Seacurity Hacking for Defense 2017
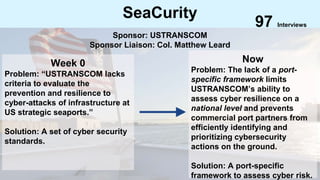
- 1. SeaCurity Week 0 Problem: “USTRANSCOM lacks criteria to evaluate the prevention and resilience to cyber-attacks of infrastructure at US strategic seaports.” Solution: A set of cyber security standards. Now Problem: The lack of a port- specific framework limits USTRANSCOM’s ability to assess cyber resilience on a national level and prevents commercial port partners from efficiently identifying and prioritizing cybersecurity actions on the ground. Solution: A port-specific framework to assess cyber risk. 97 Interviews Sponsor: USTRANSCOM Sponsor Liaison: Col. Matthew Leard
- 2. The Team Roi Chobadi Peter L. Higgins Darren Hau Mentor Mentor Benji Nguyen Public Policy Health Analytics 2017 Valerie Hau Computer Science Graphics 2018 Stanley Xie Computer Science AI 2019
- 4. -Identify possible vulnerabilities and analyze the outcomes of these risks if they are carried through. -Create protocol for personnel to follow in the case of a cyber attack Military Sponsor: USTRANSCOM Civilian/Commercial Providers and Contractors Commercial Shipping and Warehouse Companies Cyber Security Experts Primary: United States Armed Forces Provide increased efficiency and reliability in transportation of personnel and material Secondary: Civilian Partners Increased reliability and control of day-to-day operations, improving efficacy of seaport both in military and commercial sectors Help prevent cyber attacks: -Provide clear understanding of current system capabilities -Identify potential security vulnerabilities -Evaluate strength of existing cyber defenses Help improve resiliency to cyber-attacks -Assess possible effects of a cyber attack -Reduce response time to cyber attacks, such as by training seaport personnel with a clear response protocol Improved understanding of current cyber defenses of U.S. strategic seaports Increase resilience of strategic seaports against hostile cyber activity -Deploy pilot system at California port (Oakland, Los, Angeles, San Diego Costs: -Personnel to update and maintain database and/or software system -Training programs/cost of integration -Software background will help understand existing seaport computer systems -Contacts with Oakland seaport will help understand the needs of commercial seaport stakeholders -Contacts with officers in Israeli Defense Forces cyber unit -Need partnership with a local military seaport to understand USTRANSCOM and the US Armed Forces’ needs -Need partnership with a local commercial seaport to test and provide feedback on prototypes Beneficiaries Mission Achievement Mission Budget/Costs Buy-In/Support Deployment Value PropositionKey Activities Key Resources Key Partners SeaCurity: Week 0 Mission Model Canvas
- 5. -Identify possible vulnerabilities and analyze the outcomes of these risks if they are carried through. -Create protocol for personnel to follow in the case of a cyber attack Military Sponsor: USTRANSCOM Civilian/Commercial Providers and Contractors Commercial Shipping and Warehouse Companies Cyber Security Experts Primary: United States Armed Forces Provide increased efficiency and reliability in transportation of personnel and material Secondary: Civilian Partners Increased reliability and control of day-to-day operations, improving efficacy of seaport both in military and commercial sectors Help prevent cyber attacks: -Provide clear understanding of current system capabilities -Identify potential security vulnerabilities -Evaluate strength of existing cyber defenses Help improve resiliency to cyber-attacks -Assess possible effects of a cyber attack -Reduce response time to cyber attacks, such as by training seaport personnel with a clear response protocol Improved understanding of current cyber defenses of U.S. strategic seaports Increase resilience of strategic seaports against hostile cyber activity -Deploy pilot system at California port (Oakland, Los, Angeles, San Diego Costs: -Personnel to update and maintain database and/or software system -Training programs/cost of integration -Software background will help understand existing seaport computer systems -Contacts with Oakland seaport will help understand the needs of commercial seaport stakeholders -Contacts with officers in Israeli Defense Forces cyber unit -Need partnership with a local military seaport to understand USTRANSCOM and the US Armed Forces’ needs -Need partnership with a local commercial seaport to test and provide feedback on prototypes Beneficiaries Mission Achievement Mission Budget/Costs Buy-In/Support Deployment Value PropositionKey Activities Key Resources Key Partners SeaCurity: Week 0 Mission Model Canvas Primary: United States Armed Forces Provide increased efficiency and reliability in transportation of personnel and material Help prevent cyber attacks: -Provide clear understanding of current system capabilities -Identify potential security vulnerabilities -Evaluate strength of existing cyber defenses Help improve resiliency to cyber-attacks -Assess possible effects of a cyber attack -Reduce response time to cyber attacks, such as by training seaport personnel with a clear response protocol
- 6. Initial Thoughts (Week 0-1) This problem space is enormous...
