Poster_PamelaDempster_40096050
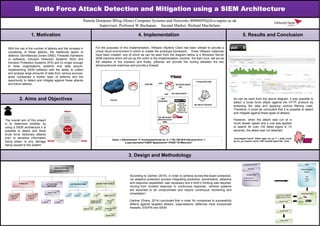
- 1. Brute Force Attack Detection and Mitigation using a SIEM Architecture Pamela Dempster BEng (Hons) Computer Systems and Networks 40096050@live.napier.ac.uk Supervisor: Professor W Buchanan Second Marker: Richard Macfarlane Pamela Dempster BEng (Hons) Computer Systems and Networks 40096050@live.napier.ac.uk Supervisor: Professor W Buchanan Second Marker: Richard Macfarlane 1. Motivation 4. Implementation 5. Results and Conclusion 2. Aims and Objectives 3. Design and Methodology With the rise in the number of attacks and the increase in complexity of these attacks, the traditional layers of defence; Demilitarized Zones (DMZ), Firewalls (hardware or software), Intrusion Detection Systems (IDS) and Intrusion Protection Systems (IPS) are no longer enough to keep organisations systems and data secure. Implementing SIEM software with the ability to collect and analyse large amounts of data from various sources, gives companies a further layer of defence and the opportunity to detect and mitigate against these attacks and future attacks. For the purposes of this implementation, VMware vSphere Client has been utilised to provide a virtual cloud environment in which to create the prototype framework. Three VMware instances have been created, one of which as can be seen from the diagram below is a Windows Server 2008 machine which will act as the victim in the implementation, another, the Kali Linux, will act as the attacker in the scenario and finally, pfSense will provide the routing between the two aforementioned machines and provide a firewall. The overall aim of this project is to determine whether by using a SIEM architecture it is possible to detect and block brute force dictionary attacks prior to sensitive information being stolen or any damage being caused to the system. As can be seen from the above diagram, it was possible to detect a brute force attack against the HTTP protocol by analysing the data and applying various filtering rules. Therefore, it could be concluded that it is possible to detect and mitigate against these types of attacks. However, when the attack was run at a much slower speed and a rule was applied to search for over 100 failed logins in 10 seconds, the attack was not detected. sourcetype="snort" failed login src_ip =* | stats count by src_ip | search count >100 | bucket span=10s _time According to Gartner (2014), in order to achieve across-the-board protection, ‘an adaptive protection process integrating predictive, preventative, detective and response capabilities’ was necessary and a shift in thinking was required, moving from ‘incident response’ to ‘continuous response’, ‘wherein systems are assumed to be compromised and require continuous monitoring and remediation’. Gartner (Orans, 2014) concluded that in order for companies to successfully defend against targeted attacks, organisations’ defences must incorporate firewalls, IDS/IPS and SIEM. hydra -l Administrator -P /home/passwords.txt -V -f 192.168.56.9 http-post-form “/ 2.asp:username^USER^&password=^PASS^:S=Welcome”