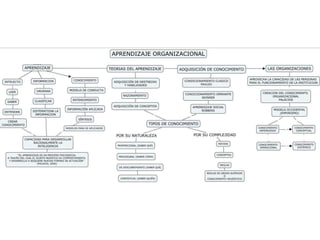
Aprendizaje oranizacional
•Descargar como PPTX, PDF•
0 recomendaciones•127 vistas
MAPA DE APRENDIZAJE ORGANIZACIONAL
Denunciar
Compartir
Denunciar
Compartir
Recomendados
Recomendados
Más contenido relacionado
Destacado
Destacado (12)
Pso based optimized security scheme for image authentication and tamper proofing

Pso based optimized security scheme for image authentication and tamper proofing
Secure & fault tolerance handoff in vanet using special mobile agent

Secure & fault tolerance handoff in vanet using special mobile agent
Sar ice image classification using parallelepiped classifier based on gram sc...

Sar ice image classification using parallelepiped classifier based on gram sc...
Review of access control models for cloud computing

Review of access control models for cloud computing
Último
Último (20)
TIPOLOGÍA TEXTUAL- EXPOSICIÓN Y ARGUMENTACIÓN.pptx

TIPOLOGÍA TEXTUAL- EXPOSICIÓN Y ARGUMENTACIÓN.pptx
SELECCIÓN DE LA MUESTRA Y MUESTREO EN INVESTIGACIÓN CUALITATIVA.pdf

SELECCIÓN DE LA MUESTRA Y MUESTREO EN INVESTIGACIÓN CUALITATIVA.pdf
Tema 8.- PROTECCION DE LOS SISTEMAS DE INFORMACIÓN.pdf

Tema 8.- PROTECCION DE LOS SISTEMAS DE INFORMACIÓN.pdf
Criterios ESG: fundamentos, aplicaciones y beneficios

Criterios ESG: fundamentos, aplicaciones y beneficios
2 REGLAMENTO RM 0912-2024 DE MODALIDADES DE GRADUACIÓN_.pptx

2 REGLAMENTO RM 0912-2024 DE MODALIDADES DE GRADUACIÓN_.pptx
PIAR v 015. 2024 Plan Individual de ajustes razonables

PIAR v 015. 2024 Plan Individual de ajustes razonables
BIOMETANO SÍ, PERO NO ASÍ. LA NUEVA BURBUJA ENERGÉTICA

BIOMETANO SÍ, PERO NO ASÍ. LA NUEVA BURBUJA ENERGÉTICA
LABERINTOS DE DISCIPLINAS DEL PENTATLÓN OLÍMPICO MODERNO. Por JAVIER SOLIS NO...

LABERINTOS DE DISCIPLINAS DEL PENTATLÓN OLÍMPICO MODERNO. Por JAVIER SOLIS NO...
ACERTIJO DE LA BANDERA OLÍMPICA CON ECUACIONES DE LA CIRCUNFERENCIA. Por JAVI...

ACERTIJO DE LA BANDERA OLÍMPICA CON ECUACIONES DE LA CIRCUNFERENCIA. Por JAVI...
Curso = Metodos Tecnicas y Modelos de Enseñanza.pdf

Curso = Metodos Tecnicas y Modelos de Enseñanza.pdf
