Denunciar
Compartir
Descargar para leer sin conexión
Recomendados
Many Machine Learning inference workloads compute predictions based on a limited number of models that are deployed together in the system. These models often share common structure and state. This scenario provides large rooms for optimizations of runtime and memory, which current systems fall short in exploring because they employ a black-box model of ML models and tasks, thus being unaware of optimization and sharing opportunities.
On the opposite side, Pretzel adopts a white-box description of ML models, which allows the framework to perform optimizations over deployed models and running tasks, saving memory and increasing the overall system performance. In this talk we will show the motivations behind Pretzel, its current design and possible future developments.Pretzel: optimized Machine Learning framework for low-latency and high throug...

Pretzel: optimized Machine Learning framework for low-latency and high throug...NECST Lab @ Politecnico di Milano
Recomendados
Many Machine Learning inference workloads compute predictions based on a limited number of models that are deployed together in the system. These models often share common structure and state. This scenario provides large rooms for optimizations of runtime and memory, which current systems fall short in exploring because they employ a black-box model of ML models and tasks, thus being unaware of optimization and sharing opportunities.
On the opposite side, Pretzel adopts a white-box description of ML models, which allows the framework to perform optimizations over deployed models and running tasks, saving memory and increasing the overall system performance. In this talk we will show the motivations behind Pretzel, its current design and possible future developments.Pretzel: optimized Machine Learning framework for low-latency and high throug...

Pretzel: optimized Machine Learning framework for low-latency and high throug...NECST Lab @ Politecnico di Milano
Addition is a fundamental arithmetic operation and acts as a building block for synthesizing of all other operations. A high-performance adder is one of the key components in the design of Application Specific Integrated Circuits (ASIC). In this work, three low power full adders are designed with full swing AND, OR and XOR gates to reduce threshold voltage problem which is commonly encountered in Gate Diffusion Input (GDI) logic. This problem usually does not allow the full adder circuits to operate without additional inverters. However, the three full adders are successfully realized using full swing gates with the significant improvement in their performance. The performance of the proposed design is simulated through SPICE simulations using 45 nm technology models.Energy Efficient Full Adders for Arithmetic Applications Based on GDI Logic

Energy Efficient Full Adders for Arithmetic Applications Based on GDI LogicAssociate Professor in VSB Coimbatore
1st Semester M Tech Computer Science and Engg (Dec-2013) Question Papers 

1st Semester M Tech Computer Science and Engg (Dec-2013) Question Papers BGS Institute of Technology, Adichunchanagiri University (ACU)
Más contenido relacionado
La actualidad más candente
Addition is a fundamental arithmetic operation and acts as a building block for synthesizing of all other operations. A high-performance adder is one of the key components in the design of Application Specific Integrated Circuits (ASIC). In this work, three low power full adders are designed with full swing AND, OR and XOR gates to reduce threshold voltage problem which is commonly encountered in Gate Diffusion Input (GDI) logic. This problem usually does not allow the full adder circuits to operate without additional inverters. However, the three full adders are successfully realized using full swing gates with the significant improvement in their performance. The performance of the proposed design is simulated through SPICE simulations using 45 nm technology models.Energy Efficient Full Adders for Arithmetic Applications Based on GDI Logic

Energy Efficient Full Adders for Arithmetic Applications Based on GDI LogicAssociate Professor in VSB Coimbatore
La actualidad más candente (19)
FPGA Implementation of Mix and Inverse Mix Column for AES Algorithm

FPGA Implementation of Mix and Inverse Mix Column for AES Algorithm
A high performance fir filter architecture for fixed and reconfigurable appli...