- 7. Initial Thoughts (Week 0-1) It seems like a lot of research has been done already in cybersecurity! DHS Coast Guard NIST
- 8. Initial Thoughts (Week 0-1) TRANSCOM lacks a clear understanding of the consequences of cyber attacks. -D R Kenerley (TCJ6)
- 9. Initial MVP (Week 0-1) Identification of critical points Map of port facility
- 10. Initial Thoughts (Week 0-1) There is already an existing visualization tool : DAGGER -D R Kenerley (TCJ6)
- 11. Initial Thoughts (Week 0-1) Commercial partners must also be a primary beneficiary - Industry Mentors, TRANSCOM, Coast Guard, and SDDC
- 12. Primary: Commercial Port Manager Commercial Shipping Lines Managers Secondary: TCCC/SDDC officers SeaCurity: Week 1 Mission Model Canvas -Reach out to “hobby hackers” -Establish legal and secure limits for information sharing -Design clear, easy-to-use, and secure interface Military Sponsor: USTRANSCOM (TCCC and SDDC Division) Civilian/Commercial Providers and Contractors Commercial Shipping and Warehouse Companies Commercial Port Managers/Security Officers Improved understanding of current cyber defenses of U.S. strategic seaports Increase resilience of strategic seaports against hostile cyber activity -Deploy pilot system at California port (Oakland, Los, Angeles, San Diego Costs: -Personnel to update and maintain database and/or software system -Training programs/cost of integration -Software background will help understand existing seaport computer systems -Contacts with Oakland seaport will help understand the needs of commercial seaport stakeholders -”Hobby hackers” -Need partnership with a local military seaport to understand USTRANSCOM and the US Armed Forces’ needs -Need partnership with a local commercial seaport to test and provide feedback on prototypes Beneficiaries Mission Achievement Mission Budget/Costs Buy-In/Support Deployment Value PropositionKey Activities Key Resources Key Partners Low-cost identification of vulnerabilities Low-cost identification of vulnerabilities Increased awareness of cyber threat space Clearer understanding of commercial capabilities Secondary: -TCCC/SDDC Officers Primary: -Commercial Port Manager -Commercial Shipping Lines Manager
- 13. Let’s Focus on Commercial Partners (Week 2-3)
- 14. MVP II (Week 0-1) Bug Bounty Platform
- 15. It Already Exists?! (Week 2-3) Red Team/Bug Bounty Platform Visualization tool DAGGER
- 16. Data Sharing Problem (Week 2-3) Ports are reluctant to share sensitive info about their systems… Herbert Lin (Hoover Institute), TRANSCOM
- 17. Visiting the Port of Oakland (Week 4-5)
- 18. Visiting the Port of Oakland (Week 4-5) Cranes Cargo Mgmt System Scanning System
- 19. Primary: Secondary: SeaCurity: Week 3 Mission Model Canvas -Identify “Critical Infrastructure” (defining it as infrastructure that must be available/operating in order for ships to come in and out of port and cargo to be taken in/shipped out) -Code up system for visualizing critical infrastructure and provide analysis of potential patches -Establish legal and secure limits for information sharing -Design clear, easy-to-use, and secure interface Military Sponsor: USTRANSCOM (TCCC and SDDC Division) Civilian/Commercial Providers and Contractors Commercial Shipping and Warehouse Companies Commercial Port Managers/Security Officers Improved understanding of current cyber defenses of U.S. strategic seaports Increase resilience of strategic seaports against hostile cyber activity -Deploy pilot system at California port (Oakland, Los, Angeles, San Diego Costs: -Personnel to update and maintain database and/or software system -Training programs/cost of integration -Software background will help understand existing seaport computer systems -Contacts with Oakland seaport will help understand the needs of commercial seaport stakeholders -”Hobby hackers” -Need partnership with a local military seaport to understand USTRANSCOM and the US Armed Forces’ needs -Need partnership with a local commercial seaport to test and provide feedback on prototypes Beneficiaries Mission Achievement Mission Budget/Costs Buy-In/Support Deployment Value PropositionKey Activities Key Resources Key Partners -Quicker baseline assessment of basic cyber hygiene -Allow ports to assess themselves relative to other port facilities -Provide baseline for common understanding between commercial and military representatives -Allows for baseline platform for discussion between commercial and military organizations Commercial Port Security Officer TCCC-X Officer SDDC Officer Mission Assurance Officer -Provide General McDew with better grasp of cybersecurity assessments and better understanding of cybersecurity rankings of sea ports - Effective UI/UX distills high volume of information to better understand cyber- vulnerabilities Coast Guard - Better understanding of baseline port comparisons Key Activity -Identify “Critical Infrastructure”
- 20. Isolating the Pain Point (Week 4-5) Week 0 Week 1 Week 2 Week 3 Week 4 Week 5 MVP Idea Standards? Visualization? Bounty platform?
