Cambio dinamico de datos
•Descargar como DOCX, PDF•
0 recomendaciones•154 vistas
Denunciar
Compartir
Denunciar
Compartir
Recomendados
Recomendados
Modularny JavaScript - meet.js

Prezentacja przygotowana przez Patryka yarpo Jara na pierwsze meet.js w Gdańsku 11 marca 2013 r.
Dotyczy modularnego JS
Project Roslyn: Exposing the C# and VB compiler’s code analysis

Project Roslyn: Exposing the C# and VB compiler’s code analysisMicrosoft Developer Network (MSDN) - Belgium and Luxembourg
More info on http://www.techdays.be Coding dojo

A presentation made by eXo Platform SEA.
Presentation introduce and demo about Coding Dojo, a methodology enhance the coding skills of attendees by doing some very small exercices in a funny atmosphere. This is like when you want to practice a sport like Judo, you need to practice some basic exercices with some judo masters before doing serious business like competitions.
There are usually two styles of exercices :
- Kata prepared by someone before the session and executed in front of the public or
Randori, a more exploraty form of a Kata where the whole group participates.
Dojo: Beautiful Web Apps, Fast

An overview of the dojo javascript toolkit showcasing several of the powerful widgets added in dojo 1.7.
Time-Based Blind SQL Injection

This presentation was given at the November 2012 chapter meeting of the Memphis ISSA. In the presentation, I discuss various methods of exploiting common SQL Injection vulnerabilities, as well as present a specialized technique known as Time-Based Blind SQL Injection. Related to the latter, I give a scenario in which other common forms of SQL Injection would fail to produce results for a penetration tester or attacker, and show how one may overcome this situation by using the specialized technique. The scenario given, along with the sample code, is NOT a contrived example, but instead is closely based on a real-world application that I encountered as part of an assessment.
A live demonstration of the common forms of SQL Injection was also given which utilized the OWASP Broken Web Apps VM, DVWA, Burp Proxy and SQL Power Injector. To demo a real-world time-based blind injection, I created and locally hosted a new application which closely mimicked the real-world application mentioned above.
How dojo works

Basic Introduction to Dojo JavaScript toolkit. Find Video tutorial at http://www.youtube.com/watch?v=Q3S3yb8OlTU
Multi-tenancy in the cloud

Multi-tenancy refers to the ability to run multiple users of an application on a shared infrastructure. Such an infrastructure makes oblivious the need for having a dedicated infrastructure for each user or user group. This helps in the economies of scale by saving on the per user cost of operations.
Several SaaS based applications like SalesForce.com provide a fine grained multi-tenant model. The common way to implement multi-tenancy is at the data layer, however this introduces a fair set of challenges when one decides to move to the cloud. Most solutions would focus around spreading the users across the cloud, however, what happens when a user is large enough to spread across the cloud? If you have an existing application, it requires a complete rewrite and also forces fairly significant changes to the existing data model. The current set of multi-tenant practices do not address the challenges of dynamic elasticity. The session tries to look at the challenges and possible solutions for the context.
Más contenido relacionado
Destacado
Modularny JavaScript - meet.js

Prezentacja przygotowana przez Patryka yarpo Jara na pierwsze meet.js w Gdańsku 11 marca 2013 r.
Dotyczy modularnego JS
Project Roslyn: Exposing the C# and VB compiler’s code analysis

Project Roslyn: Exposing the C# and VB compiler’s code analysisMicrosoft Developer Network (MSDN) - Belgium and Luxembourg
More info on http://www.techdays.be Coding dojo

A presentation made by eXo Platform SEA.
Presentation introduce and demo about Coding Dojo, a methodology enhance the coding skills of attendees by doing some very small exercices in a funny atmosphere. This is like when you want to practice a sport like Judo, you need to practice some basic exercices with some judo masters before doing serious business like competitions.
There are usually two styles of exercices :
- Kata prepared by someone before the session and executed in front of the public or
Randori, a more exploraty form of a Kata where the whole group participates.
Dojo: Beautiful Web Apps, Fast