A high performance fir filter architecture for fixed and reconfigurable appli...
Future semantic segmentation with convolutional LSTM

Future semantic segmentation with convolutional LSTM
Iaetsd vlsi architecture for exploiting carry save arithmetic using verilog hdl

Iaetsd vlsi architecture for exploiting carry save arithmetic using verilog hdl
High performance nb-ldpc decoder with reduction of message exchange 

High performance nb-ldpc decoder with reduction of message exchange
Implementation of Low Power and Area-Efficient Carry Select Adder

Implementation of Low Power and Area-Efficient Carry Select Adder
COUPLED FPGA/ASIC IMPLEMENTATION OF ELLIPTIC CURVE CRYPTO-PROCESSOR

COUPLED FPGA/ASIC IMPLEMENTATION OF ELLIPTIC CURVE CRYPTO-PROCESSOR
Energy Efficient Full Adders for Arithmetic Applications Based on GDI Logic

Energy Efficient Full Adders for Arithmetic Applications Based on GDI Logic
Similar a ca-ap9222-pdf
1st Semester M Tech Computer Science and Engg (Dec-2013) Question Papers 

1st Semester M Tech Computer Science and Engg (Dec-2013) Question Papers BGS Institute of Technology, Adichunchanagiri University (ACU)
2nd Semester M Tech: Structural Engineering (June-2015) Question Papers2nd Semester M Tech: Structural Engineering (June-2015) Question Papers

2nd Semester M Tech: Structural Engineering (June-2015) Question PapersBGS Institute of Technology, Adichunchanagiri University (ACU)
8th Semester Computer Science (2013-June) Question Papers

8th Semester Computer Science (2013-June) Question PapersBGS Institute of Technology, Adichunchanagiri University (ACU)
7th Semester (June; July-2015) Computer Science and Information Science Engineering Question Papers7th Semester (June; July-2015) Computer Science and Information Science Engin...

7th Semester (June; July-2015) Computer Science and Information Science Engin...BGS Institute of Technology, Adichunchanagiri University (ACU)
Achieving Portability and Efficiency in a HPC Code Using Standard Message-pas...

Achieving Portability and Efficiency in a HPC Code Using Standard Message-pas...Derryck Lamptey, MPhil, CISSP
Similar a ca-ap9222-pdf (20)
1st Semester M Tech Computer Science and Engg (Dec-2013) Question Papers 

1st Semester M Tech Computer Science and Engg (Dec-2013) Question Papers
IFSM 310 Software and Hardware Infrastructure ConceptsComputer.docx

IFSM 310 Software and Hardware Infrastructure ConceptsComputer.docx
2nd Semester M Tech: Structural Engineering (June-2015) Question Papers

2nd Semester M Tech: Structural Engineering (June-2015) Question Papers
Digital Ic Applications Jntu Model Paper{Www.Studentyogi.Com}

Digital Ic Applications Jntu Model Paper{Www.Studentyogi.Com}
D I G I T A L I C A P P L I C A T I O N S J N T U M O D E L P A P E R{Www

D I G I T A L I C A P P L I C A T I O N S J N T U M O D E L P A P E R{Www
8th Semester Computer Science (2013-June) Question Papers

8th Semester Computer Science (2013-June) Question Papers
7th Semester (June; July-2015) Computer Science and Information Science Engin...

7th Semester (June; July-2015) Computer Science and Information Science Engin...
Lightweight hamming product code based multiple bit error correction coding s...

Lightweight hamming product code based multiple bit error correction coding s...
Achieving Portability and Efficiency in a HPC Code Using Standard Message-pas...

Achieving Portability and Efficiency in a HPC Code Using Standard Message-pas...
Comprehensive Performance Evaluation on Multiplication of Matrices using MPI

Comprehensive Performance Evaluation on Multiplication of Matrices using MPI
III EEE-CS2363-Computer-Networks-important-questions-for-unit-3-unit-4-for-ma...

