Infographic - 2013 Mobile Security Analysis
•
2 recomendaciones•1,282 vistas
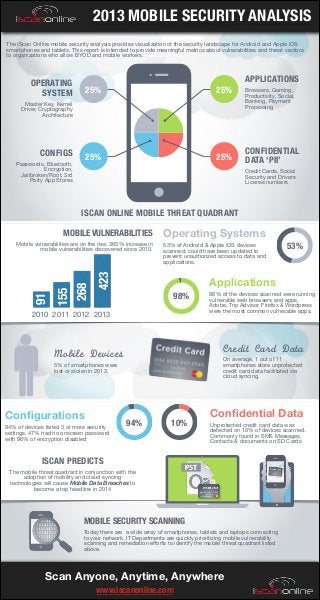
The iScan Online mobile security analysis provides visualization of the vulnerability landscape pertaining to Android and Apple iOS smartphones and tablets. This report is intended to provide meaningful metrics to organizations who need to assess mobile vulnerabilities and protect confidential PII data.
Denunciar
Compartir
Denunciar
Compartir
Descargar para leer sin conexión
Recomendados
Recomendados
Más contenido relacionado
Último
Último (20)
Salesforce Adoption – Metrics, Methods, and Motivation, Antone Kom

Salesforce Adoption – Metrics, Methods, and Motivation, Antone Kom
Choosing the Right FDO Deployment Model for Your Application _ Geoffrey at In...

Choosing the Right FDO Deployment Model for Your Application _ Geoffrey at In...
Powerful Start- the Key to Project Success, Barbara Laskowska

Powerful Start- the Key to Project Success, Barbara Laskowska
The Value of Certifying Products for FDO _ Paul at FIDO Alliance.pdf

The Value of Certifying Products for FDO _ Paul at FIDO Alliance.pdf
SOQL 201 for Admins & Developers: Slice & Dice Your Org’s Data With Aggregate...

SOQL 201 for Admins & Developers: Slice & Dice Your Org’s Data With Aggregate...
PLAI - Acceleration Program for Generative A.I. Startups

PLAI - Acceleration Program for Generative A.I. Startups
UiPath Test Automation using UiPath Test Suite series, part 2

UiPath Test Automation using UiPath Test Suite series, part 2
AI presentation and introduction - Retrieval Augmented Generation RAG 101

AI presentation and introduction - Retrieval Augmented Generation RAG 101
Agentic RAG What it is its types applications and implementation.pdf

Agentic RAG What it is its types applications and implementation.pdf
Extensible Python: Robustness through Addition - PyCon 2024

Extensible Python: Robustness through Addition - PyCon 2024
Simplified FDO Manufacturing Flow with TPMs _ Liam at Infineon.pdf

Simplified FDO Manufacturing Flow with TPMs _ Liam at Infineon.pdf
Unpacking Value Delivery - Agile Oxford Meetup - May 2024.pptx

Unpacking Value Delivery - Agile Oxford Meetup - May 2024.pptx
Destacado
Destacado (20)
Product Design Trends in 2024 | Teenage Engineerings

Product Design Trends in 2024 | Teenage Engineerings
How Race, Age and Gender Shape Attitudes Towards Mental Health

How Race, Age and Gender Shape Attitudes Towards Mental Health
AI Trends in Creative Operations 2024 by Artwork Flow.pdf

AI Trends in Creative Operations 2024 by Artwork Flow.pdf
Content Methodology: A Best Practices Report (Webinar)

Content Methodology: A Best Practices Report (Webinar)
How to Prepare For a Successful Job Search for 2024

How to Prepare For a Successful Job Search for 2024
Social Media Marketing Trends 2024 // The Global Indie Insights

Social Media Marketing Trends 2024 // The Global Indie Insights
Trends In Paid Search: Navigating The Digital Landscape In 2024

Trends In Paid Search: Navigating The Digital Landscape In 2024
5 Public speaking tips from TED - Visualized summary

5 Public speaking tips from TED - Visualized summary
Google's Just Not That Into You: Understanding Core Updates & Search Intent

Google's Just Not That Into You: Understanding Core Updates & Search Intent
The six step guide to practical project management

The six step guide to practical project management
Beginners Guide to TikTok for Search - Rachel Pearson - We are Tilt __ Bright...

Beginners Guide to TikTok for Search - Rachel Pearson - We are Tilt __ Bright...
Infographic - 2013 Mobile Security Analysis
- 1. 2013 MOBILE SECURITY ANALYSIS The iScan Online mobile security analysis provides visualization of the security landscape for Android and Apple iOS smartphones and tablets. This report is intended to provide meaningful metrics about vulnerabilities and threat vectors to organizations who allow BYOD and mobile workers. OPERATING SYSTEM 25% 25% Master Key, Kernel Driver, Cryptography Architecture CONFIGS 25% Passwords, Bluetooth, Encryption, Jailbroken/Root, 3rd Party App Stores 25% APPLICATIONS Browsers, Gaming, Productivity, Social, Banking, Payment Processing CONFIDENTIAL DATA ‘PII’ Credit Cards, Social Security and Drivers License numbers ISCAN ONLINE MOBILE THREAT QUADRANT 53% of Android & Apple iOS devices scanned, could have been updated to prevent unauthorized access to data and applications. 423 Mobile vulnerabilities are on the rise. 365% increase in mobile vulnerabilities discovered since 2010. 155 268 Operating Systems 91 MOBILE VULNERABILITIES Applications 98% 2010 2011 2012 2013 98% of the devices scanned were running vulnerable web browsers and apps. Adobe, Trip Advisor, Firefox & Wordpress were the most common vulnerable apps. Credit Card Data Mobile Devices On average, 1 out of 11 smartphones store unprotected credit card data facilitated via cloud syncing. 5% of smartphones were lost or stolen in 2013. Configurations 94% of devices failed 3 or more security settings. 47% had no onscreen password with 96% of encryption disabled 53% 94% 10% Confidential Data Unprotected credit card data was detected on 10% of devices scanned. Commonly found in SMS Messages, Contacts & documents on SD Cards ISCAN PREDICTS The mobile threat quadrant in conjunction with the adoption of mobility and cloud syncing technologies will cause Mobile Data Breaches to become a top headline in 2014 70% 50 MOBILE SECURITY SCANNING Today there are a wide array of smartphones, tablets and laptops connecting to your network. IT Departments are quickly prioritizing mobile vulnerability scanning and remediation efforts to identify the mobile threat quadrant listed above. Scan Anyone, Anytime, Anywhere www.iscanonline.com
