Intellectual Property Law Roundtable - What Businesses Need to Know | Los Angeles Business Journal
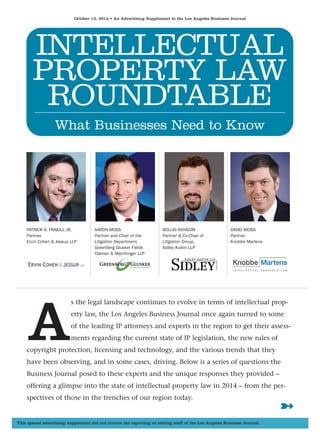
- 1. October 13, 2014 • An Advertising Supplement to the Los Angeles Business Journal INTELLECTUAL PROPERTY LAW ROUNDTABLE What Businesses Need to Know PATRICK A. FRAIOLI, JR. Partner, Ervin Cohen & Jessup LLP AARON MOSS Partner and Chair of the Litigation Department, Greenberg Glusker Fields Claman & Machtinger LLP ROLLIN RANSOM Partner & Co-Chair of Litigation Group, Sidley Austin LLP DAVID WEISS Partner, Knobbe Martens As the legal landscape continues to evolve in terms of intellectual prop-erty law, the Los Angeles Business Journal once again turned to some of the leading IP attorneys and experts in the region to get their assess-ments regarding the current state of IP legislation, the new rules of copyright protection, licensing and technology, and the various trends that they have been observing, and in some cases, driving. Below is a series of questions the Business Journal posed to these experts and the unique responses they provided – offering a glimpse into the state of intellectual property law in 2014 – from the per-spectives of those in the trenches of our region today. This special advertising supplement did not involve the reporting or editing staff of the Los Angeles Business Journal. ➼
- 2. 20 AN ADVERTISING SUPPLEMENT TO THE LOS ANGELES BUSINESS JOURNAL OCTOBER 13, 2014 ◆ How has the intellectual property law land-scape changed over the last five years? Weiss: As intellectual property, and patents in partic-ular, has become more critical to the economy, the Supreme Court has sought to limit the breadth of patent protection and Congress has made it easier to challenge patents within the U.S. Patent Office. In the past term, the Court limited the eligibility for patent protection of certain software inventions, which has made it more difficult to find a party libel for indirect infringement, has made it easier to inval-idate patents for indefiniteness, and has made it easi-er for prevailing parties in patent litigation to be awarded attorney fees. The Federal Circuit has made it more difficult for patent plaintiffs to collect huge awards. Under the new procedures for challenging patents in the U.S. Patent Office, a high percentage of patents that have undergone such procedures have been invalidated. Ransom: The digital revolution has led to great tech-nological and economic advances; at times, however, intellectual property law has struggled to keep up. Each new advance in how information is stored, communicated, or made available brings with it new opportunities for infringement or other rights viola-tions. Laws that were passed decades ago are not always well suited to address these issues, and Congress has had difficulty reaching agreement on revisions that balance the need to protect innovation with the need to facilitate advances in the arts and sciences. The “solutions” often generate more dis-putes. Perhaps as a result, the Supreme Court has recently been more active in intellectual property cases, a trend that is likely to continue. In areas not exclusively governed by federal law (for example, data breaches), state legislatures have been extremely active (or more accurately, reactive) in passing new legislation; that trend is also likely to continue. ◆ Why has the Supreme Court been so active in IP cases in the past few terms, and what does it portend for the future? Ransom: There are a few things at work here. First, with respect to patent law, it seems clear that the Supreme Court has no confidence in the Federal Circuit Court of Appeals. Of the six patent cases heard in the most recent term, the Court unani-mously reversed the Federal Circuit in five of them, continuing a trend seen in recent years. Second, the Court also seems intent on narrowing the scope of patent protection – among other things, its decisions tightened the requirements for patenting computer software (Alice Corp.) and proving induced infringe-ment (Limelight Networks) and relaxed the standard for invalidating a patent based on indefiniteness (Nautilus). And finally, the number of IP cases of all varieties that have been taken in recent years sug-gests that the Court recognizes the fundamental importance of intellectual property issues to the American economy, making it likely that the Supreme Court’s interest in these matters will contin-ue in coming years. Weiss: Ten out of the 67 cases heard by the Supreme Court in its last term were intellectual property cases, including six patent cases. This reflects the Supreme Courts understanding of the increasing importance that intellectual property plays in today’s economy. The Court appears to be sensitive to complaints that rather than encouraging innova-tion, patents, especially when asserted by non-prac-ticing entities, often hinder innovation. In response, the Court has sought to limit the breadth of patent protection. The Court limited the eligibility for patent protection of certain software inventions, which has made it more difficult to find a party libel for indirect infringement, has made it easier to invalidate patents for indefiniteness, and has made it easier for prevailing parties in patent litigation to be awarded attorney fees. We can expect to see the Supreme Court continue to weigh-in on intellectual property matters for the foreseeable future. ◆ What was the most surprising IP decision the Supreme Court issued last term? Moss: Petrella v. MGM surprised me the most. Essentially, the Court ruled that the equitable doc-trine of laches could not be used to prevent a plain-tiff from suing for monetary damages in a copyright infringement suit – even if the defendant’s infringing conduct first began decades earlier and the plaintiff delayed filing a lawsuit during that time. Even more surprising, the Court explicitly endorsed the practice of plaintiffs watching and waiting to see whether the alleged infringing motion picture or other product is going to make money before filing