- 21. Isolating the Pain Point (Week 4-5) Week 0 Week 1 Week 2 Week 3 Week 4 Week 5 MVP Idea Standards? Visualization? Bounty platform? Who are our beneficiaries?
- 22. What frameworks are used now?(Week 4-5) NIST
- 23. What frameworks are used now?(Week 4-5) NIST Big companies Small Businesses Federal Agencies Private Organizations
- 24. SeaCurity
- 25. Isolating the Pain Point (Week 4-5) No port-specific framework baseline.
- 26. Isolating the Pain Point (Week 4-5) Back to Square One!
- 27. Isolating the Pain Point (Week 4-5) Finding a proxy...
- 28. MVP III (Week 4-5) System Low Risk Medium Risk High Risk Cargo Management System ● Software running on antiquated operating systems ● Accessible through network ● Access limited to central port authority or terminal operator ● Software running on antiquated operating systems ● Accessible through network ● Shared among multiple parties Crane ● Manually operated ● Access limited to physical presence ● Significant human intervention during operation ● Mostly manually operated ● Connections to other systems within terminal or port ● Automated ● High network connectivity with other automated systems ● Limited human intervention Scanning System ● Requires human verification of results ● Access limited to authorized personnel ● Not connected to broader network ● Mostly automatic (?) ● Connected to outside network
- 29. A New Path (Week 6-Present) For TRANSCOM, mission criticality level crucial for framework to be utilized. -Elizabeth Durham-Ruiz (Deputy Director, TCJ-6)
- 30. Mission Criticality (Week 6-Present) System Low Critical Medium Critical High Critical Cargo Management System ● Communication alternatives and protocols in place that would allow for identification and processing of military cargo ● Shutdown of cargo management stops all port activities at terminal ● No alternative method for identifying military outload safely and efficiently Crane ● Cargo being transported is RORO ● Separate RORO terminals available ● Multiple crane facilities available for military transport ● Both container and RORO cargo, but critical cargo is RORO ● Critical cargo is container Scanning System ● Alternative communication or protocol in place for identification and verification of military cargo ● Shutdown prevents efficient verification and identification of military cargo
- 31. Mission Criticality (Week 6-Present) Risk LevelMission Critical Level Risk Alleviation Guidelines Score
- 32. A New Path (Week 6-Present) Teaching Team: How will our framework be used?
