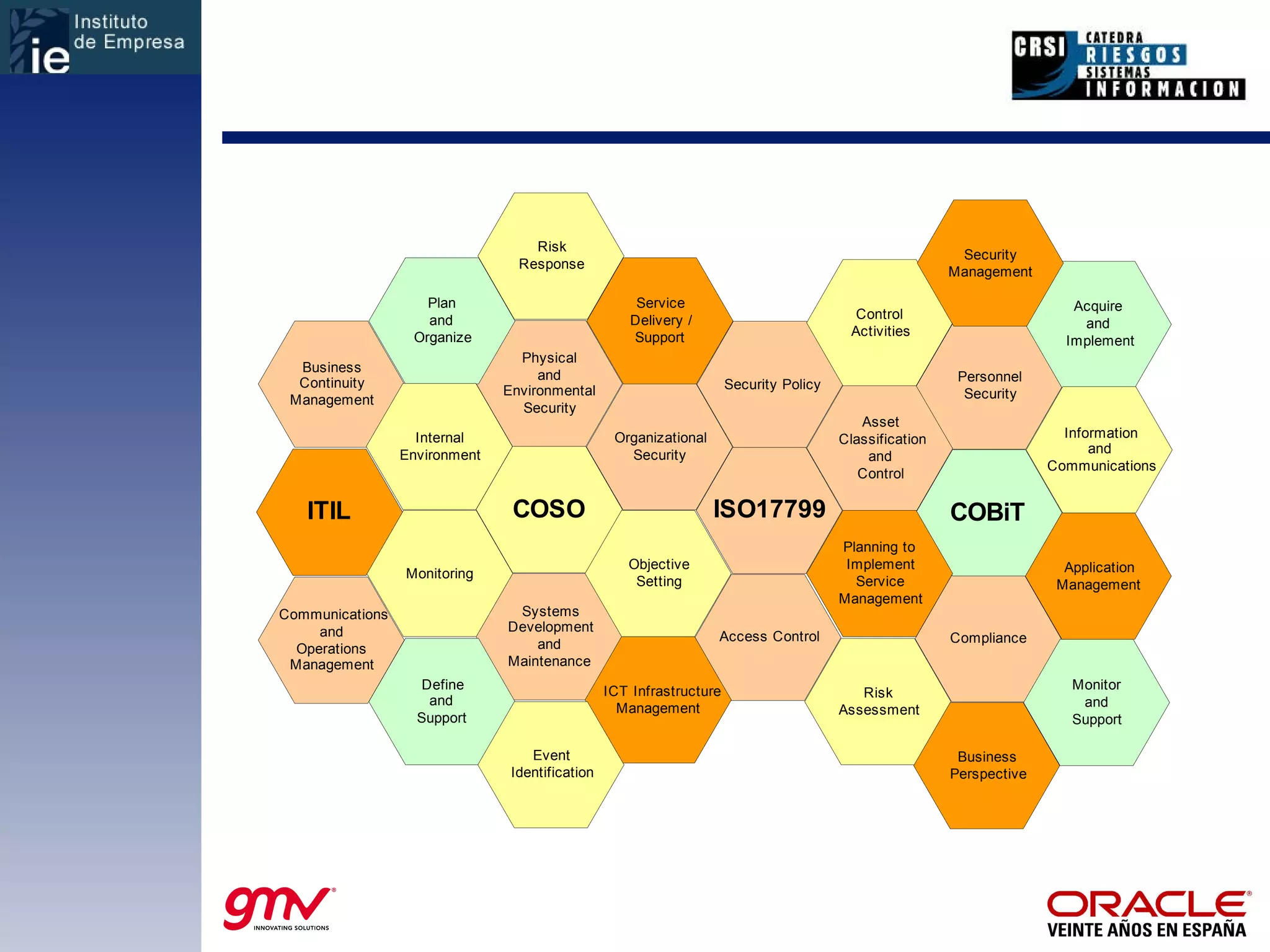
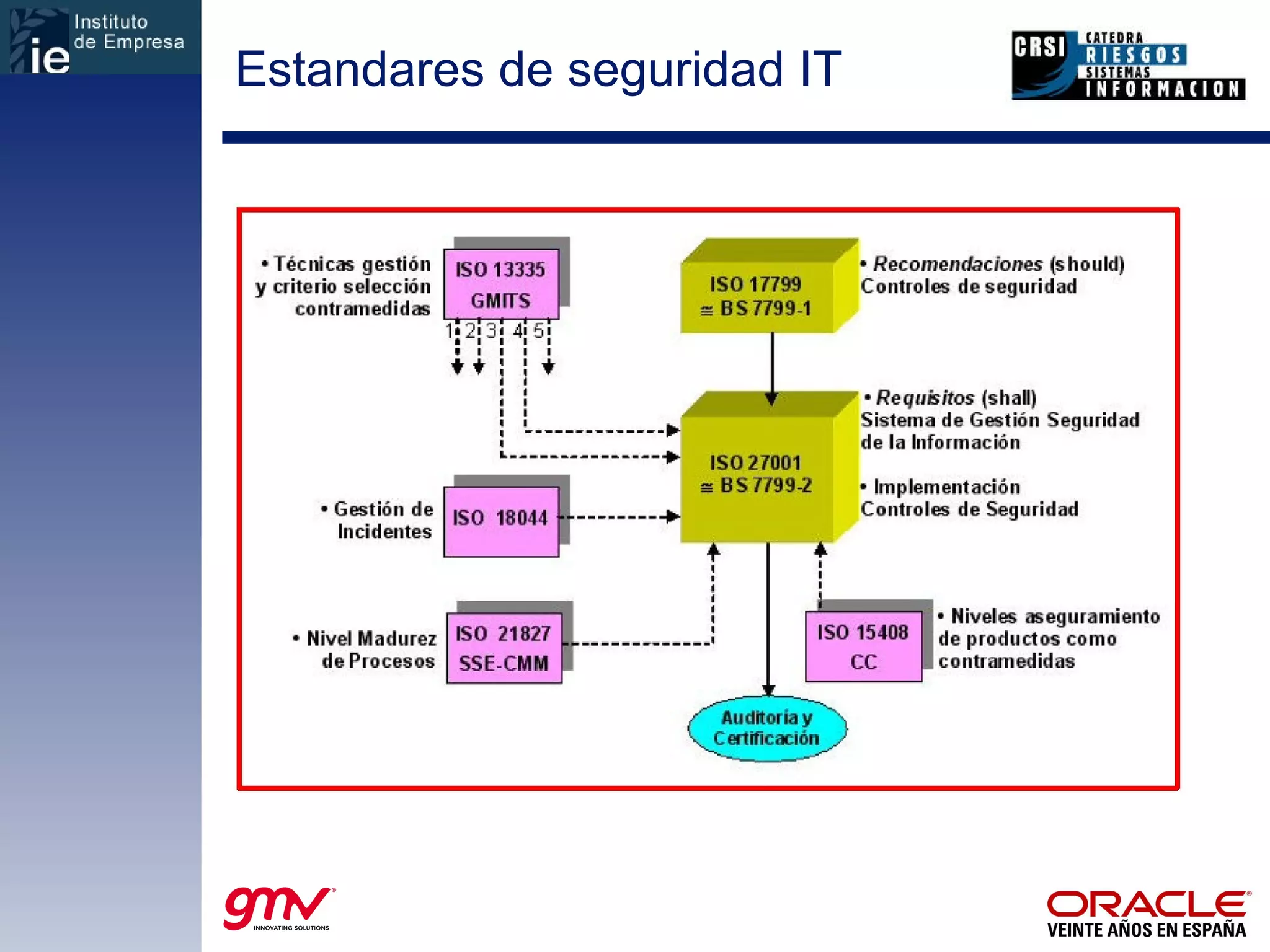
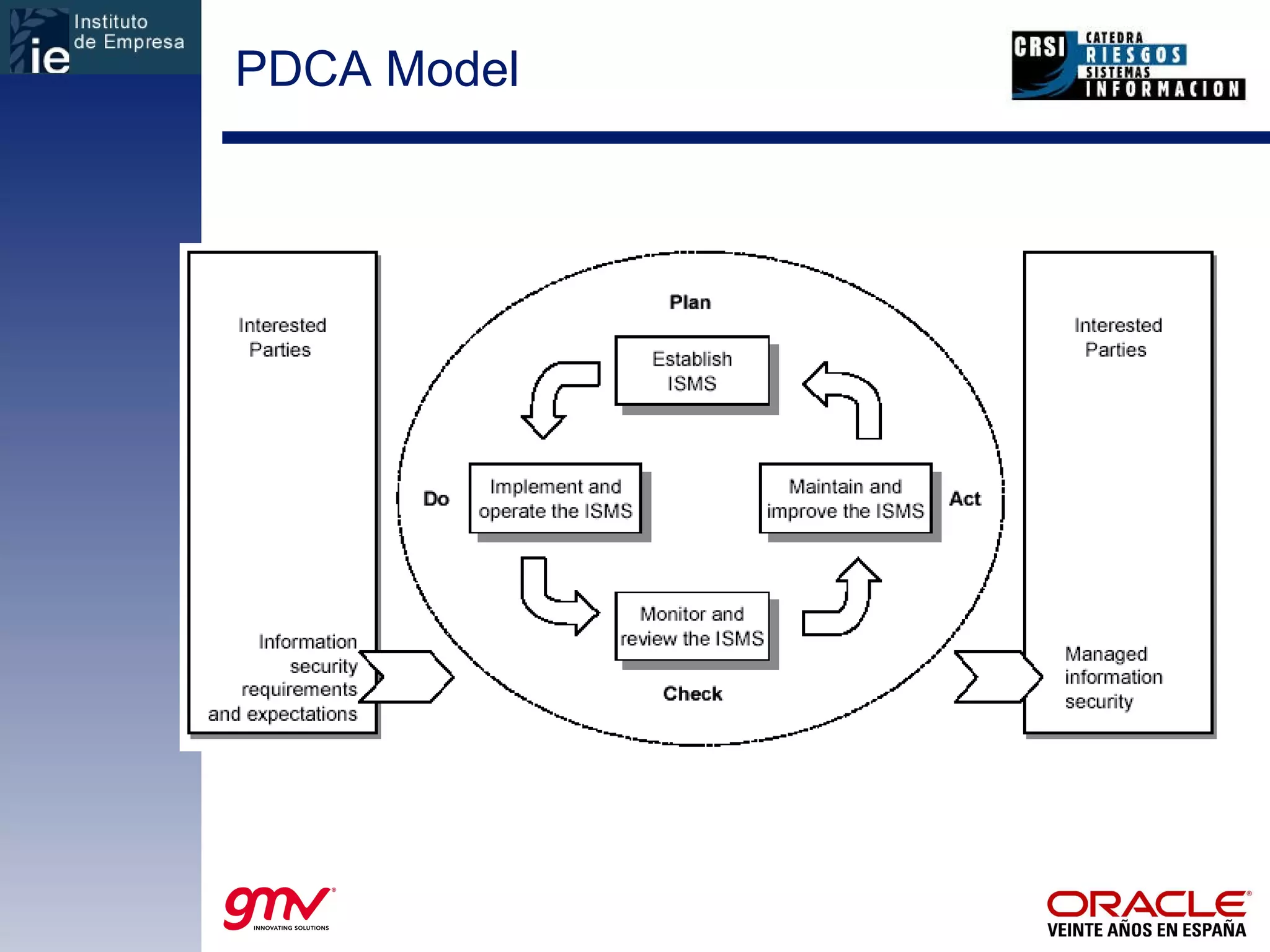
