Avi solution2
- 2. WHY RFID • Why RFID (Radio Frequency IDentification) ? o o o Complexities o To avoid reading & typing errors To enable the data entry directly from the point of activity To make sure the accurate data entering into SAP-WMS To speed up the transaction activity by enabling faster data-collection RFID / Barcode Improve accuracy and Automated Facilities reduce latency of existing transactions Automate physical Inventory handling With Auto-ID Manual Inventory Human Dependent & Error-prone Volumes
- 3. Our Approach
- 4. Our team’s experience Our Team Team of Hands-on Experience professionals Sound understanding of Solution Development Comply with Standards Comply with industry specific Standards of solution Scalable approach Our Eco-system Established global partner links for Auto-ID Solutions Strong partnership with OEMs • Consultants experience: o o o o o Implemented RFID & Barcode based Assets Management Solution Enabled many Warehouse process automation Handheld based inventory management Warranty Tracking solution AVI Solution
- 5. Potential Benefits of technology On Time Delivery • Overall performance and timely deliveries • Streamline the overall operations Improved Availability • Improve order accuracy • Increased inventory visibility Potential Benefits Complex SKUs • Manage high number of SKUs • Increased throughput & accuracy Low Cost • Reduce the inventory carrying costs • Improve the resource efficiency
- 6. RFID as Process Enabler Inbound Processing Outbound RFID based data collection at each of the proposed process stage • Receiving •Staging • Put-away • Despatch •Picking RFID on each Windscreens Wi-Fi HHTs for data collection Wi-Fi Access Points Enterprise Application Service / Connectors Enterprise Application Service
- 7. Way Forward Process Study Process Study Current / Proposed Processes study Information Information Gathering Gathering Identification of touch points & site environmental factors Analysis Analysis Enterprise Application touch Points & checks Analyze the primary and secondary data / details Integration Integration Approach Approach Proposal along with BoM, SoW and Implementation Schedule Solution Proposal Solution Proposal
- 8. Products Mobile Computers & Terminals Data capture Application Software UHF RFID Readers RFID Readers & Labels Integration & Custom Development HR Solutions Smart cards
- 9. UHF Class1Gen2 General Purpose
- 10. Tagging strategy With many inlay types on the market for all types of FG material (i.e. Tyres, Harness, Windshields, Boards etc.), We helps you decide which inlay works best and where it works best on your products to ensure it is read properly. Installation & Continued On-Site Support Through on-site services and support, We will help you maximize your RFID investment by ensuring that your solution is properly installed and achieving your targeted goals.
- 11. Why RFID Solution To avoid Manual reading, Read Miss & typing errors To enable the data entry directly from the point of activity to ERP / Applications. To validate the data before entering into SAP. To speed up the transaction / physical activity by enabling faster data entry. Automate the Verification and authentication on real Online Mode.
- 12. RFID Integration with SAP & ERP VARIOUS MEANS AND METHODS FOR DATA CAPTURING AND SAP / ERP INTEGRATION
- 13. Material Inward Flow (SAP) Supplier Subcontractor MIGO MES/GR Unrestricted stock QA Production Floor Finished Goods Finished Goods store
- 14. General SAP process for data entry Document SAP GUI Material SAP Server DB User feeds the data into SAP screen by bringing the document to SAP terminal
- 15. RFID with SAP (Scenario –I) RFID Label document Typically a LAN Based RFID Reader is connected to LAN to scan the RFID Labels on items / FG. This allows the faster and accurate data entry into ERP database with the help of Middleware application on real time data sharing basis. SAP GUI
- 16. RFID & SAP (Scenario-II) Text files SAP GUI RFID Tagged goods Using Mobile computers allows the direct scanning of RFID on products and update the transactions through flat files. •Allows limited validations on data •Stores the data on hand held memory •Needs a PC for communication with SAP SAP
- 17. RFID& SAP (Scenario-III) Online RFID Tagged goods Using RF system allows online transaction with SAP system directly from hand held computers using a middleware software communicating with SAP using RFC/BAPI interface RFC/BAPI Middleware SAP
- 18. SCANNING METHODS AVAILABLE VARIOUS OPTIONS AVAILABLE AS PER STANDARD PRACTICE
- 20. Wireless / Batch Inventory Management Where is it? What is it? What is inside the box? Material Handling Aggregate / De-aggregate What have I assembled or disassembled? How many do I have? Do I have enough? Material Handling By Destination Where is it going? Where has it been? Should it be here? Material Handling Inspecting / Maintaining Has this been repaired? Is this under warrantee? Has this been inspected? Is this complete? What is the asset’s status or state?