An overview of the dojo javascript toolkit showcasing several of the powerful widgets added in dojo 1.7.
Time-Based Blind SQL Injection

This presentation was given at the November 2012 chapter meeting of the Memphis ISSA. In the presentation, I discuss various methods of exploiting common SQL Injection vulnerabilities, as well as present a specialized technique known as Time-Based Blind SQL Injection. Related to the latter, I give a scenario in which other common forms of SQL Injection would fail to produce results for a penetration tester or attacker, and show how one may overcome this situation by using the specialized technique. The scenario given, along with the sample code, is NOT a contrived example, but instead is closely based on a real-world application that I encountered as part of an assessment.
A live demonstration of the common forms of SQL Injection was also given which utilized the OWASP Broken Web Apps VM, DVWA, Burp Proxy and SQL Power Injector. To demo a real-world time-based blind injection, I created and locally hosted a new application which closely mimicked the real-world application mentioned above.
How dojo works

Basic Introduction to Dojo JavaScript toolkit. Find Video tutorial at http://www.youtube.com/watch?v=Q3S3yb8OlTU
Multi-tenancy in the cloud

Multi-tenancy refers to the ability to run multiple users of an application on a shared infrastructure. Such an infrastructure makes oblivious the need for having a dedicated infrastructure for each user or user group. This helps in the economies of scale by saving on the per user cost of operations.
Several SaaS based applications like SalesForce.com provide a fine grained multi-tenant model. The common way to implement multi-tenancy is at the data layer, however this introduces a fair set of challenges when one decides to move to the cloud. Most solutions would focus around spreading the users across the cloud, however, what happens when a user is large enough to spread across the cloud? If you have an existing application, it requires a complete rewrite and also forces fairly significant changes to the existing data model. The current set of multi-tenant practices do not address the challenges of dynamic elasticity. The session tries to look at the challenges and possible solutions for the context.
Destacado (16)
#win8acad : Building Metro Style Apps with XAML for .NET Developers

#win8acad : Building Metro Style Apps with XAML for .NET Developers
Project Roslyn: Exposing the C# and VB compiler’s code analysis

Project Roslyn: Exposing the C# and VB compiler’s code analysis
Cambio dinamico de datos
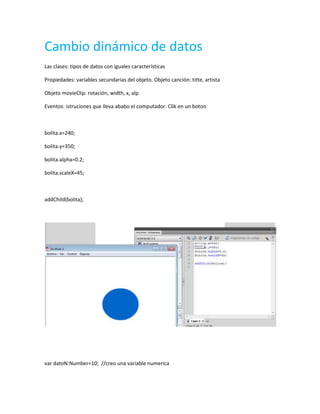
- 1. Cambio dinámico de datos Las clases: tipos de datos con iguales características Propiedades: variables secundarias del objeto. Objeto canción: titte, artista Objeto movieClip: rotación, width, x, alp Eventos: istruciones que lleva ababo el computador. Clik en un boton bolita.x=240; bolita.y=350; bolita.alpha=0.2; bolita.scaleX=45; addChild(bolita); var datoN:Number=10; //creo una variable numerica
- 2. var datoT:String=detoN.toString(); //convierto la variable en numerica o de tipo string trace (datoT): trace (typeof datoT): var saludo="bienvenidos"; var nombre"omaira.com"; var misaludo=saludo.concat{" ",nombre}; trace (misaludo);
- 3. var saludo="bienvenidos"; var nombre"omaira.com"; var misaludo=saludo.concat{" ",nombre}; trace (misaludo); var a="4"; var b="5" var c=a+b; trace (c);
- 4. var a="4"; var b="5" var c=a+b; trace (c); var a=4; var b=5; trace (a==b); var a=4; var b=4; trace (a==b); var a="hola"; var b="ola"; trace (a==b); stop(); var username="123";
- 5. var clave"123"; if(username==clave){ gotoAndStop(5); }else{ gotoAndStop*(10); } force-download asociatividad y preferencia de operaciones en actionscript