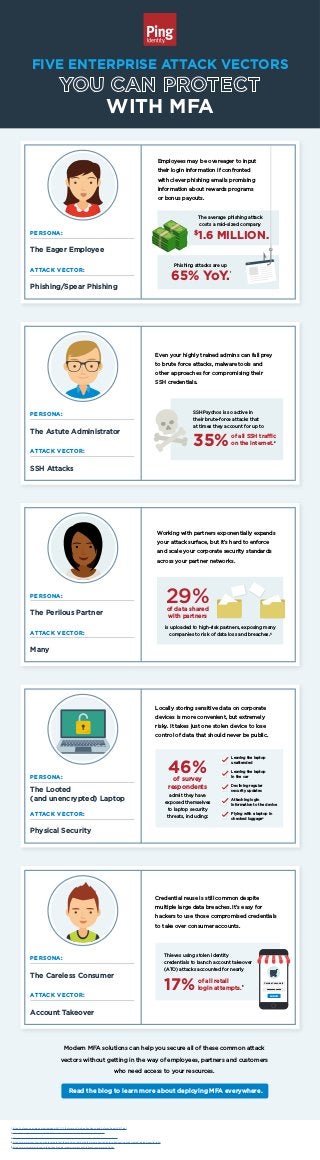
5 Attack Vectors You Can Protect with MFA
- 1. The Eager Employee WITH MFA PERSONA: Phishing/Spear Phishing ATTACK VECTOR: Employees may be overeager to input their login information if confronted with clever phishing emails promising information about rewards programs or bonus payouts. The average phishing attack costs a mid-sized company $ 1.6 MILLION. Phishing attacks are up 1 65% YoY. The Astute Administrator PERSONA: SSH Attacks ATTACK VECTOR: Even your highly trained admins can fall prey to brute force attacks, malware tools and other approaches for compromising their SSH credentials. 35% SSHPsychos is so active in their brute-force attacks that at times they account for up to of all SSH traffic on the internet. The Perilous Partner PERSONA: Many ATTACK VECTOR: Working with partners exponentially expands your attack surface, but it’s hard to enforce and scale your corporate security standards across your partner networks. 29% is uploaded to high-risk partners, exposing many companies to risk of data loss and breaches.3 of data shared with partners The Looted (and unencrypted) Laptop PERSONA: Physical Security ATTACK VECTOR: Locally storing sensitive data on corporate devices is more convenient, but extremely risky. It takes just one stolen device to lose control of data that should never be public. 46% admit they have exposed themselves to laptop security threats, including: Leaving the laptop unattended Leaving the laptop in the car Declining regular security updates Attaching login information to the device Flying with a laptop in checked luggage4 of survey respondents The Careless Consumer PERSONA: Account Takeover ATTACK VECTOR: Credential reuse is still common despite multiple large data breaches. It’s easy for hackers to use those compromised credentials to take over consumer accounts. Modern MFA solutions can help you secure all of these common attack vectors without getting in the way of employees, partners and customers who need access to your resources. 17% Thieves using stolen identity credentials to launch account takeover (ATO) attacks accounted for nearly of all retail login attempts. Read the blog to learn more about deploying MFA everywhere. FIVE ENTERPRISE ATTACK VECTORS CarelessConsumer1 ************* LOG IN 2 5 1 https://cofense.com/wp-content/uploads/2017/11/Enterprise-Phishing-Resiliency-and-Defense-Report-2017.pdf 2 https://securityboulevard.com/2017/10/hackers-are-now-scanning-for-ssh-keys-to-exploit/ 3 https://www.skyhighnetworks.com/cloud-security-blog/target-breach-reveals-risk-of-business-partners/ 4 https://www.alertsec.com/new-data-reveals-that-the-machine-that-holds-the-most-sensitive-data-is-frequently-not-encrypted-raising-security-risks/ 5 https://www.threatmetrix.com/digital-identity-blog/cybercrime/account-takeover-ecommerce-fraud/
