Architecting the Future: Abstractions and Metadata - STL SilverLinings
•
0 recomendaciones•259 vistas
Kubernetes and Docker are two of the top open source projects, and they’re built around abstractions and metadata. These two concepts are the key to architecting in the future. Come with me as I dig a little deeper into these concepts within k8s and Docker and provide some examples from my own work on Deployment Pipelines.
Denunciar
Compartir
Denunciar
Compartir
Descargar para leer sin conexión
Recomendados
Recomendados
Más contenido relacionado
La actualidad más candente
La actualidad más candente (20)
Testing cloud and kubernetes applications - ElasTest

Testing cloud and kubernetes applications - ElasTest
Bring and distribute your dekstop applications on the Universal Windows Platf...

Bring and distribute your dekstop applications on the Universal Windows Platf...
Laravel (8) php_framework_handbook__start_from_zer_18604872_(z-lib.org)

Laravel (8) php_framework_handbook__start_from_zer_18604872_(z-lib.org)
Testing fácil con Docker: Gestiona dependencias y unifica entornos

Testing fácil con Docker: Gestiona dependencias y unifica entornos
Bgoug 2019.11 test your pl sql - not your patience

Bgoug 2019.11 test your pl sql - not your patience
Laravel 9 is now out – how is an improvement over its predecessors

Laravel 9 is now out – how is an improvement over its predecessors
Similar a Architecting the Future: Abstractions and Metadata - STL SilverLinings
Similar a Architecting the Future: Abstractions and Metadata - STL SilverLinings (20)
Architecting the Future: Abstractions and Metadata - BSidesKC

Architecting the Future: Abstractions and Metadata - BSidesKC
Becoming a Plumber: Building Deployment Pipelines - RevConf

Becoming a Plumber: Building Deployment Pipelines - RevConf
Architecting the Future: Abstractions and Metadata - GlueCon

Architecting the Future: Abstractions and Metadata - GlueCon
Architecting The Future - WeRise Women in Technology

Architecting The Future - WeRise Women in Technology
Architecting the Future: Abstractions and Metadata - All Things Open

Architecting the Future: Abstractions and Metadata - All Things Open
TDC2018FLN | Trilha Containers - Kubernetes para usuarios Docker.

TDC2018FLN | Trilha Containers - Kubernetes para usuarios Docker.
JavaOne 2016: Kubernetes introduction for Java Developers 

JavaOne 2016: Kubernetes introduction for Java Developers
Kubernetes One-Click Deployment: Hands-on Workshop (Mainz)

Kubernetes One-Click Deployment: Hands-on Workshop (Mainz)
DEF CON 27 - workshop - ISAAC EVANS - discover exploit and eradicate entire v...

DEF CON 27 - workshop - ISAAC EVANS - discover exploit and eradicate entire v...
The DevOps paradigm - the evolution of IT professionals and opensource toolkit

The DevOps paradigm - the evolution of IT professionals and opensource toolkit
Más de Daniel Barker
Más de Daniel Barker (11)
Make just culture just your culture devopsdays raleigh

Make just culture just your culture devopsdays raleigh
Understanding Risk Can Fund Transformation - DOD Dallas

Understanding Risk Can Fund Transformation - DOD Dallas
Monitoring the right way - DevOpsDays Kiev - Ignite

Monitoring the right way - DevOpsDays Kiev - Ignite
Leading Transformations in FinTech STL SilverLinings

Leading Transformations in FinTech STL SilverLinings
Último
Enterprise Knowledge’s Urmi Majumder, Principal Data Architecture Consultant, and Fernando Aguilar Islas, Senior Data Science Consultant, presented "Driving Behavioral Change for Information Management through Data-Driven Green Strategy" on March 27, 2024 at Enterprise Data World (EDW) in Orlando, Florida.
In this presentation, Urmi and Fernando discussed a case study describing how the information management division in a large supply chain organization drove user behavior change through awareness of the carbon footprint of their duplicated and near-duplicated content, identified via advanced data analytics. Check out their presentation to gain valuable perspectives on utilizing data-driven strategies to influence positive behavioral shifts and support sustainability initiatives within your organization.
In this session, participants gained answers to the following questions:
- What is a Green Information Management (IM) Strategy, and why should you have one?
- How can Artificial Intelligence (AI) and Machine Learning (ML) support your Green IM Strategy through content deduplication?
- How can an organization use insights into their data to influence employee behavior for IM?
- How can you reap additional benefits from content reduction that go beyond Green IM?
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...Enterprise Knowledge
Último (20)
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
IAC 2024 - IA Fast Track to Search Focused AI Solutions

IAC 2024 - IA Fast Track to Search Focused AI Solutions
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
What Are The Drone Anti-jamming Systems Technology?