III EEE-CS2363-Computer-Networks-important-questions-for-unit-3-unit-4-for-ma...
Más de SRI TECHNOLOGICAL SOLUTIONS
Más de SRI TECHNOLOGICAL SOLUTIONS (20)
Request for-new-pan-card-or-and-changes-or-correction-in-pan-data-form

Request for-new-pan-card-or-and-changes-or-correction-in-pan-data-form
Último
💉💊+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHABI}}+971581248768
+971581248768 Mtp-Kit (500MG) Prices » Dubai [(+971581248768**)] Abortion Pills For Sale In Dubai, UAE, Mifepristone and Misoprostol Tablets Available In Dubai, UAE CONTACT DR.Maya Whatsapp +971581248768 We Have Abortion Pills / Cytotec Tablets /Mifegest Kit Available in Dubai, Sharjah, Abudhabi, Ajman, Alain, Fujairah, Ras Al Khaimah, Umm Al Quwain, UAE, Buy cytotec in Dubai +971581248768''''Abortion Pills near me DUBAI | ABU DHABI|UAE. Price of Misoprostol, Cytotec” +971581248768' Dr.DEEM ''BUY ABORTION PILLS MIFEGEST KIT, MISOPROTONE, CYTOTEC PILLS IN DUBAI, ABU DHABI,UAE'' Contact me now via What's App…… abortion Pills Cytotec also available Oman Qatar Doha Saudi Arabia Bahrain Above all, Cytotec Abortion Pills are Available In Dubai / UAE, you will be very happy to do abortion in Dubai we are providing cytotec 200mg abortion pill in Dubai, UAE. Medication abortion offers an alternative to Surgical Abortion for women in the early weeks of pregnancy. We only offer abortion pills from 1 week-6 Months. We then advise you to use surgery if its beyond 6 months. Our Abu Dhabi, Ajman, Al Ain, Dubai, Fujairah, Ras Al Khaimah (RAK), Sharjah, Umm Al Quwain (UAQ) United Arab Emirates Abortion Clinic provides the safest and most advanced techniques for providing non-surgical, medical and surgical abortion methods for early through late second trimester, including the Abortion By Pill Procedure (RU 486, Mifeprex, Mifepristone, early options French Abortion Pill), Tamoxifen, Methotrexate and Cytotec (Misoprostol). The Abu Dhabi, United Arab Emirates Abortion Clinic performs Same Day Abortion Procedure using medications that are taken on the first day of the office visit and will cause the abortion to occur generally within 4 to 6 hours (as early as 30 minutes) for patients who are 3 to 12 weeks pregnant. When Mifepristone and Misoprostol are used, 50% of patients complete in 4 to 6 hours; 75% to 80% in 12 hours; and 90% in 24 hours. We use a regimen that allows for completion without the need for surgery 99% of the time. All advanced second trimester and late term pregnancies at our Tampa clinic (17 to 24 weeks or greater) can be completed within 24 hours or less 99% of the time without the need surgery. The procedure is completed with minimal to no complications. Our Women's Health Center located in Abu Dhabi, United Arab Emirates, uses the latest medications for medical abortions (RU-486, Mifeprex, Mifegyne, Mifepristone, early options French abortion pill), Methotrexate and Cytotec (Misoprostol). The safety standards of our Abu Dhabi, United Arab Emirates Abortion Doctors remain unparalleled. They consistently maintain the lowest complication rates throughout the nation. Our Physicians and staff are always available to answer questions and care for women in one of the most difficult times in their lives. The decision to have an abortion at the Abortion Cl+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...?#DUbAI#??##{{(☎️+971_581248768%)**%*]'#abortion pills for sale in dubai@
Último (20)
Why Teams call analytics are critical to your entire business

Why Teams call analytics are critical to your entire business
Vector Search -An Introduction in Oracle Database 23ai.pptx

Vector Search -An Introduction in Oracle Database 23ai.pptx
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood

Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood
TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery

TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery
Connector Corner: Accelerate revenue generation using UiPath API-centric busi...

Connector Corner: Accelerate revenue generation using UiPath API-centric busi...
Apidays New York 2024 - Accelerating FinTech Innovation by Vasa Krishnan, Fin...

