5 Indisputable Facts about IoT Security
•
1 recomendación•1,486 vistas
Some concepts have long been accepted as universal truths. Among the most familiar are Sir Isaac Newton’s laws of motion, which date back to the 17th century. Today, however, there are new principles defining how technologies will behave in specific situations. As one example, the proliferation of Internet of Things (IoT) devices has generated serious concerns for IT security. And that’s led IBM to identify five indisputable facts you need to know about IoT security. To learn more about how IBM can help your organization create a more secure environment for taking advantage of IoT technology, visit: ibm.com/IoT/security
Denunciar
Compartir
Denunciar
Compartir
Descargar para leer sin conexión
Recomendados
Recomendados
Más contenido relacionado
Destacado
Destacado (8)
Migration to Microsoft Online Services from Exchange and Non-Microsoft Platforms

Migration to Microsoft Online Services from Exchange and Non-Microsoft Platforms
How to Increase Student Engagement at Your School in 3 Easy Steps

How to Increase Student Engagement at Your School in 3 Easy Steps
Asia Pacific & The Security Gap: Don't Stand Still

Asia Pacific & The Security Gap: Don't Stand Still
Safeguard Healthcare Identities and Data with Identity Governance and Intelli...

Safeguard Healthcare Identities and Data with Identity Governance and Intelli...
Más de IBM Security
Más de IBM Security (20)
Leaders & Laggards: The Latest Findings from the Ponemon Institute’s Study on...

Leaders & Laggards: The Latest Findings from the Ponemon Institute’s Study on...
Bridging the Gap between Privacy and Security: Using Technology to Manage Com...

Bridging the Gap between Privacy and Security: Using Technology to Manage Com...
The Resilient End-of-Year Review: The Top Cyber Security Trends in 2018 and P...

The Resilient End-of-Year Review: The Top Cyber Security Trends in 2018 and P...
Leveraging Validated and Community Apps to Build a Versatile and Orchestrated...

Leveraging Validated and Community Apps to Build a Versatile and Orchestrated...
Accelerating SOC Transformation with IBM Resilient and Carbon Black

Accelerating SOC Transformation with IBM Resilient and Carbon Black
How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration

How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration
Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence

Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence
Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...

Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...
Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...

Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...
Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...

Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...
How to Improve Threat Detection & Simplify Security Operations

How to Improve Threat Detection & Simplify Security Operations
See How You Measure Up With MaaS360 Mobile Metrics

See How You Measure Up With MaaS360 Mobile Metrics
Nowhere to Hide: Expose Threats in Real-time with IBM QRadar Network Insights

Nowhere to Hide: Expose Threats in Real-time with IBM QRadar Network Insights
Último
Enterprise Knowledge’s Urmi Majumder, Principal Data Architecture Consultant, and Fernando Aguilar Islas, Senior Data Science Consultant, presented "Driving Behavioral Change for Information Management through Data-Driven Green Strategy" on March 27, 2024 at Enterprise Data World (EDW) in Orlando, Florida.
In this presentation, Urmi and Fernando discussed a case study describing how the information management division in a large supply chain organization drove user behavior change through awareness of the carbon footprint of their duplicated and near-duplicated content, identified via advanced data analytics. Check out their presentation to gain valuable perspectives on utilizing data-driven strategies to influence positive behavioral shifts and support sustainability initiatives within your organization.
In this session, participants gained answers to the following questions:
- What is a Green Information Management (IM) Strategy, and why should you have one?
- How can Artificial Intelligence (AI) and Machine Learning (ML) support your Green IM Strategy through content deduplication?
- How can an organization use insights into their data to influence employee behavior for IM?
- How can you reap additional benefits from content reduction that go beyond Green IM?
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...Enterprise Knowledge
Último (20)
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke

ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
What Are The Drone Anti-jamming Systems Technology?

What Are The Drone Anti-jamming Systems Technology?
Driving Behavioral Change for Information Management through Data-Driven Gree...

Driving Behavioral Change for Information Management through Data-Driven Gree...
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments

TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024

Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
5 Indisputable Facts about IoT Security
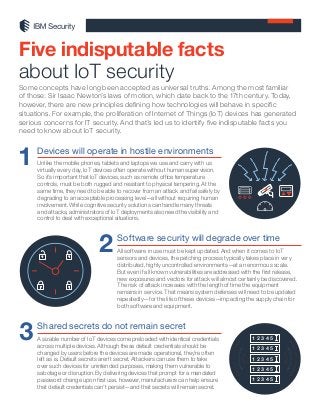
- 1. Some concepts have long been accepted as universal truths. Among the most familiar of those: Sir Isaac Newton’s laws of motion, which date back to the 17th century. Today, however, there are new principles defining how technologies will behave in specific situations. For example, the proliferation of Internet of Things (IoT) devices has generated serious concerns for IT security. And that’s led us to identify five indisputable facts you need to know about IoT security. Five indisputable facts about IoT security 1 Devices will operate in hostile environments Unlike the mobile phones, tablets and laptops we use and carry with us virtually every day, IoT devices often operate without human supervision. So it’s important that IoT devices, such as remote office temperature controls, must be both rugged and resistant to physical tampering. At the same time, they need to be able to recover from an attack and fail safely by degrading to an acceptable processing level—all without requiring human involvement. While cognitive security solutions can handle many threats and attacks, administrators of IoT deployments also need the visibility and control to deal with exceptional situations. Software security will degrade over time All software in use must be kept updated. And when it comes to IoT sensors and devices, the patching process typically takes place in very distributed, highly uncontrolled environments—at an enormous scale. But even if all known vulnerabilities are addressed with the first release, new exposures and vectors for attack will almost certainly be discovered. The risk of attack increases with the length of time the equipment remains in service. That means system defenses will need to be updated repeatedly—for the life of these devices—impacting the supply chain for both software and equipment. 2 1 2 3 4 5 1 2 3 4 5 1 2 3 4 5 1 2 3 4 5 1 2 3 4 5 Shared secrets do not remain secret A sizable number of IoT devices come preloaded with identical credentials across multiple devices. Although these default credentials should be changed by users before the devices are made operational, they’re often left as is. Default secrets aren’t secret. Attackers can use them to take over such devices for unintended purposes, making them vulnerable to sabotage or disruption. By delivering devices that prompt for a mandated password change upon first use, however, manufacturers can help ensure that default credentials can’t persist—and that secrets will remain secret. 3 1 2 3 4 5 1 2 3 4 5 1 2 3 4 5 1 2 3 4 5 1 2 3 4 5
- 2. Get the facts about what you can do To learn more about how IBM can help your organization create a more secure environment for taking advantage of IoT technology, visit: ibm.com/IoT/security © Copyright IBM Corporation 2017 IBM Security Route 100 Somers, NY 10589 Produced in the United States of America February 2017 IBM, the IBM logo and ibm.com are trademarks of International Business Ma- chines Corp., registered in many jurisdictions worldwide. Other product and service names might be trademarks of IBM or other companies. A current list of IBM trademarks is available on the web at “Copyright and trademark information” at ibm.com/legal/copytrade.shtml This document is current as of the initial date of publication and may be changed by IBM at any time. Not all offerings are available in every country in which IBM operates. THE INFORMATION IN THIS DOCUMENT IS PROVID- ED “AS IS” WITHOUT ANY WARRANTY, EXPRESS OR IMPLIED, INCLUD- ING WITHOUT ANY WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND ANY WARRANTY OR CONDITION OF NON-INFRINGEMENT. IBM products are warranted according to the terms and conditions of the agreements under which they are provided. The client is responsible for ensuring compliance with laws and regulations applicable to it. IBM does not provide legal advice or represent or warrant that its services or products will ensure that the client is in compliance with any law or regulation. Statement of Good Security Practices: IT system security involves protecting systems and information through prevention, detection and response to im- proper access from within and outside your enterprise. Improper access can result in information being altered, destroyed, misappropriated or misused or can result in damage to or misuse of your systems, including for use in attacks on others. No IT system or product should be considered completely secure and no single product, service or security measure can be completely effective in preventing improper use or access. IBM systems, products and services are designed to be part of a lawful, comprehensive security ap- proach, which will necessarily involve additional operational procedures, and may require other systems, products or services to be most effective. IBM DOES NOT WARRANT THAT ANY SYSTEMS, PRODUCTS OR SERVICES ARE IMMUNE FROM, OR WILL MAKE YOUR ENTERPRISE IMMUNE FROM, THE MALICIOUS OR ILLEGAL CONDUCT OF ANY PARTY. SEF03018-USEN-01 As data accumulates, exposure issues will increase One of the key business drivers for IoT is the data that’s generated from devices and solutions. That puts the spotlight on data security—along with how it’s created, used and deleted. Over time, connections between different, seemingly disparate datasets may emerge. IoT devices are accumulating massive amounts of personal and sensitive data, including everything from audio recordings and transcripts to GPS locations and heart rate readings. If the data isn’t managed, secured and destroyed when it’s determined to be worth less than the risk of holding on to it, the results may lead to loss of privacy and to issues of data ownership—all of which increase the importance of partnering with IoT vendors and solution providers who can be trusted with your data. Please Recycle Weak configurations will persist The default configuration of an IoT device will usually remain in place because it takes thought and effort by users to change it. If the default settings for a given device have access control turned off, for example, it’s left up to the owner to take measures to improve that security. Instead, security options should be enabled either by default or as part of an initial setup process, so that users are required to make a conscious decision to remove the default protections. 4 5 1 2 3 4 5 1 2 3 4 5 1 2 3 4 5 1 2 3 4 5 1 2 3 4 5