What Are The Drone Anti-jamming Systems Technology?
Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...

Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
Architecting the Future: Abstractions and Metadata - STL SilverLinings
- 3. Architecting the Future Abstractions and Metadata Dan Barker @barkerd427 danbarker.codes
- 5. The current data center is...challenging... RHEL 6.9 Dev RHEL 6.8 Test RHEL 6.6 Prod Dev Test Prod RHEL 6.7 Prod Admin Admin Admin Admin Admin Admin Dev RHEL 6.7 Dev RHEL 6.4 Dev RHEL 6.8 Dev Ubuntu Trusty RHEL 6.9 Dev RHEL 6.6 Dev Ubuntu Trusty RHEL 6.7 Dev RHEL 6.4 Dev RHEL 6.8 Dev Ubuntu Trusty RHEL 6.9 Dev RHEL 6.6 Dev RHEL 6.7 Dev RHEL 6.4 Dev RHEL 6.8 Dev Ubuntu Trusty RHEL 6.9 Dev RHEL 6.6 Dev
- 6. The new data center is understandable and usable. Developer Access Production Controlled Network Storage Compute Platform Deployment Pipeline RHEL 6.9 App1 RHEL 6.9 App1 RHEL 6.9 App1 RHEL 6.9 App1 RHEL 6.9 App1 RHEL 6.9 App1 RHEL 6.9 App2 RHEL 6.9 App2 RHEL 6.9 App2 RHEL 6.9 App2 RHEL 6.9 App2 RHEL 6.9 App2
- 7. Docker - the early ● Docker is an abstraction ○ cgroups ○ Namespaces ● Not Included ○ Metadata ○ Volumes ○ Secrets ○ Services ○ Network ○ Plugins
- 8. Docker - the latter ● Volumes ● Secrets ● Networks ● Plugins ● Services ● Labels
- 9. Kubernetes (k8s) ● Secrets ● PersistentVolumes ● Services ● Pods ● Ingress ● DaemonSets ● ReplicaSets ● Deployments
- 10. OpenShift ● Routes ○ > Ingress ● DeploymentConfig ○ > Deployments ● ImageStream ● BuildConfig ● RBAC
- 11. Services will change your life
- 12. Services ● Identifies a set of pods using label selectors ○ Can be any label ○ Should be specific to avoid picking up disparate applications unintentionally ● Passes requests to pods internally to a Kubernetes cluster ○ Routes and Services are different ● Provides an abstraction for a Route to pass traffic from outside the cluster to desired endpoints
- 13. One Route, One Service, One Application Route Service Pod
- 14. The Route directs to the Service application0 ➜ ~ oc export routes application0 apiVersion: v1 kind: Route [...] spec: host: application0-presentation... to: kind: Service name: application0 weight: 100 [...]
- 15. The Service matches on the label “deploymentconfig” with the value “application0”. ➜ ~ oc export svc application0 apiVersion: v1 kind: Service spec: selector: deploymentconfig: application0
- 16. The Pod has many labels. ➜ ~ oc export -o yaml po/application0-1-ao16l apiVersion: v1 kind: Pod metadata: labels: app: application0 deploymentconfig: application0 environment: dev partition: customerA release: stable tier: frontend [...]
- 17. The Service now matches on the label “tier” with the value “frontend”. ➜ ~ oc export svc application0 apiVersion: v1 kind: Service spec: selector: tier: frontend
- 18. One Route, One Service, Two Applications Route Application Application Service Service
- 19. Curling the same Route results in two different applications responding.
- 20. The Pod has many labels. ➜ ~ oc export -o yaml po/application0-beta-1-ao16l apiVersion: v1 kind: Pod metadata: labels: app: application0-beta deploymentconfig: application0-beta environment: dev partition: customerA release: stable tier: frontend [...]
- 21. We’ve deleted application1 and added application0-beta.
- 23. ImageStreams ● May contain images from: ○ Image repository in OpenShift’s integrated registry ○ Other image streams ○ Image repositories from external registries ● Automatically trigger an action when new images are created ● Convenient abstraction ○ Related images ○ Image organization ○ Image history
- 24. ImageStreams ● Metadata ○ Commands ○ Entrypoint ○ Environment variables ○ Image Layers ○ Labels ○ Ports ● Could also reference other container kinds like rkt
- 26. Not this
- 27. This
- 28. Operators ● Represents human operational knowledge in software to reliably manage an application ○ AI? ● Uses the Kubernetes concept of 3rd-party resources ○ Operates as a controller of controllers and resources ● Identical model to current Kubernetes controllers ○ Observe, Analyze, Act ○ Deployments, DaemonSets, ReplicationControllers ● Not supported in OpenShift