- 33. A New Path (Week 6-Present) USTRANSCOM TCCC-X TCJ6 TCJ3 SDDC Port Authorities
- 34. A New Path (Week 6-Present) “We would like real-time data if possible” D R Kenerley (TCJ6), Cheryl Hepp (TCJ6)
- 36. Breakthrough : MPS-ISAO MPS-ISAO TRANSCOM Commercial Port Authorities Data Framework Data
- 37. Breakthrough : MPS-ISAO MPS-ISAO TRANSCOMSeaCurity Commercial Port Authorities Data Framework Data
- 38. Primary: Secondary: SeaCurity Current: Mission Model Canvas -Identify “Critical Infrastructure” (defining it as infrastructure that must be available/operating in order for ships to come in and out of port and cargo to be taken in/shipped out) - Provide general framework for port cybersecurity and more specific example of cargo mangement system -Establish legal and secure limits for information sharing - Create partnership between TRANSCOM and ISAO for valuable data aggregation and sharing -Work with TCJ3 and TCJ6 officials to reach an agreed-upon framework -Work with SDDC or DHS assessment teams to integrate into an existing pipeline Costs: -Personnel to update and maintain database and/or software system -Training programs/cost of integration - ISAO and TRANSCOM SME - Terminal Operating System Software provider SMEs -Need partnership with a local military seaport to understand USTRANSCOM and the US Armed Forces’ needs -Need agreement of TCJ3 and TCJ6 -SDDC officials must be willing to work with new assessment Beneficiaries Mission Achievement Mission Budget/Costs Buy-In/Support Deployment Value PropositionKey Activities Key Resources Key Partners -Quicker baseline assessment of basic cyber hygiene -Allow ports to assess themselves relative to other port facilities -Provide baseline for common understanding between commercial and military representatives -Allows for baseline platform for discussion between commercial and military organizations Commercial Port Security Officer TCCC-X Officer Mission Assurance Officer -Provide General McDew with better grasp of cybersecurity assessments and better understanding of cybersecurity rankings of sea ports - Effective UI/UX distills high volume of information to better understand cyber- vulnerabilities Coast Guard -Method for baseline port comparisons TCJ6 Officer -Provide a standard for evaluating and an incentive to improve cyber readiness. See table on next slide ISAO -Cooperation with TRANSCOM and usage of standards could provide fruitful new partnership with valuable information Military Sponsor: USTRANSCOM (TCCC- x, TCJ6, TCJ3, and SDDC Division) Military Partner: Maritime and Port Security ISAO Civilian/Commercial Providers and Contractors Commercial Shipping and Warehouse Companies Commercial Port Managers/Security Officers Primary Beneficiaries: ● TCJ6 ● Port Security Officers ● MPS-ISAO
- 39. Final MVP (Week 4-5)
- 40. Mission Achievement Beneficiary Mission Achievement TRANSCOM Improved understanding of cyber readiness at the national level Commercial Port Security Officer Guidelines for cybersecurity improvements MPS-ISAO New partnership and new channel to collect data on seaport infrastructure
- 41. Internal Readiness Level & Next Steps 1. Refine and submit our framework with a report detailing our findings 1. Foster partnership between MPS- ISAO and USTRANSCOM 1. Eventually have TRANSCOM and MPS-ISAO refine and expand our framework for integration Port Infrastructure Identification Research of Industry Standards Development of Product Product Demonstration and User Feedback Organizational Adoption Product Launch
- 42. Acknowledgements Thank you to the teaching staff, our sponsor at USTRANSCOM, Col. Leard, our mentors Roi Chobadi and Peter Higgins, and all our interviewees who have taken valuable time out of their day to talk with us.
- 43. Appendix
- 44. Cost Flow Diagram Initial Refinement by MSEs: $200? Initial Refinement by MSEs: $200? TRANSCOM MSP-ISAO Approval Process: $50? Approval Process: $50? Build into Integrated Platform: $500? Monthly ISAO Subscription: $50-100/mo
- 45. Financial/Operations Timeline 1 month 1 month 1 month 1 month 1 month 1-2 weeks 2-3 months 2-3 months Indefinitely SME-? SME- ? Monthly ISAO Subscription Fee- $50-100/mo Disperse ISAO Info to Lessees- $0 Build Platform with ISAO- $500
- 46. Minimum Viable Product: Framework Risk Level Mission Critical Level (TRANSCOM only) Risk Alleviation Guidelines Score
- 47. Path for Integration... Integrate framework into existing SDDC pipeline
- 48. Path for Integration... Maritime and Port Security Information Sharing and Analysis Organization (MPS-ISAO)
- 49. Procurement Process: Framework TCCC-x within TRANSCOM requests framework Approval from TCJ6 Division Approval from TCJ3 Division Integration into existing assessment pipeline H4D team contacted Framework submitted for review Refinement by TRANSCOM SME Integration into data collection pipeline Framework submitted for review Refinement by ISAO SME