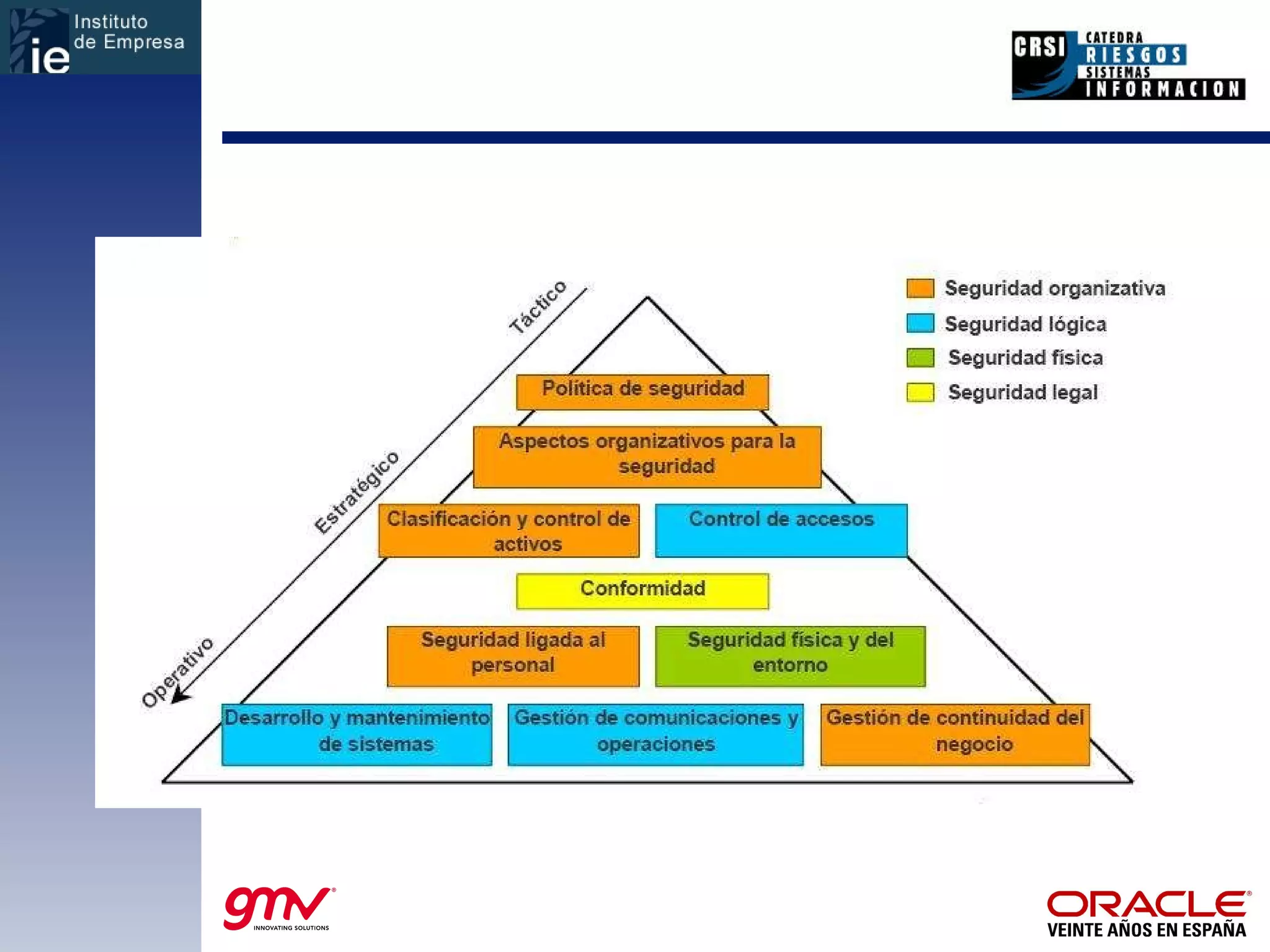
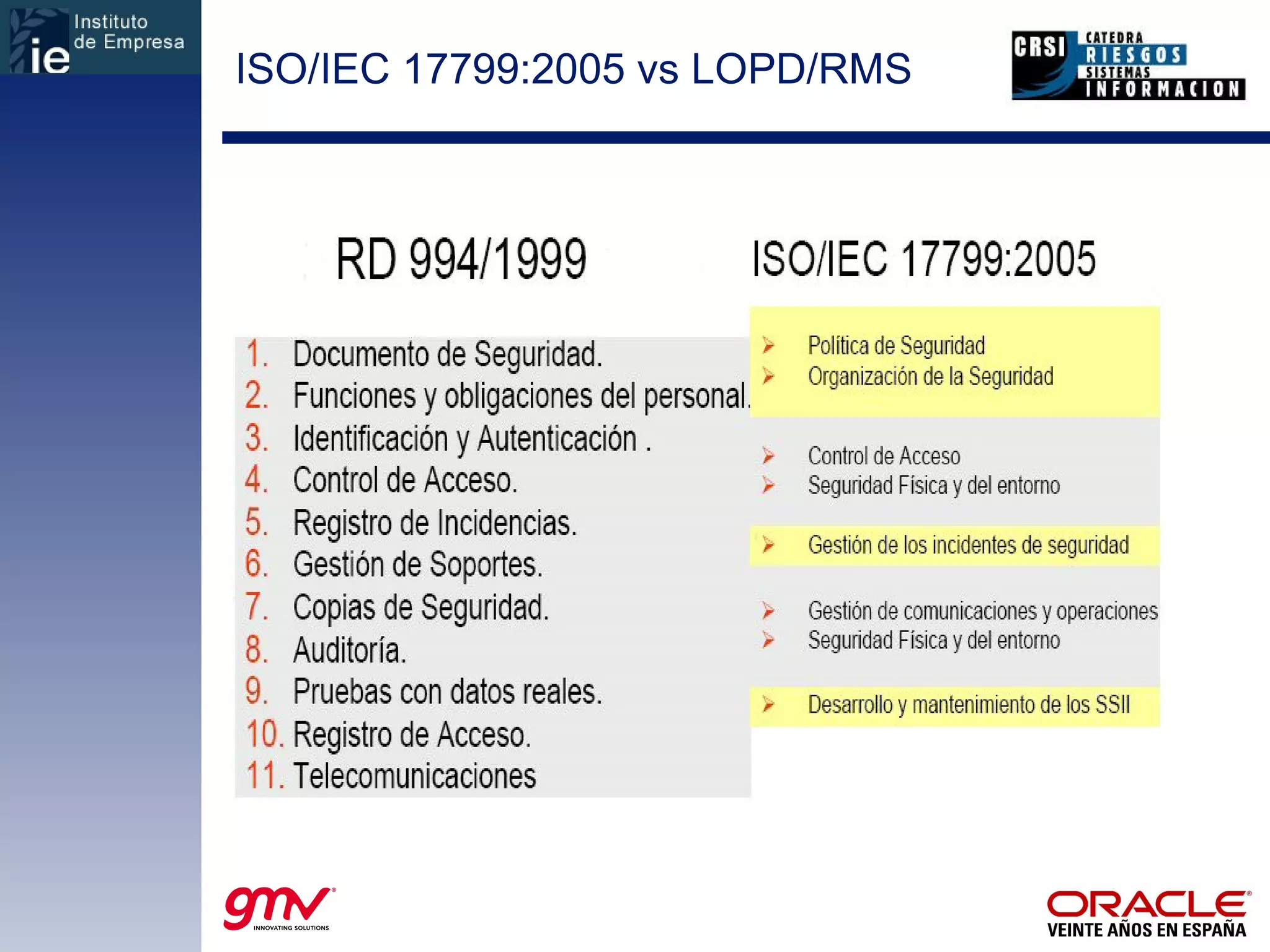
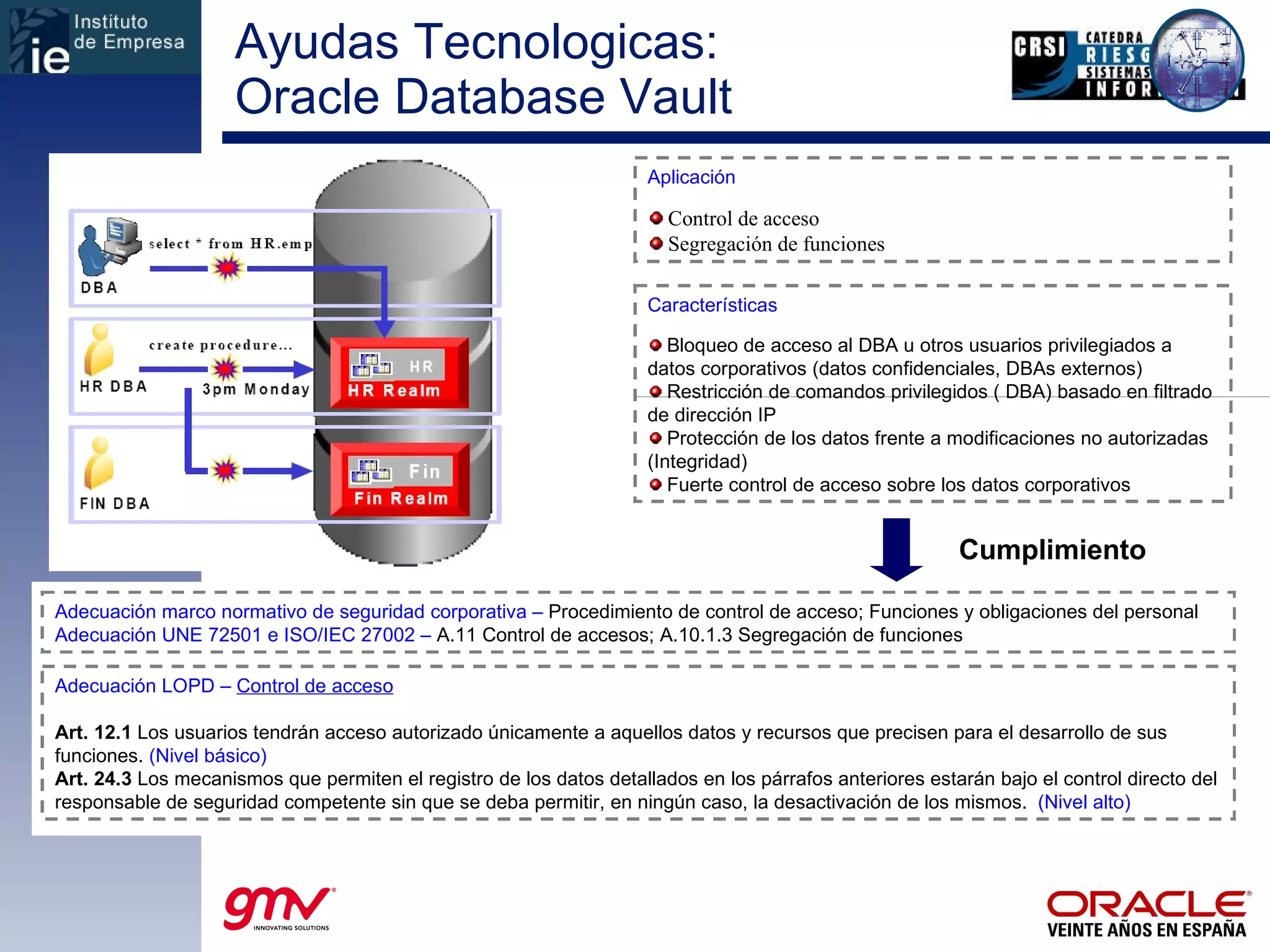
