Digital Information Law & Your Business - The Alternative Board
•Descargar como PPTX, PDF•
1 recomendación•2,592 vistas
A discussion for business owners of digital information law issues of social media law, data security and data breach law, and trade secrets and corporate espionage issues.
Denunciar
Compartir
Denunciar
Compartir
Recomendados
Recomendados
Más contenido relacionado
La actualidad más candente
La actualidad más candente (20)
Legal Issues Impacting Data Center Owners, Operators & Users

Legal Issues Impacting Data Center Owners, Operators & Users
Cybersecurity Legal and Compliance Issues Business & IT Leaders Must Know -- ...

Cybersecurity Legal and Compliance Issues Business & IT Leaders Must Know -- ...
Cybersecurity Legal Trends: The Evolving Standard of Care for Companies and M...

Cybersecurity Legal Trends: The Evolving Standard of Care for Companies and M...
Cyber Liability Insurance Counseling and Breach Response

Cyber Liability Insurance Counseling and Breach Response
Cyber Insurance, A Novel of 2017, Q1. By Statewide Insurance

Cyber Insurance, A Novel of 2017, Q1. By Statewide Insurance
Cyber Liability & Cyber Insurance - Cybersecurity Seminar Series

Cyber Liability & Cyber Insurance - Cybersecurity Seminar Series
Cyber Security for Your Clients: Business Lawyers Advising Business Clients

Cyber Security for Your Clients: Business Lawyers Advising Business Clients
Overview and Update on the Computer Fraud and Abuse Act (CFAA) for the Data ...

Overview and Update on the Computer Fraud and Abuse Act (CFAA) for the Data ...
Computer Fraud and Abuse Act CLE - Dallas Bar Ass'n (8.22.11)

Computer Fraud and Abuse Act CLE - Dallas Bar Ass'n (8.22.11)
Leadership Through the Firestorm - Legal Counsel's Role in Guiding Through Cy...

Leadership Through the Firestorm - Legal Counsel's Role in Guiding Through Cy...
Cybersecurity for Your Law Firm: Data Security and Data Encryption

Cybersecurity for Your Law Firm: Data Security and Data Encryption
Data Breach Response: Realtime Cyber Incident Simulation

Data Breach Response: Realtime Cyber Incident Simulation
Privacy and Technology in Your Practice: Why it Matters & Where is the Risk

Privacy and Technology in Your Practice: Why it Matters & Where is the Risk
Collin County Bench Bar Conference: Cybersecurity Mitigation & Compliance Str...

Collin County Bench Bar Conference: Cybersecurity Mitigation & Compliance Str...
Destacado
Destacado (7)
OSCON 2013 - Planning an OpenStack Cloud - Tom Fifield

OSCON 2013 - Planning an OpenStack Cloud - Tom Fifield
Similar a Digital Information Law & Your Business - The Alternative Board
Similar a Digital Information Law & Your Business - The Alternative Board (20)
Cybersecurity (and Privacy) Issues - Legal and Compliance Issues Everyone in ...

Cybersecurity (and Privacy) Issues - Legal and Compliance Issues Everyone in ...
Cyber Risks Looming in the Transportation Industry

Cyber Risks Looming in the Transportation Industry
Cyber Risk Presentation to Murphy Chamber of Commerce (5.28.15)

Cyber Risk Presentation to Murphy Chamber of Commerce (5.28.15)
Cybersecurity and Privacy for In-House Counsel: How the New Regulations and G...

Cybersecurity and Privacy for In-House Counsel: How the New Regulations and G...
2015 LOMA Conference - Third party risk management - Session 20

2015 LOMA Conference - Third party risk management - Session 20
The Unseen Enemy - Protecting the Brand, the Assets and the Customers 

The Unseen Enemy - Protecting the Brand, the Assets and the Customers
Cybersecurity | Fraud 2.0 Presentation to the Association of Certified Fraud ...

Cybersecurity | Fraud 2.0 Presentation to the Association of Certified Fraud ...
Cyber security legal and regulatory environment - Executive Discussion

Cyber security legal and regulatory environment - Executive Discussion
Cybersecurity & Data Protection: Thinking About Risk & Compliance

Cybersecurity & Data Protection: Thinking About Risk & Compliance
Corporate & Regulatory Compliance Boot Camp - Data Privacy Compliance

Corporate & Regulatory Compliance Boot Camp - Data Privacy Compliance
Data Privacy Compliance (Series: Corporate & Regulatory Compliance Boot Camp)

Data Privacy Compliance (Series: Corporate & Regulatory Compliance Boot Camp)
ISSA North Texas - SecureWorld Expo Dallas - Cybersecurity Legal Issues: What...