a complaint. This is going to make it more difficult for studios and other content creators to get long-delayed claims dis-missed early in litigation. Ransom: I was surprised by the Court’s decision in Petrella v. MGM, in which the Court held that the defense of laches (a plaintiff’s unreasonable delay in bringing suit, coupled with resulting prejudice to the defendant) does not bar a claim for damages under the Copyright Act, so long as the claim is brought within the Copyright Act’s statute of limitations. Because of the way the copyright statute of limita-tions works, a claim is timely as long as any act of infringement has occurred within the three years preceding suit. The consequence of the Court’s ruling is that copyright infringement that commenced decades ago is still actionable today, so long as there has also been some recent act of infringement, even if the plaintiff has long known about the claim, unrea-sonably waited decades to assert it, and the defen-dant was prejudiced by the delay (e.g., by the inter-vening death of a key witness). This raises the prospect of a new wave of “old” infringement claims, and reduces the ability of defendants to fight them. ◆ In light of recent Supreme Court decisions in false advertising cases, do you see any likely trends in false advertising litigation? Ransom: Perhaps the most significant development in this space was in POM Wonderful LLC v. The Coca- Cola Company. The Supreme Court held that com-petitors can challenge food and beverage labeling claims as false or misleading, even where the label meets the requirements of the federal Food, Drug, and Cosmetic Act. This ruling has the potential to expand false advertising litigation in this industry. At a minimum, it should prompt food and beverage companies to scrutinize their own product labeling, as well as that of their competitors, even more close-ly than they might have in the past. In certain respects, the Court’s opinion appears to be limited in scope – language in the opinion suggests that its rationale would not apply to state-law based con-sumer class actions, or to drug (rather than food and beverage) labeling – but only time will tell. ◆ Is there pending new IP legislation coming soon? If so, does this stand to help or hinder existing businesses? Moss: Among other things, there have been some very preliminary discussions about amending the Copyright Act to address the Supreme Court’s ruling last year in Kirtsaeng v. John Wiley & Sons, Inc., which held that the first sale doctrine applies to copyright-ed goods manufactured abroad and imported into the United States. The first sale doctrine is what allows people to sell DVDs on eBay and for libraries to lend books without needing permission from the copyright owner. I litigated the foreign manufacture issue in the landmark Costco v. Omega case. A change in the law would allow manufacturers more control over the distribution of their goods, but would give retailers less control over the resale of those goods. ◆ What are some common copyright issues that small businesses face? How can they best be addressed? Ransom: The biggest issue is a lack of understanding of the fundamentals of copyright law. A common misconception is that if a photograph is available online, then it is free for the business to use. Or that music or video may be used in a website with-out permission if credit is given to the copyright owner. Or that third party works can be used and copied so long as they are not sold or profit gener-ating. A related problem is a relative lack of internal controls over the conduct of employees (who may INTELLECTUAL PROPERTY LAW ROUNDTABLE ‘The failure to encrypt covered data on mobile devices, and the widespread, careless use of one password across all of a user’s devices, are common, ticking time bombs.’ PATRICK A. FRAIOLI, JR. ‘The digital revolution has led to great technological and economic advances; at times, however, intellec-tual property law has struggled to keep up. Each new advance in how information is stored, communicat-ed, or made available brings with it new opportunities for infringement or other rights violations.’ ROLLIN RANSOM 22➼
- 3. OCTOBER 13, 2014 AN ADVERTISING SUPPLEMENT TO THE LOS ANGELES BUSINESS JOURNAL 21 GreenbergGlusker.com The Nexus of Entertainment and Tech We counsel emerging companies and industry leaders in intellectual property-driven industries on strategies to protect, defend and exploit their intellectual property. Charles Shephard 310.201.7494 CShephard@greenbergglusker.com Aaron Moss 310.785.6814 AMoss@greenbergglusker.com Jesse Saivar 310.201.7549 JSaivar@greenbergglusker.com
- 4. 22 AN ADVERTISING SUPPLEMENT TO THE LOS ANGELES BUSINESS JOURNAL OCTOBER 13, 2014 INTELLECTUAL PROPERTY LAW ROUNDTABLE ‘One common issue is that businesses will often hire photographers or marketing agencies without negotiating or fully understanding the copyright ownership of the resulting photos and materials.’ AARON MOSS ‘A startup’s most important intellectu-al property is often created at the out-set. Indeed, startups are often founded to commercialize an innovative idea. Therefore it is critical that a startup allocate a portion of its limited resources to protect its most important inventions via the patent process.’ DAVID WEISS labor under some or all of these misconceptions) – no in-house lawyer, risk manager, or other mecha-nism in place to ensure compliance with copyright law. Education is key – for example, a “copyright basics” presentation by an experienced attorney – coupled with regular review of business-generated materials to ensure compliance. Moss: One common issue is that businesses will often hire photographers or marketing agencies without negotiating or fully understanding the copyright ownership of the resulting photos and materials. Without a written agreement, the photographer or other commissioned party will usually own the copy-right, so it’s important to spell out in advance the precise scope of the hiring company’s license to use the materials. The commissioning business will be better off obtaining full rights if this can be negotiat-ed, but the parties should at the very least come to an agreement in advance on the type, extent and duration of the company’s use – before disputes arise later on. ◆ How real is the threat of injunctive relief in copyright and trademark actions? Is an injunction likely to follow if there is a find-ing of liability? Ransom: It used to be that injunctive relief was fairly automatic (or at least easier to obtain), because a finding of liability typically carried with it a pre-sumption of irreparable harm. However, in eBay v. MercExchange, the Supreme Court rejected a similar presumption in the patent context, requiring a show-ing of irreparable harm to obtain an injunction. Since the eBay decision in 2006, several courts, including the Ninth Circuit, have extended its hold-ing to copyright and trademark infringement claims as well. The impact of these rulings is that it will be harder for plaintiffs to obtain injunctions, even where they have prevailed on the merits of their claims, as they will need to demonstrate that they will suffer irreparable harm from the violation, rather than relying on a presumption of such harm. ◆ How “safe” is the safe harbor under the Digital Millennium Copyright Act? Moss: The DMCA safe harbor completely immunizes a service provider from liability for copyright infringement claims if it implements particular notice and takedown procedures. But uncertainty arises from the requirement that the service provider must not have actual knowledge that the material in question is infringing or be aware of facts or circum-stances that make it apparent that there is infringing activity. The question is how to define “knowledge.” There have been a number of circuit-level cases dis-cussing the issue, but no guidance from the Supreme Court. In the Ninth Circuit, there is no safe harbor when the provider is subjectively aware of facts that would have made the specific infringement “objec-tively” obvious to a reasonable person. I suppose that’s pretty safe, if you can figure out what it means. Ransom: This is an ongoing battle between content owners and online service providers. In the absence of either actual or so-called “red flag” knowledge of specific acts infringement, and assuming compliance with the other requirements of the statute, courts have generally concluded that online service providers are insulated from claims of copyright infringement occurring on their sites. However, the level of awareness necessary to satisfy actual or “red flag” knowledge – among other things – remains actively in dispute. In the future, courts will be look-ing at that question from various angles, including whether viewing material online that contains all or virtually all of another’s well-known copyrighted work constitutes actual or “red flag” knowledge of infringement of that work, and whether an online service provider’s “willful blindness” to infringement prevents it from taking advantage of the safe harbor. ◆ The Trademark Trial and Appeal Board recently cancelled several Washington Redskins trademark registrations, conclud-ing they were disparaging of Native Americans. How significant is the threat of a “disparaging mark” challenge to trademark owners? Moss: There’s a misconception that if a trademark is cancelled (or refused for registration) because it con-sists of “immoral, deceptive, or scandalous matter,” this means that the owner does not have the right to use or enforce the mark. The owner may still have common law rights that would prevent third parties from infringing the mark. This being said, there are a number of benefits offered by federal registration, including presumptions of ownership and nation-wide rights. Until the Redskins’ case is resolved on appeal, the mark continues to be registered and the owner retains the benefits of the federal registration. Ransom: Although the TTAB decision received a great deal of news coverage, the practical impact for trade-mark owners is fairly modest. The standard for find-ing a registered mark disparaging was, and remains, whether the mark was disparaging when registered. So even if the meaning of mark changes over time, a trademark registration is not in jeopardy unless the mark was disparaging at the time of the original reg-istration. Moreover, cancellation of a registration of a disparaging mark does not prevent enforcement of common law rights in the mark, though there may, of course, be public relations consequences associat-ed with using and enforcing a disparaging mark. ◆ The news is full of stories about massive cor-porate data breaches; what exposure do busi-nesses in California face from data breaches? Fraioli: Well, there is a large company like Target, with approximately $150 million specifically result-ing from this breach, to date. Some analysts esti-mate that the total, future loss may reach $1 bil-lion. On the other hand, as Stan Stahl, President of ISSA-LA always reminds audiences, every year approximately 30% of all small to medium sized businesses (250 employees are less) get hit with a cyberattack; of that group, 60% are out of business in less than 6 months. In IP litigation, we often speak of “Bet the Company Lawsuits.” If you are a Small to Medium Sized Business in California, there is a good chance that a data breach will be a Bet Your Company event. Ransom: It is often said that it’s not whether your business will suffer a data breach, but when. Every business in California faces potential harm from data breaches and should take measures to minimize both the risks of a breach and the level of harm. Data breaches have both direct and indirect effects on business. Not only does the business have to spend money –the reported average is over $5 million – to resolve a data breach and address the underlying cause, but it must also deal with reputational harm, loss of customer loyalty, negative press, and, increas-ingly, litigation. The California legislature has also been active in this area. Most recently, the