Apidays New York 2024 - Accelerating FinTech Innovation by Vasa Krishnan, Fin...
ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke

ProductAnonymous-April2024-WinProductDiscovery-MelissaKlemke
Finding Java's Hidden Performance Traps @ DevoxxUK 2024

Finding Java's Hidden Performance Traps @ DevoxxUK 2024
Elevate Developer Efficiency & build GenAI Application with Amazon Q

Elevate Developer Efficiency & build GenAI Application with Amazon Q
"I see eyes in my soup": How Delivery Hero implemented the safety system for ...

"I see eyes in my soup": How Delivery Hero implemented the safety system for ...
Biography Of Angeliki Cooney | Senior Vice President Life Sciences | Albany, ...

Biography Of Angeliki Cooney | Senior Vice President Life Sciences | Albany, ...
Modular Monolith - a Practical Alternative to Microservices @ Devoxx UK 2024

Modular Monolith - a Practical Alternative to Microservices @ Devoxx UK 2024
Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...

Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...
+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...
Rising Above_ Dubai Floods and the Fortitude of Dubai International Airport.pdf

Rising Above_ Dubai Floods and the Fortitude of Dubai International Airport.pdf
Introduction to Multilingual Retrieval Augmented Generation (RAG)

Introduction to Multilingual Retrieval Augmented Generation (RAG)
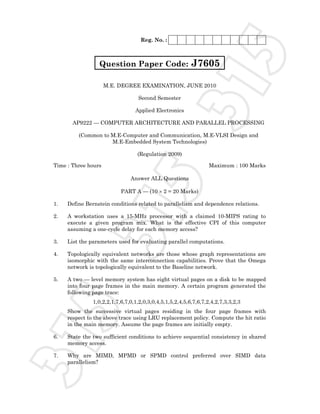
ca-ap9222-pdf
- 1. Reg. No. : M.E. DEGREE EXAMINATION, JUNE 2010 Second Semester Applied Electronics AP9222 — COMPUTER ARCHITECTURE AND PARALLEL PROCESSING (Common to M.E-Computer and Communication, M.E-VLSI Design and M.E-Embedded System Technologies) (Regulation 2009) Time : Three hours Maximum : 100 Marks Answer ALL Questions PART A — (10 × 2 = 20 Marks) 1. Define Bernstein conditions related to parallelism and dependence relations. 2. A workstation uses a 15-MHz processor with a claimed 10-MIPS rating to execute a given program mix. What is the effective CPI of this computer assuming a one-cycle delay for each memory access? 3. List the parameters used for evaluating parallel computations. 4. Topologically equivalent networks are those whose graph representations are isomorphic with the same interconnection capabilities. Prove that the Omega network is topologically equivalent to the Baseline network. 5. A two — level memory system has eight virtual pages on a disk to be mapped into four page frames in the main memory. A certain program generated the following page trace: 1,0,2,2,1,7,6,7,0,1,2,0,3,0,4,5,1,5,2,4,5,6,7,6,7,2,4,2,7,3,3,2,3 Show the successive virtual pages residing in the four page frames with respect to the above trace using LRU replacement policy. Compute the hit ratio in the main memory. Assume the page frames are initially empty. 6. State the two sufficient conditions to achieve sequential consistency in shared memory access. 7. Why are MIMD, MPMD or SPMD control preferred over SIMD data parallelism? Question Paper Code: J7605315 315 315
- 2. J76052 8. Compare the advantages and disadvantages of chained directories for cache coherence control in large-scale multiprocessor systems. 9. Bring out the differences in the message passing OS models. 10. Distinguish between spin locks and suspended locks for sole access Lou critical section. PART B — (5 × 16 = 80 Marks) 11. (a) (i) Analyze the data dependencies among the following statements in the given program: s1: Load RI, 1024 s2: Load R2, M(10) s3: Add Rl, R2 s4: Store M(1024), R1 s5: Store M((R2)), 1024 where (Ri) means the content of register Ri and M(10) contains 64 initially. (1) Draw a dependence graph to show all the dependencies. (2) Are there any resource dependencies if only one copy of each functional unit is available the CPU? (8) (ii) Explain about the theoretical models of parallel computers used by algorithm designers and chip developers. (8) Or (b) Characterize the architectural operations of SIMD and MIMD computers. Distinguish between multiprocessors and multicomputer based on their structures, resource sharing and interprocessor communications. Also explain the differences among