ISSA North Texas - SecureWorld Expo Dallas - Cybersecurity Legal Issues: What...
Legal Issues Impacting Data Center Owners, Operators and Users

Legal Issues Impacting Data Center Owners, Operators and Users
Más de Shawn Tuma
Más de Shawn Tuma (20)
Lifecycle: Responding to a Ransomware Attack - A Professional Breach Guide's ...

Lifecycle: Responding to a Ransomware Attack - A Professional Breach Guide's ...
Incident Response Planning - Lifecycle of Responding to a Ransomware Attack

Incident Response Planning - Lifecycle of Responding to a Ransomware Attack
Cybersecurity is a Team Sport: How to Use Teams, Strategies, and Processes to...

Cybersecurity is a Team Sport: How to Use Teams, Strategies, and Processes to...
Reimagine Your Company Operating Again After a Ransomware Attack -- The Lifec...

Reimagine Your Company Operating Again After a Ransomware Attack -- The Lifec...
The Role of Contracts in Privacy, Cybersecurity, and Data Breach

The Role of Contracts in Privacy, Cybersecurity, and Data Breach
Cybersecurity is a Team Sport: How to Use Teams, Strategies, and Processes to...

Cybersecurity is a Team Sport: How to Use Teams, Strategies, and Processes to...
Cybersecurity is a Team Sport: How to Use Teams, Strategies, and Processes to...

Cybersecurity is a Team Sport: How to Use Teams, Strategies, and Processes to...
The Legal Case for Cyber Risk Management Programs and What They Should Include

The Legal Case for Cyber Risk Management Programs and What They Should Include
Cybersecurity: Cyber Risk Management for Lawyers and Clients

Cybersecurity: Cyber Risk Management for Lawyers and Clients
Cybersecurity is a Team Sport (SecureWorld - Dallas 2018)

Cybersecurity is a Team Sport (SecureWorld - Dallas 2018)
Cybersecurity: Cyber Risk Management for Banks & Financial Institutions

Cybersecurity: Cyber Risk Management for Banks & Financial Institutions
Something is Phishy: Cyber Scams and How to Avoid Them

Something is Phishy: Cyber Scams and How to Avoid Them
Cybersecurity Fundamentals for Legal Professionals (and every other business)

Cybersecurity Fundamentals for Legal Professionals (and every other business)
NYDFS Cybersecurity Regulations - 23 NYCRR Part 500

NYDFS Cybersecurity Regulations - 23 NYCRR Part 500
Último
Sensual Moments: +91 9999965857 Independent Call Girls Vasundhara Delhi {{ Monika}} Online
Booking Contact Details :-
WhatsApp Chat :- [+91-9999965857 ]
The Best Call Girls Delhi At Your Service
Russian Call Girls Delhi Doing anything intimate with can be a wonderful way to unwind from life's stresses, while having some fun. These girls specialize in providing sexual pleasure that will satisfy your fetishes; from tease and seduce their clients to keeping it all confidential - these services are also available both install and outcall, making them great additions for parties or business events alike. Their expert sex skills include deep penetration, oral sex, cum eating and cum eating - always respecting your wishes as part of the experience
(29-April-2024(PSS)
Two shots with one girl: ₹4000/in-call, ₹7000/out-call
Body to body massage with : ₹4500/in-call
Full night for one person: ₹7000/in-call, ₹12000/out-call
Delhi Russian Escorts provide clients with the opportunity to experience an array of activities - everything from dining at upscale restaurants to watching the latest movies. Hotel call girls are available year-round to offer unforgettable experiences and fulfill all of your erotica desires. Escort services go beyond the traditional notion of call girls by providing clients with customized experiences beyond dinner companionship to social events. (29-April-2024(PSS)Sensual Moments: +91 9999965857 Independent Call Girls Vasundhara Delhi {{ Mo...

