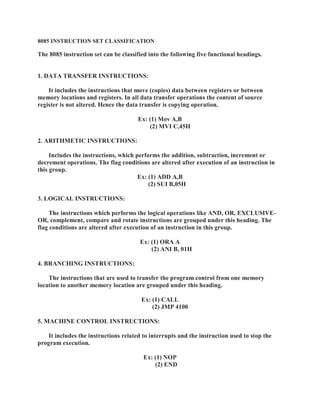
8085 instruction set and addressing modes
- 1. ¡ ¢ £ ¤ ¥ ¦ § ¨ © ¦ £ ¤ ¥ ¦ © ¥ ¥ £ £ © ¦ £ ¤ ! # $ % ' $ ! ( # $ ' ) 0 ' 1 ) # # ! 2 ! 3 ! $ ( $ 2 ( 1 1 ( 4 ! 5 2 ! 6 2 ' $ ! ( ) 1 ) 3 ! 5 # 7 8 7 9 @ @ A @ B C D E A F B C A G H F I B C P F $ ! ' 1 3 # $ ! # $ % ' $ ! ( # $ ) $ Q ( 6 R ' ( S ! # T 3 ) $ ) 0 $ 4 % 5 ! # $ % # ( % 0 $ 4 Q Q ( % U 1 ( ' ) $ ! ( # ) 3 % 5 ! # $ % # 7 F ) 1 1 3 ) $ ) $ % ) # 2 % ( S % ) $ ! ( # $ ' ( $ $ ( 2 # ( % ' % 5 ! # $ % ! # ( $ ) 1 $ % 3 7 V ' $ 3 ) $ ) $ % ) # 2 % ! # ' ( S U ! 5 ( S % ) $ ! ( 7 E W P R 8 T X ( 6 @ Y ` R a T X b F H Y c V a 7 @ A F V X E F H F B C A G H F I B C P F ' 1 3 # $ ! # $ % ' $ ! ( # Y 4 ! ' S % 2 ( % Q # $ ) 3 3 ! $ ! ( Y # 0 $ % ) ' $ ! ( Y ! ' % Q $ ( % 3 ' % Q $ ( S % ) $ ! ( # 7 2 1 ) 5 ' ( 3 ! $ ! ( # ) % ) 1 $ % 3 ) 2 $ % W ' $ ! ( ( 2 ) ! # $ % ' $ ! ( ! $ ! # 5 % ( S 7 E W P R 8 T @ 9 9 @ Y ` R a T C G F ` Y V d 7 e I f F H @ e F B C A G H F I B C P ! # $ % ' $ ! ( # 4 ! ' S % 2 ( % Q # $ 1 ( 5 ! ' ) 1 ( S % ) $ ! ( # 1 ! g @ B 9 Y I A Y E h H e G C F b E i I A Y ' ( Q S 1 Q $ Y ' ( Q S ) % ) 3 % ( $ ) $ ! # $ % ' $ ! ( # ) % 5 % ( S 3 3 % $ ! # ) 3 ! 5 7 2 1 ) 5 ' ( 3 ! $ ! ( # ) % ) 1 $ % 3 ) 2 $ % W ' $ ! ( ( 2 ) ! # $ % ' $ ! ( ! $ ! # 5 % ( S 7 E W P R 8 T I A @ @ R a T @ B F ` Y 8 V c 7 ` A @ B H V F B f F B C A G H F I B C P ! # $ % ' $ ! ( # $ ) $ ) % # 3 $ ( $ % ) # 2 % $ S % ( 5 % ) Q ' ( $ % ( 1 2 % ( Q ( Q Q ( % U 1 ( ' ) $ ! ( $ ( ) ( $ % Q Q ( % U 1 ( ' ) $ ! ( ) % 5 % ( S 3 3 % $ ! # ) 3 ! 5 7 E W P R 8 T H @ e e R a T p X q c 8 7 X @ H V F B E H I B A I e F B C A G H F I B C P F $ ! ' 1 3 # $ ! # $ % ' $ ! ( # % 1 ) $ 3 $ ( ! $ % % S $ # ) 3 $ ! # $ % ' $ ! ( # 3 $ ( # $ ( S $ S % ( 5 % ) Q W ' $ ! ( 7 E W P R 8 T B I q R a T E B 9
- 2. r r § ¥ ¥ £ ¤ s t r ¥ ¡ ¢ x E 6 % U ! # $ % ' $ ! ( ( 2 ) S % ( 5 % ) Q ) # $ ( ( S % ) $ ( ) 3 ) $ ) 7 x Q $ ( 3 ( 2 # S ' ! 2 U ! 5 $ 3 ) $ ) $ ( 0 ( S % ) $ 3 0 U $ ! # $ % ' $ ! ( ! # ' ) 1 1 3 @ 3 3 % # # ! 5 7 x ) # $ 2 ( 1 1 ( 4 ! 5 3 ! 2 2 % $ $ U S # ( 2 ) 3 3 % # # ! 5 7 8 7 F Q Q 3 ! ) $ @ 3 3 % # # ! 5 a 7 9 ! % ' $ @ 3 3 % # # ! 5 d 7 A 5 ! # $ % @ 3 3 % # # ! 5 c 7 A 5 ! # $ % F 3 ! % ' $ @ 3 3 % # # ! 5 7 F Q S 1 ! 3 @ 3 3 % # # ! 5 8 7 F Q Q 3 ! ) $ @ 3 3 % # # ! 5 P x F ! Q Q 3 ! ) $ ) 3 3 % # # ! 5 Q ( 3 Y $ 3 ) $ ) ! # # S ' ! 2 ! 3 ! $ ! # $ % ' $ ! ( ! $ # 1 2 7 3 ) $ ) 4 ! 1 1 0 ) S ) % $ ( 2 $ S % ( 5 % ) Q ! # $ % ' $ ! ( 7 x E h 7 X b F ` Y d E V i X ( 6 $ 3 ) $ ) d E V 5 ! 6 ! $ ! # $ % ' $ ! ( $ ( ` % 5 ! # $ % u e h F C q Y a v V 7 a 7 9 ! % ' $ @ 3 3 % # # ! 5 P x F 3 ! % ' $ ) 3 3 % # # ! 5 Q ( 3 Y $ ) 3 3 % # # ( 2 $ 3 ) $ ) ! # # S ' ! 2 ! 3 ! $ ! # $ % ' $ ! ( 7 3 ) $ ) 4 ! 1 1 0 ! Q Q ( % U 7 F $ ! # ) 3 3 % # # ! 5 Q ( 3 Y $ S % ( 5 % ) Q ! # $ % ' $ ! ( # ) 3 3 ) $ ) ' ) 0 # $ ( % 3 ! 3 ! 2 2 % $ Q Q ( % U 7 x E h 7 e 9 @ 8 V i e ( ) 3 $ 3 ) $ ) ) 6 ) ! 1 ) 0 1 ! Q Q ( % U 1 ( ' ) $ ! ( 8 V ! $ ( ) ' ' Q 1 ) $ ( % u C V e 9 d V d 7 A 5 ! # $ % @ 3 3 % # # ! 5 P x F % 5 ! # $ % ) 3 3 % # # ! 5 Q ( 3 Y $ ! # $ % ' $ ! ( # S ' ! 2 ! # $ ) Q ( 2 $ % 5 ! # $ % ! 4 ! ' $ 3 ) $ ) ! # ) 6 ) ! 1 ) 0 1 7 x E h 7 X I b @ Y ` i X ( 6 $ ' ( $ $ ( 2 ` % 5 ! # $ % $ ( @ % 5 ! # $ % u C q V e u @ 9 9 H 7 c 7 A 5 ! # $ % F 3 ! % ' $ @ 3 3 % # # ! 5 P x F % 5 ! # $ % ! 3 ! % ' $ ) 3 3 % # # ! 5 Q ( 3 Y $ ! # $ % ' $ ! ( # S ' ! 2 ! # $ ) Q ( 2 $ % 5 ! # $ % ! 4 ! ' $ ) 3 3 % # # ( 2 $ 3 ) $ ) ! # ) 6 ) ! 1 ) 0 1 7 V % $ 3 ) $ ) 4 ! 1 1 0 ! Q Q ( % U ) 3 $ ) 3 3 % # # 4 ! 1 1 0 ! $ % 5 ! # $ % S ) ! % 7 x E h 7 X I b @ Y X i Q Q ( % U 3 ) $ ) ) 3 3 % # # 3 0 U V e S ) ! % ! # Q ( 6 3 $ ( @ % 5 ! # $ % 7 e 9 @ h ` 7 7 F Q S 1 ! 3 @ 3 3 % # # ! 5 P x F ! Q S 1 ! 3 ) 3 3 % # # ! 5 Q ( 3 Y $ ! # $ % ' $ ! ( ! $ # 1 2 # S ' ! 2 ! # $ 3 ) $ ) $ ( 0 ( S % ) $ 3 7 x E h 7 H X @ i H ( Q S 1 Q $ $ ' ( $ $ ( 2 ) ' ' Q 1 ) $ ( % u A @ e
