Cybersecurity Threat Intelligence Briefing
Mark is regarded as a Cybersecurity thought Leader. In 2002 Mark founded the Atlantic Canada High Technology Crime Investigation Association. In 2015 Mark published the first NIST Cybersecurity Framework Foundation course. Mark was trained by IBM on IBM’s AS400 and worked with IBM Global Services on a Red Team conducting penetration testing against off shore financial institutions.Mark has led the design and implementation of information security programs for many US and Canadian organisations using ISO. Mark led Central 1 Credit Union to become the first Canadian Bank to earn ISO/IEC 27001 Certification. During Mark’s work with BC Government 2008 he also led the Ministry of Finance Division Corporate Account Services to become the first Canadian Government entity to earn ISO 27001 Registration /Certification.
Recomendados
Recomendados
Más contenido relacionado
La actualidad más candente
La actualidad más candente (20)
Similar a Cybersecurity Threat Intelligence Briefing
Similar a Cybersecurity Threat Intelligence Briefing (20)
Más de www.securekm.com; Secure Knowledge Management Inc.
Más de www.securekm.com; Secure Knowledge Management Inc. (7)
Último
Último (20)
Cybersecurity Threat Intelligence Briefing
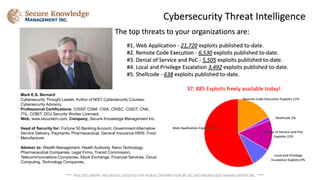
- 1. The top threats to your organizations are: #1. Web Application - 21,720 exploits published to-date. #2. Remote Code Execution - 6,530 exploits published to-date. #3. Denial of Service and PoC - 5,505 exploits published to-date. #4. Local and Privilege Escalation 3,492 exploits published to-date. #5. Shellcode - 638 exploits published to-date. 37, 885 Exploits freely available today! Cybersecurity Threat Intelligence *** THIS DOCUMENT HAS BEEN CLASSIFIED FOR PUBLIC DISTRIBUTION BY SECURE KNOWLEDGE MANAGEMENT INC. *** Mark E.S. Bernard Cybersecurity Thought Leader, Author of NIST Cybersecurity Courses, Cybersecurity Advisory, Professional Certifications; CISSP, CISM, CISA, CRISC, CGEIT, CNA, ITIL, COBIT, DOJ Security Worker Licensed. Web; www.securekm.com; Company; Secure Knowledge Management Inc. Head of Security for: Fortune 50 Banking Account, Government Alternative Service Delivery, Payments, Pharmaceutical, General Insurance HRIS, Food Manufacturer Advisor to: Wealth Management, Health Authority, Nano Technology, Pharmaceutical Companies, Legal Firms, Transit Commission, Telecommunications Companies, Stock Exchange, Financial Services, Cloud Computing, Technology Companies,