legislature amended the state’s data breach notification law to expand the scope of businesses covered by data secu-rity requirements, among other measures. ◆ What advice would you give to an early stage technology company with respect to protecting its intellectual property assets? Weiss: A startup’s most important intellectual proper-ty is often created at the outset. Indeed, startups are often founded to commercialize an innovative idea. Therefore it is critical that a startup allocate a portion of its limited resources to protect its most important inventions via the patent process. If a patent applica-tion is not timely filed, a startup may lose its ability to later seek patent protection for its key inventions. Additionally, such key inventive ideas may have been created by a founder prior to the formation of the startup, and it is vital that such inventive ideas and other intellectual property are assigned to the startup. If a startup is outsourcing work to contrac-tors, it is essential that appropriate assignments are executed to ensure that the startup has ownership of the work. Fraioli: Protect the IP like it is the Crown Jewels. Identify the likely threats, make available signifi-cant corporate resources for IP protection; actively manage a comprehensive IP Protection Program — 24➼ Continued from page 20
- 5. OCTOBER 13, 2014 AN ADVERTISING SUPPLEMENT TO THE LOS ANGELES BUSINESS JOURNAL 23 Your IP is like your child: It needs care and protection. And it needs to get a job. The ECJ IP Workgroup provides counsel and guidance so your IP brings home a growing paycheck without worrying about bullies, patent trolls, or other threats.We’re part tutor, part bodyguard, part business manager. When it comes to your pride and joy, depend on the IP Workgroup at ECJ.We take your business as personally as you do. 9401 Wilshire Blvd., 9th Floor, Beverly Hills, CA 90212 310.273.6333 ȧ www.ecjlaw.com
- 6. 24 AN ADVERTISING SUPPLEMENT TO THE LOS ANGELES BUSINESS JOURNAL OCTOBER 13, 2014 INTELLECTUAL PROPERTY LAW ROUNDTABLE put a C-Suite Executive in charge; constantly mon-itor for threats and take active steps to thwart them, including cease-and-desist letters and actions for Declaratory Relief where warranted; regularly re-assess your strategy and tactics. At the same time, you must monetize your IP. Be equally aggressive in seeking licenses and other monetiza-tion opportunities. Focus; Execute; Re-assess; Re-focus. Rinse; Repeat. ◆ With all of the data breach incidents being reported, do businesses need Cyber-insur-ance? What does it cover a business for, in the event of a data breach? What if the busi-ness in question is a professional firm, and has client information? Does that make a dif-ference? Fraioli: According to the Ponemon Institute, the average cost of a data breach was approximately $3.5 million in 2013. Stuart Pardau, noted privacy expert and Ponemon Institute Fellow, believes the cost is likely to continue to rise, especially if more class action attorneys are successful in having class-es certified, as in last year’s ComScore case, which settled for $14 million. Attorneys continue to invest in these cases, and Pardau believes these trends will only accelerate. Increasingly, professional firms are being targeted. They often hold essential subsets of client information (the wheat without all the chaff) and their security profile can be more lax. An issue to review before a breach is that a firm’s professional liability policy may cover its client’s information but not the firm’s, and another policy may cover its own information. ◆ What are the most important steps busi-nesses in Los Angeles can/should take before, during and after a data breach incident? Ransom: The most important steps a business can take are preventative. Good internal procedures regarding safeguarding information – at time of col-lection, use and disposal – are crucial. Just as impor-tant is the establishment of data breach response protocols and a trained team. Businesses may also consider purchasing cyber insurance to offset costs in the event of a data breach. Once a breach occurs, a business must immediately implement its response protocols, including stopping further data loss, hiring a forensics team, and beginning any required notification process – to law enforcement, government entities, and customers. The business will also need a plan for making public announce-ments, particularly in the era of social media, where brand reputations can suffer quickly. A good plan will also address how to communicate with cus-tomers regarding the breach, risks they may face, steps to protect themselves, and the availability of any credit monitoring or identity protection servic-es provided by the company. Fraioli: Form a Data Governance Team today: Risk Management/Insurance, Attorneys (In-House and Outside Counsel), IT/Security, Corporate Communications. Build the Preparedness/Response Plan. Use it throughout your Security Event Life Cycle, the four stages of which are: Protect, Detect, Respond, Recover. It is critical to engage the C-Suite and the Board: Cybersecurity is a risk management issue, not an IT matter. You must always know (by regular reviews) what data you have, why you have it, how you store it, how you secure it, and why/whether you still need to keep it. You cannot lose data that you don’t have. Risk cannot be man-aged only after a breach occurs – panic and confusion will have set in — chaos and denial will infiltrate your statements to the outside world. Clear, effective inquiries will lead to calm communication of facts, showing a company in control of itself, its systems, and the story. ◆ Increasingly, companies are choosing to let their employees “Bring Your Own Device” (BYOD), rather than buying everyone the same device. What are the legal and practical implications of this policy in California today, when both mobile devices and data breaches are so prevalent? Fraioli: The real paradigm shift wrought by mobile devices has been in employee attitudes towards data and connectivity. It is