គម្រោងបង្កើតគេហទំព័រអង្គរមាស
- 4. II
- 8. 1
- 9. 2
- 10. 3
- 11. 4
- 12. 5 ) ) Web Email Sub Domains Web Mail 100 Daily Back Up 20
- 13. 6
- 14. 7
- 15. 8
- 16. 9
- 17. 10
- 18. 11
- 19. 12 PeopleOrMachine Days Unit Price Subtotal I. Workshop Attendance 3 2 $15 $90 LCD 1 1 1 $200 $200 Designer 1 $100 $100 Programmer 1 $200 $200 III. Training and Support Trainee 2 2 $15 $60 Computer 1 $20 $20 1 0 Grand Total $980 Month1 Month2 Week1Week2Week3Week4Week1Week2 Gathering&Consultancy
- 20. 13
- 21. 14
- 22. 15
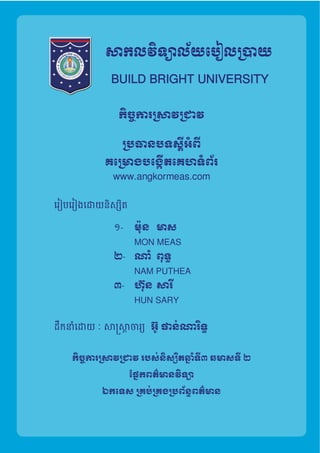
- 23. !កុម%រ'បចំ(និសិ.តជំ12!គប់!គងព័ត៌9នវិទ< ជំ1ន់ទី១១) ! " " " ! " ស$%&&ចរ&)*&នំៈ អ៊ូ ផន់ណរ5ទ្! ១-ណំ ពុទ<&! ២-ម៉ុន មស! ៣-ហ៊ុន សរD!
- 24. ! អំពីគំ@Aង ! រច1សមB័នCេគហទំព័រ ! បេចFកេទសកGុងHររច1េគហទំព័រ ! Hររច1េគហទំព័រ ! ថវិHរJសGKរសុំគ@!9ង ! រយៈេពលៃនHរអនុវតPន៍គ@!9ង ! យុទCR!សS!បកួត!បែជង និង ផ.ពWផXយ ! ឯកRរ@Zង មតិករ&
- 25. អំពីគំ@Aង! ១ @[លបំណងៃនគំ@Aង! • 'ើម*+ីឲ*.មនករ0្ើទីផ*4 5ើបណ8*ញ អ៊<នធឺ?*ត ( ) សំរួលឲ*.មនករDEកចំDEន និង ផ*Iព្ផ*4យនូវផលិតផល & • សំរួលឲ*.អតិថិជន ឬQ R*ិយមិត្ អចQផ*Iព្ផ*4យQទំនិញផV*ល់ខ្Zន( )& • អចផ្ល់ឱកសករងរQដល់បុគ្លិក ឬ ភb*ក់ងរcើង& • ផ្ល់ទំននុលចិត្ដល់អតិថិ& • បd្ើតឲ*.មនករទិញលក់f*បច*gប់ និង សុវត្ិភពចំhះអ្កលក់ និង អ្កទិញ& • ផ្ល់អត្R*lជន៍ដល់អតិថិជន ឬ n*ុមហ៊ុនp*លបនផ*Iព្ផ*4យ rយ ឥតគិតt្*ក្uង លក្័ណកំណត់របស់ពួកcើង ។& • ផ្ល់ឲ*.មនករDEកចំDEនទំងពួកcើង និង ទំងn*ុមហ៊ុន {*មទំងអតិថជនក្uងស}*រតី សមគ្ីភព ក្uងករអភិវឌ*Äន៍R*Å*សជតិ ។& &
- 26. ២ @[ល^_ៃនគ@!9ង! • É្*ងរកអតិថិជន'ើម*+ីឲ*.មនករផ*Iព្ផ*4យពQណិជ្កម្5ើá*ហទំព័ររបស់ cើង ។& • ទញយកថវàករពីក្uងករផ*Iព្ផ*4យពនិជ្កម្ ។& • ឈនäរកករទិញលក់ជលក្ណៈ - ។& • បd្ើតជ & & & សំរប់çé*ទីn*ុងភ្ំè*ញ ចំhះករDៀបចំករលក់& ករផ*4ព្ផ*4យទូរទំងR*Å*ស ។& ៣ @[ល^_អតិថិជន!
