Tor Tracer
•Descargar como PPTX, PDF•
1 recomendación•447 vistas
A Software to track anonymity of tor browser
Denunciar
Compartir
Denunciar
Compartir
Recomendados
Más contenido relacionado
La actualidad más candente
La actualidad más candente (17)
Darknets - Introduction & Deanonymization of Tor Users By Hitesh Bhatia

Darknets - Introduction & Deanonymization of Tor Users By Hitesh Bhatia
Tor - Using alternative networks to protect your online privacy, by Tobias Cl...

Tor - Using alternative networks to protect your online privacy, by Tobias Cl...
Comparison of Anonymous Communication Networks-Tor, I2P, Freenet

Comparison of Anonymous Communication Networks-Tor, I2P, Freenet
Similar a Tor Tracer
BlueHat v17 || Dyre to Trickbot: An Inside Look at TLS-Encrypted Command-And-...

BlueHat v17 || Dyre to Trickbot: An Inside Look at TLS-Encrypted Command-And-...BlueHat Security Conference
Similar a Tor Tracer (20)
DEFCON 23 - Patrick Mcneil and Owen - sorry wrong number

DEFCON 23 - Patrick Mcneil and Owen - sorry wrong number
Privacy on the Internet - Init6 InfoSec August Meeting

Privacy on the Internet - Init6 InfoSec August Meeting
BlueHat v17 || Dyre to Trickbot: An Inside Look at TLS-Encrypted Command-And-...

BlueHat v17 || Dyre to Trickbot: An Inside Look at TLS-Encrypted Command-And-...
(130727) #fitalk anonymous network concepts and implementation

(130727) #fitalk anonymous network concepts and implementation
A Deeper Look into Network Traffic Analysis using Wireshark.pdf

A Deeper Look into Network Traffic Analysis using Wireshark.pdf
Touring the Dark Side of Internet: A Journey through IOT, TOR & Docker

Touring the Dark Side of Internet: A Journey through IOT, TOR & Docker
Más de Vishal Aditya
Más de Vishal Aditya (13)
Brain Game Simulator using BCI | EEG Applications | NeuroSky Minwave 

Brain Game Simulator using BCI | EEG Applications | NeuroSky Minwave
Brain Computer Interface & It's Applications | NeuroSky Minwave | Raspberry Pi

Brain Computer Interface & It's Applications | NeuroSky Minwave | Raspberry Pi
RAIOT- Robotics Automation & Internet of Things Lab Report

RAIOT- Robotics Automation & Internet of Things Lab Report
Hand Gesture Game Simulator Practical Presentation II

Hand Gesture Game Simulator Practical Presentation II
Último
Último (20)
Vector Search -An Introduction in Oracle Database 23ai.pptx

Vector Search -An Introduction in Oracle Database 23ai.pptx
Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe

Apidays New York 2024 - Scaling API-first by Ian Reasor and Radu Cotescu, Adobe
"I see eyes in my soup": How Delivery Hero implemented the safety system for ...

"I see eyes in my soup": How Delivery Hero implemented the safety system for ...
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
WSO2's API Vision: Unifying Control, Empowering Developers

WSO2's API Vision: Unifying Control, Empowering Developers
Mcleodganj Call Girls 🥰 8617370543 Service Offer VIP Hot Model

Mcleodganj Call Girls 🥰 8617370543 Service Offer VIP Hot Model
CNIC Information System with Pakdata Cf In Pakistan

CNIC Information System with Pakdata Cf In Pakistan
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
Apidays New York 2024 - The Good, the Bad and the Governed by David O'Neill, ...

Apidays New York 2024 - The Good, the Bad and the Governed by David O'Neill, ...
Apidays New York 2024 - Accelerating FinTech Innovation by Vasa Krishnan, Fin...

Apidays New York 2024 - Accelerating FinTech Innovation by Vasa Krishnan, Fin...
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Connector Corner: Accelerate revenue generation using UiPath API-centric busi...

Connector Corner: Accelerate revenue generation using UiPath API-centric busi...
Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...

Apidays New York 2024 - Passkeys: Developing APIs to enable passwordless auth...
Tor Tracer
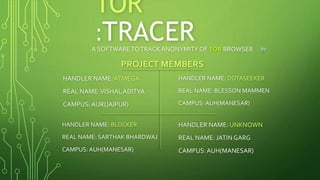
- 1. TOR :TRACERA SOFTWARETOTRACK ANONYMITYOF TOR BROWSER PROJECT MEMBERS HANDLER NAME:ATMEGA REAL NAME:VISHAL ADITYA CAMPUS:AUR(JAIPUR) HANDLER NAME: DOTASEEKER REAL NAME: BLESSON MAMMEN CAMPUS: AUH(MANESAR) HANDLER NAME: UNKNOWN REAL NAME: JATIN GARG CAMPUS:AUH(MANESAR) HANDLER NAME: BLOCKER REAL NAME: SARTHAK BHARDWAJ CAMPUS: AUH(MANESAR)
- 2. ABOUT PROJECT This project is about making people un-anonymous on TOR and to be able to track every person using TOR in our server or network. Language: Python
- 3. PROJECT DETAILS • Our idea is to develop a software/product that can be installed on any network and is capable of binding encrypted packets to every node/workstation connected to that network. • Encrypted packets will concatenate all the IP addresses from source to destination and whatever IP’s it bounces through. • Decrypt packet to extract list of IP addresses from entry to exit node and trace the route to get victim/TOR user real IP address.
- 4. REQUIREMENTS This project is required as there is an urgent need to remove anonymity of people on our network and to monitor the users activities on our network. It will make our system secure from people trying to use it for illegal activities.
- 5. STEPS INVOLVED IN DEVELOPMENT • Step1: Network information to bind encrypted packet. • Step2: Encryption algorithm. • Step3: Decryption algorithm. • Step4: Interface to display frontend and backend. • Step5: Frontend: START, STOP, TRACE(Display route and real IP address) • Step6: Backend: Admin, Encrypt Packet, Decrypt Packet, Hashing etc. Join a packet of data with the original data being sent. Use this packet to trace and add all the various IP addresses that the data was sent to. So when the IP address reaches the destination, it brings along al the information about its route and the original IP source.
- 6. PHASE TASK TIMELIN E I Study and implement source code of TOR browser & network layers. 1 weeks II Binding, Encryption, Decryption of packets over the network 2 weeks III Client-side application development using PYTHON 1 weeks PHASES OR TIMELINE
- 7. • It can be used to monitor malicious activities on the internet. • It can be used to prevent terrorist attacks. • It can be used to prevent illegal sale of fire-arms etc. • In this age of networking anonymity can become a great tool for exploiting personal web resources and with this software we can monitor such people. FUTURE SCOPE