- 50. Path for Integration... ● Currently MPS-ISAO does not have a partnership established to share information with USTRANSCOM, but are working towards secure information sharing with commercial port partners Christy Coffey (Director of Strategic Alliances, MPS-ISAO) ● USTRANSCOM officials are not aware of MPS-ISAO, but desire real-time data on cyber risk Lt. Col. Leard (TCCC-X), Cheryl Hepp (TCJ6), Phil Krueger (SDDC)
- 51. Path for Integration... Key Partnership Opportunity
- 52. Activities Gantt Chart 1 month 1 month 1 month 1 month 1 month 1-2 weeks 2-3 months 2-3 months Indefinitely
- 53. Resources, Partners, Activities Customer Discovery Outreach Review and Approval Integration Implementation USTRANSCOM Seaport Terminal Operators, Commercial Partners Maritime and Port Security ISAO Maritime ISAC Subject Matter Experts, TCJ-6, TCJ-3
- 54. Minimum Viable Product: TRANSCOM Framework Risk Level Mission Critical Level Risk Alleviation Guidelines Score
- 55. Minimum Viable Product: ISAO/Commercial Framework Risk Level Risk Alleviation Guidelines Score
- 56. Minimum Viable Product: Vulnerability Level Low Risk Medium Risk High Risk ● Generally well-established practices ● Follows basic cyber hygiene ● Generally manually operated with high levels of human intervention/authentication ● Uses antiquated software, but with good access control ● Some automation ● Moderate levels of human intervention ● Uses antiquated software without good access control ● High levels of automation ● High connectivity to outside network ● Low levels of human intervention
- 57. Things We Learned/Other Feedback Cargo Management System Terminal Operating System
- 58. Minimum Viable Product: Mission Critical Level C3 C2 C1 ● Minor slowdown ● Capabilities can be easily achieved through alternative method ● Moderate time delay (hours) ● Capabilities can be achieved with significant effort (manual, etc) ● Significant time delay (days) or complete stoppage of goods ● Capabilities cannot be replaced ● Casualties (injuries or death)
- 59. Minimum Viable Product: Systems, Mission System Low Critical Medium Critical High Critical Cargo Management System ● Communication alternatives and protocols in place that would allow for identification and processing of military cargo ● Shutdown of cargo management stops all port activities at terminal ● No alternative method for identifying military outload safely and efficiently Crane ● Cargo being transported is RORO ● Separate RORO terminals available ● Multiple crane facilities available for military transport ● Both container and RORO cargo, but critical cargo is RORO ● Critical cargo is container Scanning System ● Alternative communication or protocol in place for identification and verification of military cargo ● Shutdown prevents efficient verification and identification of military cargo
- 60. Old Minimum Viable Product: Systems, Risk System Low Risk Medium Risk High Risk Terminal Operating System Crane Scanning System
- 61. Old Minimum Viable Product: Systems, Risk System Low Risk Medium Risk High Risk Terminal Operating System Crane Scanning System
- 62. Minimum Viable Product: Systems, Risk Capability Score Cyber Hygiene Automation Level Network Connectivity Access Control Software Support Point Score System currently used in SDDC assessment (Philip Krueger, SDDC)
- 63. Minimum Viable Product: Systems, Risk Software Support Low Risk Medium Risk High Risk Software Updates Software updates offered frequently and are utilized in timely manner Available, but updated infrequently or is not on most recent version No longer supported, or software updates not utilized Monitoring Software providers or third parties utilized to provide monitoring system to detect anomalies No monitoring utilized. Relationship with Software Provider Frequent connection with software provider; software provider plays active role in implementation and maintenance of system No contact with software provider since time of implementation
- 64. Minimum Viable Product: Systems, Risk Considerations ● Is the system is native to the port environment (running on port computers vs cloud-based solution)? ● How do different parties have access to this shared database? ● What is the authentication process for logging into the dashboard? ● How are updates carried out (through physical visits by software provider, over the internet)
- 65. Next Steps 1. Talk to both a terminal operating system provider like NAVIS and a terminal operator at a port to map out attack surfaces. 1. Schedule and facilitate joint meeting between USTRANSCOM and ISAO to discuss potential possibility of partnership.