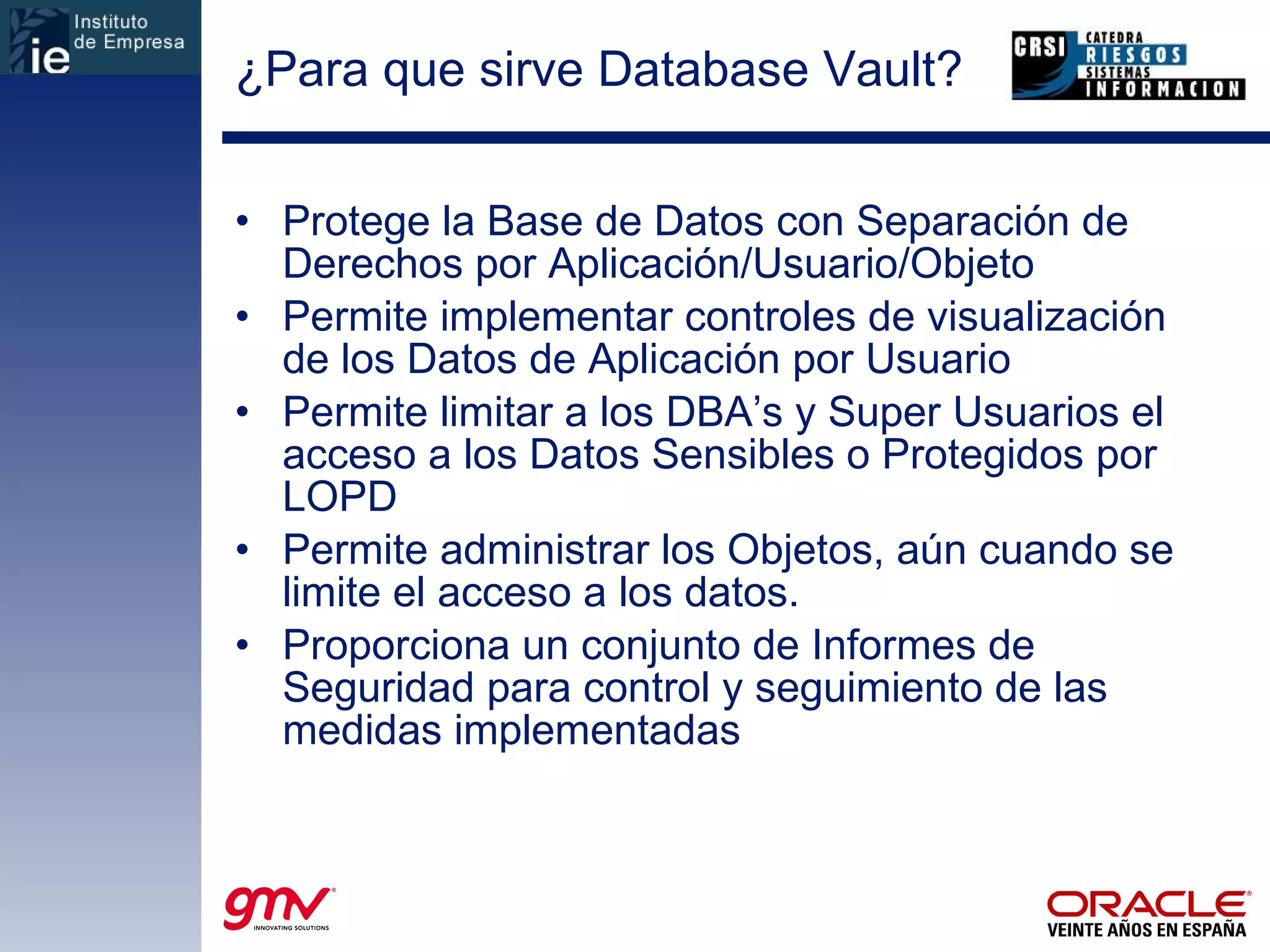
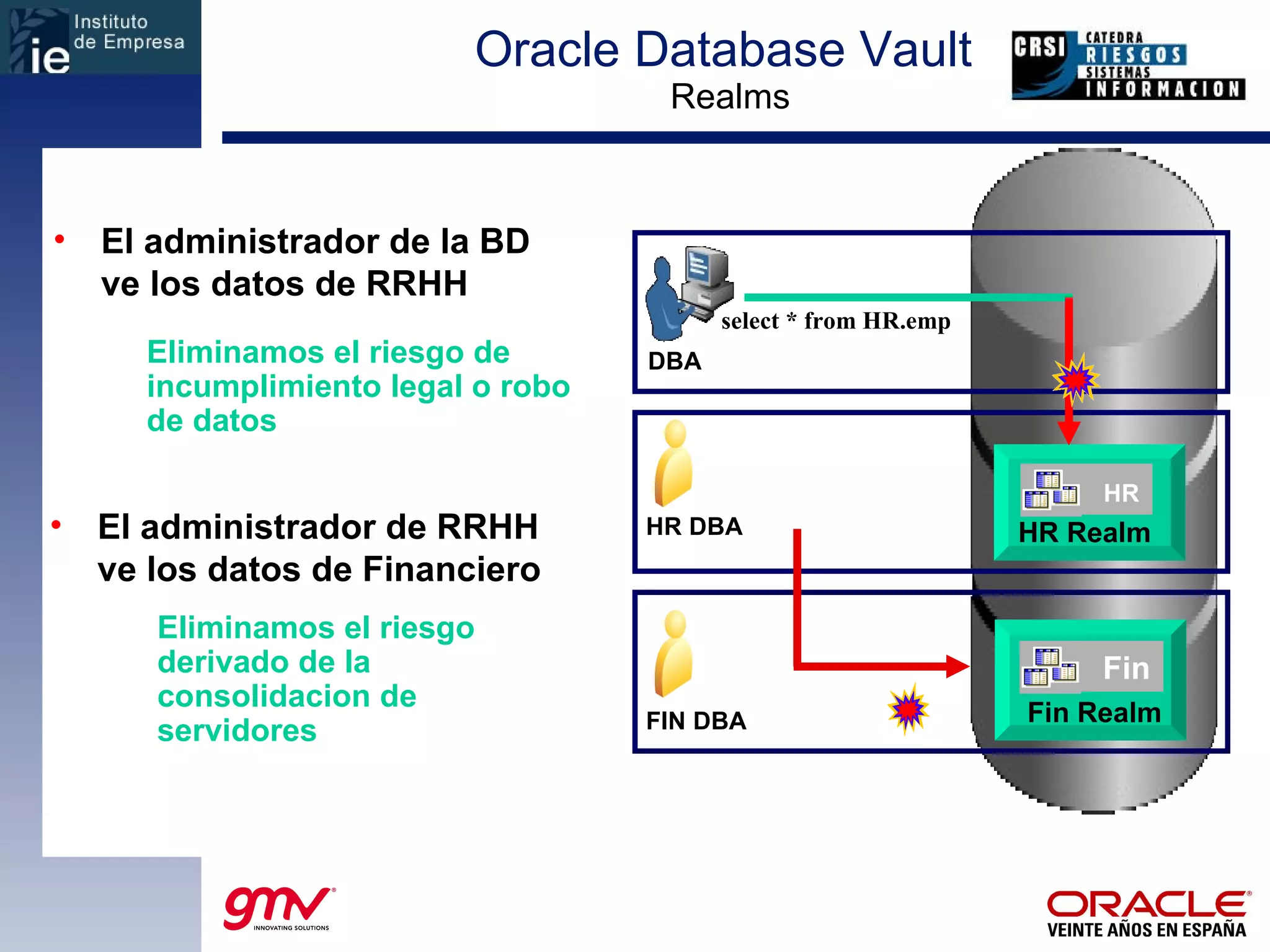
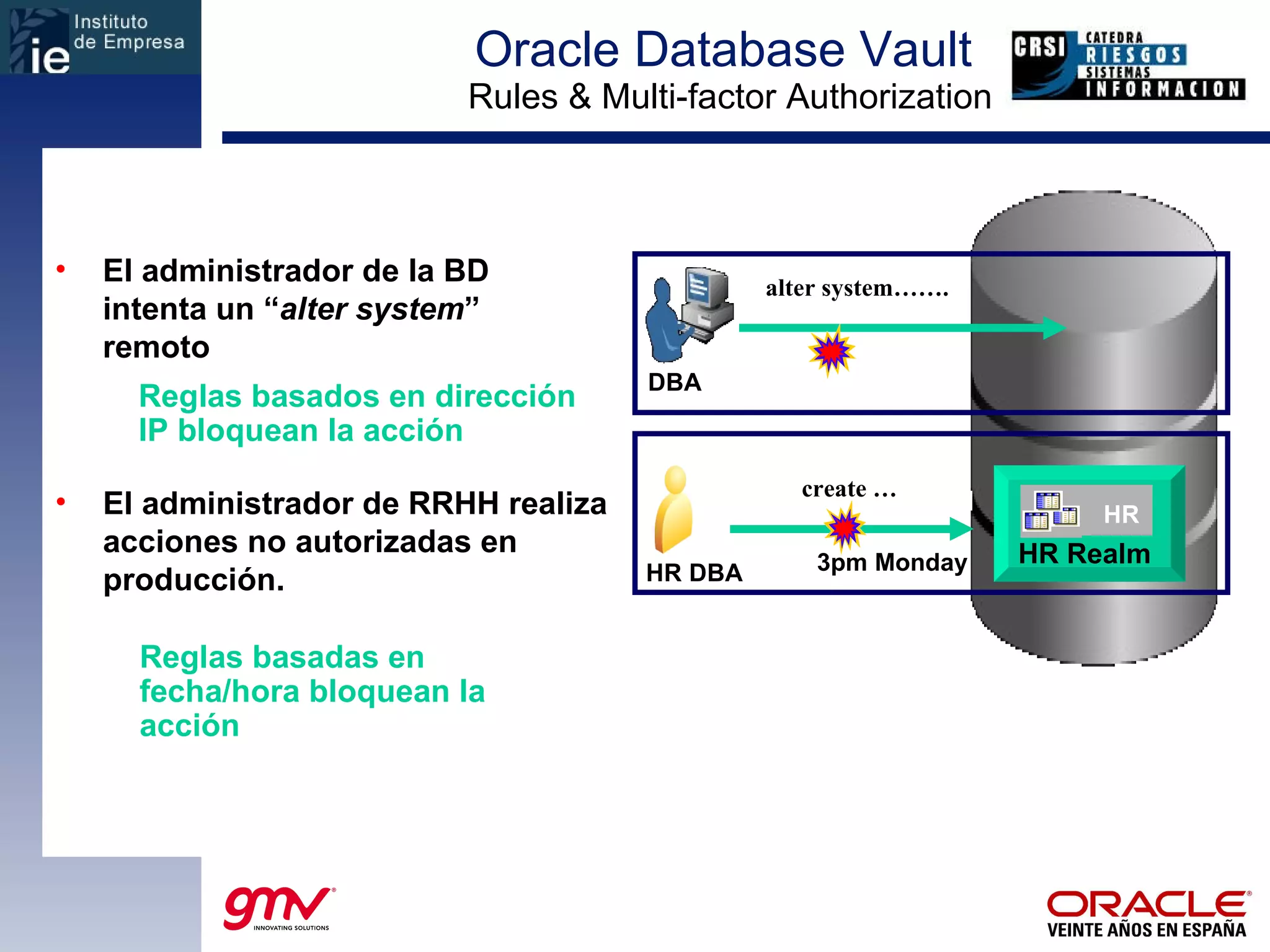