- 29. Operators ● Deployed into a k8s cluster ● Interactions occur through the new controller ○ kubectl get prometheuses --all-namespaces ○ kubectl get alertmanagers --all-namespaces ● Abstraction around k8s primitives ○ Users just want to use a MySQL cluster. ● Complex tasks that can be performed ○ Rotating credentials, certs, versions ○ Perform backups
- 31. An Application includes a Pipeline, which is based on an opinionated PipelineTemplate. These combine to make a PipelineConfig. apiVersion: v1 kind: Application name: app1 cap: template: name: approvedTemplates/Tomcat8.yaml pipeline: notifications: mattermost: team: cloud channel: general on_success: never on_failure: always dependencies: - name: authn dnsName: authn - name: key-management username: reference_to_username password: reference_to_password stages: - name: build steps: - action: build baseImage: version: 8.0.41 - name: dev approvers: - role: app1-dev steps: - action: deploy params: environment: dev apiVersion: v1 kind: PipelineTemplate name: Tomcat8 labels: type: application build: manager: maven version: latest builderImage: java8-builder version: latest baseImage: tomcat8 version: latest deploy: deploymentType: canary maxUnavailable: 10% maxSurge: 20% apiVersion: v1 kind: PipelineConfig name: app1-pipeline labels: type: application pipeline: notifications: mattermost: team: cloud channel: general on_success: never on_failure: always dependencies: - name: authn dnsName: authn - name: key-management username: reference_to_username password: reference_to_password stages: - name: build steps: - action: build manager: maven builderImage: java8-builder baseImage: tomcat8 version: 8.0.41 - name: dev approvers: - role: app1-dev steps: - action: deploy params: environment: dev
- 32. Pipelines ● Stages ● Steps ● Application ● PipelineTemplate ● PipelineConfig
- 33. An Application and PipelineTemplate also combine to create a DeploymentConfig. apiVersion: v1 kind: Application name: app1 cap: template: name: approvedTemplates/Tomcat8.yaml pipeline: notifications: mattermost: team: cloud channel: general on_success: never on_failure: always dependencies: - name: authn dnsName: authn - name: key-management username: reference_to_username password: reference_to_password stages: - name: build steps: - action: build baseImage: version: 8.0.41 - name: dev approvers: - role: app1-dev steps: - action: deploy params: environment: dev apiVersion: v1 kind: PipelineTemplate name: Tomcat8 labels: type: application build: manager: maven version: latest builderImage: java8-builder version: latest baseImage: tomcat8 version: latest deploy: deploymentType: canary maxUnavailable: 10% maxSurge: 20% apiVersion: v1 kind: DeploymentConfig metadata: name: app1-pipeline type: application spec: replicas: 2 selector: name: frontend template: { ... } triggers: - type: ConfigChange - imageChangeParams: automatic: true containerNames: - helloworld from: kind: ImageStreamTag name: hello-openshift:latest type: ImageChange strategy: type: Rolling
- 34. The value of Pipelines ● Abstract the details of audit and compliance ○ Approvals are added dynamically and automatically ● Trivialities eliminated ○ Tabs vs. spaces ○ Curly braces placement ○ Semicolons or not ● Security checks occur early and often with helpful feedback ○ When a violation of policy or vulnerability is detected a direction for remediating it should be provided with additional resources or contacts available
- 35. The value of Pipelines ● Inject security testing across all applications easily ● Update security tooling and configuration centrally ● Utilize common artifact repositories ○ Restrict undesirable dependencies ○ Notify dependent applications when a vulnerability is discovered ● Standardized/Centralized approval system for Audit/Compliance ● Applications will become secure by default as the pipeline enforces additional policies
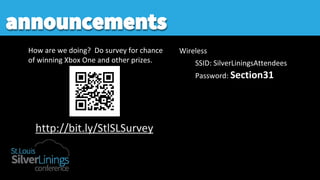
- 36. announcements