now more likely that a depart-ing employee will be able to obtain trade secret infor-mation by accessing the network from remote loca-tions, or sending or carrying information out. Similarly, that employee is more likely to use social media on this device, bring work home on it, text colleagues on it – and to do so casually and recklessly because it is a “personal” device. So, companies must involve HR and employment counsel, not just IT, in Mobile Device Management (MDM) and BYOD poli-cy. Many large data breaches were caused when lap-tops full of unencrypted PII were stolen from or for-gotten by employees. The failure to encrypt covered data on mobile devices, and the widespread, careless use of one password across all of a user’s devices, are common, ticking time bombs. ◆ Over the past year, the House Judiciary Subcommittee on Courts, Intellectual Property and the Internet has been undertak-ing comprehensive review of the Copyright Act. What are some areas that need to be addressed in a future legislative revision of the Act? Moss: When the current Copyright Act was enacted, consumers bought physical books and musical recordings that could not be easily reproduced in violation of the copyright owner’s exclusive rights. At the same time, particular copies could be lawful-ly resold or given away under the Act’s “first sale doctrine.” Now that consumers obtain so much entertainment media on digital sources, Congress should discuss an appropriate compromise that will allow copyright holders to protect their rights to prevent duplicative copies, while at the same time giving consumers some degree of property interest in the particular digital copy they’ve obtained. Notice I didn’t say “purchased,” because that’s real-ly the question we need to figure out. Is it a pur-chase or is it a license? And if it’s a license, do we want to have a copyright law where nobody actual-ly owns anything? ◆ Do the Privacy & Data Security laws apply only to electronic records? Where can these laws be found? Are there one federal and one California privacy & data breach law? Fraioli: No. Take HIPAA, for example. The HIPAA Privacy Rule covers Protected Health Care Information (PHI); the Security Rule covers electroni-cally transmitted PHI (ePHI). Throwing a box of patient records in a dumpster can be a significant breach under HIPAA. Federally, there are myriad other laws and agencies with their own statutes and subject matter jurisdiction. The Federal Trade Commission (FTC) has jurisdiction to enforce multi-ple civil statutes; this is being challenged in the Third Circuit in the Wyndham Hotels v. FTC case. Currently, 47 states (and D.C.) have passed data breach notification laws. California was first; it recently amended Civil Code section 1798.82 to specify what disclosures must be made following a breach, and to require offering of “identity theft pre-vention and mitigation services.” Section 1798.82 exempts entities covered by HIPAA, financial institu-tions, and any business “…regulated by state or fed-eral law providing greater protection to personal information…” ◆ It seems that schools have a lot of very per-sonal information about kids and their fami-lies. Does California or federal law allow schools to disclose a child’s personally identi-fiable information to third parties without the parent’s consent? Fraioli: The Family Educational Rights and Privacy Act (FERPA) was enacted forty years ago to safeguard the privacy of student data. With social media, schools can gather Personally Identifiable Information (PII) of students that may be leaked, stolen by hackers, or simply sold to advertisers by vendors to whom the school has outsourced func-tions. A loophole in FERPA protected these contrac-tors from liability, so California passed SOPIPA – the Student Online Personal Information Protection Act. Under new Education Code section 49073.6, schools are prohibited from gathering such information unless it pertains to school or student safety; stu-dents must be given access to it; parents must be ‘Now that consumers obtain so much entertainment media on digital sources, Congress should discuss an appropriate compromise that will allow copyright holders to protect their rights to prevent duplicative copies.’ AARON MOSS ‘A firm should help you pro-tect it from harm with an IP protection program, but also can help you monetize it, with an effective licensing framework and tax-efficient corporate planning and litigation counseling.’ PATRICK A. FRAIOLI, JR. Continued from page 22
- 7. OCTOBER 13, 2014 AN ADVERTISING SUPPLEMENT TO THE LOS ANGELES BUSINESS JOURNAL 25 For more than 50 years, Knobbe Martens has been devoted to the practice of IP law. Our specialization allows us to promote and protect innovation across a broad spectrum of technologies and industries. While elevating our clients to new levels of success and profitability. It’s one thing we’re good at. Because it’s the only thing that matters. Find out more at knobbe.com. knobbe.com notified of the program; outsourced vendors to whom student data is provided are prohibited from using that data for any purpose other than the con-tracted purpose; and the information must be destroyed within a year of the student turning 18 or no longer being enrolled. ◆ Should California companies that hire coders to develop software for the company always use a “Work for Hire” Agreement, or is there another way of securing the rights to the software? Moss: Software rights can also be transferred by assignment, but because assignments are subject to termination under the Copyright Act, work for hire agreements are generally preferable. However, California businesses need to take into account state labor and unemployment insurance laws that deem creators of works made for hire “employees” for pur-pose of requiring employers to maintain workers compensation and unemployment insurance for these workers. One way around this is to enter into agreements with contractor companies instead of individuals, but it’s an important decision that needs to be thought out