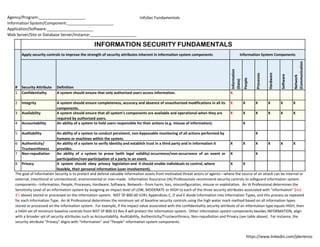
Information Security Fundamentals
•
1 recomendación•652 vistas
Information Security Fundamentals
Denunciar
Compartir
Denunciar
Compartir
Descargar para leer sin conexión
Recomendados
Recomendados
PAFF 6315: Management of Government Information Systems;
Fall 2015, Module OneInformation Security and Privacy - Public Sector actions, policies and regula...

Information Security and Privacy - Public Sector actions, policies and regula...The University of Texas (UTRGV)
Más contenido relacionado
La actualidad más candente
PAFF 6315: Management of Government Information Systems;
Fall 2015, Module OneInformation Security and Privacy - Public Sector actions, policies and regula...

Information Security and Privacy - Public Sector actions, policies and regula...The University of Texas (UTRGV)
La actualidad más candente (17)
Information Security and Privacy - Public Sector actions, policies and regula...

Information Security and Privacy - Public Sector actions, policies and regula...
Accuracy constrained privacy-preserving access control mechanism for relation...

Accuracy constrained privacy-preserving access control mechanism for relation...
Destacado
Fundamentals Matter - A Brief Introduction to Risk Analysis for Information SecurityNTXISSACSC3 - Fundamentals Matter - A Brief Introduction to Risk Analysis for...

NTXISSACSC3 - Fundamentals Matter - A Brief Introduction to Risk Analysis for...North Texas Chapter of the ISSA
Destacado (20)
NIST Policy Mapped to 800-53-800-53A-controls-and-objectives (Legal Size)

NIST Policy Mapped to 800-53-800-53A-controls-and-objectives (Legal Size)
Job aid framework-for-improving-critical-infrastructure-cybersecurity-core-jwd

Job aid framework-for-improving-critical-infrastructure-cybersecurity-core-jwd
Risk Management Framework (RMF) STEP 4- Access Security Controls - NIST SP 80...

Risk Management Framework (RMF) STEP 4- Access Security Controls - NIST SP 80...
Information Security Fundamentals - New Horizons Bulgaria

Information Security Fundamentals - New Horizons Bulgaria
NTXISSACSC3 - Fundamentals Matter - A Brief Introduction to Risk Analysis for...

NTXISSACSC3 - Fundamentals Matter - A Brief Introduction to Risk Analysis for...
(1b) Map CSC v5.0 to NIST SP 800 53 Revision 4 (security control table landsc...

(1b) Map CSC v5.0 to NIST SP 800 53 Revision 4 (security control table landsc...
(1a) map csc 5 to nist sp 800 53 rev 4 (security control table portrait) 2014...

(1a) map csc 5 to nist sp 800 53 rev 4 (security control table portrait) 2014...
Policy. FedRAMP Security Assessment Plan (SAP) Template, Policy and Procedure...

Policy. FedRAMP Security Assessment Plan (SAP) Template, Policy and Procedure...
Map Critical Security Controls (CSC) v5.0 to NIST SP 800-53 Revision 4 (Summa...

Map Critical Security Controls (CSC) v5.0 to NIST SP 800-53 Revision 4 (Summa...
Critical Security Controls v4 1 Mapped to NIST SP 800-53 Rev.4-final r6a

Critical Security Controls v4 1 Mapped to NIST SP 800-53 Rev.4-final r6a
RMF STEP 2: SELECT (NIST 800-53 Rev. 3 Controls, Enhancements and Supplementa...

RMF STEP 2: SELECT (NIST 800-53 Rev. 3 Controls, Enhancements and Supplementa...
Information System Sensitivity Level Impact Assessment (NIST SP 800-60v2r1)

Information System Sensitivity Level Impact Assessment (NIST SP 800-60v2r1)
Similar a Information Security Fundamentals
Similar a Information Security Fundamentals (20)
Exploring the Seven Key Attributes of Security Testing.pdf

Exploring the Seven Key Attributes of Security Testing.pdf
database-security-access-control-models-a-brief-overview-IJERTV2IS50406.pdf

database-security-access-control-models-a-brief-overview-IJERTV2IS50406.pdf
Legal and Ethical Considerations in Nursing Informatics

Legal and Ethical Considerations in Nursing Informatics
Comprehensive Analysis of Contemporary Information Security Challenges

Comprehensive Analysis of Contemporary Information Security Challenges
Más de James W. De Rienzo
Más de James W. De Rienzo (10)
FedRAMP 2.0 Control-Implementation-Summary (CIS) v2 1 cross-matrixed with Fed...

FedRAMP 2.0 Control-Implementation-Summary (CIS) v2 1 cross-matrixed with Fed...
NIST NVD REV 4 Security Controls Online Database Analysis

NIST NVD REV 4 Security Controls Online Database Analysis
(4) NIST SP 800-53 Revision 4 (security control enhancements omitted) 20140804

(4) NIST SP 800-53 Revision 4 (security control enhancements omitted) 20140804
(3) Map Council on CyberSecurity's Critical Security Controls (CSC) Version 5...

(3) Map Council on CyberSecurity's Critical Security Controls (CSC) Version 5...
(2) map csc 5 to nist sp 800 53 rev 4 (controls & enhancements) 20140804

(2) map csc 5 to nist sp 800 53 rev 4 (controls & enhancements) 20140804
Information Assurance, A DISA CCRI Conceptual Framework

Information Assurance, A DISA CCRI Conceptual Framework
Último
Último (20)
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
Boost PC performance: How more available memory can improve productivity

Boost PC performance: How more available memory can improve productivity
Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024

Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
Advantages of Hiring UIUX Design Service Providers for Your Business

Advantages of Hiring UIUX Design Service Providers for Your Business
Automating Google Workspace (GWS) & more with Apps Script

Automating Google Workspace (GWS) & more with Apps Script
Exploring the Future Potential of AI-Enabled Smartphone Processors

Exploring the Future Potential of AI-Enabled Smartphone Processors
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...

Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...
Factors to Consider When Choosing Accounts Payable Services Providers.pptx

Factors to Consider When Choosing Accounts Payable Services Providers.pptx
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