- 3. I S ' ( 3 I S % ) 3 E W S 1 ) ) $ ! ( ( 2 F # $ % ' $ ! ( 9 # ' % ! S $ ! ( X I b A 3 Y A # X Y A # A 3 Y X w x y € ‚ x ƒ „ x … ‚ † ‡ ˆ ‰ „ ‘ x ’ ‡ „ ‘ “ ” • ‘ “ x ” ˆ ‰ ’ – — “ „ “ ” „ ‘ ‚ … † ‘ “ x ” † x y “ ‡ „ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ „ x … ‚ † ‡ ‚ ‡ ˜ “ „ ‘ ‡ ‚ “ ” ‘ x ‘ — ‡ ’ ‡ „ ‘ “ ” • ‘ “ x ” ‚ ‡ ˜ “ „ ‘ ‡ ‚ ™ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ „ x … ‚ † ‡ ‚ ‡ ˜ “ „ ‘ ‡ ‚ • ‚ ‡ ” x ‘ • d ‘ ‡ ‚ ‡ ’ e f x ” ‡ x ‘ — ‡ x y ‡ ‚ • ” ’ „ “ „ • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” g “ ‘ „ d x † • ‘ “ x ” “ „ „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ e E W ) Q S 1 P X I b ` Y H ( % X I b ` Y X X b F A 3 Y 3 ) $ ) X Y 3 ) $ ) k x l ‡ “ ƒ ƒ ‡ ’ “ • ‘ ‡ m n h “ ‘ – — ‡ m n h “ ‘ ’ • ‘ • “ „ „ ‘ x ‚ ‡ ’ “ ” ‘ — ‡ ’ ‡ „ ‘ “ ” • ‘ “ x ” ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € e f ‘ — ‡ x y ‡ ‚ • ” ’ “ „ • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” g “ ‘ „ d x † • ‘ “ x ” “ „ „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ e E W ) Q S 1 P X b F ` Y v V ( % X b F X Y v V e 9 @ 8 o i 0 ! $ ) 3 3 % # # j x • ’ • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” g „ y ‡ † “ “ ‡ ’ h € • p q n h “ ‘ • ’ ’ ‚ ‡ „ „ “ ” ‘ — ‡ x y ‡ ‚ • ” ’ g • ‚ ‡ † x y “ ‡ ’ ‘ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ „ x … ‚ † ‡ • ‚ ‡ ” x ‘ • d ‘ ‡ ‚ ‡ ’ e E W ) Q S 1 P e 9 @ a d c V e 9 @ h ` r 9 A 5 7 S ) ! % j x • ’ • † † … ƒ … d • ‘ x ‚ “ ” ’ “ ‚ ‡ † ‘ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ ’ ‡ „ “ ˜ ” • ‘ ‡ ’ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ y x “ ” ‘ ‘ x • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” e – — “ „ “ ” „ ‘ ‚ … † ‘ “ x ” † x y “ ‡ „ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — • ‘ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” “ ” ‘ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e – — ‡ † x ” ‘ ‡ ” ‘ „ x ‡ “ ‘ — ‡ ‚ ‘ — ‡ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ x ‚ ‘ — ‡ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” • ‚ ‡ ” x ‘ • d ‘ ‡ ‚ ‡ ’ e E W ) Q S 1 P e 9 @ h ` e h F A 5 7 S ) ! % Y 8 o i 0 ! $ 3 ) $ ) j x • ’ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ “ ƒ ƒ ‡ ’ “ • ‘ ‡ – — ‡ “ ” „ ‘ ‚ … † ‘ “ x ” d x • ’ „ p q n h “ ‘ ’ • ‘ • “ ” ‘ — ‡ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ ’ ‡ „ “ ˜ ” • ‘ ‡ ’ “ ” ‘ — ‡ x y ‡ ‚ • ” ’ e s W ) Q S 1 P e h F V Y a d c V ( % e h F V Y h t u e V e 9 8 o i 0 ! $ ) 3 3 % # # j x • ’ i • ” ’ j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ ’ “ ‚ ‡ † ‘ – — ‡ “ ” „ ‘ ‚ … † ‘ “ x ” † x y “ ‡ „ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” y x “ ” ‘ ‡ ’ x … ‘ h € ‘ — ‡ p q n h “ ‘ • ’ ’ ‚ ‡ „ „ “ ” ‘ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ j • ” ’ † x y “ ‡ „ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ ” ‡ v ‘ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” “ ” ‘ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ i e – — ‡ † x ” ‘ ‡ ” ‘ „ x „ x … ‚ † ‡ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” „ • ‚ ‡ ” x ‘ • d ‘ ‡ ‚ ‡ ’ e E W ) Q S 1 P e V e 9 a c V
- 4. C @ 8 o i 0 ! $ ) 3 3 % # # p q n h “ ‘ • ’ ’ ‚ ‡ „ „ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ‚ ‡ † x y “ ‡ ’ “ ” ‘ x ‘ — ‡ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ x y ‡ ‚ • ” ’ e – — “ „ “ „ • w n h € ‘ ‡ “ ” „ ‘ ‚ … † ‘ “ x ” g ‘ — ‡ „ ‡ † x ” ’ h € ‘ ‡ „ y ‡ † “ “ ‡ „ ‘ — ‡ d x x n x ‚ ’ ‡ ‚ • ’ ’ ‚ ‡ „ „ • ” ’ ‘ — ‡ ‘ — “ ‚ ’ h € ‘ ‡ „ y ‡ † “ “ ‡ „ ‘ — ‡ — “ ˜ — n x ‚ ’ ‡ ‚ • ’ ’ ‚ ‡ „ „ e E W ) Q S 1 P C @ c d V C @ h A 5 7 S ) ! % y ‘ x ‚ ‡ • † † … ƒ … d • ‘ x ‚ “ ” ’ “ ‚ ‡ † ‘ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ‚ ‡ † x y “ ‡ ’ “ ” ‘ x ‘ — ‡ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ x y ‡ ‚ • ” ’ ˆ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ e – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ‚ ‡ ” x ‘ • d ‘ ‡ ‚ ‡ ’ e E W ) Q S 1 P C @ h ` C V e 9 8 o i 0 ! $ ) 3 3 % # # y ‘ x ‚ ‡ i • ” ’ j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ ’ “ ‚ ‡ † ‘ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ j • ‚ ‡ „ ‘ x ‚ ‡ ’ “ ” ‘ x ‘ — ‡ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ p q n h “ ‘ • ’ ’ ‚ ‡ „ „ “ ” ‘ — ‡ x y ‡ ‚ • ” ’ • ” ’ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x i ‚ ‡ ˜ “ „ ‘ ‡ ‚ • ‚ ‡ „ ‘ x ‚ ‡ ’ “ ” ‘ x ‘ — ‡ ” ‡ v ‘ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” h € “ ” † ‚ ‡ ƒ ‡ ” ‘ “ ” ˜ ‘ — ‡ x y ‡ ‚ • ” ’ e – — ‡ † x ” ‘ ‡ ” ‘ „ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ i j • ‚ ‡ ” x ‘ • d ‘ ‡ ‚ ‡ ’ e – — “ „ “ „ • w n h € ‘ ‡ “ ” „ ‘ ‚ … † ‘ “ x ” g ‘ — ‡ „ ‡ † x ” ’ h € ‘ ‡ „ y ‡ † “ “ ‡ „ ‘ — ‡ d x x n x ‚ ’ ‡ ‚ • ’ ’ ‚ ‡ „ „ • ” ’ ‘ — ‡ ‘ — “ ‚ ’ h € ‘ ‡ „ y ‡ † “ “ ‡ „ ‘ — ‡ — “ ˜ — n x ‚ ’ ‡ ‚ • ’ ’ ‚ ‡ „ „ e E W ) Q S 1 P C V e 9 a c v V h H V f ( s v † — • ” ˜ ‡ i • ” ’ j x “ ‘ — z • ” ’ s – — ‡ † x ” ‘ ‡ ” ‘ „ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ i • ‚ ‡ ‡ v † — • ” ˜ ‡ ’ x “ ‘ — ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ z g • ” ’ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ j • ‚ ‡ ‡ v † — • ” ˜ ‡ ’ x “ ‘ — ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ s e E W ) Q S 1 P h H V f C q V e ( w x y € i • ” ’ j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ ‘ x ‘ — ‡ „ ‘ • † { y x “ ” ‘ ‡ ‚ – — ‡ “ ” „ ‘ ‚ … † ‘ “ x ” d x • ’ „ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i • ” ’ j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ “ ” ‘ x ‘ — ‡ „ ‘ • † { y x “ ” ‘ ‡ ‚ ‚ ‡ ˜ “ „ ‘ ‡ ‚ g ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i ‚ ‡ ˜ “ „ ‘ ‡ ‚ y ‚ x l “ ’ ‡ ‘ — ‡ — “ ˜ — n x ‚ ’ ‡ ‚ • ’ ’ ‚ ‡ „ „ • ” ’ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ j ‚ ‡ ˜ “ „ ‘ ‡ ‚ y ‚ x l “ ’ ‡ ‘ — ‡ d x x n x ‚ ’ ‡ ‚ • ’ ’ ‚ ‡ „ „ e – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i • ” ’ j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ • ‚ ‡ ” x ‘ • d ‘ ‡ ‚ ‡ ’ e E W ) Q S 1 P C q V e h V e ( s v † — • ” ˜ ‡ i • ” ’ j x “ ‘ — ‘ x y x „ ‘ • † { – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ j ‚ ‡ ˜ “ „ ‘ ‡ ‚ • ‚ ‡ ‡ v † — • ” ˜ ‡ ’ x “ ‘ — ‘ — ‡ „ ‘ • † { d x † • ‘ “ x ” y x “ ” ‘ ‡ ’ x … ‘ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ „ ‘ • † { y x “ ” ‘ ‡ ‚ ‚ ‡ ˜ “ „ ‘ ‡ ‚ e – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i ‚ ‡ ˜ “ „ ‘ ‡ ‚ • ‚ ‡ ‡ v † — • ” ˜ ‡ ’ x “ ‘ — ‘ — ‡ ” ‡ v ‘ „ ‘ • † { d x † • ‘ “ x ” ˆ y | } p ™ — x x ‡ l ‡ ‚ g ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ „ ‘ • † { y x “ ” ‘ ‡ ‚ ‚ ‡ ˜ “ „ ‘ ‡ ‚ • ‚ ‡ ” x ‘ • d ‘ ‡ ‚ ‡ ’ e
- 5. E W ) Q S 1 P h V e q G C V A 5 7 S ) ! % | … „ — ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ x ” ‘ x „ ‘ • † { – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ ’ ‡ „ “ ˜ ” • ‘ ‡ ’ “ ” ‘ — ‡ x y ‡ ‚ • ” ’ • ‚ ‡ † x y “ ‡ ’ x ” ‘ x ‘ — ‡ „ ‘ • † { “ ” ‘ — ‡ x d d x x “ ” ˜ „ ‡ ~ … ‡ ” † ‡ e – — ‡ „ ‘ • † { y x “ ” ‘ ‡ ‚ ‚ ‡ ˜ “ „ ‘ ‡ ‚ “ „ ’ ‡ † ‚ ‡ ƒ ‡ ” ‘ ‡ ’ • ” ’ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ — “ ˜ — x ‚ ’ ‡ ‚ ‚ ‡ ˜ “ „ ‘ ‡ ‚ ˆ g z g i g € • ‚ ‡ † x y “ ‡ ’ “ ” ‘ x ‘ — • ‘ d x † • ‘ “ x ” e – — ‡ „ ‘ • † { y x “ ” ‘ ‡ ‚ ‚ ‡ ˜ “ „ ‘ ‡ ‚ “ „ ’ ‡ † ‚ ‡ ƒ ‡ ” ‘ ‡ ’ • ˜ • “ ” • ” ’ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ d x x n x ‚ ’ ‡ ‚ ‚ ‡ ˜ “ „ ‘ ‡ ‚ ˆ w g s g j g d • ˜ „ • ‚ ‡ † x y “ ‡ ’ ‘ x ‘ — • ‘ d x † • ‘ “ x ” e E W ) Q S 1 P q G C V ` ( % q G C V @ q I q A 5 7 S ) ! % | x y x „ ‘ • † { ‘ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” y x “ ” ‘ ‡ ’ x … ‘ h € ‘ — ‡ „ ‘ • † { y x “ ” ‘ ‡ ‚ ‚ ‡ ˜ “ „ ‘ ‡ ‚ • ‚ ‡ † x y “ ‡ ’ ‘ x ‘ — ‡ d x x n x ‚ ’ ‡ ‚ ‚ ‡ ˜ “ „ ‘ ‡ ‚ ˆ w g s g j g „ ‘ • ‘ … „ d • ˜ „ x ‘ — ‡ x y ‡ ‚ • ” ’ e – — ‡ „ ‘ • † { y x “ ” ‘ ‡ ‚ “ „ “ ” † ‚ ‡ ƒ ‡ ” ‘ ‡ ’ h € p • ” ’ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — • ‘ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” • ‚ ‡ † x y “ ‡ ’ ‘ x ‘ — ‡ — “ ˜ — n x ‚ ’ ‡ ‚ ‚ ‡ ˜ “ „ ‘ ‡ ‚ ˆ g z g i g € x ‘ — ‡ x y ‡ ‚ • ” ’ e – — ‡ „ ‘ • † { y x “ ” ‘ ‡ ‚ ‚ ‡ ˜ “ „ ‘ ‡ ‚ “ „ • ˜ • “ ” “ ” † ‚ ‡ ƒ ‡ ” ‘ ‡ ’ h € p e E W ) Q S 1 P q I q V ( % q I q @ I G i 0 ! $ S ( % $ ) 3 3 % # # … ‘ y … ‘ ’ • ‘ • ‚ x ƒ • † † … ƒ … d • ‘ x ‚ ‘ x • y x ‚ ‘ x “ ‘ — m n h “ ‘ • ’ ’ ‚ ‡ „ „ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ‚ ‡ † x y “ ‡ ’ “ ” ‘ x ‘ — ‡ f ‚ y x ‚ ‘ „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ x y ‡ ‚ • ” ’ e E W ) Q S 1 P I G D V F B i 0 ! $ S ( % $ ) 3 3 % # # f ” y … ‘ ’ • ‘ • ‘ x • † † … ƒ … d • ‘ x ‚ ‚ x ƒ • y x ‚ ‘ x “ ‘ — m n h “ ‘ • ’ ’ ‚ ‡ „ „ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ “ ” y … ‘ y x ‚ ‘ ’ ‡ „ “ ˜ ” • ‘ ‡ ’ “ ” ‘ — ‡ x y ‡ ‚ • ” ’ • ‚ ‡ ‚ ‡ • ’ • ” ’ d x • ’ ‡ ’ “ ” ‘ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e E W ) Q S 1 P F B H V I S ' ( 3 I S % ) 3 E W S 1 ) ) $ ! ( ( 2 F # $ % ' $ ! ( 9 # ' % ! S $ ! ( @ 9 9 A X € ’ ’ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € g ‘ x • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ x y ‡ ‚ • ” ’ ˆ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € • ‚ ‡ • ’ ’ ‡ ’ ‘ x ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ „ ‘ x ‚ ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e f ‘ — ‡ x y ‡ ‚ • ” ’ “ „ • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” g “ ‘ „ d x † • ‘ “ x ” “ „ „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ e € d d d • ˜ „ • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ • ’ ’ “ ‘ “ x ” e E W ) Q S 1 P @ 9 9 ` ( % @ 9 9 X @ 9 H A € ’ ’ ‚ ‡ ˜ “ „ ‘ ‡ ‚ ‘ x • † † … ƒ … d • ‘ x ‚ x “ ‘ — – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ x y ‡ ‚ • ” ’ ˆ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € • ” ’ k ‘ — ‡ w • ‚ ‚ € d • ˜ • ‚ ‡ • ’ ’ ‡ ’ ‘ x ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡
- 6. X † • ‚ ‚ € • † † … ƒ … d • ‘ x ‚ • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ „ ‘ x ‚ ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e f ‘ — ‡ x y ‡ ‚ • ” ’ “ „ • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” g “ ‘ „ d x † • ‘ “ x ” “ „ „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ e € d d d • ˜ „ • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ • ’ ’ “ ‘ “ x ” e E W ) Q S 1 P @ 9 H ` ( % @ 9 H X @ 9 F i 0 ! $ 3 ) $ ) € ’ ’ “ ƒ ƒ ‡ ’ “ • ‘ ‡ ‘ x • † † … ƒ … d • ‘ x ‚ – — ‡ m n h “ ‘ ’ • ‘ • ˆ x y ‡ ‚ • ” ’ “ „ • ’ ’ ‡ ’ ‘ x ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ „ ‘ x ‚ ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e € d d d • ˜ „ • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ • ’ ’ “ ‘ “ x ” e E W ) Q S 1 P @ 9 F c V @ H F i 0 ! $ 3 ) $ ) € ’ ’ “ ƒ ƒ ‡ ’ “ • ‘ ‡ ‘ x • † † … ƒ … d • ‘ x ‚ x “ ‘ — † • ‚ ‚ € – — ‡ m n h “ ‘ ’ • ‘ • ˆ x y ‡ ‚ • ” ’ • ” ’ ‘ — ‡ w • ‚ ‚ € d • ˜ • ‚ ‡ • ’ ’ ‡ ’ ‘ x ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ „ ‘ x ‚ ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e € d d d • ˜ „ • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ • ’ ’ “ ‘ “ x ” e E W ) Q S 1 P @ H F c V e h F A 5 7 S ) ! % Y 8 o i 0 ! $ 3 ) $ ) j x • ’ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ “ ƒ ƒ ‡ ’ “ • ‘ ‡ – — ‡ “ ” „ ‘ ‚ … † ‘ “ x ” d x • ’ „ p q n h “ ‘ ’ • ‘ • “ ” ‘ — ‡ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ ’ ‡ „ “ ˜ ” • ‘ ‡ ’ “ ” ‘ — ‡ x y ‡ ‚ • ” ’ e s W ) Q S 1 P e h F V Y a d c V ( % e h F V Y h t u 9 @ 9 A 5 7 S ) ! % € ’ ’ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ ‘ x i • ” ’ j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ – — ‡ p q n h “ ‘ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ „ y ‡ † “ “ ‡ ’ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ • ‚ ‡ • ’ ’ ‡ ’ ‘ x ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ • ” ’ ‘ — ‡ „ … ƒ “ „ „ ‘ x ‚ ‡ ’ “ ” ‘ — ‡ i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ e – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ „ x … ‚ † ‡ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ • ‚ ‡ ” x ‘ • d ‘ ‡ ‚ ‡ ’ e f ‘ — ‡ ‚ ‡ „ … d ‘ “ „ d • ‚ ˜ ‡ ‚ ‘ — • ” p q h “ ‘ „ g ‘ — ‡ w ƒ d • ˜ “ „ „ ‡ ‘ e „ x x ‘ — ‡ ‚ d • ˜ „ • ‚ ‡ • ‡ † ‘ ‡ ’ e E W ) Q S 1 P 9 @ 9 V C G ` A X y … h ‘ ‚ • † ‘ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € ‚ x ƒ • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ x y ‡ ‚ • ” ’ ˆ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € • ‚ ‡ „ … h ‘ ‚ • † ‘ ‡ ’ ‚ x ƒ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ g • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ „ ‘ x ‚ ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e f ‘ — ‡ x y ‡ ‚ • ” ’ “ „ • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” g “ ‘ „ d x † • ‘ “ x ” “ „ „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ e € d d d • ˜ „ • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ „ … h ‘ ‚ • † ‘ “ x ” e E W ) Q S 1 P C G ` ` ( % C G ` X C ` ` A X y … h ‘ ‚ • † ‘ „ x … ‚ † ‡ • ” ’ h x ‚ ‚ x x ‚ x ƒ • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ x y ‡ ‚ • ” ’ ˆ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € • ” ’ k ‘ — ‡ x ‚ ‚ x x d • ˜ • ‚ ‡ „ … h ‘ ‚ • † ‘ ‡ ’ ‚ x ƒ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ y d • † ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e f ‘ — ‡ x y ‡ ‚ • ” ’ “ „ • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” g “ ‘ „ d x † • ‘ “ x ” “ „ „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ e € d d d • ˜ „ • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ „ … h ‘ ‚ • † ‘ “ x ” e E W ) Q S 1 P C ` ` ` ( % C ` ` X
- 7. C G F i 0 ! $ 3 ) $ ) y … h ‘ ‚ • † ‘ “ ƒ ƒ ‡ ’ “ • ‘ ‡ ‚ x ƒ • † † … ƒ … d • ‘ x ‚ – — ‡ m n h “ ‘ ’ • ‘ • ˆ x y ‡ ‚ • ” ’ “ „ „ … h ‘ ‚ • † ‘ ‡ ’ ‚ x ƒ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ „ ‘ x ‚ ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e € d d d • ˜ „ • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ „ … h ‘ ‚ • † ‘ “ x ” e E W ) Q S 1 P C G F c V C ` F i 0 ! $ 3 ) $ ) y … h ‘ ‚ • † ‘ “ ƒ ƒ ‡ ’ “ • ‘ ‡ ‚ x ƒ • † † … ƒ … d • ‘ x ‚ x “ ‘ — h x ‚ ‚ x x – — ‡ † x ” ‘ ‡ ” ‘ „ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ i • ‚ ‡ ‡ v † — • ” ˜ ‡ ’ x “ ‘ — ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ z g • ” ’ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ j • ‚ ‡ ‡ v † — • ” ˜ ‡ ’ x “ ‘ — ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ s e E W ) Q S 1 P h H V f F B A A X f ” † ‚ ‡ ƒ ‡ ” ‘ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € h € p – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ ’ ‡ „ “ ˜ ” • ‘ ‡ ’ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € • ‚ ‡ “ ” † ‚ ‡ ƒ ‡ ” ‘ ‡ ’ h € p • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ „ ‘ x ‚ ‡ ’ “ ” ‘ — ‡ „ • ƒ ‡ y d • † ‡ e f ‘ — ‡ x y ‡ ‚ • ” ’ “ „ • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” g “ ‘ „ d x † • ‘ “ x ” “ „ „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ e E W ) Q S 1 P F B A ` ( % F B A X F B h A f ” † ‚ ‡ ƒ ‡ ” ‘ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ h € p – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ ’ ‡ „ “ ˜ ” • ‘ ‡ ’ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ • ‚ ‡ “ ” † ‚ ‡ ƒ ‡ ” ‘ ‡ ’ h € p • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ „ ‘ x ‚ ‡ ’ “ ” ‘ — ‡ „ • ƒ ‡ y d • † ‡ e E W ) Q S 1 P F B h V 9 H A A X z ‡ † ‚ ‡ ƒ ‡ ” ‘ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € h € p – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ ’ ‡ „ “ ˜ ” • ‘ ‡ ’ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € • ‚ ‡ k ’ ‡ † ‚ ‡ ƒ ‡ ” ‘ ‡ ’ h € p • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ „ ‘ x ‚ ‡ ’ “ ” ‘ — ‡ „ • ƒ ‡ y d • † ‡ e f ‘ — ‡ x y ‡ ‚ • ” ’ “ „ • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” g “ ‘ „ d x † • ‘ “ x ” “ „ „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ e E W ) Q S 1 P 9 H A ` ( % 9 H A X 9 H h A z ‡ † ‚ ‡ ƒ ‡ ” ‘ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ h € p – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ ’ ‡ „ “ ˜ ” • ‘ ‡ ’ ‚ ‡ ˜ “ „ ‘ ‡ ‚ y • “ ‚ • ‚ ‡ ’ ‡ † ‚ ‡ ƒ ‡ ” ‘ ‡ ’ h € p • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ „ ‘ x ‚ ‡ ’ “ ” ‘ — ‡ „ • ƒ ‡ y d • † ‡ e E W ) Q S 1 P 9 H h V 9 @ @ ( z ‡ † “ ƒ • d • ’ … … „ ‘ • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ‚ ‡ † — • ” ˜ ‡ ’ ‚ x ƒ • h “ ” • ‚ € l • d … ‡ ‘ x ‘ x x † n h “ ‘ h “ ” • ‚ € † x ’ ‡ ’ ’ ‡ † “ ƒ • d ˆ w z ’ “ ˜ “ ‘ „ e – — “ „ “ „ ‘ — ‡ x ” d € “ ” „ ‘ ‚ … † ‘ “ x ” ‘ — • ‘ … „ ‡ „ ‘ — ‡ • … v “ d “ • ‚ € d • ˜ ‘ x y ‡ ‚ x ‚ ƒ ‘ — ‡ h “ ” • ‚ € ‘ x w z † x ” l ‡ ‚ „ “ x ” g • ” ’ ‘ — ‡ † x ” l ‡ ‚ „ “ x ” y ‚ x † ‡ ’ … ‚ ‡ “ „ ’ ‡ „ † ‚ “ h ‡ ’ h ‡ d x x e y g ‡ g € w g | g w ƒ d • ˜ „ • ‚ ‡ • d ‘ ‡ ‚ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ „ x ‘ — ‡ x y ‡ ‚ • ‘ “ x ” e f ‘ — ‡ l • d … ‡ x ‘ — ‡ d x x n x ‚ ’ ‡ ‚ † n h “ ‘ „ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ “ „ ˜ ‚ ‡ • ‘ ‡ ‚ ‘ — • ” ˆ x ‚ “ € w d • ˜ “ „ „ ‡ ‘ g ‘ — ‡ “ ” „ ‘ ‚ … † ‘ “ x ” • ’ ’ „ q ‘ x ‘ — ‡ d x x n x ‚ ’ ‡ ‚ x … ‚ h “ ‘ „ e
- 8. f ‘ — ‡ l • d … ‡ x ‘ — ‡ — “ ˜ — n x ‚ ’ ‡ ‚ † n h “ ‘ „ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ “ „ ˜ ‚ ‡ • ‘ ‡ ‚ ‘ — • ” ˆ x ‚ “ ‘ — ‡ w • ‚ ‚ € d • ˜ “ „ „ ‡ ‘ g ‘ — ‡ “ ” „ ‘ ‚ … † ‘ “ x ” • ’ ’ „ q ‘ x ‘ — ‡ — “ ˜ — n x ‚ ’ ‡ ‚ x … ‚ h “ ‘ „ e E W ) Q S 1 P 9 @ @ I S ' ( 3 I S % ) 3 E W S 1 ) ) $ ! ( ( 2 F # $ % ' $ ! ( 9 # ' % ! S $ ! ( p X q 8 o i 0 ! $ ) 3 3 % # # ‰ … ƒ y … ” † x ” ’ “ ‘ “ x ” • d d € – — ‡ y ‚ x ˜ ‚ • ƒ „ ‡ ~ … ‡ ” † ‡ “ „ ‘ ‚ • ” „ ‡ ‚ ‚ ‡ ’ ‘ x ‘ — ‡ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ p q n h “ ‘ • ’ ’ ‚ ‡ „ „ ˜ “ l ‡ ” “ ” ‘ — ‡ x y ‡ ‚ • ” ’ e E W ) Q S 1 P p X q a d c V ( % p X q h t u y † x ’ ‡ z ‡ „ † ‚ “ y ‘ “ x ” Š d • ˜ y ‘ • ‘ … „ p H p Q S ( H ) % % U H t ‹ 8 p B H p Q S ( ( H ) % % U H t ‹ p q p Q S ( S ( # ! $ ! 6 C ‹ p X p Q S ( Q ! # C ‹ 8 p u p Q S ( Œ % ( u ‹ 8 p B u p Q S ( ( Œ % ( u ‹ p q E p Q S ( S ) % ! $ U 6 q ‹ 8 p q I p Q S ( S ) % ! $ U ( 3 3 q ‹ 8 o i 0 ! $ ) 3 3 % # # ‰ … ƒ y † x ” ’ “ ‘ “ x ” • d d € – — ‡ y ‚ x ˜ ‚ • ƒ „ ‡ ~ … ‡ ” † ‡ “ „ ‘ ‚ • ” „ ‡ ‚ ‚ ‡ ’ ‘ x ‘ — ‡ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ p q n h “ ‘ • ’ ’ ‚ ‡ „ „ ˜ “ l ‡ ” “ ” ‘ — ‡ x y ‡ ‚ • ” ’ h • „ ‡ ’ x ” ‘ — ‡ „ y ‡ † “ “ ‡ ’ d • ˜ x ‘ — ‡ | y • „ ’ ‡ „ † ‚ “ h ‡ ’ h ‡ d x x e E W ) Q S 1 P p u a d c V ( % p u h t u y † x ’ ‡ z ‡ „ † ‚ “ y ‘ “ x ” Š d • ˜ y ‘ • ‘ … „ H H H ) 1 1 ( H ) % % U H t ‹ 8 H B H H ) 1 1 ( ( H ) % % U H t ‹ 8 o i 0 ! $ ) 3 3 % # # Ž ” † x ” ’ “ ‘ “ x ” • d „ … h ‚ x … ‘ “ ” ‡ † • d d – — ‡ y ‚ x ˜ ‚ • ƒ „ ‡ ~ … ‡ ” † ‡ “ „ ‘ ‚ • ” „ ‡ ‚ ‚ ‡ ’ ‘ x ‘ — ‡ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ p q n h “ ‘ • ’ ’ ‚ ‡ „ „ ˜ “ l ‡ ” “ ” ‘ — ‡ x y ‡ ‚ • ” ’ e ‡ x ‚ ‡ ‘ — ‡ ‘ ‚ • ” „ ‡ ‚ g ‘ — ‡ • ’ ’ ‚ ‡ „ „ x ‘ — ‡ ” ‡ v ‘ “ ” „ ‘ ‚ … † ‘ “ x ” • ‘ ‡ ‚ w € j j ˆ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ y ‚ x ˜ ‚ • ƒ † x … ” ‘ ‡ ‚ “ „