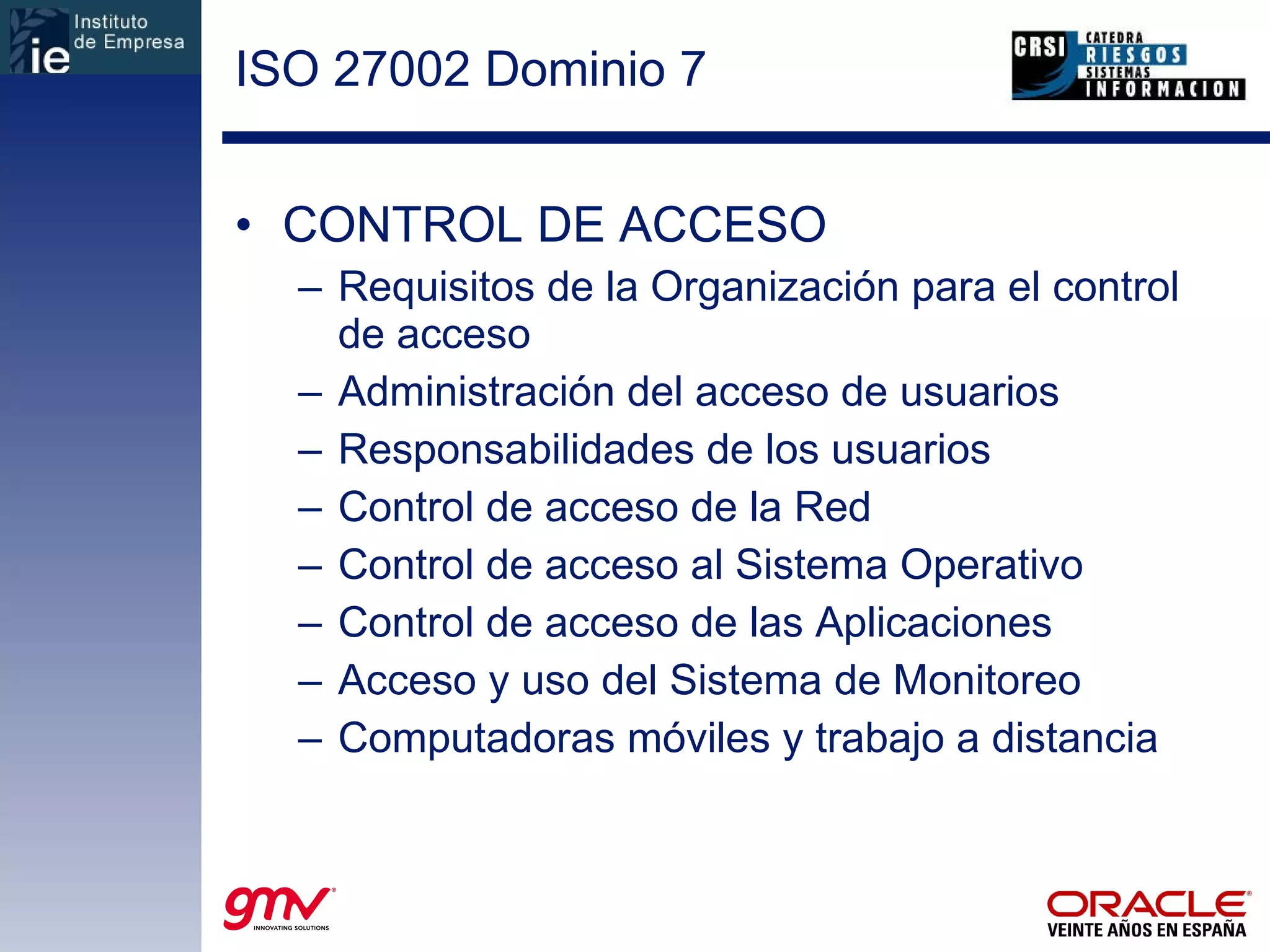
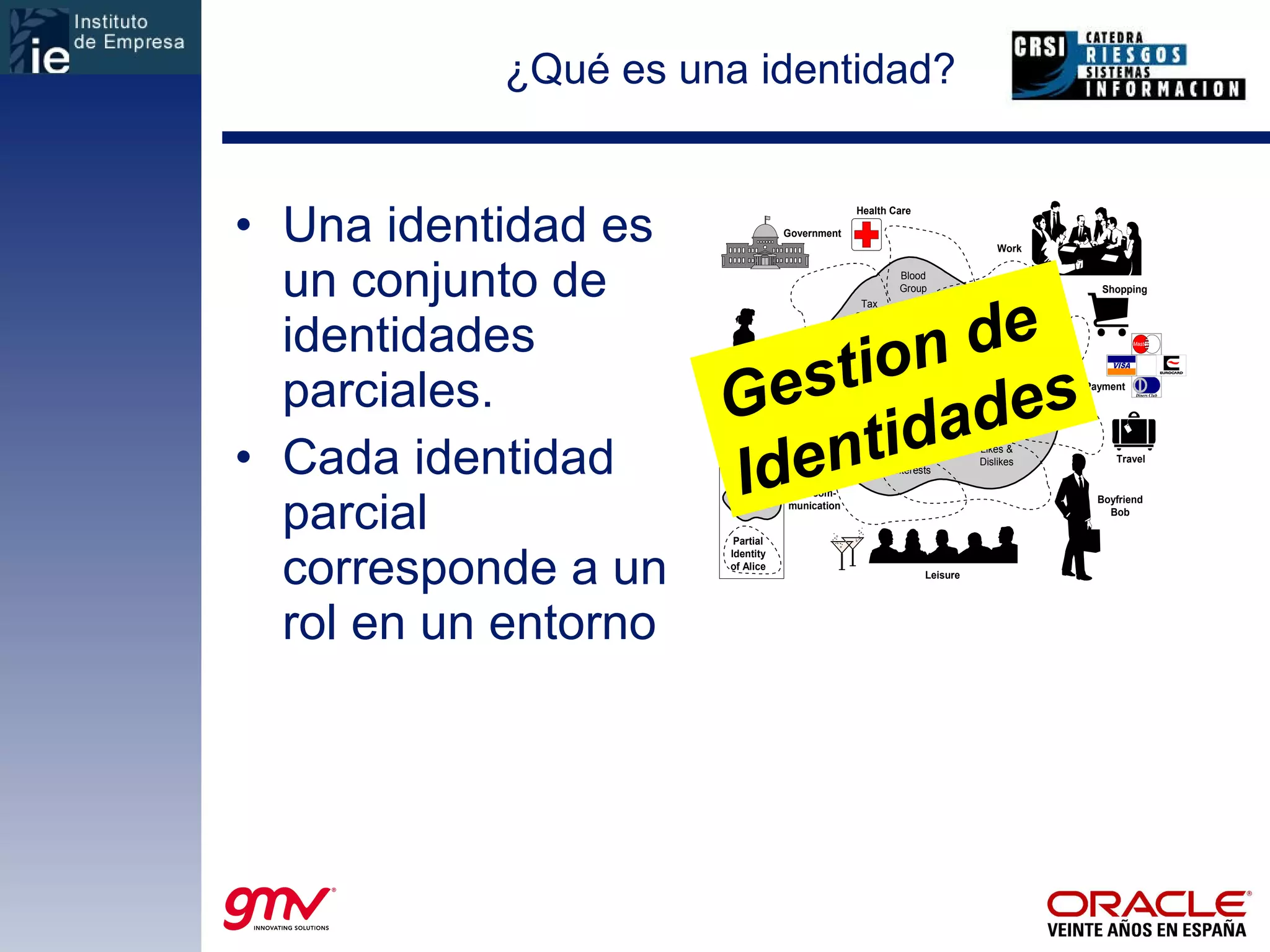
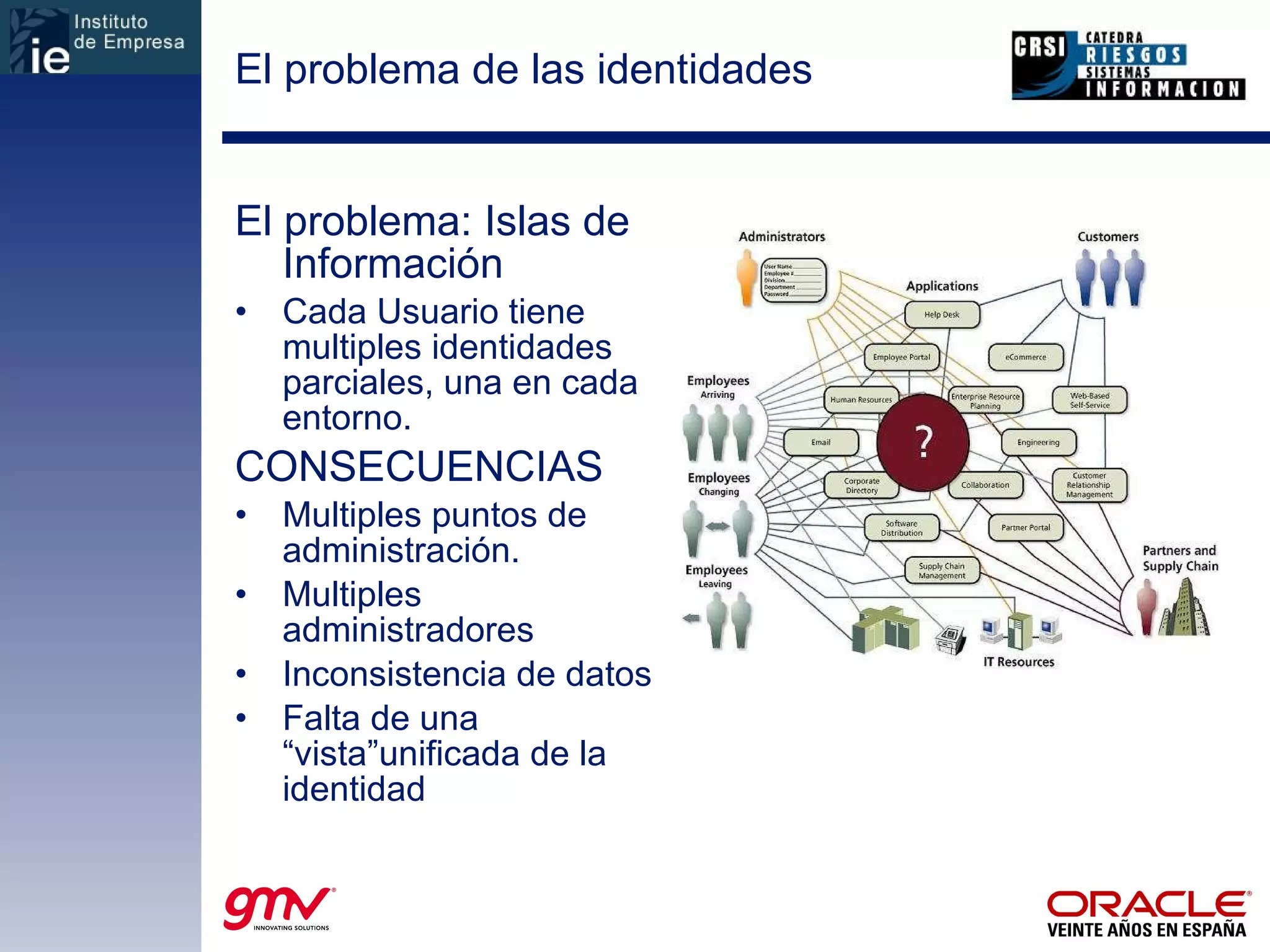