carefully. Weiss: If a company is employing an independent contractor to code software, the company should use an assignment clause, instead of or in addition to, a work-for-hire clause, in order to ensure that the com-pany obtains ownership of the software. With respect to software, “Work for Hire” agreements are rarely effective in granting the company ownership in soft-ware developed by independent contractors. Even if the company and the independent contractor con-tractually when ip law is your focus, the winning touch comes easily. agree that the software is a “work-for-hire,” it may not qualify as such as software does not gen-erally fall into one of the eligible categories listed set forth in the copyright laws. ◆ If a company makes software for adults, does it still have to be concerned about liabili-ty under the Child Online Privacy Protection Act (COPPA)? Fraioli: Yes. Just ask Yelp!. It is not a “kids’ site;” its audience frequents restaurants, bars and other adult activities. The Children’s Online Privacy Protection Act (COPPA) – requires that companies collecting information about children under 13 clearly disclose how the information is used directly to parents and seek verifiable parental consent before collecting any information from children. Recently, the FTC filed a Complaint against Yelp! alleging that from 2009- 2013, it collected personal information when such children registered through its mobile app, providing required birthdates, name, email, location, et al. (Given the ubiquity of mobile devices, the FTC has identified geo-location information as Personally Identifying Information.) The birthdates demonstrat-ed the kids were less than 13, but Yelp! collected their information anyway without first notifying par-ents and obtaining consent, even though Yelp!’s web-site maintained a screen that prevented this from occurring there. Yelp! settled with the FTC and paid a $450,000 civil penalty. ◆ There is a lot in the news about Google and the European Union’s “Right to Be Forgotten” law; does California have any law like that about which businesses need to be aware? Fraioli: Yes, California’s controversial new “Internet Eraser” law (B&P Code Sec. 22580-22582) will take effect as of January 1, 2015. It will allow any minor (user under 18) to allegedly “permanently erase” photos, tweets, status updates and ill-advised rants by requiring “the operator of an Internet Web site, online service, online application or mobile applica-tion to permit a minor who is a registered user of the operator’s Internet Web site, online service, online application, or mobile application, to remove, or to obtain and request removal of, content or informa-tion posted.” Thus, any business that is “connected” and allows sharing or posting by anyone who may be under 18 must be aware of the contours of this new law. For example, the law requires that operators honor requests only from posters themselves. So, if a jerk posted a picture you wish you had never let him take, and you ask the operator to erase it, the new law will not apply. ◆ What criteria should be used in deciding what inventions to patent? Weiss: Companies should identify inventions that are core to their business and revenue streams, rather than simply patent technically clever inventions that may not significantly enhance revenues or provide a significant competitive advantage. ◆ What are the risks in filing provisional patent applications? Weiss: Provisional patent applications are often filed to save on costs and to get something on file quickly. However, to gain the benefit of a provisional patent application, a non-provisional patent application 26➼ INTELLECTUAL PROPERTY LAW ROUNDTABLE
- 8. 26 AN ADVERTISING SUPPLEMENT TO THE LOS ANGELES BUSINESS JOURNAL OCTOBER 13, 2014 PROTECTING THE INTEGRITY OF INNOVATION Sidley’s Intellectual Property practice provides tailored solutions for disputes involving patents, copyright infringement and theft of ideas, trademarks, false advertising, trade secrets and unfair competition. As a fi rm with more than 1,800 lawyers in 18 offi ces worldwide, we have built a reputation as an adviser for global business spanning every area of law. TALENT. TEAMWORK. RESULTS. Visit us: sidley.com/intellectual-property- litigation/ Follow us: PTO Trials blog (ptotrials.sidley.com/) Twitter: @SidleyPTOTrials 555 West Fifth Street Los Angeles, CA 90013 213.896.6000 NAMED THE 2014 “TEAM OF THE YEAR” FOR INTELLECTUAL PROPERTY LITIGATION — CHAMBERS USA sidley.com AMERICAS • ASIA PACIFIC • EUROPE Attorney Advertising - For purposes of compliance with New York State Bar rules, our headquarters are Sidley Austin LLP, 787 Seventh Avenue, New York, NY 10019, 212.839.5300; One South Dearborn, Chicago, IL 60603, 312.853.7000; and 1501 K Street, N.W., Washington, D.C. 20005, 202.736.8000. Sidley Austin refers to Sidley Austin LLP and affiliated partnerships as explained at www.sidley.com/disclaimer. Prior results do not guarantee a similar outcome. Continued from page 25 must be filed within 12 months, and the filing date of the non-provisional patent application will then be deemed to be the filing date of the earlier filed provi-sional patent application, but only with respect to what was actually disclosed in the provisional patent application. Failure to adequately describe important features in the provisional patent appli-cation may result in the loss of patent 28➼ protection for those features. ◆ What are the timing constraints in filing a patent application? Weiss: The United States now has a first to file regime. Thus, the first inventor to file a patent application on an invention will generally be entitled to patent protection over a second inven-tor who later files a patent application. This creates a rush to the patent office. Because generally the race goes to the swiftest it is imperative to be diligent in timely filing patent applications. In any case, in the United States, inventors have a one-year grace period after a public disclosure of an invention by the inventor to file a patent