UMA, NUMA, COMA and NORMA computers. (16) 12. (a) Explain the applicability and restrictions involved in using Amdhal’s law, Guustafon’s law, Sun and Ni’s law to estimate the speedup performance of an n-processor system compared with that of a single-processor system ignoring all communication overheads. (16) Or (b) (i) Compare control flow, data flow and reduction computers in terms of the program flow mechanism used. Comment on the advantages and disadvantages of the above computer models. (8) (ii) Explain the steps involved in calculating the grain size and communication latency for multiplying two 2 × 2 matrices. (8) 315 315 315
- 3. J76053 13. (a) (i) Explain the difference between superscalar and VLIW architectures in terms of hardware and software requirements. (8) (ii) Consider a two level memory hierarchy M1 and M2. Denote the hit ratio of MI as h. Let c1 and c2 be the costs per kilobyte, s1 and s2 the memory capacities, and t1 and t2 the access times respectively. (8) (1) Under what conditions will the average cost of the entire memory approach c2. (2) What is the effective memory access time of this hierarchy? (3) Let r=t2/tl be the speed ratio of the two memories. Let E=t1/ta be the access efficiency of the memory system. Express E in terms of r and h. (4) What is the required hit ratio h to make E>0.95 if r=l00? Or (b) (i) Describe the daisy chaining and the distributed arbiter for bus arbitration on a multiprocessor system. State the advantages and shortcomings of each from both the implementational and operational points of view. (8) (ii) Consider the following three interleaved memory designs for a main memory system with 16 memory modules. Each module is assumed to have a capacity of 1Mbyte. The machine is byte-addressable. Design I: 16- way interleaving with one memory bank Design 2: 8-way interleaving with two memory banks. Design 3: 4 way interleaving with four memory banks. (1) Specify the address formats for each of the above memory organizations. (2) Determine the maximum memory bandwidth obtained if only one memory module fails in each of the above memory organizations. (3) Comment on the relative merits of the three interleaved memory organizations. (8) 14. (a) (i) Why are fine-grain processors chosen for future multiprocessors over medium-grain processors used in the past? From scalability point of view why is fine-grain parallelism more appealing than medium-grain or coarse-grain parallelism for building MPP systems? (8) (ii) Compare the connection machines CM-2 and CM-5 in their architectures, operation modes, functional capabilities and potential performance. Comment on the improvement made in CM-5 over CM-2 from the viewpoints of a computer architect and a machine programmer. (8) Or 315 315 315
- 4. J76054 (b) (i) Prove that the greedy algorithm for multicast routing on a wormhole routed hypercube network always yields the minimum network traffic and minimum distance from the source to any of the destinations. (6) (ii) Consider the following reservation table for a four stage pipeline with a clock cycle r = 20 ns. 1 2 3 4 5 6 S1 X X S2 X X S3 X S4 X X One non-compute delay stage into the pipeline can be inserted to make a latency of 1 permissible in the shortest greedy cycle. The purpose is to yield a new reservation table leading to an optimal latency equal to the upper bound. (10) (1) Show the modified reservation table with five rows and seven columns. (2) Draw the state transition diagram for the optimal cycle. (3) List all the simple and greedy cycles from the state diagram. (4) Prove that the new MAL equals the lower bound. (5) What is the optimal throughput of this pipeline? 15. (a) (i) What is perfect decomposition? Discuss the differences in program replication techniques on multi-computers as opposed to program partitioning on multiprocessors. (8) (ii) Explain the multiprocessor UNIX design goals in the areas of compatibility, portability, address space, load balancing, parallel I/O and network services. (8) Or (b) Explain loop transformation theory and discuss how it can be applied for loop vectorization or Parallelization. ——————— 315 315 315