Sensual Moments: +91 9999965857 Independent Call Girls Vasundhara Delhi {{ Mo...Call Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
The Active Management Value Ratio (AMVR) is a variation of the popular cost-benefit analysis metric commonly uased in the business world the evaluate projects. The AMVR uses the incremental costs and incremental returns between an actively managed mutual fund and an index fund to evaluate the cost-efficiency, or cost-inefficiency, of an actively managed fund relative to a comparable index fund.
The AMVR allows plan sponsors, trustees, and other investment fiduciaries to avoid unwanted fiduciary liability. The AMVR allows attorneys and investors to easily assess the prudence of actively managed mutual funds in terms of investment prudence.
"Active Management Value Ratio", "AMVR" and the "InvestSense" logo are trademarks of InvestSense, LLC.The Active Management Value Ratio: The New Science of Benchmarking Investment...

The Active Management Value Ratio: The New Science of Benchmarking Investment...James Watkins, III JD CFP®
Último (20)
Presentation on Corporate SOCIAL RESPONSIBILITY- PPT.pptx

Presentation on Corporate SOCIAL RESPONSIBILITY- PPT.pptx
Smarp Snapshot 210 -- Google's Social Media Ad Fraud & Disinformation Strategy

Smarp Snapshot 210 -- Google's Social Media Ad Fraud & Disinformation Strategy
KEY NOTE- IBC(INSOLVENCY & BANKRUPTCY CODE) DESIGN- PPT.pptx

KEY NOTE- IBC(INSOLVENCY & BANKRUPTCY CODE) DESIGN- PPT.pptx
IBC (Insolvency and Bankruptcy Code 2016)-IOD - PPT.pptx

IBC (Insolvency and Bankruptcy Code 2016)-IOD - PPT.pptx
Audience profile - SF.pptxxxxxxxxxxxxxxxxxxxxxxxxxxx

Audience profile - SF.pptxxxxxxxxxxxxxxxxxxxxxxxxxxx
How do cyber crime lawyers in Mumbai collaborate with law enforcement agencie...

How do cyber crime lawyers in Mumbai collaborate with law enforcement agencie...
Sensual Moments: +91 9999965857 Independent Call Girls Vasundhara Delhi {{ Mo...

Sensual Moments: +91 9999965857 Independent Call Girls Vasundhara Delhi {{ Mo...
PowerPoint - Legal Citation Form 1 - Case Law.pptx

PowerPoint - Legal Citation Form 1 - Case Law.pptx
The doctrine of harmonious construction under Interpretation of statute

The doctrine of harmonious construction under Interpretation of statute
CAFC Chronicles: Costly Tales of Claim Construction Fails

CAFC Chronicles: Costly Tales of Claim Construction Fails
The Active Management Value Ratio: The New Science of Benchmarking Investment...

The Active Management Value Ratio: The New Science of Benchmarking Investment...
PPT- Voluntary Liquidation (Under section 59).pptx

