Agenda
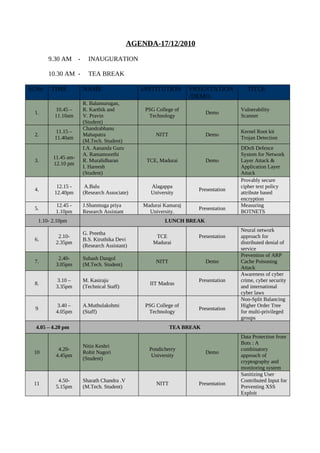
- 1. AGENDA-17/12/2010 9.30 AM - INAUGURATION 10.30 AM - TEA BREAK Sl.No TIME NAME INSTITUTION PRSENTATION TITLE /DEMO R. Balamurugan, 10.45 – R. Karthik and PSG College of Vulnerability 1. Demo 11.10am V. Pravin Technology Scanner (Student) Chandrabhanu 11.15 – Kernel Root kit 2. Mahapatra NITT Demo 11.40am Trojan Detection (M.Tech. Student) I.A. Aananda Guru DDoS Defence A. Ramamoorthi System for Network 11.45 am- 3. R. Muralidharan TCE, Madurai Demo Layer Attack & 12.10 pm I. Hareesh Application Layer (Student) Attack Provably secure 12.15 - A.Balu Alagappa cipher text policy 4. Presentation 12.40pm (Research Associate) University attribute based encryption 12.45 - J.Shanmuga priya Madurai Kamaraj Measuring 5. Presentation 1.10pm Research Assistant University. BOTNETS 1.10- 2.10pm LUNCH BREAK Neural network G. Preetha 2.10- TCE Presentation approach for 6. B.S. Kiruthika Devi 2.35pm Madurai distributed denial of (Research Assistant) service Prevention of ARP 2.40- Subash Dangol 7. NITT Demo Cache Poisoning 3.05pm (M.Tech. Student) Attack Awareness of cyber 3.10 – M. Kasiraju Presentation crime, cyber security 8. IIT Madras 3.35pm (Technical Staff) and international cyber laws Non-Split Balancing 3.40 – A.Muthulakshmi PSG College of Higher Order Tree 9 Presentation 4.05pm (Staff) Technology for multi-privileged groups 4.05 – 4.20 pm TEA BREAK Data Protection from Bots : A Nitin Keshri 4.20- Pondicherry combinatory 10 Rohit Nagori Demo 4.45pm University approach of (Student) cryptography and monitoring system Sanitizing User 4.50- Sharath Chandra .V Contributed Input for 11 NITT Presentation 5.15pm (M.Tech. Student) Preventing XSS Exploit
- 2. 18/12/2010 Sl. Time NAME INSTITUTION PRESENTATION TITLE No. /DEMO Installation of Bot and 9.30- Kritika Govind 1 NITT Demo Processing of its 9.50am (Research Assistant) Response L.Kavisankar , 9.55- E-mail Phishing 2 R.Dhanalakshmi Anna University Demo 10.15am Attack Mitigation (Research Associate) PHISHING Prediction 10.20 – K.Hemachandar Pondicherry 3 Demo of Sites using URL 10.40am (Research Assistant) University Validation 10.45 – R.Sasirekha Madurai Kamaraj 4 Demo Text Analyzer 11.05am (Research Assistant) University 11. 05 – 11.20 am TEA BREAK Extracting Features 11.20- Vasudevan, A.R. from Network Packets 5 NITT Presentation 11.40am (Research Associate) Using Tstat Tool for Dataset Creation T. Ruso and Application layer multicast for p2p 11.45 – 6 IIT Madras Demo multiparty video 12.05pm C.Prabhu conference over the (Research Assistant) internet Color Model Based 12.10- P.Thiyagarajan Pondicherry 7 Presentation Steganalysis using 12.30pm (Research Associate) University Chisquare 12.30 – 1.30pm LUNCH BREAK User authentication by 1.35- Shounak chakraborty 8 Anna University Demo using handwriting 1.55pm (Student) style parameters Detection of DDoS P. Arun Raj 2.00- Attacks using Hybrid 9 Kumar NITT Presentation 2.20pm and Adaptive Neuro- (Research Associate) Fuzzy Classifier Detection of Malicious Nodes and Swetha Semi-Randomized 2.25- Srinivasan P.T. 10 Anna University Demo Propagation for 2.45pm (Student) Secure Routing in Wireless Sensor Networks 2.50- V. Natarajan PSG College of Steganalysis Using 11 Demo 3.10pm (Research Associate) Technology Contourlet Transform 3.15- B.Radha Prevention of DNS 12 NITT Presentation 3.35pm (Research Assistant) Rebinding Attack 3.40 – TEA BREAK 3.55pm 4.00-4.30pm Monograph Discussion PRESENTATIONS – 10 DEMOS – 13 TOTAL – 23
