Infocom Security
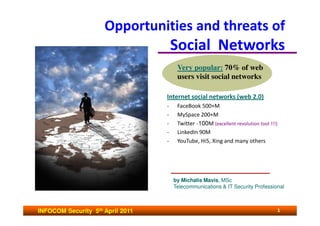
- 1. Opportunities and threats of Social Networks Very popular: 70% of web users visit social networks Internet social networks (web 2.0) - FaceBook 500+M - MySpace 200+M - Twitter ~100M (excellent revolution tool !!!) - LinkedIn 90M - YouTube, Hi5, Xing and many others by Michalis Mavis, MSc Telecommunications & IT Security Professional INFOCOM Security 5th April 2011 1
- 2. THE ENISA Report (Feb-2010) • According to ENISA report experiencing online Social Networking Sites (SNSs) has become one of the most popular activities carried out on the Internet, for staying in touch with business and personal contacts. • According to recent statistics more than 65 million active users are accessing Facebook through their mobile devices => European Network and Information Security Agency INFOCOM Security 5th April 2011 2
- 3. Agenda • Understanding the dangers of social networks (SNs) to corporate security and personal privacy. • Discussing methods to protect you and your business. • Identify the dangers for the industry. • Legal and illegal methods used to get confidential information by using SNs. • Opportunities of SNs in investigations. INFOCOM Security 5th April 2011 3
- 4. Definition - Social Network ( web 2.0 ) It is an online community that allows people, through a built-up profile, to meet, communicate, keep in touch, share pictures and videos with other community members with whom a connection is shared INFOCOM Security 5th April 2011 4
- 5. Attack to privacy from: • Third parties that gain fraudulent access to personal data. • Other users • Platform provider personnel that may override privacy settings and gain access to information (e.g. IP address, browser type, etc.) leaking this info to search engines, third parties. INFOCOM Security 5th April 2011 5
- 6. Major risks and threats • Identity theft. • Malware propagation • Corporate data leakage and reputation risk. • User’s position tracking (when the user mobile phone is equipped with the necessary technology – map function ). • Data misuse. INFOCOM Security 5th April 2011 6
- 7. Computer worm INFOCOM Security 5th April 2011 7
- 8. Malicious Applications From time to time, social networks are hit with malicious applications. Trend Micro has recently found a number of rogue apps on Facebook (with names such as “Stream” and “Birthday Invitations”) that sent users to a known phishing domain, with a page claiming they needed to enter their login credentials to use the application. Victims would then be directed to the Facebook site. Facebook removed six of the apps identified by Trend. Unfortunately, more popped up. Users should be aware of apps from unknown developers, especially those that request personal information. Rogue applications on Facebook (Stream, Birthday invitations), that sent users to known phishing domains. INFOCOM Security 5th April 2011 8
- 9. Faked facebook web site to steal your credentials… INFOCOM Security 5th April 2011 9
- 10. INFOCOM Security 5th April 2011 10
- 11. The study by ISACA (Information Systems Audit and Control Association) ISACA (2010 study) isn't warning companies not to use Web 2.0 tools or to not fully embrace social networking. However, they need to go into it with their eyes wide open to the risks as well as the benefits. INFOCOM Security 5th April 2011 11
- 12. Golden Rules • Pay attention to what you post and upload. Consider carefully which images, videos and information you choose to publish. • Never post sensitive info and if needed use a pseudonym. • Verify all your contacts and do not accept friend requests from people you don’t know. • Protect your work environment and avoid reputation risk • Use privacy and security oriented settings in your profile. • Deactivate location bases services of your mobile phone if you don’t need them. INFOCOM Security 5th April 2011 12
- 13. Facebook faces legal action in Germany for mining information of non users saving private information of individuals who don't use the site and haven't granted it access to their details INFOCOM Security 5th April 2011 13
- 14. Where and how … ? • Intelligence gathering. Sometimes there is no reason to spend a lot of money to gather useful information. It is available free on the Internet, by using the right tools. • With the use of the right tools and techniques you may find extremely useful information about competitors, individuals, governments, companies and not only. • It is possible by using legitimate or illegal ways. • But you should know how and where to search for… INFOCOM Security 5th April 2011 14
- 15. O.S.INT (Open Source INTelligence) gathering Be alerted by Google ! Google Alerts (Email updates of latest relevant results) http://www.google.com/alerts • Keeping current on a competitor or industry. • Getting the latest on an event. • Keeping tabs on your favorite issues. • Monitoring a developing news story. A good source on mining news on the net can be found here : http://www.spylogic.net/2009/10/enterprise-open-source-intelligence-gathering- part-1-social-networks/ http://www.spylogic.net/2009/10/enterprise-open-source-intelligence-gathering- %E2%80%93-part-2-blogs-message-boards-and-metadata/ http://www.spylogic.net/2009/10/enterprise-open-source-intelligence-gathering- part-3-monitoring/ INFOCOM Security 5th April 2011 15
- 16. BLOGS postings • Blogs can be searched via any traditional search engine, however, the challenge with blogs are not the posts themselves but the comments. • Especially comments coming from current or former employees or customers on highly sensitive public relations issues. • It is important to be monitoring blogs and their comments, before they go viral. INFOCOM Security 5th April 2011 16
- 17. “I hate my Job. My boss is a total…” INFOCOM Security 5th April 2011 17
- 18. Leakage of confidential Info • Do you know what is being posted by your employees, customers, or your competition? • What does the Internet say about your company ? • We all know information or intelligence gathering is one of the most important phases of a penetration test. • However, gathering information and intelligence about your own company is even more valuable and can help an organization proactively determine the information that may damage your brand, reputation and help mitigate leakage of confidential information. INFOCOM Security 5th April 2011 18
- 19. Serious FaceBook Security leak (UK) His wife published their holiday photo on FaceBook INFOCOM Security 5th April 2011 19