- 66. Primary: Secondary: SeaCurity: Mission Model Canvas -Identify “Critical Infrastructure” (defining it as infrastructure that must be available/operating in order for ships to come in and out of port and cargo to be taken in/shipped out) - Provide general framework for port cybersecurity and more specific example of cargo mangement system -Establish legal and secure limits for information sharing - Create partnership between TRANSCOM and ISAO for valuable data aggregation and sharing Military Sponsor: USTRANSCOM (TCCC- x, TCJ6, TCJ3, and SDDC Division) Military Partner: Maritime and Port Security ISAO Civilian/Commercial Providers and Contractors Commercial Shipping and Warehouse Companies Commercial Port Managers/Security Officers -Work with TCJ3 and TCJ6 officials to reach an agreed-upon framework -Work with SDDC or DHS assessment teams to integrate into an existing pipeline Costs: -Personnel to update and maintain database and/or software system -Training programs/cost of integration - ISAO and TRANSCOM SME - Terminal Operating System Software provider SMEs -Need partnership with a local military seaport to understand USTRANSCOM and the US Armed Forces’ needs -Need agreement of TCJ3 and TCJ6 -SDDC officials must be willing to work with new assessment Beneficiaries Mission Achievement Mission Budget/Costs Buy-In/Support Deployment Value PropositionKey Activities Key Resources Key Partners -Quicker baseline assessment of basic cyber hygiene -Allow ports to assess themselves relative to other port facilities -Provide baseline for common understanding between commercial and military representatives -Allows for baseline platform for discussion between commercial and military organizations Commercial Port Security Officer TCCC-X Officer SDDC Officer Mission Assurance Officer -Provide General McDew with better grasp of cybersecurity assessments and better understanding of cybersecurity rankings of sea ports - Effective UI/UX distills high volume of information to better understand cyber- vulnerabilities Coast Guard -Method for baseline port comparisons TCJ6 Officer -Provide a standard for evaluating and an incentive to improve cyber readiness. See table on previous slide ISAO -Cooperation with TRANSCOM and usage of standards could provide fruitful new partnership with valuable information
- 67. Deployment Timeline 1 week 2 weeks 2-3 weeks Framework Integration 6 months - 1 year (?)
- 68. Awareness Interest Consideration Adoption Keep Referrals Cross-sell Up-Sell Un-Bundle Get Keep Grow ● Awareness: Problem sponsor LTC Leard @ USTRANSCOM recognizes need for better characterization of cyber-risk at US Seaports ● Interest: Discussed problem/proposed MVPs with various possible beneficiaries including ports, shipping lines, coast guard, etc. ● Consideration: Iteratively improving the MVP and validating features of the product through discussions with beneficiaries ● Adoption: Put standards into use at various strategic ports ○ Requires buy-in from TCCC-X officers and TCJ6 officers ○ SDDC officers must be able to seamlessly integrate framework into existing assessment pipeline
- 69. Awareness Interest Consideration Adoption Keep Referrals Cross-sell Up-Sell Un-Bundle Get Keep Grow ● Regular customer check-ins and feedback from ports ● TC sends representatives to each port to increase engagement and delegate responsibility ● Maintain updated set of standards and risk assessments
- 70. Awareness Interest Consideration Adoption Keep Referrals Cross-sell Up-Sell Un-Bundle Get Keep Grow ● Grow ○ Begin with military and strategic ports ○ Spread potential through Coast Guard contacts to other commercial seaports ○ Adoption of our standards at all U.S ports
- 71. Supporters, Saboteurs Supporters ○ Port Security Officer ○ Coast Guard representative: Brian Griffiths Advocates ○ USTRANSCOM ■ TJC6: D. R. Kenerley (Chief of Cyber Strategy) ■ TCCC-X (Lt. Col Leard) Saboteurs ○ Commercial lessees (Maersk, etc)
- 72. This Week: TCCC-X Assessment Flow TCCC-X Officer TCCC (General Darren W. McDew) Wants to be able to assess ports’ cyber capabilities in wartime crisis, requests method for doing so Reports on new ideas/research, drafts speeches and presentations TCJ6 OfficerH4D Mission Assurance Officer Requests Assessment Standards Strategic Ports Program Manager (MARAD)
- 73. This Week: Ground Assessment Workflow Mission Assurance Officer SDDC Officer Commercial Port Security Officer SDDC Contractor Coast Guard Requests Capabilities Report Requests Cyber Report Compile Score Matrix and Format Report Accompanies SDDC to ports (Just started doing this/Military Ports only) Joint Cyber Center Officer Request Scheduling Schedules Schedules Meets with @ Port Facilities Participates in “tabletop exercises” and “operation exercises” to evaluate port protocol and response TCJ6 Officer Accompanies SDDC to ports to conduct cyber research Commercial Cyber Company Conduct port-specific cyber vulnerability assessment = Requested by TCCC-X
- 74. This Week: Policy Assessment Workflow Coast Guard Strategic Ports Program Manager (MARAD) TCJ6 Officer = Requested by TCCC-X Commercial Port Security Officer Meet, compile, and discuss research and possible policy solutions (NPRN) Create committees and subcommittees to research port- specific vulnerabilities