- 27. ៤ វិធីR!សSកGុងHរJលKកកំពស់ េគហទំព័រ!1-បd្ើតបណ8*ញទំនក់ទំនងសង្ម ដូចជ í្*សប៊ុក ( )& & 2-ករផ*Iព្ផ*4យតមរយៈបណ8*រថយន្n*ុង ម៉ូតូតុកតុក តកសុី ï*I*ងៗ &
- 28. ៥ ខeឹមRរៃនគ@!9ង! ខ្ឹមសរសំខន់ៗ ô*គö**ង õះគឺ ផ*4ព្ផ*4យ នូវផលិតផល និង ទំនិញ p*ល n*ុមហ៊ុន រú អ្កចង់លក់ផលិតផល បន រú ផ*Iព្ផ*4យ äដល់អតិថិជន រú អ្ក p*លមនតំរូវករអច ចូលÉ្*ងរក ចូលùើលនូវ5ើ á*ហទំព័រ ។ & ៦ J!ជKសJរKស Domain'Name'និង Hos,ng!• www.angkormeas.com.kh តំû* $20 & • Hos,ng តü្* $30 & ទំហំផhុងកឯកRរ(Disk'Space)& 2'GB& HរេផhរទិនG័យកGុងមួយែខ(Bandwidth'Per'Month)& 20GB& Web'Email& Unlimited& Sub'Domains& Unlimited& Web'Mail'& 100& Daily'Back'Up& Unlimited& ijេបស(MySQL)& 20&
- 29. ចំ†*កឯរចនសម្័ន្á*ហទំព័ររបស់ អង្រមស បនDៀបចំ§យមន៖& រច1សមB័នCេគហទំព័រ! អងkរ9ស ទំព័រJដKម ចលនៈ!ពទm Zនជំនិះ របស់J!បK!oស់ p!គqងេអឡិច!តូនិច Register អំពីពួកJយKង " ចលនៈ¶*ទ*. គឺជទំព័រមន៖ និង & " យនជំនិះ គឺជទំព័រp*លមន៖ និង & " p!គqងេអឡិច!តូនិច:!tទំព័រែដល9ន៖Phone និង Computer!& : គឺជទំព័រ p*លអច§យcើង អច ®*©** កំណត់ ផ្ល់សិទ្ លុប ប´្≠ល មន លក្ណៈï*I*ងៗ ។&
- 30. ១ កមvវិធិJ!បK!oស់ • ចំhះលក្ណៈពិÆ*សរបស់Ø∞*បសយ គឺវអចùើលបន≤*ប់កម្វàធី និង ≤*ប់ឧបករណ៍ ពី¥**ះវមនលក្ណៈ អចùើលបន & ២ កមvវិធិJ!បK!oស់ Q ចំhះករDៀបចំQ និង Ø∞*បសយµ*ះ∂ើងគឺ∑*∏វបនយកកម្វàធីមួយចំនួនមក ចូលរួមp*លរួមកម្វàធី ៖& 5 & 2.2 គឺជកម្វàធីសំរប់ នូវ Q រួមមន៖& – 2.2.22 & – 5.3.13& – 3.4.10.1 & 5 គឺជកម្វàធីសំរប់ រូបភពï*I*ងៗ& គឺជកម្វàធីសំរប់ចប់ពណ៌ï*I*ងៗp*លcើងចង់បន & ៣ ឧបករណ៍J!បK!oស់ស!9ប់JបKកេគហទំព័រ , , , , , , ទូរស័ព្R*º*ទ ( , , , , , .) , ។& បេចFកេទសកGុងHររច1េគហទំព័រ! !
- 33. ថវិHរJសGKរសុំគ@!9ង! ' People'Or'Machine Days Unit'Price Subtotal I.'Workshop ''''AKendance 3 2 $15 $90 ''''LCD 1 2 $15 $30 ''''Building 1 2 $60 $120 II.'Website'Development ''''Analysis 1 ! $200 $200 ''''Designer 1 ! $100 $100 ''''Programmer 1 ! $200 $200 III.'Training'and'Support ''''Trainee 2 2 $15 $60 ''''Computer 3 2 $15 $90 Data'Entry 2 2 $20 $40 IV.'Domain'and'Hos,ng ''''Domain 1 ! $20 $20 ''''Hos,ng 1 ! $30 30 Grand'Total $980
- 34. ! Month1 Month2 Week1 Week2 Week3 Week4 Week1 Week2 Week3 Week4 Collect!InformaEon ! ! ! ! ! ! ! ! Gathering!&!Consultancy ! ! ! ! ! ! ! ! Project!Design ! ! ! ! ! ! ! ! Template!Design ! ! ! ! ! ! ! ! Content!Gathering ! ! ! ! ! ! ! ! Web!Develop ! ! ! ! ! ! ! ! TesEng!&!Debug ! ! ! ! ! ! ! ! Develop!User!Manual ! ! ! ! ! ! ! ! Training ! ! ! ! ! ! ! ! Entry!Data ! ! ! ! ! ! ! ! Upgrade!&!Maintenance ! ! ! ! ! ! ! ! រយៈេពលៃនHរអនុវតPន៍គ@!9ង!
- 35. ១ ដំxក់Hលដំបូង – %រ'បចំ@yយ9នHរផ.ពWផXយឥតគិតៃថeកGុងដំxក់Hលដំបូង JដKម{ី@yយ អតិថិជនR|ល់oនJ!ចKនtមុនសិន! – !តូវJធWKHរផ.ពWផXយjមរយៈបx}ញសងkម ដូចt Facebook!,!TwiSer,…! – JធWKHរផ.ពWផXយjមរយៈRរពត៌9ន ទស.1វដPី ! – ែចកខិតបណព័ត៌9ន ! – iក់ Link!^ÄJលKេគហទំព័រព័ត៌9ន េគហទំព័រផ.ពWផXយេផ.ងៗ! ២ ដំxក់Hលប1Çប់(បែនÉមនូវចំនុចÑងJល█) – %រ'បចំ@yយ9នHរផ.ពWផXយ គិតៃថe ចំ@Öះចំនួនែដលoនកំណត់! – JធWKHរផ.ពWផXយjមម៉ូតូតុកតុក áន!កុង និង Taxi!! 'យុទCR!សS!បកួត!បែជង និង ផ.ពWផXយ!
- 36. ! ឯកសរù*Dៀនរបស់ Ωកសæø**ចរ*. អ៊ូ âន់xរិទC ! á*ហទំព័រ . & ! ឯកសរ¿្*កច*gប់0្ើកិច្សន*¡ របស់Ωក ស សូវ¬*ន (បណ√ិតច*gប់ R*Å*សបរំង)& ! Æៀវƒសរណរបស់n*ុមនិសិ*Iត និស*Iិត ≈ៀល∆**យ ជំនន់ទី០៩& (គំ…ង វàបសយ)& ឯកRរ@Zង! !