application describing their invention. However, disclosures by third parties who inde-pendently come up with the invention prior to the inventor filing his/her application may destroy patentability. ◆ Should companies take advan-tage of the Track One Prioritized Examination option to speed up the examination of their patent applications? Weiss: For a relatively low fee ($2000 for small business entities, $4000 for large business entities) Prioritized Examination enables business to greatly speed up the process of obtaining a patent. The Patent Office will provide a final disposition from the USPTO within twelve months from the grant-priori-tized status. The average time from filing an application and obtaining Prioritized Examination authorization to final dis-position (an allowance or final Rejection) is about eight months, as compared to more than three years for many types of applications under regu-lar examination. Thus, companies that can benefit from quickly gaining patent protection for their products or services should seriously consider taking advan-tage of the Track One Prioritized Examination option. ◆ Do patent trolls still present a risk to traditional businesses, and what is happening that may affect the future of trolls? Ransom: There has been a great deal of activity in this area. On the judicial front, the Supreme Court has eased the standard for a prevailing party to obtain fees in patent litigation. This may have some deterrent effect on so-called “trolls,” given the substantial cost of liti-gation and the increased downside risk of unsuccessful prosecution. The FTC has also stepped into the action, con-ducting a study of the tactics and busi-ness models of patent assertion entities and investigating at least one alleged troll for deceptive trade practices. On the legislative front, bills directed at curbing abusive litigation practices have failed to achieve sufficient support to advance. Among other things, members
- 9. OCTOBER 13, 2014 AN ADVERTISING SUPPLEMENT TO THE LOS ANGELES BUSINESS JOURNAL 27
- 10. 28 AN ADVERTISING SUPPLEMENT TO THE LOS ANGELES BUSINESS JOURNAL OCTOBER 13, 2014 INTELLECTUAL PROPERTY LAW ROUNDTABLE of Congress have disagreed on the fundamental question of how to define “trolls,” including whether and how to exempt universities and other research institutes, garage inventors, and various other non-practicing entities. Weiss: The number of patent suits instituted by non-practicing entities (sometimes referred to as patent trolls) has continuously increased. Defending against such suits consumes business’s financial resources and is a source of great distraction. Congress has attempted, but failed multiple times to bring a meas-ure intended to curb non-practicing entities to a vote. The courts have been more successful in addressing the sometimes insubstantial cases brought by certain non-practicing entities. In the past term, the Supreme Court limited the eligibility for patent protection of certain software inventions, has made it more difficult to find a party libel for indirect infringement, has made it easier to invalidate patents for indefiniteness, and has made it easier for prevail-ing parties in patent litigation to be awarded attor-ney fees. The Federal Circuit has made it hard to col-lect huge damage awards. Under the new procedures for challenging patents in the U.S. Patent Office, a high percentage of patents that have been undergone such procedures have been invalidated. ◆ How should companies change their patent filing strategies in view of the American Invents Act first-to-file regime? Weiss: The United States now has a first to file regime. Thus, the first inventor to file a patent appli-cation on an invention will generally be entitled to patent protection over a second inventor who later files a patent application. This creates a rush to the patent office. Because generally the race goes to the swiftest, it is imperative to be diligent in filing patent applications. ◆ How important is foreign patent protection? Weiss: The foreign patent process can be very expen-sive. If foreign markets are critical to a business, then it may be essential to invest in foreign patent protec-tion despite the costs. However, if a company does not realistically have the resources to market its products in foreign markets, then it may make more sense to invest into expanding their patent protec-tion in their primary market, the United States. In addition, certain types of inventions, such as non-technical business method inventions, may not be patentable in certain foreign markets, such as Europe and China. ◆ Are software inventions still patentable? Weiss: The Supreme Court has delivered a blow to certain types of software patents. In Alice Corp. Pty. Ltd. vs. CLS Bank Int’l, in finding the claims of a software patent to be invalid, the Supreme Court held that “the claims at issue are drawn to the abstract idea … and that merely requiring generic computer implementation fails to transform that abstract idea into a patent-eligible invention.” However, the court also stated that “there is no dispute that many computer-implemented claims are formally addressed to patent-eligible subject matter.” The Patent Office continues to issue patents for software-related inventions, taking the position that certain software inventions are still eligible for patenting. However, the boundaries of patent eligibility for software inventions are unclear, and it will take future court decision to clarify those boundaries. ◆ What is driving the popularity of patent grant reviews of patents? Weiss: Post-grant proceedings offer certain advan-tages for challenging the validity of a patent as com-pared to litigation in the courts because the burden of proof on invalidity is lower in the Patent Office than in district court (“preponderance of the evi-dence” rather than “clear and convincing”) and the Patent Office interprets patent claims more broadly than the courts, making patent claims easier to inval-idate. In addition, many allege that the Patent Office