- 75. TCJ6 Officer: Archetype ● 30-60 years ● Mix of civilian and military background ● Cyber/Security domain experts ● Concerned with adoption of new ideas and standards specifically for security purposes
- 76. TCJ6 Officers: Value Proposition Canvas Products & Services Seaport Security Visualization -Application offers easy-to- digest framework for assessing cyber readiness at the port level -Application makes it easier to evaluate cyber readiness of ports against each other. Customer Jobs Identify and create new, better policies for security for DoD transport systems 1. No national picture to understand the port security status as a whole 2. Ports have widely different infrastructures and it is difficult to compare them Gains Pains Gain Creators Pain Relievers Increased understanding of port critical infrastructure, easy accessibility to such info, and the ability to compare individual seaports’ cyber readiness. -Provide basic framework to understand current systems in place for critical infrastructure - Removes need for TCJ6 Officers to manually assess cyber readiness -Keep focus on critical infrastructure that is common at all ports across the nation
- 77. ISAO Official: Archetype ● 20-40 years ● Civilian background ● Maritime domain expertise ● Concerned with adoption of information sharing platform
- 78. ISAO Official: Value Proposition Canvas Products & Services Seaport Security Visualization -Framework provides detailed, port-specific skeleton to understand the flow of cyber information at the national port level Customer Jobs Channel ideas, risk detection, and standards between commercial and federal spheres 1. Little clarity on port-specific needs 2. No existing way to connect with TRANSCOM, a key player in the maritime transportation industry Gains Pains Gain Creators Pain Relievers Good understanding of maritime domain = ability to effectively collect and prioritize information sharing -Framework focuses only on maritime port infrastructure -Framework is split into mission-specific and commercial-specific sectors for easy sharing of information for TRANSCOM and ISAO
- 79. SDDC Engineer: Archetype ● 30-50 years ● Civilian background ● Views role as performing “on ground” checks based on concerns identified from higher-up chain of command ● Concerned with capability of ports to support wartime military activity
- 80. SDDC Engineer: Value Proposition Canvas -Database of common systems in place and corresponding vulnerabilities = better baseline assessment of critical infrastructure at ports Customer Jobs Assess capabilities that can be provided to military during wartimes at port 1. Little domain expertise in cyber area 2. Have to talk with many different port and commercial authorities who have overlapping jurisdiction at the port facility Gains Pains Gain Creators Pain Relievers 1. Expedited identification of vulnerabilities = faster assessment 2. Better understanding of critical vulnerabilities in our seaports -Database provides understanding of vulnerabilities and systems of interest - Platform provides baseline for common understanding between commercial and military representatives Products & Services Seaport Security Visualization
- 81. Landlord Port Security Officer: Archetype ● 30-50 years ● Civilian background, may have industry security experience ● Concerned mostly with keeping commercial operations flowing
- 82. Landlord Port Security Officer: Value Proposition Canvas -Visualization and Database of known common system vulnerabilities = quicker baseline assessment of basic cyber hygiene Customer Jobs Assess security at commercial port to ensure continuous commercial business 1. Current solutions are very high cost 2. Limited understanding of current capabilities 3. No common platform to compare and learn from other ports Gains Pains Gain Creators Pain Relievers Evaluation of existing cyber defenses + Identification of vulnerabilities = Safer and more reliable cargo transport = Better reputation and more business - “Big-picture” vulnerabilities allow ports to assess themselves relative to other port facilities - Effective UI/UX distills high volume of information to better understand cyber- vulnerabilities Products & Services Seaport Security Visualization
- 83. Coast Guard Security Officer: Archetype ● 30-40 years ● Civilian background ● Domain expert for security measures at specific port at which he/she is deployed ● Concerned with ensuring safety at port facility and security of cargo transport ● Responsible for collecting and compiling reports on “suspicious activities” and “security breaches”
- 84. Coast Guard Security Officer: Value Proposition Canvas Products & Services Seaport Security Visualization -Focuses on “big-picture” critical infrastructure as a basic platform for discussion Customer Jobs Ensure the “Safety and Security” of personnel and cargo at portside facility 1. No existing method to evaluate ports to each other 2. Given control of cyber domain, but may not be technical cyber experts Gains Pains Gain Creators Pain Relievers Better understanding of baseline port comparisons = better able to manage and create security protocol at specific port - Enhances Coast Guard port- specific domain knowledge with broader port system visualization