- 20. Company data loss 17% of experienced company data loss is related to social networks (Source: Proofpoint Inc. - 2009 Survey). WHAT IS POSTED ON THE INTERNET ? Complaints by employees (e.g. In Twiter) Security Vulnerabilities of company network. Exposure of Confidential Information. Documents on the Internet contain METADATA !!! INFOCOM Security 5th April 2011 20
- 21. The Super Cookies Risk • Some web sites put on your computer an invisible “super cookie” stored in a secret area of your computer or smart phone. • Specific Internet servers keep track of all your search history (associating your searches with this supper cookie). • When you built your profile on a Social Network these super cookies are connecting your pc cookie with your profile (name). • So some people may know what exactly you have searched on the Internet for many years in the past. INFOCOM Security 5th April 2011 21
- 22. Internet postings metadata • Metadata (data about data) are in documents traditionally used for indexing files, and finding out information about : – The document creator. – s/w used to create the document, and many more... • By reading metadata you may discover – vulnerable versions of s/w, that can be used for client side attacks, – OS versions, – path disclosure, – user id’s and more… INFOCOM Security 5th April 2011 22
- 23. Metadata (the silent Killer…) • Metadata are hidden from the user. • There are lots of tools to pull out metadata from documents and pictures (see paper by Larry Pesce in www.sans.org). • On a posted document a lot of revealing metadata may exist, like user id, OS, s/w version number, telephone number & email address of document owner, MAC address, document path, Location (city), etc… INFOCOM Security 5th April 2011 23
- 24. WHAT SHOULD BE DONE ? • Removal of Internet postings, metadata. • Setting up a simple (cheap) monitoring program. • Built an Internet Posting Policy (who is responsible for authorization, what is confidential – when). INFOCOM Security 5th April 2011 24
- 25. Ciscos’s Internet Postings Policy http://blogs.cisco.com/news/comments/ciscos_internet_postings_policy/ INFOCOM Security 5th April 2011 25
- 26. Social Networks as opportunity for investigations • Socnet Search Engines - RSS feeds/Google Hacks (Google Alerts + Google Reader) - Facebook status updates. - Photo Search. - YouTube Video Search. - Maltego + Mesh = WIN INFOCOM Security 5th April 2011 26
- 27. Social Network Search Engines Search engines specifically look for “public” information on some of the major social networks. They only pull public information that can be easily indexed. While there are other ways to search specific social networks (like search.twitter.com or FriendFeed) there are search engines that search multiple networks and go beyond public information… Private information like the Facebook cannot be indexed without violating the TOS (Terms of Service) but … there are tools like Maltego that can have transforms written to “page scrape” private information. See : www.ethicalhcacker.net/content/view/204/24/ INFOCOM Security 5th April 2011 27
- 28. What is Maltego • Maltego is an open source intelligence and forensics application. • It allows to identify unknown key relationships between information elements. • Probably the best tool to “visually” show you information found on some of the social networks and the relationships that information has connected to it. • It works well for Twitter, Facebook, LinkedIn and MySpace profiles (publicly available). • The Twitter transforms are probably the highlight since you can dig into conversations as well. • The Facebook transform was specifically written to search within the Facebook network using a real user account. However, this transform doesn’t work anymore due to recent structural changes to the way Facebook HTML was coded. This transform violates Facebook TOS since it did screen scraping but when it did work it was a great way to search status and group updates not available to public search engines ! • Hackers are trying to update the transform so it works again !!! INFOCOM Security 5th April 2011 28
- 29. Maltego relationships • Maltego is an information gathering tool that allows you to enumerate network and domain information like: – Domain names – Whois information – DNS names – Netblocks – IP Addresses • Maltego also allows you to enumerate people information like: – Email address with person’s name – Web sites associated with a person’s name – Social groups associated with a person’s name – Companies and organizations associated with a person’s name. INFOCOM Security 5th April 2011 29
- 30. Emails belonging to a person - Don Denzal (forensics information provided by Maltego tool) INFOCOM Security 5th April 2011 30
- 31. Computer Based Social Engineering Tools: Maltego Mesh • Maltego answers the question ‘what binds these 10 email addresses together?’ • Maltego also answers the question ‘what can you find on this IP address?’ • By default Maltego Mesh searches for the following 'entities' within a page: – IP Addresses – Email Addresses – Netblocks (IP addresses under a block) – Named entity Extraction (SillyNer) – Phone Numbers – Websites – Dates INFOCOM Security 5th April 2011 31
- 32. More information… • For more information on Maltego and how to use it check out the work Chris Gates has done in his Maltego tutorials : www.ethicalhacker.net/content/view/251/24 • Keep in mind, Maltego works great for finding information if you need it for a specific scope, like a penetration testing. • For automating monitoring, use Google or Yahoo Pipes. INFOCOM Security 5th April 2011 32
- 33. INFOCOM Security 5th April 2011 33
- 34. Why you'd want to use Metago Mesh Its free (always a plus). It helps you find information quickly within a large page (no need to read an entire blog to find email addresses) Quickly have options like 'search on facebook' with email addresses instead of having to browse to each site. The ability to add your own 'entities' (eg, if you are looking for an internal customer-id and you know the format, you can add your own regular expression for it) Exploiting Human Vulnerabilities http://www.social-engineer.org/ INFOCOM Security 5th April 2011 34
- 35. CONCLUSIONS • Social Networks (SNs) is a useful but also risky environment. • Companies should establish rules and polices on the way they are used by their staff. • SNs may be an opportunity for information gathering in fraud investigations. Attention, a business oriented Social Network… THANK YOU. Michalis Mavis http://gr.linkedin.com/in/mmavis INFOCOM Security 5th April 2011 35