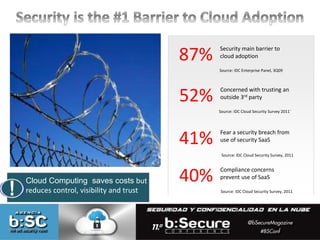
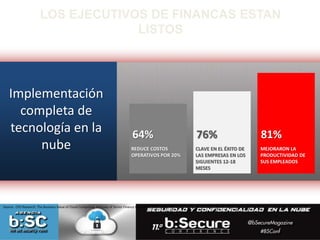
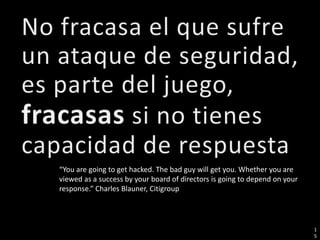
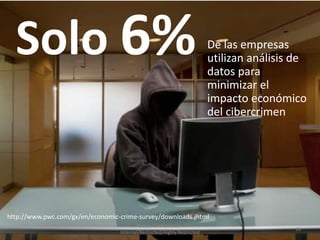
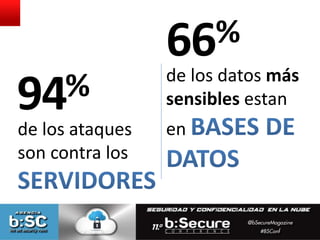
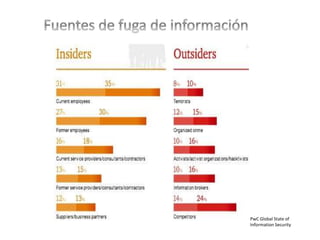
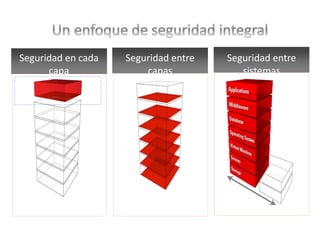
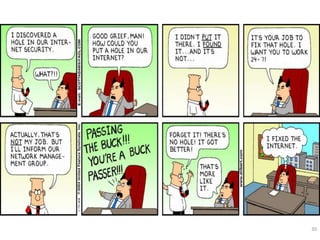
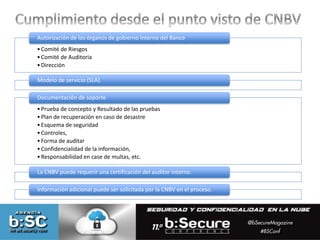
El documento discute los desafíos de seguridad y privacidad relacionados con la adopción de la nube. Señala que la principal barrera para la adopción de la nube es la seguridad (87%) y que muchas empresas tienen preocupaciones sobre confiar en un tercero externo con sus datos (52%) o sobre posibles violaciones de seguridad al usar servicios de seguridad en la nube (41%). También menciona que la complejidad reduce la innovación y que se necesita un enfoque integral de gestión de riesgos para abordar vulnerabilidades