- 9. H q H ) 1 1 ( S ( # ! $ ! 6 C ‹ H X H ) 1 1 ( Q ! # C ‹ 8 H u H ) 1 1 ( Œ % ( u ‹ 8 H B u H ) 1 1 ( ( Œ % ( u ‹ H q E H ) 1 1 ( S ) % ! $ U 6 q ‹ 8 H q I H ) 1 1 ( S ) % ! $ U ( 3 3 q ‹ y … „ — ‡ ’ x ” ‘ x ‘ — ‡ „ ‘ • † { e E W ) Q S 1 P H @ e e a d c V ( % H @ e e h t u A E ( ‰ ‡ ‘ … ‚ ” ‚ x ƒ „ … h ‚ x … ‘ “ ” ‡ … ” † x ” ’ “ ‘ “ x ” • d d € – — ‡ y ‚ x ˜ ‚ • ƒ „ ‡ ~ … ‡ ” † ‡ “ „ ‘ ‚ • ” „ ‡ ‚ ‚ ‡ ’ ‚ x ƒ ‘ — ‡ „ … h ‚ x … ‘ “ ” ‡ ‘ x ‘ — ‡ † • d d “ ” ˜ y ‚ x ˜ ‚ • ƒ e – — ‡ ‘ x x h € ‘ ‡ „ ‚ x ƒ ‘ — ‡ ‘ x y x ‘ — ‡ „ ‘ • † { • ‚ ‡ † x y “ ‡ ’ “ ” ‘ x ‘ — ‡ y ‚ x ˜ ‚ • ƒ † x … ” ‘ ‡ ‚ g • ” ’ y ‚ x ˜ ‚ • ƒ ‡ v ‡ † … ‘ “ x ” h ‡ ˜ “ ” „ • ‘ ‘ — ‡ ” ‡ x • ’ ’ ‚ ‡ „ „ e E W ) Q S 1 P A E y † x ’ ‡ z ‡ „ † ‚ “ y ‘ “ x ” Š d • ˜ y ‘ • ‘ … „ A H A $ % ( H ) % % U H t ‹ 8 A B H A $ % ( ( H ) % % U H t ‹ A q A $ % ( S ( # ! $ ! 6 C ‹ A X A $ % ( Q ! # C ‹ 8 A u A $ % ( Œ % ( u ‹ 8 A B u A $ % ( ( Œ % ( u ‹ A q E A $ % ( S ) % ! $ U 6 q ‹ 8 A q I A $ % ( S ) % ! $ U ( 3 3 q ‹ ( ‰ ‡ ‘ … ‚ ” ‚ x ƒ „ … h ‚ x … ‘ “ ” ‡ † x ” ’ “ ‘ “ x ” • d d € – — ‡ y ‚ x ˜ ‚ • ƒ „ ‡ ~ … ‡ ” † ‡ “ „ ‘ ‚ • ” „ ‡ ‚ ‚ ‡ ’ ‚ x ƒ ‘ — ‡ „ … h ‚ x … ‘ “ ” ‡ ‘ x ‘ — ‡ † • d d “ ” ˜ y ‚ x ˜ ‚ • ƒ h • „ ‡ ’ x ” ‘ — ‡ „ y ‡ † “ “ ‡ ’ d • ˜ x ‘ — ‡ | y • „ ’ ‡ „ † ‚ “ h ‡ ’ h ‡ d x x e – — ‡ ‘ x x h € ‘ ‡ „ ‚ x ƒ ‘ — ‡ ‘ x y x ‘ — ‡ „ ‘ • † { • ‚ ‡ † x y “ ‡ ’ “ ” ‘ x ‘ — ‡ y ‚ x ˜ ‚ • ƒ † x … ” ‘ ‡ ‚ g • ” ’ y ‚ x ˜ ‚ • ƒ ‡ v ‡ † … ‘ “ x ” h ‡ ˜ “ ” „ • ‘ ‘ — ‡ ” ‡ x • ’ ’ ‚ ‡ „ „ e E W ) Q S 1 P A u q H V e ( j x • ’ y ‚ x ˜ ‚ • ƒ † x … ” ‘ ‡ ‚ x “ ‘ — i j † x ” ‘ ‡ ” ‘ „ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ i • ” ’ j • ‚ ‡ † x y “ ‡ ’ “ ” ‘ x ‘ — ‡ y ‚ x ˜ ‚ • ƒ † x … ” ‘ ‡ ‚ e – — ‡ † x ” ‘ ‡ ” ‘ „ x i • ‚ ‡ y d • † ‡ ’ • „ ‘ — ‡ — “ ˜ — n x ‚ ’ ‡ ‚ h € ‘ ‡ • ” ’ ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x j • „ ‘ — ‡ d x x n x ‚ ’ ‡ ‚ h € ‘ ‡ e s v • ƒ y d ‡ | w i j
- 10. A C i v ‰ ‡ „ ‘ • ‚ ‘ – — ‡ ‰ y – “ ” „ ‘ ‚ … † ‘ “ x ” “ „ ‡ ~ … “ l • d ‡ ” ‘ ‘ x • p n h € ‘ ‡ † • d d “ ” „ ‘ ‚ … † ‘ “ x ” ‘ x x ” ‡ x ‡ “ ˜ — ‘ ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” „ ’ ‡ y ‡ ” ’ “ ” ˜ … y x ” ‘ — ‡ ” … ƒ h ‡ ‚ e – — ‡ “ ” „ ‘ ‚ … † ‘ “ x ” „ • ‚ ‡ ˜ ‡ ” ‡ ‚ • d d € … „ ‡ ’ “ ” † x ” … … ” † ‘ “ x ” x “ ‘ — “ ” ‘ ‡ ‚ ‚ … y ‘ „ • ” ’ “ ” „ ‡ ‚ ‘ ‡ ’ … „ “ ” ˜ ‡ v ‘ ‡ ‚ ” • d — • ‚ ’ x • ‚ ‡ e i x x ‡ l ‡ ‚ ‘ — ‡ „ ‡ † • ” h ‡ … „ ‡ ’ • „ „ x ‘ x • ‚ ‡ “ ” „ ‘ ‚ … † ‘ “ x ” „ “ ” • y ‚ x ˜ ‚ • ƒ ‘ x ‘ ‚ • ” „ ‡ ‚ y ‚ x ˜ ‚ • ƒ ‡ v ‡ † … ‘ “ x ” ‘ x x ” ‡ x ‘ — ‡ ‡ “ ˜ — ‘ d x † • ‘ “ x ” „ e – — ‡ • ’ ’ ‚ ‡ „ „ ‡ „ • ‚ ‡ f ” „ ‘ ‚ … † ‘ “ x ” ‰ ‡ „ ‘ • ‚ ‘ € ’ ’ ‚ ‡ „ „ A C V A C 8 V A C a 8 V A C d 8 V A C c a V A C a V A C o d V A C v d V – — ‡ m m ‘ — • „ x … ‚ • ’ ’ “ ‘ “ x ” • d “ ” ‘ ‡ ‚ ‚ … y ‘ „ • ” ’ ‘ — ‡ „ ‡ “ ” ‘ ‡ ‚ ‚ … y ‘ „ ˜ ‡ ” ‡ ‚ • ‘ ‡ ‰ y – “ ” „ ‘ ‚ … † ‘ “ x ” „ “ ” ‘ ‡ ‚ ” • d d € • ” ’ ‘ — … „ ’ x ” x ‘ ‚ ‡ ~ … “ ‚ ‡ • ” € ‡ v ‘ ‡ ‚ ” • d — • ‚ ’ x • ‚ ‡ e – — ‡ „ ‡ “ ” „ ‘ ‚ … † ‘ “ x ” „ • ” ’ ‘ — ‡ “ ‚ ‰ ‡ „ ‘ • ‚ ‘ • ’ ’ ‚ ‡ „ „ ‡ „ • ‚ ‡ f ” ‘ ‡ ‚ ‚ … y ‘ ‰ ‡ „ ‘ • ‚ ‘ € ’ ’ ‚ ‡ „ „ A @ q a c V A C 7 a H V A C o 7 d c V A C v 7 d H V
- 11. I S ' ( 3 I S % ) 3 E W S 1 ) ) $ ! ( ( 2 F # $ % ' $ ! ( 9 # ' % ! S $ ! ( H X q A X w x ƒ y • ‚ ‡ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € x “ ‘ — • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ x y ‡ ‚ • ” ’ ˆ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € • ‚ ‡ k † x ƒ y • ‚ ‡ ’ x “ ‘ — ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e x ‘ — † x ” ‘ ‡ ” ‘ „ • ‚ ‡ y ‚ ‡ „ ‡ ‚ l ‡ ’ e – — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ † x ƒ y • ‚ “ „ x ” “ „ „ — x x ” h € „ ‡ ‘ ‘ “ ” ˜ ‘ — ‡ d • ˜ „ x ‘ — ‡ | y • „ x d d x x „ “ ˆ € ’ ˆ ‚ ‡ ˜ ‚ ƒ ‡ ƒ † • ‚ ‚ € d • ˜ “ „ „ ‡ ‘ “ ˆ € “ ˆ ‚ ‡ ˜ ‚ ƒ ‡ ƒ ” ‡ ‚ x d • ˜ “ „ „ ‡ ‘ “ ˆ € • ˆ ‚ ‡ ˜ ‚ ƒ ‡ ƒ † • ‚ ‚ € • ” ’ ” ‡ ‚ x d • ˜ „ • ‚ ‡ ‚ ‡ „ ‡ ‘ E W ) Q S 1 P H X q ` ( % H X q X H q F i 0 ! $ 3 ) $ ) w x ƒ y • ‚ ‡ “ ƒ ƒ ‡ ’ “ • ‘ ‡ x “ ‘ — • † † … ƒ … d • ‘ x ‚ – — ‡ „ ‡ † x ” ’ h € ‘ ‡ ˆ m n h “ ‘ ’ • ‘ • “ „ † x ƒ y • ‚ ‡ ’ x “ ‘ — ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e – — ‡ l • d … ‡ „ h ‡ “ ” ˜ † x ƒ y • ‚ ‡ ’ ‚ ‡ ƒ • “ ” … ” † — • ” ˜ ‡ ’ e – — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ † x ƒ y • ‚ “ „ x ” “ „ „ — x x ” h € „ ‡ ‘ ‘ “ ” ˜ ‘ — ‡ d • ˜ „ x ‘ — ‡ | y • „ x d d x x „ “ ˆ € ’ ’ • ‘ • † • ‚ ‚ € d • ˜ “ „ „ ‡ ‘ “ ˆ € “ ’ • ‘ • ” ‡ ‚ x d • ˜ “ „ „ ‡ ‘ “ ˆ € • ’ • ‘ • † • ‚ ‚ € • ” ’ ” ‡ ‚ x d • ˜ „ • ‚ ‡ ‚ ‡ „ ‡ ‘ E W ) Q S 1 P H q F – V @ B @ A X j x ˜ “ † • d € „ z ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € x “ ‘ — • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ‚ ‡ d x ˜ “ † • d d € € „ z ‡ ’ x “ ‘ — k ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ x y ‡ ‚ • ” ’ ˆ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € g • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ y d • † ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e f ‘ — ‡ x y ‡ ‚ • ” ’ “ „ • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” g “ ‘ „ • ’ ’ ‚ ‡ „ „ “ „ „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ e y g ‡ g | • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ x y ‡ ‚ • ‘ “ x ” e w ƒ “ „ ‚ ‡ „ ‡ ‘ e € w “ „ „ ‡ ‘ e E W ) Q S 1 P @ B @ ` ( % @ B @ X @ B F i 0 ! $ 3 ) $ ) j x ˜ “ † • d € „ z “ ƒ ƒ ‡ ’ “ • ‘ ‡ x “ ‘ — • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ‚ ‡ d x ˜ “ † • d d € € „ z ‡ ’ x “ ‘ — ‘ — ‡ m n h “ ‘ ’ • ‘ • ˆ x y ‡ ‚ • ” ’ • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ y d • † ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e y g ‡ g | • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ x y ‡ ‚ • ‘ “ x ” e w ƒ “ „ ‚ ‡ „ ‡ ‘ e € w “ „ „ ‡ ‘ e E W ) Q S 1 P @ B F o V h A @ A X s v † d … „ “ l ‡ ‰ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € x “ ‘ — • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ‚ ‡ s v † d … „ “ l ‡ ‰ ‡ ’ x “ ‘ — k ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ x y ‡ ‚ • ” ’ ˆ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € g • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ y d • † ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e f ‘ — ‡ x y ‡ ‚ • ” ’ “ „ • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” g “ ‘ „ • ’ ’ ‚ ‡ „ „ “ „ „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ e y g ‡ g | • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡
- 12. x y ‡ ‚ • ‘ “ x ” e w ƒ • ” ’ € w • ‚ ‡ ‚ ‡ „ ‡ ‘ e E W ) Q S 1 P h A @ ` ( % h A @ X h A F i 0 ! $ 3 ) $ ) s v † d … „ “ l ‡ ‰ “ ƒ ƒ ‡ ’ “ • ‘ ‡ x “ ‘ — • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ‚ ‡ s v † d … „ “ l ‡ ‰ ‡ ’ x “ ‘ — ‘ — ‡ m n h “ ‘ ’ • ‘ • ˆ x y ‡ ‚ • ” ’ • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ y d • † ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e y g ‡ g | • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ x y ‡ ‚ • ‘ “ x ” e w ƒ • ” ’ € w • ‚ ‡ ‚ ‡ „ ‡ ‘ e E W ) Q S 1 P h A F o V I A @ A X j x ˜ “ † • d ‰ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € x “ ‘ — • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ‚ ‡ d x ˜ “ † • d d € ‰ ‡ ’ x “ ‘ — k ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ x y ‡ ‚ • ” ’ ˆ ‚ ‡ ˜ “ „ ‘ ‡ ‚ x ‚ ƒ ‡ ƒ x ‚ € g • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ y d • † ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e f ‘ — ‡ x y ‡ ‚ • ” ’ “ „ • ƒ ‡ ƒ x ‚ € d x † • ‘ “ x ” g “ ‘ „ • ’ ’ ‚ ‡ „ „ “ „ „ y ‡ † “ “ ‡ ’ h € ‘ — ‡ † x ” ‘ ‡ ” ‘ „ x i j ‚ ‡ ˜ “ „ ‘ ‡ ‚ „ e y g ‡ g | • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ x y ‡ ‚ • ‘ “ x ” e w ƒ • ” ’ € w • ‚ ‡ ‚ ‡ „ ‡ ‘ e E W ) Q S 1 P I A @ ` ( % I A @ X I A F i 0 ! $ 3 ) $ ) j x ˜ “ † • d ‰ “ ƒ ƒ ‡ ’ “ • ‘ ‡ x “ ‘ — • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ‚ ‡ d x ˜ “ † • d d € ‰ ‡ ’ x “ ‘ — ‘ — ‡ m n h “ ‘ ’ • ‘ • ˆ x y ‡ ‚ • ” ’ • ” ’ ‘ — ‡ ‚ ‡ „ … d ‘ “ „ y d • † ‡ ’ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ e y g ‡ g | • ‚ ‡ ƒ x ’ “ “ ‡ ’ ‘ x ‚ ‡ d ‡ † ‘ ‘ — ‡ ‚ ‡ „ … d ‘ x ‘ — ‡ x y ‡ ‚ • ‘ “ x ” e w ƒ • ” ’ € w • ‚ ‡ ‚ ‡ „ ‡ ‘ e E W ) Q S 1 P I A F o V A e H ( ‰ x ‘ • ‘ ‡ • † † … ƒ … d • ‘ x ‚ d ‡ ‘ s • † — h “ ” • ‚ € h “ ‘ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ “ „ ‚ x ‘ • ‘ ‡ ’ d ‡ ‘ h € x ” ‡ y x „ “ ‘ “ x ” e “ ‘ z — “ „ y d • † ‡ ’ “ ” ‘ — ‡ y x „ “ ‘ “ x ” x z • „ x ‡ d d • „ “ ” ‘ — ‡ w • ‚ ‚ € d • ˜ e w ƒ “ „ ƒ x ’ “ “ ‡ ’ • † † x ‚ ’ “ ” ˜ ‘ x h “ ‘ z — e y g ‡ g | g € w • ‚ ‡ ” x ‘ • ‡ † ‘ ‡ ’ e E W ) Q S 1 P A e H A A H ( ‰ x ‘ • ‘ ‡ • † † … ƒ … d • ‘ x ‚ ‚ “ ˜ — ‘ s • † — h “ ” • ‚ € h “ ‘ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ “ „ ‚ x ‘ • ‘ ‡ ’ ‚ “ ˜ — ‘ h € x ” ‡ y x „ “ ‘ “ x ” e “ ‘ z “ „ y d • † ‡ ’ “ ” ‘ — ‡ y x „ “ ‘ “ x ” x z — • „ x ‡ d d • „ “ ” ‘ — ‡ w • ‚ ‚ € d • ˜ e w ƒ “ „ ƒ x ’ “ “ ‡ ’ • † † x ‚ ’ “ ” ˜ ‘ x h “ ‘ z e y g ‡ g | g € w • ‚ ‡ ” x ‘ • ‡ † ‘ ‡ ’ e E W ) Q S 1 P A A H A @ e ( ‰ x ‘ • ‘ ‡ • † † … ƒ … d • ‘ x ‚ d ‡ ‘ ‘ — ‚ x … ˜ — † • ‚ ‚ € s • † — h “ ” • ‚ € h “ ‘ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ “ „ ‚ x ‘ • ‘ ‡ ’ d ‡ ‘ h € x ” ‡ y x „ “ ‘ “ x ” ‘ — ‚ x … ˜ — ‘ — ‡ w • ‚ ‚ € d • ˜ e “ ‘ z — “ „ y d • † ‡ ’ “ ” ‘ — ‡ w • ‚ ‚ € d • ˜ g • ” ’ ‘ — ‡ w • ‚ ‚ € d • ˜ “ „ y d • † ‡ ’ “ ” ‘ — ‡ d ‡ • „ ‘ „ “ ˜ ” “ “ † • ” ‘ y x „ “ ‘ “ x ” z e w ƒ “ „ ƒ x ’ “ “ ‡ ’ • † † x ‚ ’ “ ” ˜ ‘ x h “ ‘ z — e y g ‡ g | g € w • ‚ ‡ ” x ‘ • ‡ † ‘ ‡ ’ e E W ) Q S 1 P A @ e A @ A ( ‰ x ‘ • ‘ ‡ • † † … ƒ … d • ‘ x ‚ ‚ “ ˜ — ‘ s • † — h “ ” • ‚ € h “ ‘ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ “ „ ‚ x ‘ • ‘ ‡ ’ ‚ “ ˜ — ‘ h € x ” ‡ y x „ “ ‘ “ x ” ‘ — ‚ x … ˜ — ‘ — ‡ w • ‚ ‚ € d • ˜ e “ ‘ z “ „ y d • † ‡ ’ “ ” ‘ — ‡