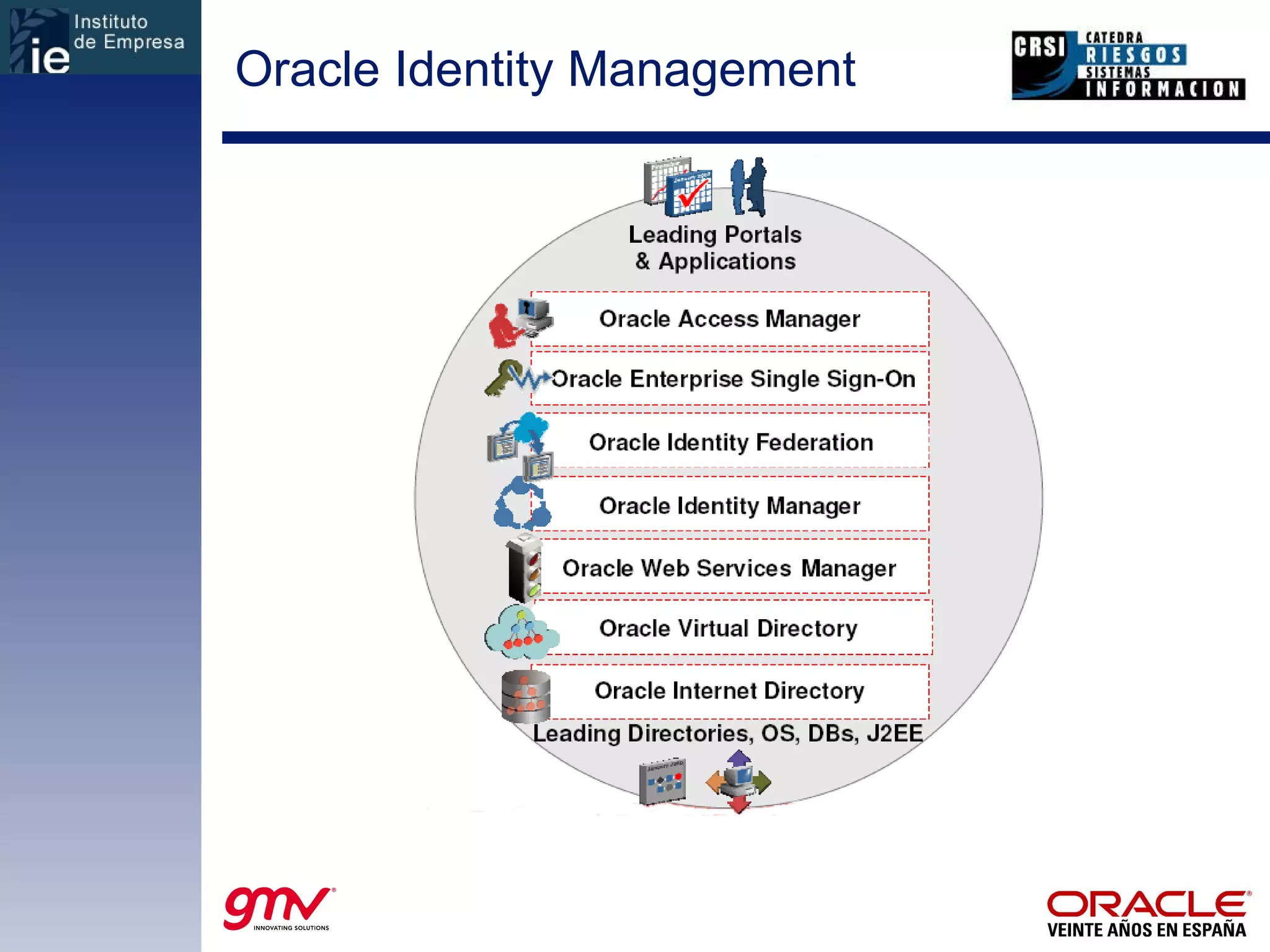
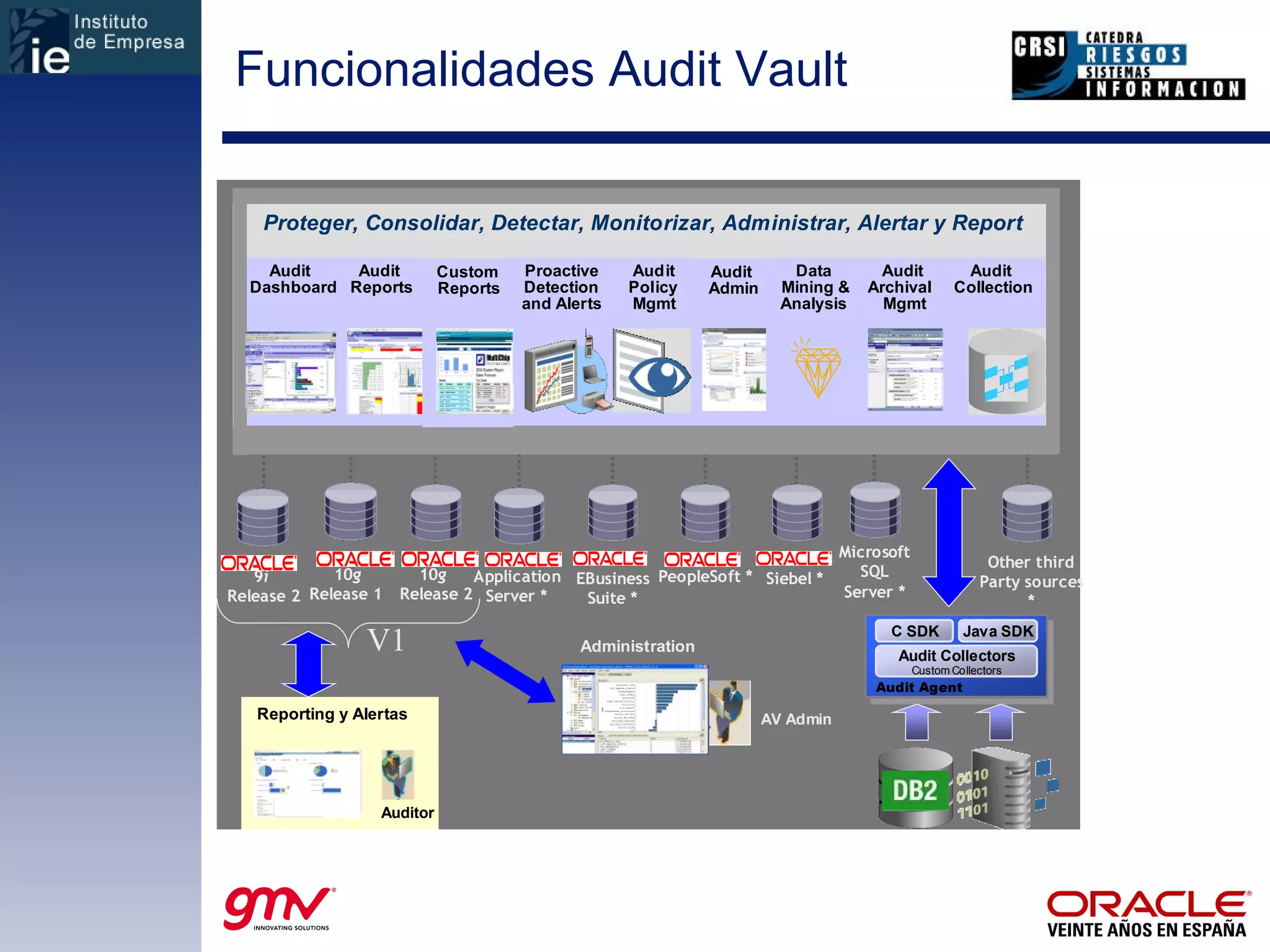
El documento describe cómo la tecnología puede facilitar el cumplimiento de los controles de seguridad de la información definidos en los estándares ISO 27001 e ISO 27002. Explica cómo herramientas como Oracle Database Vault y Oracle Identity Management ayudan a controlar el acceso a datos y a cumplir con requisitos como la LOPD española sobre registro y auditoría de accesos.