review process demonstrates an anti-patent bias and Federal Circuit Chief Judge Rader (now retired) labeled the Patent Office review board a patent “death squad.” ◆ What is a Business Associate Agreement, and are businesses in violation of any federal or California laws if they do not have one? Fraioli: Under HIPAA, a Covered Entity (Health Care Provider, Health Plan or Clearing House) has direct liability for violation of the accounting, privacy and security provisions. Previously, Business Associates — those who receive Protected Health Information (PHI) from Covered Entities – (eg., transcription serv-ices, law firms) did not have direct liability. Instead, the Covered Entity was required to obtain from a Business Associate “documentation” providing “satis-factory assurances” it was safeguarding the PHI. The HITECH Act has now made Business Associates direct-ly liable under HIPAA, whether or not they and the Covered Entity have entered into a Business Associate Agreement, and expanded the definition of Business Associate to include a Business Associate’s subcontractors. Thus, to avoid direct liability, Business Associates now need a Business Asssociate Agreement with subcontractors that handle PHI. Penalties for knowing violation, or “willful neglect,” can be severe. ◆ What should a business look for when selecting a law firm to represent their IP interests? Ransom: Clearly, identifying a firm with highly qualified IP lawyers is key. But beyond that, it is essential that a law firm have both the ability and the willingness to work as a strategic partner with the client, and to understand how IP issues fit into the client’s overall business and to respond accord-ingly. Finally, in an increasingly competitive legal environment, firms need to be nimble and flexible in responding to clients’ needs for predictability in legal fees, and to look for ways to add value to the client above and beyond the raw provisioning of legal services. Law firms should aim to exceed their clients’ expectations. Fraioli: Find a smart lawyer at a good firm who is excited about your business. Not just getting your business, but your actual, underlying business. Coming from an immigrant family, I genuinely like and admire people who make things. A com-pany thinks about its IP the way a family views its child. It wants to protect it, help it grow, and find it a good-paying job. A firm should help you protect it from harm with an IP protection pro-gram, but also can help you monetize it, with an effective licensing framework and tax-efficient corporate planning and litigation counseling. Your business, by necessity, is about more than just IP; your lawyers should help you see the whole field from the start. Moss: Because the lines between technology and entertainment are blurring so rapidly, I think that any company in the content business, broadly defined, would benefit from using a law firm that has a strong entertainment/media presence in addi-tion to a strong IP presence. It doesn’t really matter whether you’re streaming video, publishing a new social media app, or delivering advertisements in unique ways – you’re primarily dealing in content, not just technology. It’s also important to make sure you understand and are comfortable with the lawyers who will actually be doing your work. Some clients hire a law firm because one of its lawyers has a big name, which is fine – if that lawyer is actually the one who’s going to be doing your work. If not, I think prospective clients should interview the team that will actually be doing the work, not just the lead partner. Weiss: Look for a firm that has a great reputation, an extensive practice in intellectual property, and that has expertise in your particular area of interest. Intellectual property includes a large range of legal issues, including patent law, copyright law, trade-mark law, litigation, and entertainment law. Assess your needs in selecting a law firm. If you are seeking patent protection, look for a firm that has a deep bench of attorneys with a suitable technical back-ground. For example, someone with a mechanical engineering background may not be suitable to han-dle an electrical engineering invention. ‘With respect to soft-ware, “Work for Hire” agreements are rarely effective in granting the company owner-ship in software devel-oped by independent contractors.’ DAVID WEISS ‘Once a breach occurs, a business must immediately implement its response protocols, including stopping further data loss, hiring a forensics team, and beginning any required notification process – to law enforcement, government entities, and customers.’ ROLLIN RANSOM Continued from page 26
- 11. OCTOBER 13, 2014 AN ADVERTISING SUPPLEMENT TO THE LOS ANGELES BUSINESS JOURNAL 29 2014 PATRICK SOONSHIONG INNOVATION AWARDS PRESENTING SPONSORS SAVE THE DATE PLATINUM SPONSORS GOLD SPONSORS Providence Health & Services UCLA Health LOS ANGELES BUSINESS JOURNAL pprreesseennttss The Los Angeles Business Journal is excited to host the Inaugural Patrick Soon-Shiong Innovation Symposium and Awards. Building off of the success and popularity of the Patrick Soon-Shiong Innovation Awards held for the past four years, this year the Business Journal will introduce a half-day symposium that will begin with breakfast and progress through a series of nine guest speakers. Our attendees will have an opportunity to be inspired by local innovators sharing their expertise on innovation in California. The evening portion of the event will be highlighted by the Patrick Soon-Shiong Innovation Awards dinner, where we honor and acknowledge the people and organizations that continue to stretch the boundaries and have proven to be leaders in innovation. We are proud to have a partner in Dr. Soon-Shiong who shares our vision and who himself, is a true innovator. TUESDAY, NOVEMBER 18 BREAKFAST SYMPOSIUM: 8:00 11:00AM AWARDS DINNER: 6:00 9:30PM BEVERLY WILSHIRE HOTEL at BEVERLY HILLS For more information, contact Breanne Kamai at (323) 549-5225 ext. 203 or e-mail bkamai@socalbusinessjournals.com.