- 13. ‘ — ‚ x … ˜ — † • ‚ ‚ € w • ‚ ‚ € d • ˜ g • ” ’ ‘ — ‡ w • ‚ ‚ € d • ˜ “ „ y d • † ‡ ’ “ ” ‘ — ‡ ƒ x „ ‘ „ “ ˜ ” “ “ † • ” ‘ y x „ “ ‘ “ x ” z — e w ƒ “ „ ƒ x ’ “ “ ‡ ’ • † † x ‚ ’ “ ” ˜ ‘ x h “ ‘ z e y g ‡ g | g € w • ‚ ‡ ” x ‘ • ‡ † ‘ ‡ ’ e E W ) Q S 1 P A @ A H X @ ( w x ƒ y d ‡ ƒ ‡ ” ‘ • † † … ƒ … d • ‘ x ‚ – — ‡ † x ” ‘ ‡ ” ‘ „ x ‘ — ‡ • † † … ƒ … d • ‘ x ‚ • ‚ ‡ † x ƒ y d ‡ ƒ ‡ ” ‘ ‡ ’ e „ x d • ˜ „ • ‚ ‡ • ‡ † ‘ ‡ ’ e E W ) Q S 1 P H X @ H X H ( w x ƒ y d ‡ ƒ ‡ ” ‘ † • ‚ ‚ € – — ‡ w • ‚ ‚ € d • ˜ “ „ † x ƒ y d ‡ ƒ ‡ ” ‘ ‡ ’ e „ x x ‘ — ‡ ‚ d • ˜ „ • ‚ ‡ • ‡ † ‘ ‡ ’ e E W ) Q S 1 P H X H C H ( y ‡ ‘ w • ‚ ‚ € y ‡ ‘ w • ‚ ‚ € E W ) Q S 1 P C H I S ' ( 3 I S % ) 3 E W S 1 ) ) $ ! ( ( 2 F # $ % ' $ ! ( 9 # ' % ! S $ ! ( B I q ( „ x x y ‡ ‚ • ‘ “ x ” „ x x y ‡ ‚ • ‘ “ x ” “ „ y ‡ ‚ x ‚ ƒ ‡ ’ e – — ‡ “ ” „ ‘ ‚ … † ‘ “ x ” “ „ ‡ ‘ † — ‡ ’ • ” ’ ’ ‡ † x ’ ‡ ’ e i x x ‡ l ‡ ‚ ” x x y ‡ ‚ • ‘ “ x ” “ „ ‡ v ‡ † … ‘ ‡ ’ e E W ) Q S 1 P B I q V e ( i • d ‘ • ” ’ ‡ ” ‘ ‡ ‚ x • “ ‘ „ ‘ • ‘ ‡ – — ‡ w | Ž “ ” “ „ — ‡ „ ‡ v ‡ † … ‘ “ ” ˜ ‘ — ‡ † … ‚ ‚ ‡ ” ‘ “ ” „ ‘ ‚ … † ‘ “ x ” • ” ’ — • d ‘ „ • ” € … ‚ ‘ — ‡ ‚ ‡ v ‡ † … ‘ “ x ” e € ” “ ” ‘ ‡ ‚ ‚ … y ‘ x ‚ ‚ ‡ „ ‡ ‘ “ „ ” ‡ † ‡ „ „ • ‚ € ‘ x ‡ v “ ‘ ‚ x ƒ ‘ — ‡ — • d ‘ „ ‘ • ‘ ‡ e E W ) Q S 1 P V e 9 F ( z “ „ • h d ‡ “ ” ‘ ‡ ‚ ‚ … y ‘ „ – — ‡ “ ” ‘ ‡ ‚ ‚ … y ‘ ‡ ” • h d ‡ d “ y n d x y “ „ ‚ ‡ „ ‡ ‘ • ” ’ • d d ‘ — ‡ “ ” ‘ ‡ ‚ ‚ … y ‘ „ ‡ v † ‡ y ‘ ‘ — ‡ – ‰ € | • ‚ ‡ ’ “ „ • h d ‡ ’ e „ x d • ˜ „ • ‚ ‡ • ‡ † ‘ ‡ ’ e E W ) Q S 1 P 9 F E F ( s ” • h d ‡ “ ” ‘ ‡ ‚ ‚ … y ‘ „ – — ‡ “ ” ‘ ‡ ‚ ‚ … y ‘ ‡ ” • h d ‡ d “ y n d x y “ „ „ ‡ ‘ • ” ’ • d d “ ” ‘ ‡ ‚ ‚ … y ‘ „ • ‚ ‡ ‡ ” • h d ‡ ’ e „ x d • ˜ „ • ‚ ‡ • ‡ † ‘ ‡ ’ e € ‘ ‡ ‚ • „ € „ ‘ ‡ ƒ ‚ ‡ „ ‡ ‘ x ‚ ‘ — ‡ • † { ” x x d ‡ ’ ˜ ‡ ƒ ‡ ” ‘ x • ” “ ” ‘ ‡ ‚ ‚ … y ‘ g ‘ — ‡ “ ” ‘ ‡ ‚ ‚ … y ‘ ‡ ” • h d ‡ d “ y d x y “ „ ‚ ‡ „ ‡ ‘ g ‘ — … „ ’ “ „ • h d “ ” ˜ ‘ — ‡ “ ” ‘ ‡ ‚ ‚ … y ‘ „ e – — “ „ “ ” „ ‘ ‚ … † ‘ “ x ” “ „ ” ‡ † ‡ „ „ • ‚ € ‘ x ‚ ‡ ‡ ” • h d ‡ ‘ — ‡ “ ” ‘ ‡ ‚ ‚ … y ‘ „ ˆ ‡ v † ‡ y ‘ – ‰ € | e E W ) Q S 1 P E F
- 14. A F X ( ‰ ‡ • ’ “ ” ‘ ‡ ‚ ‚ … y ‘ ƒ • „ – — “ „ “ „ • ƒ … d ‘ “ y … ‚ y x „ ‡ “ ” „ ‘ ‚ … † ‘ “ x ” … „ ‡ ’ ‘ x ‚ ‡ • ’ ‘ — ‡ „ ‘ • ‘ … „ x “ ” ‘ ‡ ‚ ‚ … y ‘ „ — e ‘ g q e ‘ g ‘ e ‘ • ” ’ ‚ ‡ • ’ „ ‡ ‚ “ • d ’ • ‘ • “ ” y … ‘ h “ ‘ e – — ‡ “ ” „ ‘ ‚ … † ‘ “ x ” d x • ’ „ ‡ “ ˜ — ‘ h “ ‘ „ “ ” ‘ — ‡ • † † … ƒ … d • ‘ x ‚ x “ ‘ — ‘ — ‡ x d d x x “ ” ˜ “ ” ‘ ‡ ‚ y ‚ ‡ ‘ • ‘ “ x ” „ e E W ) Q S 1 P A F X C F X ( y ‡ ‘ “ ” ‘ ‡ ‚ ‚ … y ‘ ƒ • „ { – — “ „ “ „ • ƒ … d ‘ “ y … ‚ y x „ ‡ “ ” „ ‘ ‚ … † ‘ “ x ” • ” ’ … „ ‡ ’ ‘ x “ ƒ y d ‡ ƒ ‡ ” ‘ ‘ — ‡ m m ‘ “ ” ‘ ‡ ‚ ‚ … y ‘ „ — e ‘ g q e ‘ g ‘ e ‘ g • ” ’ „ ‡ ‚ “ • d ’ • ‘ • x … ‘ y … ‘ e – — ‡ “ ” „ ‘ ‚ … † ‘ “ x ” “ ” ‘ ‡ ‚ y ‚ ‡ ‘ „ ‘ — ‡ • † † … ƒ … d • ‘ x ‚ † x ” ‘ ‡ ” ‘ „ • „ x d d x x „ e E W ) Q S 1 P C F X
- 15. ˜ ™ š › œ ž Ÿ ž ¡ ¢ £ ž Ÿ ž ¡ ¢ œ › ™ ¤ ¥ š ¦ ™ œ § ¤ ¨ š § © ª š © ¤ « œ ¤ ¬ ™ œ ¨ ¤ ¤ › š ¨ ® ¯ ° ° œ › ¤ ¬ ¤ ± ¯ œ › œ § ¤ § © ¨ œ ™ ² ³ ¤ ¦ š ª ¤ ¤ ª § ± ¤ ° › š § ± ¤ § © ¨ œ ™ « ´ ª › š ¥ š ¦ ™ œ § ¤ ¦ š § § ¯ › ª § ± ¤ ° › š § ± ± œ ° ¤ ¦ › ¤ § © ¨ œ ™ « µ ¯ ¬ ¤ › ° š § ¨ š › ¤ ¤ § © ¨ œ ™ œ § › ¯ œ › ¨ ¤ ¶ ¤ ¨ › ¯ ¥ š ® ¤ š ¥ š ¦ ™ œ § ¤ › ¯ ª § ± ¤ ° › š § ± « · ¯ ° ¤ ¸ š ¥ ¹ ¨ ¤ ¬ › ™ ¤ ° ¤ œ š › ° š § ¨ š › ¯ ° œ § œ ± ¤ š ¨ ¨ ¦ ¯ ¥ ¹ ª › ¤ ° ™ œ ¦ ™ › ° š § ¨ š › ¤ ¯ ª ° ¤ § © ¨ œ ™ œ § › ¯ ´ œ § š ° º ¨ š § © ª š © ¤ » ¯ ° š ¦ ¯ ¥ ¹ ª › ¤ ° › ¯ ª § ± ¤ ° › š § ± š § ± ¹ ¤ ° » ¯ ° ¥ › ™ ¤ ° ¤ ¼ ª œ ° ¤ ± ¯ ¹ ¤ ° š › œ ¯ § « µ œ ¥ œ ¨ š ° ¨ º ¬ š ¥ š ¦ ™ œ § ¤ ¨ š § © ª š © ¤ ™ œ ¦ ™ š ½ œ ¦ ° ¯ ¹ ° ¯ ¦ ¤ ¯ ° ¦ š § ª § ± ¤ ° › š § ± œ › ™ ¤ ¾ ¢ ¿ À ¨ š § © ª š © ¤ « Á ™ ¤ ¤ ™ ¤ ¸ ¦ ¯ ± ¤ š ° ¤ ¦ š ¨ ¨ ¤ ± ž Ÿ ž ¡ ¢ µ ™ œ ¦ ™ ¥ š ® ¤ š ¥ œ ¦ ° ¯ ¹ ° ¯ ¦ ¤ ¯ ° › ¯ ¯ ° ® « À › ™ ¤ ° ¤ œ § ¯ › ° š § ¨ š › ¯ ° œ § œ ± ¤ š ½ œ ¦ ° ¯ ¹ ° ¯ ¦ ¤ ¯ ° ¬ ¤ ± œ ° ¤ ¦ › ¨ º » § ± › ™ ¤ ž Ÿ ž ¡ ¢ µ » ¯ ° ¤ š ¦ ™ š § ± ¤ ¶ ¤ ° º œ § › ° ª ¦ › œ ¯ § š § ± ¤ » ¤ ¤ ± œ › š ¨ ¯ § ¤ œ § œ ± ¤ š › ° š œ § ¤ ° ® œ › « Á ™ ¯ ¤ ¯ ¹ ¦ ¯ ± ¤ œ › ™ œ › ± ¤ ¦ ° œ ¹ › œ ¯ § š ° ¤ © œ ¶ ¤ § ³ ¤ ¨ ¯ « Á ™ ¤ ž Ÿ ž ¡ ¢ ™ ¤ ¤ › œ › ™ ¯ ª › ± ¤ ¦ ° œ ¹ › œ ¯ § œ š ¨ ¯ © œ ¶ ¤ § œ § › ™ ¤ ¥ š œ § ¹ š © ¤ «