PPT- Voluntary Liquidation (Under section 59).pptx
Digital Information Law & Your Business - The Alternative Board
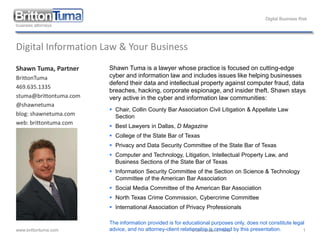
- 1. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 1 Digital Information Law & Your Business Shawn Tuma, Partner BrittonTuma 469.635.1335 stuma@brittontuma.com @shawnetuma blog: shawnetuma.com web: brittontuma.com Shawn Tuma is a lawyer whose practice is focused on cutting-edge cyber and information law and includes issues like helping businesses defend their data and intellectual property against computer fraud, data breaches, hacking, corporate espionage, and insider theft. Shawn stays very active in the cyber and information law communities: Chair, Collin County Bar Association Civil Litigation & Appellate Law Section Best Lawyers in Dallas, D Magazine College of the State Bar of Texas Privacy and Data Security Committee of the State Bar of Texas Computer and Technology, Litigation, Intellectual Property Law, and Business Sections of the State Bar of Texas Information Security Committee of the Section on Science & Technology Committee of the American Bar Association Social Media Committee of the American Bar Association North Texas Crime Commission, Cybercrime Committee International Association of Privacy Professionals The information provided is for educational purposes only, does not constitute legal advice, and no attorney-client relationship is created by this presentation.
- 2. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 2 Social Media Using It To Grow Your Business
- 3. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 3 Data Security & Data Breaches Your Company’s Biggest Threat
- 4. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 4 “Authority” Governing Data Breach • Laws • Types • Common Law (courts) • Statutory Law (legislatures) • Sources • International • Federal • State • Local • Agency Rules & Regulations • Industry Standards
- 5. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 5 What do these sources of “Authority” have in common? • Tell you what must be done following a breach. • Can you guess who “you” is? • “You” is the entity breached.
- 6. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 6 What do you have to do following a data breach? • Execute Breach Response Plan • General Steps • contact attorney (privilege) • assemble your Response Team • contact forensics • contact notification vendor • investigate breach • remediate responsible vulnerabilities • reporting & notification
- 7. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 7 What does “reporting & notification” mean? • Law Enforcement • State Attorneys General • Federal Agencies • FTC, SEC, HHS, etc. • Industry Groups • PCI, FINRA, FDIC • Credit Bureaus • Professional Vendors & Suppliers • Consumers
- 8. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 8 Cost of a Data Breach! • In 2012 • $188.00 per lost record • $188.00 x “X” - $$$$$$$$
- 9. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 9 Story Time • you were CEO of a world-wide company • breach impacting 110 million customers • $61 million in expenses alone • 10% discount to all shoppers • $5 million investment in cybersecurity coalition • offer “free” identity theft and credit monitoring to all affected customers • Net earnings down 34.28% • Earnings per share down 44.60% • Non-cash losses down 487.71% • US sales down 6.60% • Lawsuits, possible enforcement actions, who knows? • and then you learn …
- 10. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 10 Have you ever heard of …
- 11. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 11 Important Questions • Whose 110,000,000+ customers were furious? • Who spent $61 million in expenses? • Who gave a 10% discount to all shoppers? • Who gave $5 million to a cybersecurity coalition? • Who offered “free” identity theft and credit monitoring to all affected customers? • Whose net earnings are down 34.28%? • Whose earnings per share are down 44.60%? • Whose non-cash losses down 487.71%? • Whose US sales are down 6.60%? • Who is defending lawsuits, enforcement actions? • One more question …
- 12. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 12 Allocating risk and mitigating risk by contract • Allocating risk • designate duties & responsibilities A party bears the risk when the agreement allocates the risk to that party. TEX. JUR. 3d Contracts § 123 • indemnify “An undertaking against loss or damage amounts to a guaranty of reimbursement on a payment by the indemnitee. With respect to a promise to indemnify against damages, a right to bring suit does not accrue until the indemnitee has suffered damage or injury by being compelled to pay the judgment or debt.” 14 TEX. JUR. 3d Contribution § 24 • Mitigating risk • require mandatory policies, procedures, and security standards for third parties
- 13. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 13 But all are just contractual obligations • Look to you for relief, you must then go enforce your contractual remedies • Breach of Contract • Inability to perform • Unwillingness to perform • Efficient breach theory • Insolvency / bankruptcy • Cost of litigation to enforce
- 14. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 14 The contractual obligations are important and needed • Show diligence and taking data security more serious than most • FTC – looking at 3rd party contracts • SEC – looking at policies and 3rd party contracts • Post-breach = helpful for attorneys general • But more is required
- 15. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 15 Recent agency advisory statements • January 2014: SEC indicates that the new standard of care for companies may require policies in place for: 1. Prevention, detection, and response to cyber attacks and data breaches, 2. IT training focused on security, and 3. Vendor access to company systems and vendor due diligence. • January 31, 2014: GMR Transcription Svcs – FTC case – is requiring businesses to follow 3 steps when contracting with 3rd party service providers: 1. Investigate by exercising due diligence before hiring data service providers. 2. Obligate their data service providers to adhere to the appropriate level of data security protections through contractual agreements with provider. 3. Verify that the data service providers are adequately protecting data as required by the contractual standards.
- 16. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 16 Key Takeaways • You are still liable for breaches caused by 3rd parties! • Contractual agreements are not a magic wand to make liability go away – you are still responsible but now have a remedy against the 3rd party • “Trust, but verify” = Audit! • Cyber Insurance
- 17. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 17 Sun Tzu – The Art of War “In all fighting the direct method may be used for joining battle, but indirect methods will be needed to secure victory.” “You can be sure of succeeding in your attacks if you attack places which are not defended.” “The spot where we intend to fight must not be made known; for then the enemy will have to prepare against a possible attack at several different points; and his forces being thus distributed in many directions, the numbers we shall have to face at any given point will be proportionately few.”
- 18. Digital Business Risk www.brittontuma.com © 2014 Shawn E. Tuma 18 Trade Secrets Yes, Your Company Has Them and Needs to Protect Them!