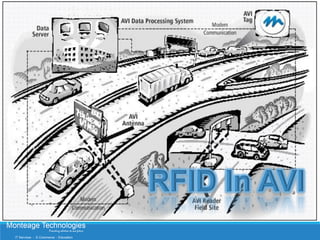
- 21. Govt. Mandate AVI Initiative FOR AUTOMOBILE MANUFACTURERS
- 22. Hi-Performance Reader/ Antennae: LANE READER Specification for Secure Tag Reading on high speed High Performance Antennas PoS Secure Tags Programmers
- 23. Government Resolution: Issued by Ministry of Road Transportation & Highways OEMs to fit RFID tags on Passenger cars and commercial vehicles (M & N Category) Gazette was published on April 8th, 2013 and will be effective from October 6th, 2013. Reference to Gazette published by MORT&H during October, 2012 and previously Sep, 2011 Tags suppliers will have to obtain the Compliance Approval from third party /agency Automotive Research Association of India (ARAI) has been nominated to test and approve the tags
- 24. Product Specs Compliance: An Overview Radio, Environmental, Installation, Durability and Memory Specifications Radio Specifications: Radio Frequency, ISO 18000 6C Protocol, Substrate and ID Printing requirements Environmental Specifications: Operating temperature, Storage temperature and Relative humidity Installation Specifications: Permanent Self adhesive, Break on Removal, and Temper evident etc. Chip Memory and Data Retention: (Minimum) 240 bits of EPC Memory , 64 bit Unique TID and Both Side Ultraviolet Rays Protection • RFID Windshield tags that are industry benchmark • Designed and developed for AVI and E Tolling applications • Approx 5 Million tags deployed on vehicles Comfortably Meets the specifications
- 25. Salient Features of Proposed Tags: Physical Security in AVI Tags. ◦ Destroy Physical and Electrical properties of tags ◦ Break the chip connections ◦ Destroy Tag Antenna on any attempts of removal ◦ True Tamper Evident ◦ Indicate tampering by leaving antenna residue ◦ Multi Layer construction (Ours Manufacturing Excellence) ◦ Can not be removable (functional) to solvents and mechanical methods ◦ Tags Manufacturing Technology ◦ Global Experience & Expertise Multi Layers Construction for true Break on Removal TM
- 26. Tags Design, Manufacturing Standard, Experience and performance is a differentiator: Silver Ink Printed Antennas High Level Quality control mechanism Each AVI tags has to pass a strict performance threshold Minimum Activation energy tests at inline TVS (Tag Verification Stations) Filed Proven “Break on Removal” performance Various semiconductors options available High operating and storage temperature tolerance Various chip sensitivity options available
- 27. Branding: Options Each of the given printing attracts a change in process. We can adopt the suitable design based on clients requirements
- 28. ISO 18000 6C: Memory Mapping
- 29. ISO18000 6C Tags Memory Banks Structure Reserve Bank (0) Kill Password Access Password EPC Bank (1) EPC Number (up to 498 bits) TID Bank (2) Gen 2 Tag IC Mfg IC Model 64-bit Factory Programmed Unique ID User Bank (3) Block 1 Block 2 Block 3 Block 4 Block 5 Block 6 Block 7 Block 8
- 30. RFID data Security in AVI Application GENERAL OVERVIEW – IN COLLABORATION TO EXITING RFID SETUP AT VARIOUS TOLL POINTS AND BACK END SYSTEM
- 31. Risks involved with Electronic Identity: Security is a common concern in many applications The security risks faced by users of RFID include business risks such as: ◦ Cloning ◦ Counterfeiting ◦ Skimming license numbers, vehicle identification numbers, or other personally identifiable information off from the tags* A security breach could cost millions in terms of Brand and Leakage of revenue with in the system. - Guidelines for Securing Radio Frequency Identification (RFID) Systems, National Institute of Standards and Technology (NIST), Special Publication 800-98, April 2007 - Construction of the Enterprise-level RFID Security and Privacy Management Using RoleBased Key Management”, Systems, Man and Cybernetics, 2006, IEEE International
- 32. ISO 18000-63 Security: Tag based Authentication Prevents counterfeit tags from being used and have physical damage mechanism inbuilt to prevent physical tag transfer. Reader based Authentication Sensitive information passed only to appropriate readers Secure Transaction Tag Data Protection Valuable information is not exposed to unauthorized applications and hardware with the help of Reader Infrastructure at place