- 85. Mission Assurance Officer: Archetype ● 30-50 years ● Civilian background ● Views role as synchronizer of analysts and contractors assessing ports “on the ground” ● Concerned mostly with identifying risks for specific operation plans/missions
- 86. -“Big Picture” visualization allows for baseline platform for discussion between commercial and military organizations -Increase common understanding of current vulnerabilities in critical infrastructure Customer Jobs Gather information about capabilities of facilities and determine risks for operation 1. Limited understanding of current capabilities 2. Have to compile situational awareness from various written paper reports Gains Pains Gain Creators Pain Relievers - Effective UI/UX distills high volume of information to better understand cyber- vulnerabilities Mission Assurance Officer: Value Proposition Canvas Developing good communication with commercial port partners = healthy relationship with commercial port partners and better assurance of reliability of port facilitiesProducts & Services Seaport Security Visualization
- 87. TCCC-X Officers: Archetype ● 20-30 years ● Military background ● May lack maritime domain expertise due to different military backgrounds (USAF) ● Concerned with facilitating the adoption of new ideas that will support individual division goals within USTRANSCOM
- 88. TCCC-X Officers: Value Proposition Canvas Products & Services Seaport Security Visualization -Application identifies vulnerabilities without adding another layer of bureaucracy -Focuses on “big-picture” critical infrastructure as a basic platform for discussion Customer Jobs Channel ideas between TRANSCOM divisions and Commander 1. Little clarity on quality of existing cyber defenses 2. Ports have widely different infrastructures and it is difficult to understand each one Gains Pains Gain Creators Pain Relievers Good understanding of maritime domain = increased confidence and ability to identify and promote valuable improvements/ideas -Provide basic framework to understand current systems in place for critical infrastructure - Removes need for TCCC Officers to have in-depth grasp of inner workings of each port
- 89. Mission Achievement Beneficiary Mission Achievement TCJ6 Having enough understanding cyber-resiliency status of ports at a national level to make systems and protocol that can be deployed at the national level that will increase efficacy and security of national supply chain TCCC-x Having enough understanding cyber-resiliency status of ports at a national level in order to portray a holistic overview of cyber resiliency status of national supply chain to TCCC General Darren W. McDew Coast Guard Understanding what vulnerabilities exist at a national level that they should be looking for and trying to fix at each port so they have a better way of ensuring all ports meet a national baseline in cyber security SDDC Provide an easier method to create a checklist for assessment officers to more easily check for cyber risks Mission Assurance Have a clear understanding of what cyber vulnerabilities may pose a direct risk to specific mission operations Commercial Port Officer Understand how they can improve their own systems based on status of other ports and based on guidelines/baseline set in place by TRANSCOM ISAO official Able to effectively collect data (i.e provide a checklist and clear categories) based on priority of critical infrastructure as it relates to commercial and federal sectors
- 90. List of Critical Infrastructure Critical Infrastructure Vulnerabilities D Category Breakwater gates - Port Channel Blockage of any kind Deny Power Grid Facilities/Connections Failure (have backup generators though) Deny/Degrade Cargo Movement Systems (e.g. cranes) “Closed systems” but could still be vulnerable (Leard: airforce example) Deny/Degrade/Destroy RADAR Complete failure: have backup systems Tampering (cybersecurity): can lead to serious problems if not detected (e.g. guiding two ships to collide together under low visibility circumstances) - Cargo Management System Complete failure: paralysis of the terminal Tampering (cybersecurity): can lead to serious slowdowns of the port or physical security breaches Deny/Degrade Scanning System Shutdown failure: paralysis of the terminal Tampering: can lead to pysical security Deny Physical Digital
- 91. Procurement Process: Third-Party Partnerships Company creates/has idea for possible solution Approach TTILO (Transportation and Technology Industry Liason Office) Reject Accept More Information Requested Referral to Subject Matter Expert (TCJ6, TCJ3, or SDDC officer in our case) AcceptReject More Information Requested Buying division adopts program/product or create CRADA for further work From http://www.ustranscom.mil/dbw/ttilo/
- 92. Procurement Process: Within TRANSCOM Division within TRANSCOM requests capability/tool Product made fully available to TRANSCOM and Strategic Seaports Division within TRANSCOM with capabilities to develop tool contacted TRANSCOM-specific product submitted back for approval
- 93. Third Party Subscription Platform 2 weeks 3 weeks 1 month 6 months3 months
