Retail Operations Uptime with ThousandEyes

Assure Ecommerce and Retail Operations Uptime with ThousandEyes
How to Effectively Monitor SD-WAN and SASE Environments with ThousandEyes

How to Effectively Monitor SD-WAN and SASE Environments with ThousandEyes
[Webinar] SpiraTest - Setting New Standards in Quality Assurance![[Webinar] SpiraTest - Setting New Standards in Quality Assurance](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Webinar] SpiraTest - Setting New Standards in Quality Assurance](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Webinar] SpiraTest - Setting New Standards in Quality Assurance
The Future Roadmap for the Composable Data Stack - Wes McKinney - Data Counci...

The Future Roadmap for the Composable Data Stack - Wes McKinney - Data Counci...
Testing tools and AI - ideas what to try with some tool examples

Testing tools and AI - ideas what to try with some tool examples
Unleashing Real-time Insights with ClickHouse_ Navigating the Landscape in 20...

Unleashing Real-time Insights with ClickHouse_ Navigating the Landscape in 20...
Mobile Vision 2020
- 1. More devices and things Mobile Vision 2020 UNIFIED ENDPOINT MANAGEMENT TOP DRIVERS OF UNIFIED ENDPOINT MANAGEMENT ADOPTION THE ENDPOINT MANAGEMENT LANDSCAPE IS INCREASINGLY COMPLEX More than half of organizations will adopt this approach by 2020. UNIFIED ENDPOINT MANAGEMENT IS GROWING RAPIDLY User demand for data anytime/anywhere Need to lower total cost of ownership Source: A commissioned study conducted by Forrester Consulting on behalf of IBM, January 2017 *Source: Forrester Data Global Business Technographics® Telecommunications And Mobility Workforce Survey, 2016 © 2017 Forrester Research, Inc. All right reserved. Forrester is a registered trademark of Forrester Research, Inc. Read the full study Artificial intelligence and cognitive computing Devices and things Productivity Security Actionable insights Apps Smartphones Tablets Laptops Wearables Internet of things Content Data Identity Threats Connectivity Contextual analytics Organizations are seeing huge increases in endpoint data . . . Organizations are supporting more devices than ever . . . . . . and will move toward a device-agnostic approach The Impact Of Mobility, IoT, And Artificial Intelligence On The Future Of Business Transformation 26% of organizations are using device-agnostic management. 42% will be using device-agnostic management by 2020. 15% are using UEM today. 54% will have UEM in place by 2020. 80% will implement AI/cognitive computing by 2020. 96% will see an increase in endpoint data in the next 3 years. Base: 556 IT professionals at the director level and above in the US, the UK,Germany, India, and Australia Methodology: In this study, Forrester conducted an online survey of 556 IT professionals at the director level and above in the US, the UK, Germany, India, and Australia. 72% of workers use a mobile device weekly for work.* 49% use at least three devices for work.* 99% use a desktop or laptop.* 88% of organizations will be managing IoT devices by 2020. . . . so they are turning to AI/cognitive computing to generate insights from this data