- 33. Salient Features: Open Standard Encryption Algorithm and Implementation Utilize ISO 18000 6C features Does not interfere with standard ISO 18000-6C features Hardware Security Interface ISO 18000-6C Interface ― Provides ability to authenticate tag and readers ― Protects tag data
- 34. Tag Authentication Mechanism: Unique TID Authentication - ― TID bits pattern in Tags Tag Challenge-Response Authentication - ― Tag challenges the reader Packet Counter - ISO18000-6C Non-Transferable Windshield Tag ― Highest Level Security with Challenge Response Mechanism ( Hardware Feature) - Low High -
- 35. Indian Experience: In Tolling Projects India: Providing Interoperable RFID ISO 18000 6C technology to Toll Solution Providers and agencies in India. 200 + Lanes ETC RFID System Supplied for different projects On ground experience of unique technology challenges in India Our readers strong Platform has helped to provide solution
- 36. WHY AIS SHOULD DO IT… 1. By deploying RFID Labels on windscreen AVI achieves betterment in following area.. 2. Material Management (MM) 3. Dispatch Management (DM) 4. Stock Delivery Confirmation from Manufacturers end 5. Lesser Human Intervention and Fully Automated DATA CAPTURING 1. Material Management – at the cost of UHF RFID Tags meant for AUTOMOBILE MANUFACTURERS. 2. Gain in profit by means of simply grabbing the opportunity of MoRTH mandate by bulk deployment at the end of process line after QC – OK stage. 3. Tracking and Tracking each and every FG Material from entry point of FG Warehouse till Raw Material Warehouse of Manufacturers. 4. Fully automated Receiving and Dispatch management system. 5. Warranty / Replacement management and tracking system, with the help of same UHF RFID Labels.
- 38. advantage to AUTOMIBILE MANuFACTuR er 1. Drastic Reduction in MM 2. Less efforts in Import / Export related process 3. No additional point of activity on production line. In case of long term association, all efforts centralized to SINGLE POINT OF COORDINATION i.e. AIS India, hence no pain in individual tracking of suppliers and Certifying authorities. No involvement on any third party and outsiders and only dependency on reliable and existing partner like AIS India. No additional point of activity on production line, because tags are customized according to different OEM’s and applied at Windscreen manufacturers location only. Hence all windscreen are ready to mount, hence reduces chance of human errors and delay at critical stage on running production line.
- 40. SECONDRY USE USAGES OF AVI TAGS AT MANUFACTURER END
- 41. RFID For Warehouse Common Applications Receiving Benefits Optimize inventory - Support JIT - Improve order-to-cash cycle Cross-Docking Improve load balancing - Reduce expediting - Increase fill rate Put-Away Optimize space allocation - Maximize stock rotation Shorten lead times Inventory Mgmt Improve capital usage - Reduce shrinkage - Optimize stock rotation Order Mgmt Reduce fulfilment time - improve order accuracy - Reduce returns Shipping Increase accuracy - Improve speed
- 42. RFID in Warehouse/Distribution? Most logical first step for most manufacturers: Better Visibility into Location of Inventory throughout the distribution chain. Reduced Warehouse Labour Costs Reduced Inventory Write offs (Refabricating, EOL, shelf life) Reduction in errors - Improved Accuracy Increased Throughput Lower Inventory Levels Improved Customer Satisfaction
- 43. Stoke Reconciliation: Solution provide total visibility in the Procurement & WMS operation. - Dispatch - Receiving - Staking (Directed and stack and CBBs association) - Picking (FMFO on Batch Basis) - WIP sequence / Blocked Material virtual Stoke Reconciliation can done on the basis of random selection of bays to verify the reliability of system.
- 44. Contact US MONTEAGE TECHNOLOGIES PVT. LTD. B-86, Sector – 60, Noida – 210310, INDIA Phone – 0120-4118472 sales@monteagetech.com
